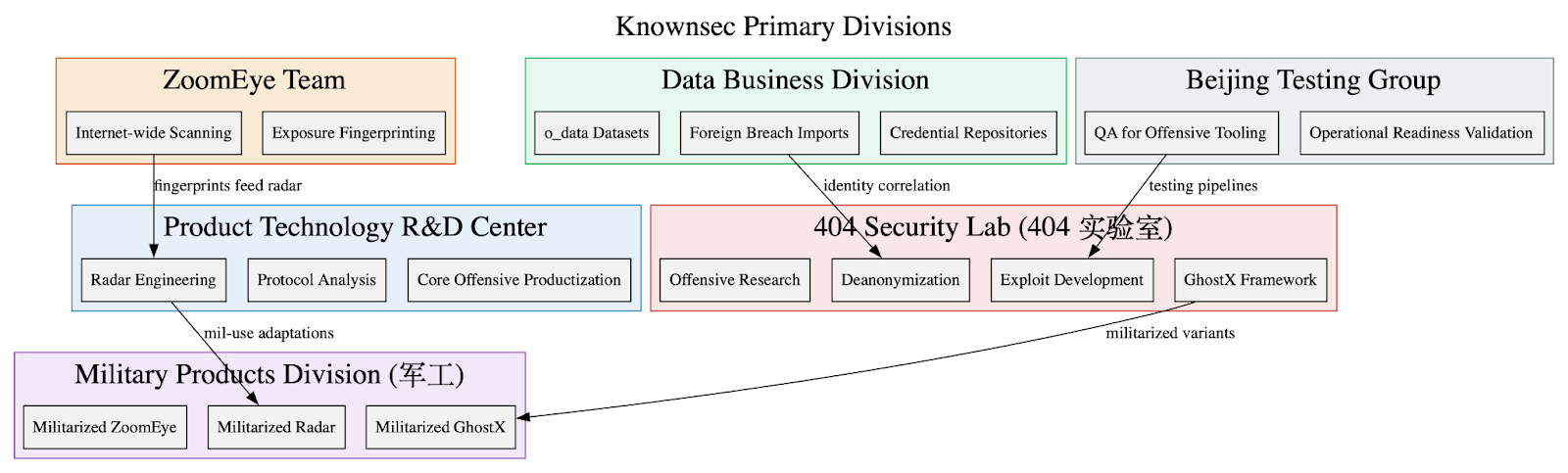
Leaked internal Knownsec documents show the company functions as a state-aligned cyber contractor providing an integrated espionage stack—ZoomEye, TargetDB, GhostX, Un‑Mail, and Passive Radar—supporting PLA/MPS/public-security and critical-infrastructure targeting worldwide. The corpus includes massive breach datasets (o_data_*), detailed TargetDB asset mappings (notably Taiwan telecom/finance/energy), and tooling for browser exploitation, mailbox takeover, PCAP-driven network reconstruction, persistence, and OPSEC/anti-forensics. #Knownsec #GhostX
Keypoints
- Knownsec operates a vertically integrated offensive capability stack (ZoomEye, TargetDB, GhostX, Un‑Mail, Passive Radar) that fuses internet-scale reconnaissance with identity datasets to enable deanonymization and targeting.
- TargetDB contains extensive classified annotations: ~378,942,040 IPs, 3,482,468 domains, and 24,241 organizations across 26 regions, mapped by sector (military, telecom, energy, finance, etc.).
- o_data_* data lake aggregates large breach and subscriber datasets (LinkedIn, Yahoo TW, Indian telecoms, Chinese national records) used to correlate infrastructure with real identities and power targeted social engineering.
- GhostX provides browser fingerprinting, credential extraction, cookie/session theft, routing/DNS manipulation, keylogging, and admin-account creation to convert fleeting access into durable control.
- Un‑Mail performs XSS-based webmail compromise, IMAP/POP mailbox replication, and real-time keyword monitoring to enable persistent COMINT-style collection across major global providers.
- Passive Radar ingests PCAPs (offline, FTP, SSH) to reconstruct internal network topologies, behavioral flows, and lateral-movement opportunities without active probing.
- Leaked org charts, WBS sheets, and personnel lists link Knownsec’s tooling and datasets directly to Public Security Bureaus, MIIT/CNNIC, and state-owned carriers, indicating institutionalized state support and procurement-aligned funding.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Used for XSS-based compromise of webmail portals enabling Un‑Mail mailbox takeover (‘XSS exploitation of webmail portals’).
- [T1566 ] Phishing – Social-engineering campaigns are built from breach datasets and credential correlations to induce initial access (‘social-engineering campaigns crafted through breach data’).
- [T1555.003 ] Credentials from Web Browsers – Browser-stored password extraction and credential theft via GhostX (‘password extraction’, ‘browser-stored passwords’).
- [T1056.001 ] Input Capture: Keylogging – Keylogging modules capture typed credentials and sensitive inputs on compromised hosts (‘keylogging’).
- [T1136 ] Create Account – Creation of admin user accounts on routers and internal services to obtain durable infrastructure-level footholds (‘admin user creation on routers or internal services’).
- [T1078 ] Valid Accounts – Credential replay and takeover of existing accounts (including reuse and session replay) to maintain access (‘credential replay attacks, account takeover attempts’).
- [T1040 ] Network Sniffing – Passive Radar ingests and analyzes PCAPs to reconstruct internal network behavior and identify high-value hosts (‘ingestion and analysis of packet capture (PCAP) data’).
- [T1114 ] Email Collection – IMAP/POP mailbox replication and full inbox exfiltration performed by Un‑Mail (‘IMAP/POP mailbox replication’, ‘Full inbox exfiltration’).
- [T1027 ] Obfuscated Files or Information – Code mixing, signatureless execution, and behavior obfuscation used to evade detection (‘code mixing, behavior shaping, and signatureless execution’).
- [T1070 ] Indicator Removal on Host – Anti-tracing modules and log/indicator modification to degrade forensic visibility (‘remove or modify indicators that typically reveal compromise’).
- [T1090 ] Proxy – Proxy chain deployment and multi-hop routing to obscure origin and resist attribution (‘proxy chain deployment, allowing operators to route traffic through multilayered, frequently shifting intermediaries’).
- [T1071 ] Application Layer Protocol – Web-based callbacks and flexible C2 communications leveraging application protocols and web callbacks (‘web-based callbacks and multi-hop proxy chains that obscure operational origins’).
Indicators of Compromise
- [IP Address ] Critical infrastructure targeting – 210.242.194.198 (Nan Shan Life Insurance, Fortinet FortiGate), 219.80.43.14 (Hua Nan Commercial Bank, Fortinet FortiGate), and other targeted CII IPs.
- [IP Address ] Telecom / energy targets – 220.130.186.202 (Chunghwa Telecom, Sophos XG), 61.65.236.240 (Taipower, Check Point), and additional Taiwan CII addresses.
- [Dataset / HDFS names ] Identity and breach archives – o_data_taiwanahooemailpwd_tw (Taiwan Yahoo email/password dump), linkedin_brazil (LinkedIn Brazil dataset), and many other o_data_* entries.
- [File names ] Leaked document artifacts – 关基目标库说明文档_V202309.pdf (TargetDB doc), 无源雷达–产品文档 (Passive Radar manual), and screenshots 1.png … 64.png.
- [Email domains ] Internal corporate accounts – @knownsec.com (Beijing/headquarters operational accounts), @xm.knownsec.com (Xiamen R&D/engineering accounts) used across WBS and personnel records.
- [Device / Service Banners ] Fingerprinted appliances – Fortinet FortiGate, Sophos XG, Check Point (identified in TargetDB rows and radar outputs) used to prioritize exploitation.
- [Organization Targets ] Named targets / customers – Chunghwa Telecom, Nan Shan Life Insurance, Hua Nan Commercial Bank, Taipower (examples cited in TargetDB / radar screenshots).