Seqrite Labs uncovered a Russian-language phishing campaign that uses ZIP->ISO->EXE staged attachments and an ISO-mounted executable to deliver the Phantom stealer, targeting finance and accounting roles. The campaign harvests browser credentials, crypto wallets, Discord tokens, clipboard data, keylogs and exfiltrates data via Telegram, Discord webhooks and FTP. #PhantomStealer #TorFX
Keypoints
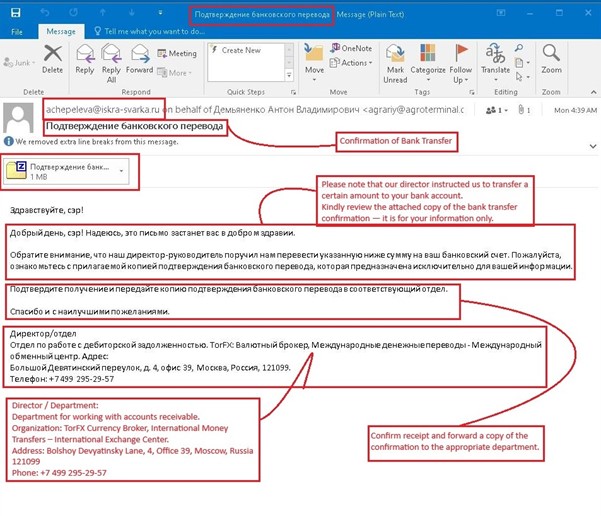
- Attack begins with a Russian-language phishing email titled “Confirmation of Bank Transfer” containing a malicious ZIP that holds an ISO image.
- Opening the ISO mounts a virtual drive with an executable that loads a staged DLL (CreativeAI.dll) which decrypts and injects the Phantom stealer into memory.
- Phantom implements multiple collection modules: browser credential/cookie/card recovery, crypto wallet harvesting (browser and desktop), Discord token theft, file collection, keylogging and clipboard monitoring.
- Anti-analysis and sandbox-evasion checks (usernames, VM GPU enumeration, process/service scans, MachineGuid checks) trigger self-deletion if analysis is detected.
- Exfiltration channels include Telegram bot API, Discord webhooks, FTP uploads and archived staging into ZIP files for transfer.
- Primary targets are finance/accounting/treasury roles in Russia, using a payment-confirmation lure and domain/email spoofing to increase credibility.
MITRE Techniques
- [T1566.001 ] Phishing: Attachment – Campaign delivered a malicious attachment used to gain initial access by impersonating a bank transfer confirmation (‘Confirmation of Bank Transfer’).
- [T1204.002 ] User Execution: Malicious File – The ISO contains an executable disguised as a payment confirmation which the user is tricked into launching (‘executable disguised as a legitimate payment confirmation’).
- [T1654 ] Drive-by Social Engineering – The email content and structure mimic legitimate business correspondence to socially engineer finance staff (‘the content and structure of the email mimic legitimate business correspondence’).
- [T1106 ] Native API Execution / Binary Execution – The delivered executable runs native APIs and binary code on the host to load further payloads (‘executable executed from mounted ISO and loaded additional payload into memory’).
- [T1027 ] Encrypted/Obfuscated Payload – The first-stage DLL (CreativeAI.dll) contains an encrypted payload that is decrypted at runtime before injection (‘DLL contains an encrypted payload, and upon decryption, it proceeds to inject the phantom Stealer’).
- [T1027.003 ] Steganography / Payload in Image – Image data (System.Drawing.Bitmap) is used as a source to reconstruct or hide executable code (‘src is a System.Drawing.Bitmap object… suggest[s] the image may contain embedded code or data’).
- [T1497 ] Virtualization/Sandbox Evasion – Anti-analysis routines enumerate GPUs, processes, services and check MachineGuid to detect virtualized or sandboxed environments and abort if detected (‘runs a sequence of environment checks to detect virtualized, sandboxed, or analyst-controlled machines’).
- [T1036 ] Masquerading – The campaign spoofs business identities and unrelated sender domains to appear legitimate (sender domains unrelated to “TorFX Currency Broker”).
- [T1070.004 ] Self-Deletion – The malware can self-destruct or erase itself if anti-analysis checks trigger (‘logs the finding and calls SelfDestruct.Melt() to abort/erase itself’).
- [T1055.001 ] DLL Injection – The first-stage component injects the decrypted payload into other processes via DLL injection (‘proceeds to inject the phantom Stealer malware’).
- [T1620 ] Reflective Loading / In-Memory Execution – Payloads are reflected/loaded into memory to avoid disk artifacts and enable in-memory execution (‘loads an additional payload into memory, which turns out to be the Phantom stealer’).
- [T1555.003 ] Credential Access from Web Browsers – Chromium-based browser credentials, cookies and credit card data are recovered via browser database parsing and decryption (‘recovers saved credentials, cookies, and stored credit-card details from the browser’s SQLite databases’).
- [T1082 ] System Information Discovery – The malware collects system metadata (username, computer name, public IP, AV status) for staging and contextual reporting (’embedding tool/version and system metadata (public IP, date, username, computer name, language, AV status)’).
- [T1057 ] Process Discovery – The malware enumerates running processes to detect analysis tools and inform anti-analysis decisions (‘iterates running processes and Windows services for known analysis tools’).
- [T1518.001 ] Security Software Discovery – The code probes for sandbox and security-related DLLs and services to evade analysis (‘probes for common sandbox DLL’).
- [T1056.001 ] Keylogging – A low-level keyboard hook captures keystrokes and writes timestamped logs periodically (‘Keylogger installs a global low-level keyboard hook… periodically writes a timestamped plaintext log’).
- [T1115 ] Clipboard Collection – Clipboard contents are polled every second and logged when new text is detected (‘spawns a background STA thread that polls the Windows clipboard every second… captures new plain-text clipboard contents’).
- [T1039 ] File Collection – Targeted file collection modules gather files from known directories for exfiltration (‘FileGrabber: Targeted File Collection and Exfiltration Module’).
- [T1119 ] Browser Data Collection – The malware enumerates browser profiles and extracts structured data from browser storage (‘scans all Chromium-based browsers… enumerates their user profiles’).
- [T1528 ] Application Token Theft (Discord) – Discord tokens are harvested from LevelDB and native client directories and validated against the Discord API (‘Discord authentication tokens… validated by sending an authenticated request to the Discord API (/users/@me)’).
- [T1555 ] Cryptocurrency Wallet Theft – Browser extension and desktop wallet directories are targeted to copy wallet data for crypto exfiltration (‘locates and extracts data from cryptocurrency wallet browser extensions… collects desktop (non-browser) cryptocurrency wallets’).
- [T1567.002 ] Exfiltration Over Web Services (Telegram) – Stolen data and reports are sent to an attacker-controlled Telegram bot via the Bot API (‘contact a Telegram Bot API endpoint using an attacker-controlled bot token’).
- [T1530 ] Exfiltration to Cloud/Webhook (Discord) – Exfiltration uses attacker-controlled Discord webhooks to upload files and reports (‘decrypted webhook URL directly from Config.DiscordWebhook’).
- [T1048 ] Exfiltration Over Unencrypted/FTP Channels – The malware can upload stolen files to an FTP server using configurable credentials (‘UploadToFtp class provides asynchronous functionality to upload files to an FTP server’).
- [T1560.001 ] Data Staged in Archive (ZIP) – Collected data is archived into ZIP files with metadata comments before exfiltration (‘Creates the output ZIP path… builds a multi-line comment embedding tool/version and system metadata’).
Indicators of Compromise
- [File Hash ] detected samples and payloads – 27bc3c4eed4e70ff5a438815b1694f83150c36d351ae1095c2811c962591e1bf, 4b16604768565571f692d3fa84bda41ad8e244f95fbe6ab37b62291c5f9b3599, and 2 more hashes
- [File Name ] malicious attachments and payloads – Подтверждение банковского перевода.zip (Confirmation of Bank Transfer.zip), Подтверждение банковского перевода.iso (Bank transfer confirmation.iso), HvNC.exe, CreativeAI.dll
- [Email / Domain ] sender and spoofed domains used in phishing – achepeleva@iskra-svarka[.]ru, agrariy@agroterminal[.]c (on behalf of), iskra-svarka[.]ru
- [C2 / Webhook URL ] command-and-control / exfiltration endpoint – Discord webhook (hxxps://discordapp.com/api/webhooks/143138186644…EPOWJm74GOZpqJMIKIKTAAWsSKMiUIaLaShpn_VTGWZPjJNYj6_ioSs-BQNZt1WK)
- [Detection Name ] vendor detection identifier – Trojan_Phantom_Y10018