Two novel XLL-based campaigns delivered a 64-bit backdoor named EchoGather via malicious Excel add-ins and weaponized archives exploiting a WinRAR ADS path-traversal vulnerability to target Russian organizations. Analysis links the infrastructure and decoy documents to the Paper Werewolf (GOFFEE) group and highlights techniques including delayed execution via DLL_THREAD_DETACH, hidden process creation, HTTP(S) C2 over WinHTTP, Base64-encoded communications, and exploitation of CVE-2025-8088. #EchoGather #PaperWerewolf #XLL #CVE-2025-8088
Keypoints
- Attackers abused the Excel .XLL add-in format to load native DLLs that execute arbitrary code when Excel loads the file, enabling native-code persistence and functionality beyond macro security controls.
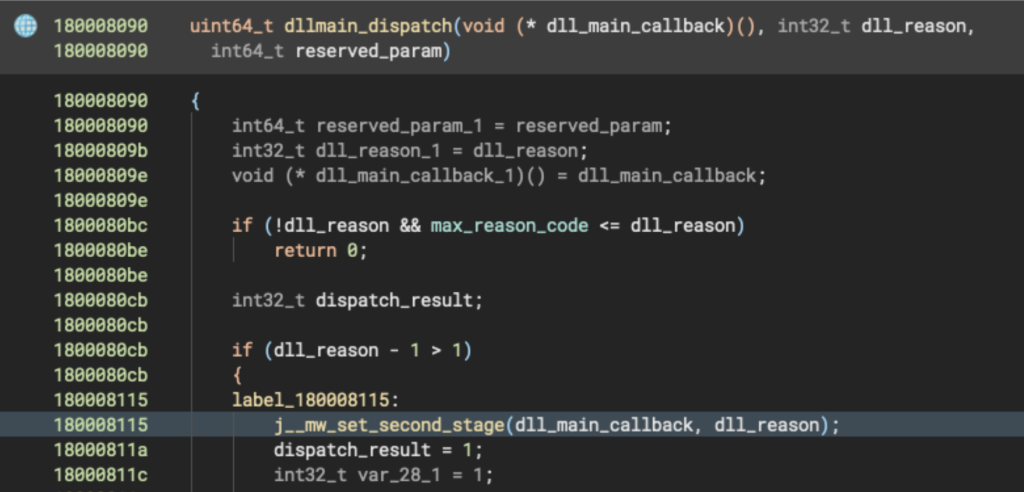
- A 64-bit XLL loader (SHA-256 0506a6f…) drops a second-stage backdoor (EchoGather, SHA-256 74fab6ad…) as mswp.exe and runs it as a hidden process using CreateProcessW with CREATE_NO_WINDOW.
- EchoGather collects system telemetry (IP, OS, NetBIOS, username, domain, PID, path, static version string), encodes it in Base64, and repeatedly POSTs to a hardcoded HTTPS C2 (e.g., fast-eda[.]my) using WinHTTP while ignoring TLS validation.
- The backdoor supports remote command execution (via cmd.exe template), returning configuration, chunked file exfiltration, and remote file write operations identified by request IDs and 512 KB chunking.
- Infrastructure pivoting identified domains ruzeda[.]com and fast-eda[.]my, RAR archives exploiting CVE-2025-8088 to plant startup scripts, and decoy Russian-language PDFs used to socially engineer targets in the Russian defense sector.
- Researchers linked the campaign to Paper Werewolf (GOFFEE) based on shared infrastructure, decoy document similarities, and reuse of WinRAR ADS-based extraction techniques, indicating evolving delivery methods (XLL) and a developing toolset.
MITRE Techniques
- [T1204.002 ] User Execution: Malicious File – XLL add-ins are executed when opened by users; quote: ‘When a user double clicks the file with the .xll extension, Excel is launched, loads the DLL and calls its exported functions such as xlAutoOpen…’
- [T1105 ] Ingress Tool Transfer – Loader drops and writes the embedded backdoor to disk as mswp.exe in AppData; quote: ‘The embedded file is dropped as mswp.exe in %APPDATA%MicrosoftWindows, then executed as a hidden process…’
- [T1547.001 ] Boot or Logon Autostart Execution: Startup Folder – Malicious RAR extraction places a batch in the Startup folder to achieve persistence; quote: ‘placing them in unintended or sensitive locations such as %APPDATA%MicrosoftWindowsStart MenuProgramsStartup.’
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – Attackers use PowerShell scripts to decode embedded payloads and spawn payload execution bypassing execution policy; quote: ‘The script is then executed via a new PowerShell instance with execution policy restrictions bypassed.’
- [T1059.003 ] Command and Scripting Interpreter: Windows Command Shell – Backdoor executes commands using cmd.exe template ‘cmd.exe /C %s’ after XOR decryption; quote: ‘decrypts the string cmd.exe /C %s using a hardcoded XOR key (0xCA)…’
- [T1071.001 ] Application Layer Protocol: Web Protocols – EchoGather communicates with C2 over HTTP(S) using WinHTTP for POST beaconing and command/control; quote: ‘communicates with the C2 over HTTP(S) using the WinHTTP API.’
- [T1041 ] Exfiltration Over C2 Channel – File exfiltration is implemented by reading files, splitting them into 512 KB chunks and sending them with request IDs to the C2; quote: ‘The file is read and transmitted in chunks, with each chunk containing the request ID, chunk index, file tag, data length, and raw file data.’
- [T1203 ] Exploitation for Client Execution – Attackers leveraged a WinRAR vulnerability (CVE-2025-8088) to perform ADS-based path traversal extraction leading to execution of startup scripts; quote: ‘a RAR archive that exploits a known vulnerability, CVE-2025-8088, … allows attackers to embed malicious content within seemingly harmless filenames by appending ADSes…’
- [T1027 ] Obfuscated Files or Information – Payloads and telemetry are Base64-encoded for delivery and C2 transport; quote: ‘EchoGather encodes that data using Base64’ and ‘Both first decode two Base64-encoded files: a PDF document and the EchoGather payload.’
- [T1036 ] Masquerading – Use of decoy documents and misleading filenames to impersonate official communications (e.g., ministry letters, concert invitation) to trick recipients; quote: ‘The document appears to be an invitation, written in Russian, to a concert for high-ranking officers.’
- [T1055 ] Process Injection (capability of XLLs) – The XLL format allows native code to call Windows APIs and inject into other processes, increasing post-execution capability; quote: ‘XLLs can call any Windows API, inject into other processes, or act as full-featured malware loaders.’
Indicators of Compromise
- [SHA-256 ] Loader and backdoor hashes – 0506a6fcee0d4bf731f1825484582180978995a8f9b84fc59b6e631f720915da (XLL loader), 74fab6adc77307ef9767e710d97c885352763e68518b2109d860bb45e9d0a8eb (EchoGather backdoor), and other submitted hashes.
- [Domain ] C2 and infrastructure – fast-eda[.]my (EchoGather C2 path used in POST beaconing), ruzeda[.]com (infrastructure serving archives and download URLs).
- [IP Address ] Resolutions and hosting – 172.64.80[.]1 (Cloudflare resolution for domains), 94.103.3[.]82 (Russian-hosted resolution observed on Nov 27); initial resolution 199.59.243[.]228 was also observed for fast-eda.my.
- [File name ] Dropped/extracted files and scripts – mswp.exe (dropped backdoor executable), docc1.ps1 and mswt.ps1 (PowerShell scripts that decode and load payloads), Вх.письмо_Мипромторг.rar (malicious RAR archive exploiting WinRAR ADSs).
- [C2 URL ] Full example C2 endpoints – https://fast-eda[.]my:443/dostavka/lavka/kategorii/zakuski/sushi/sety/skidki/regiony/msk/birylievo (EchoGather POST target); https://ruzeda[.]com/blogs/drafts/publish/…/token/refresh/ips/blocklist/whitelist (infrastructure path observed).