Acronis TRU uncovered a large malvertising campaign called TamperedChef that used social engineering to trick users into downloading malicious scripts which executed payloads to steal credentials, sell remote access, and prepare systems for future ransomware. The investigation identified dozens of malicious domains, thousands of client IPs querying IoC domains, and numerous associated email-connected and IP-connected domains. #TamperedChef #AcronisTRU
Keypoints
- Acronis TRU discovered the TamperedChef malvertising campaign that lured users into downloading malicious scripts via social engineering.
- The scripts automatically executed payloads to establish and sell remote access, steal and monetize credentials and healthcare data, prepare systems for ransomware, and enable opportunistic espionage.
- Researchers extracted 58 unique domains from initial IoCs, filtered out legitimate ones, and focused analysis on 46 suspicious domains administered via Namecheap and registered in Iceland.
- First Watch data showed 28 of the 46 domains were flagged as likely to become malicious between 155 and 335 days before being designated IoCs.
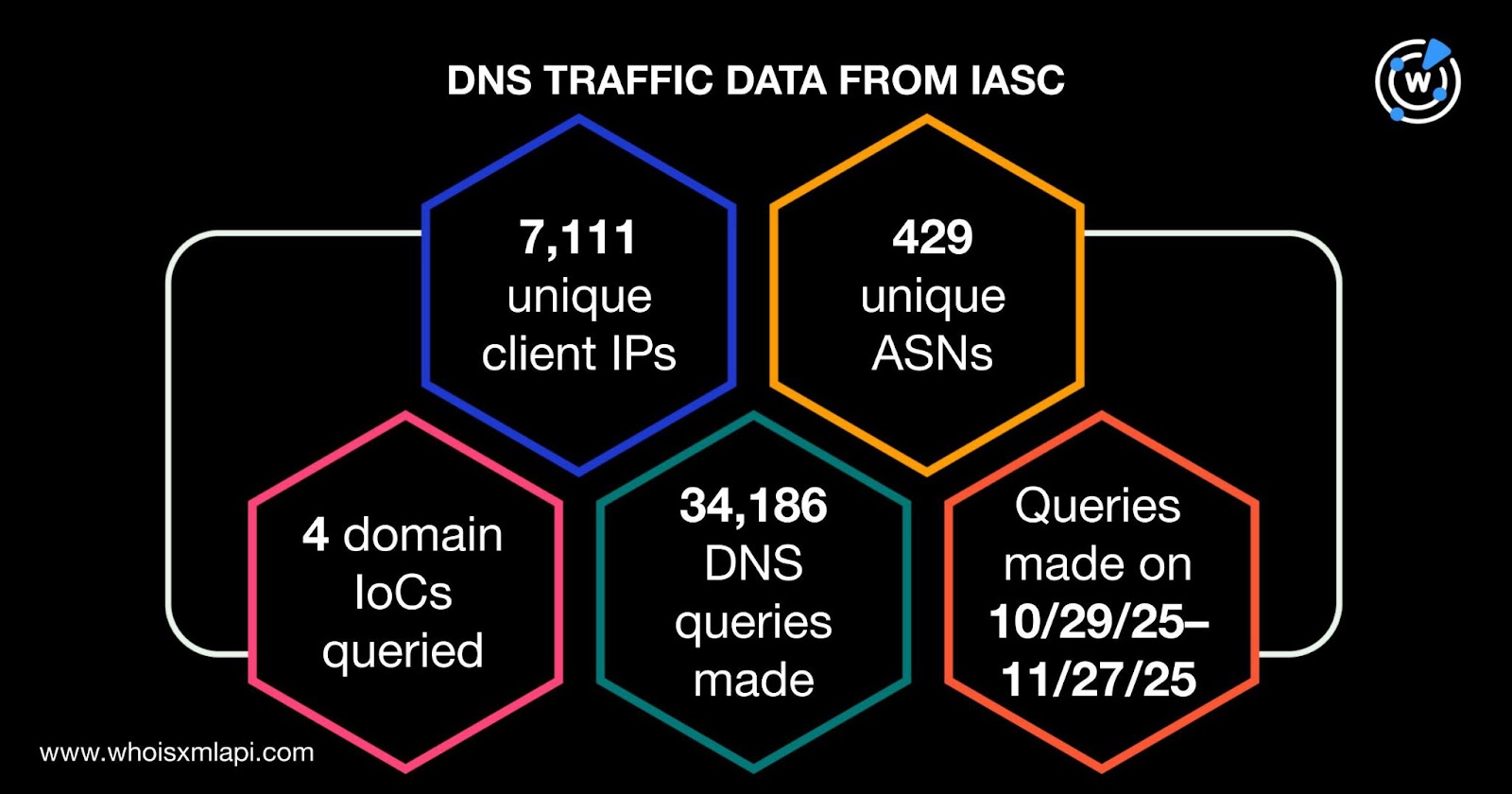
- Network telemetry revealed 7,111 unique client IPs (under 429 ASNs) made 34,186 DNS queries to four IoC domains between 29 Oct and 27 Nov 2025.
- WHOIS and DNS-history queries found 54 historical email addresses (4 public), 97 email-connected domains, 24 IP resolutions (10 weaponized), and 438 historical domain-to-IP resolutions across the IoC set.
MITRE Techniques
- [T1204 ] User Execution – Social engineering lured users into downloading malicious scripts (‘users were tricked into downloading malicious scripts via clever social engineering ruses.’)
- [T1059 ] Command and Scripting Interpreter – Malicious scripts automatically executed payloads on victims’ machines (‘The scripts automatically executed their payloads that resulted in nefarious actions…’)
- [T1133 ] External Remote Services – Actors established and sold remote access to compromised systems for profit (‘establishing and selling remote access for profit’)
- [T1005 ] Data from Local System – Actors stole and monetized sensitive credentials and healthcare data from infected systems (‘stealing and monetizing sensitive credentials and healthcare data’)
- [T1486 ] Data Encrypted for Impact (ransomware preparation) – Actors prepared compromised systems for future ransomware deployment (‘preparing compromised systems for future ransomware deployment’)
- [T1071 ] Application Layer Protocol (DNS) – Campaign leveraged DNS infrastructure and heavy DNS querying to IoC domains (‘they made 34,186 DNS queries between 29 October and 27 November 2025.’)
Indicators of Compromise
- [Domains ] malicious domains used in the campaign – getallmanuals[.]com, effortlesspdf[.]com, and 44 more domains
- [URLs/Subdomains ] IoC URLs and subdomains referenced in feed data – opfktvbbb0d5pphzlc[.]com, k2ioeasm874fnacr9x[.]com
- [IP Addresses ] historical and active IP resolutions tied to IoCs – 184[.]168[.]221[.]38, and 23 other IPs (24 IPs total, 10 flagged malicious)
- [Client IPs ] infected or querying clients observed in network data – 7,111 unique client IP addresses under 429 ASNs (34,186 DNS queries)
- [Email Addresses ] WHOIS-associated emails and public contact addresses linked to domains – 54 unique historical emails (4 public), leading to 97 email-connected domains
Read more: https://circleid.com/posts/thumbing-through-the-dns-traces-of-tamperedchef