Proofpoint observed multiple state-aligned and financially motivated threat clusters abusing the OAuth 2.0 device authorization grant flow and social-engineering lures (embedded URLs and QR codes) to trick users into approving malicious applications and grant attackers access to Microsoft 365 accounts. These campaigns leveraged tools and kits such as SquarePhish2 and Graphish and were attributed to actors including TA2723 and UNK_AcademicFlare, enabling account takeover, data exfiltration, and further lateral activity. #TA2723 #SquarePhish2
Keypoints
- Multiple threat clusters (state-aligned and financially motivated) are using OAuth device code phishing to obtain access to Microsoft 365 accounts.
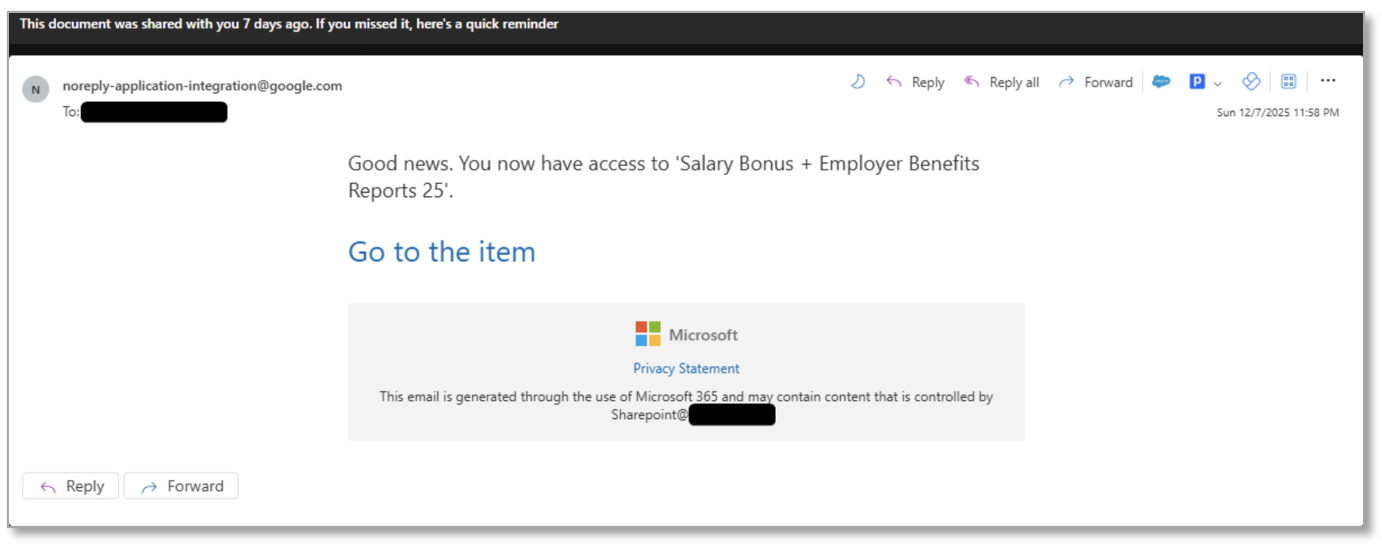
- Attack chains typically begin with phishing messages containing URLs or QR codes that redirect users to attacker-controlled landing pages which initiate the Microsoft device authorization flow.
- Once a user inputs a device code on Microsoft’s legitimate device login page, the attacker’s preconfigured application receives tokens enabling account takeover and data exfiltration.
- Tools and kits lowering the barrier to entry—SquarePhish2 and Graphish—are publicly available or circulating on forums, enabling larger and more automated campaigns.
- Proofpoint observed TA2723 conducting high-volume credential phishing and suspected Russia-aligned UNK_AcademicFlare targeting government, think tanks, higher education, and transportation sectors.
- Recommended mitigations include blocking device code flow via Conditional Access, enforcing compliant/joined devices, and user education not to enter device codes received from untrusted sources.
MITRE Techniques
- [T1566 ] Phishing – Use of email messages, embedded URLs, and QR codes to socially engineer users into initiating the device authorization flow and revealing or entering device codes (‘initial message with a URL embedded behind a button, as hyperlinked text, or within a QR code’).
- [T1557 ] Adversary-in-the-Middle – Use of reverse proxies and AiTM phishing kits (Graphish) to intercept credentials and MFA challenges, enabling session hijacking (‘leveraging Azure App Registrations and reverse proxy setups for adversary-in-the-middle (AiTM) attacks’).
- [T1078 ] Valid Accounts – Abuse of OAuth device authorization to obtain valid access tokens and use them for account takeover and persistence (‘inputting the provided code into the Microsoft-provided OAuth page provides the threat actor access to the user’s Microsoft 365 account’).
Indicators of Compromise
- [URL ] phishing/redirector/landing pages – hxxps://sharefile.progressivesharepoint.top/, hxxps://onlinedocuments-[OrganisationName].xgjtvyptrjlsosv.live/application/99[PII_Linkable]e9, and multiple other malicious redirector and landing page URLs (many listed in campaign indicators).
- [Domain ] sender or infrastructure domains used in campaigns – xgjtvyptrjlsosv.live, vaultally.com, and other sender/redirector domains such as virtoshare.com, renewauth.com, myfilepass.com.
- [Email address ] sender addresses used in phishing messages – [email protected], [email protected] (used to send lure messages and device-code emails).
- [IP ] infrastructure indicator – 196.251.80.184 (observed associated with OTP generation/redirect activity).