CRIL uncovered a large-scale, browser-based phishing campaign impersonating India’s e-Challan/Parivahan services that delivers malicious links via SMS and harvests card data through fake payment pages. The same shared infrastructure also hosts BFSI and logistics-themed lures, with key artifacts including domains like echala[.]vip and hosting IPs 101[.]33[.]78[.]145 and 43[.]130[.]12[.]41. #eChallan #StateBankOfIndia
Keypoints
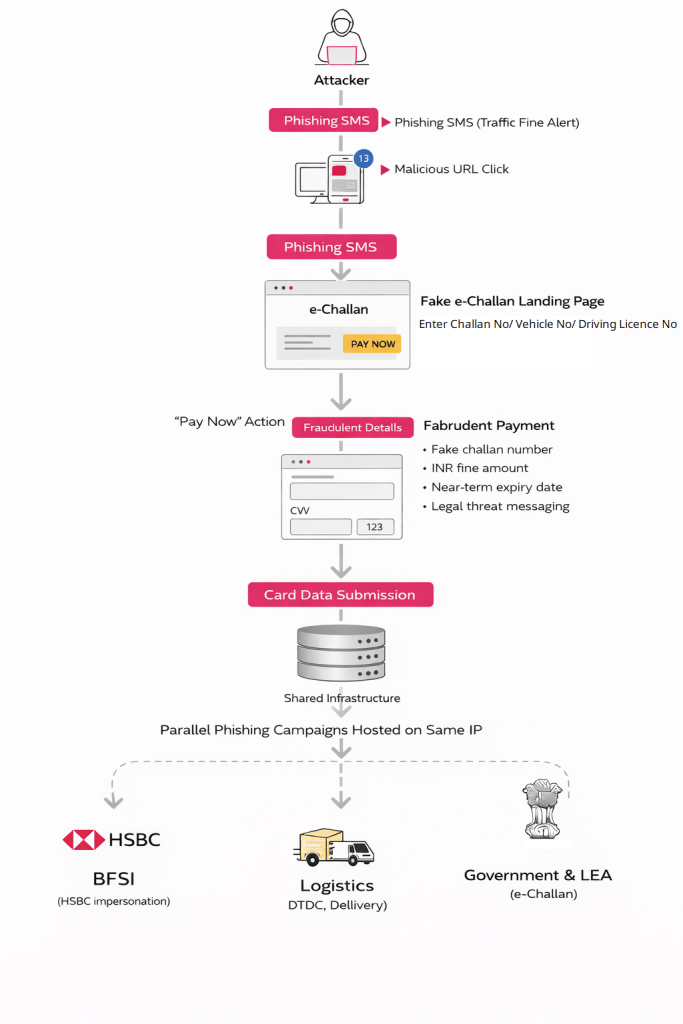
- Attackers send unsolicited SMS messages claiming overdue traffic fines containing deceptive URLs that mimic official e-Challan portals.
- Phishing pages are browser-based (no Android malware), present cloned government branding, and dynamically generate believable challan records to convince victims.
- Payment flow restricts victims to credit/debit card entry (CVV, expiry, cardholder name) and transmits card details directly to attacker-controlled backends.
- Multiple phishing lures (government, BFSI, logistics) are hosted on shared infrastructure, indicating a scalable, multi-sector phishing ecosystem.
- Primary infrastructure includes IPs 101[.]33[.]78[.]145 and 43[.]130[.]12[.]41 and more than 36 phishing domains impersonating Parivahan/e-Challan services.
- SMS origin analysis showed use of a local Reliance Jio mobile number linked to an SBI account, increasing perceived legitimacy of messages.
MITRE Techniques
- [T1566.001 ] Phishing: Spearphishing via SMS – Initial delivery via SMS claiming an overdue traffic fine to lure victims (‘victims receiving an SMS stating that a traffic violation fine is overdue and must be paid immediately’).
- [T1056 ] Input Capture – Harvesting of payment credentials on fake payment pages collecting CVV, expiry date, and cardholder name (‘CVV, expiry date, and cardholder name are collected directly’).
- [T1119 ] Automated Collection – Dynamic fabrication and generation of challan records and rotating phishing domains that automate lure creation (‘the portal prompts… Regardless of the input provided, the system returns… A valid-looking challan record’).
- [T1041 ] Exfiltration Over C2 Channel – Stolen card data and form submissions are transmitted to attacker-controlled backend infrastructure (‘all entered card data is transmitted to the attacker backend’).
- [T1657 ] Financial Theft – Direct financial fraud via harvested card-not-present data used for unauthorized transactions (‘harvest full card details while falsely claiming to be backed by the State Bank of India’).
Indicators of Compromise
- [Domain ] Phishing domains impersonating e-Challan/Parivahan and brands – echala[.]vip, parizvaihen[.]icu, and 36+ other related domains.
- [IP Address ] Hosting infrastructure serving multiple phishing lures – 101[.]33[.]78[.]145, 43[.]130[.]12[.]41.
- [Domain ] Logistics/BFSI-themed phishing examples tied to same infrastructure – dtdcspostb[.]vip, hsbc-vnd[.]cc.
- [Phone Number / Telecom ] Originating SMS source and local infrastructure – Indian mobile number registered on Reliance Jio and linked to an SBI account (used to deliver e-Challan phishing SMS).