A wave of cyberattacks exploiting two critical code-injection vulnerabilities in Ivanti Endpoint Manager Mobile (tracked as CVE-2026-1281 and CVE-2026-1340) has prompted emergency warnings from national security agencies worldwide. Ivanti released patches and urged customers to treat exposed systems as potentially compromised after confirmed and suspected breaches affected Dutch government bodies and…
Tag: ZERO-DAY

Microsoft observed December 2025 intrusions where attackers leveraged internet-accessible SolarWinds Web Help Desk instances to run PowerShell and download additional payloads, possibly exploiting recently patched vulnerabilities as zero-days. The adversaries established persistence and domain-level access using ManageEngine RMM, reverse SSH/RDP, scheduled QEMU VMs, DLL sideloading and DCSync to steal credentials. #SolarWindsWHD…

Singapore launched its largest coordinated cyber defense operation, Operation Cyber Guardian, after a highly targeted attack affected all four major telecommunications operators: M1, Singtel, StarHub, and Simba. The assault was attributed to UNC3886, which exploited a zero-day vulnerability and accessed a small number of critical systems but was contained by government…

APT28 quickly weaponized the Microsoft Office vulnerability CVE-2026-21509 to breach European military and government targets within 24 hours of disclosure. The attackers used convincing spear-phishing lures, fileless execution via OLE/WebDAV, and cloud-based C2 on filen.io to deploy implants including BeardShell and the email-stealing NotDoor. #APT28 #BeardShell…
Conpet, Romania’s national oil pipeline operator, confirmed a major cyberattack after the Qilin ransomware group claimed to have stolen nearly 1TB of sensitive data. Hudson Rock traced the breach to a single Infostealer infection on an IT employee’s personal computer on January 11, 2026, which leaked credentials (including WSUS and Cacti access) that enabled a likely full network takeover. #Qilin #Infostealer #Conpet #WSUS

This roundup condenses notable cybersecurity developments that include espionage, large-scale DDoS activity, AI-driven intrusions, vulnerability disclosures, and consumer data breaches. This week’s highlights include the conviction of former Google engineer Linwei Ding for stealing AI trade secrets, Cloudflare reporting a record 31.4 Tbps DDoS attack, an LLM-assisted AWS admin takeover observed…
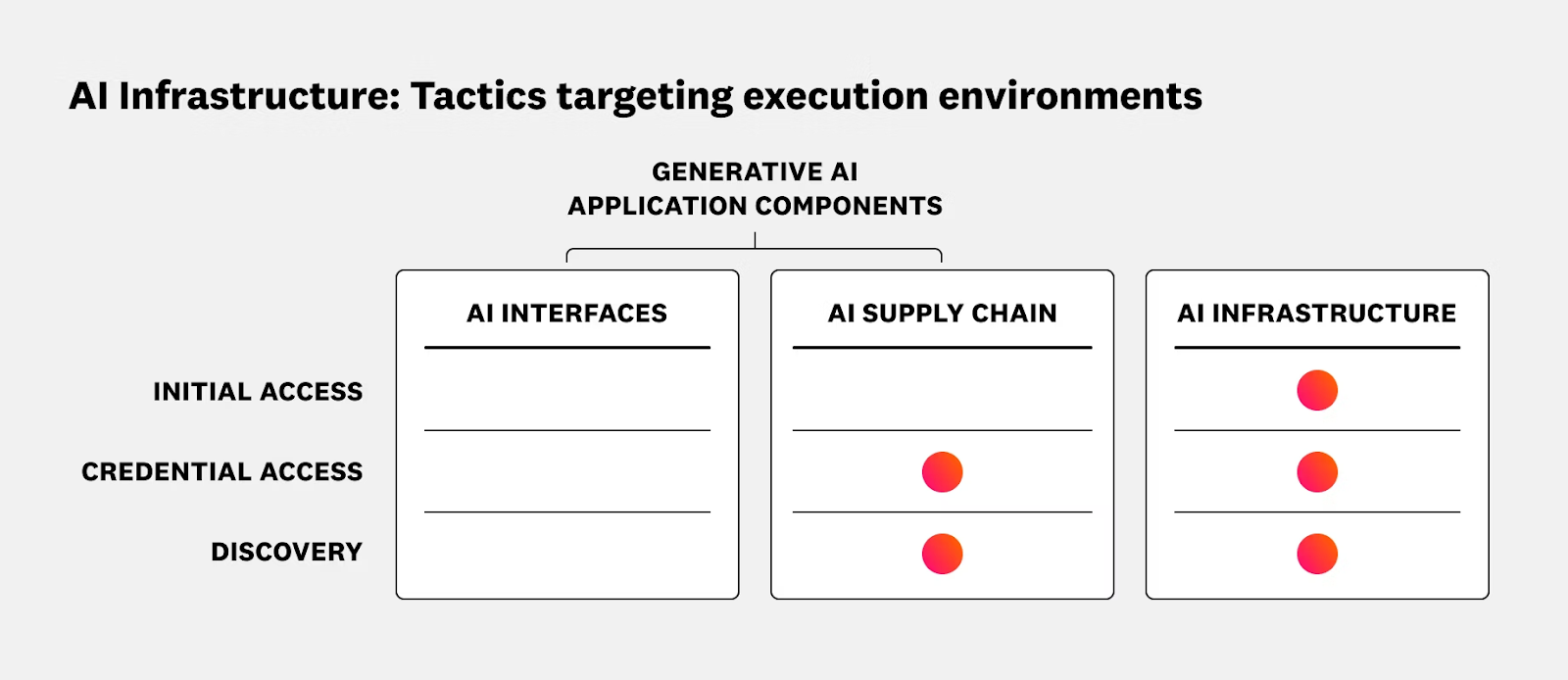
The article outlines security risks and operational best practices for running AI and ML workloads on Kubernetes and Oracle Cloud Infrastructure (OCI), emphasizing the shared responsibility model and the need to secure data planes, GPU nodes, inference services, and supply chains. It reviews recent AI-targeted incidents and promotes runtime protection, CI/CD hygiene, and integrated solutions such as Sysdig Secure with OKE to provide real-time detection and response. #ShadowRay2_0 #OCI

Black Basta operators (tracked as the group Cardinal) deployed a ransomware payload that uniquely bundled a vulnerable NsecSoft NSecKrnl kernel driver (CVE-2025-68947) to kill security processes and evade defenses, appending a “.locked” extension to encrypted files. The campaign also included a prior side-loaded loader and post-deployment presence of the GotoHTTP RAT, suggesting long dwell time or attempts to maintain persistence. #BlackBasta #Cardinal
Unit 42 attributes a large-scale, state-aligned cyberespionage campaign — tracked as TGR-STA-1030 and called the Shadow Campaigns — to an Asia-based actor that has compromised government and critical infrastructure across 37 countries using phishing, exploitation, C2 frameworks and a novel eBPF rootkit. The group used tools including Diaoyu Loader, Cobalt Strike,…
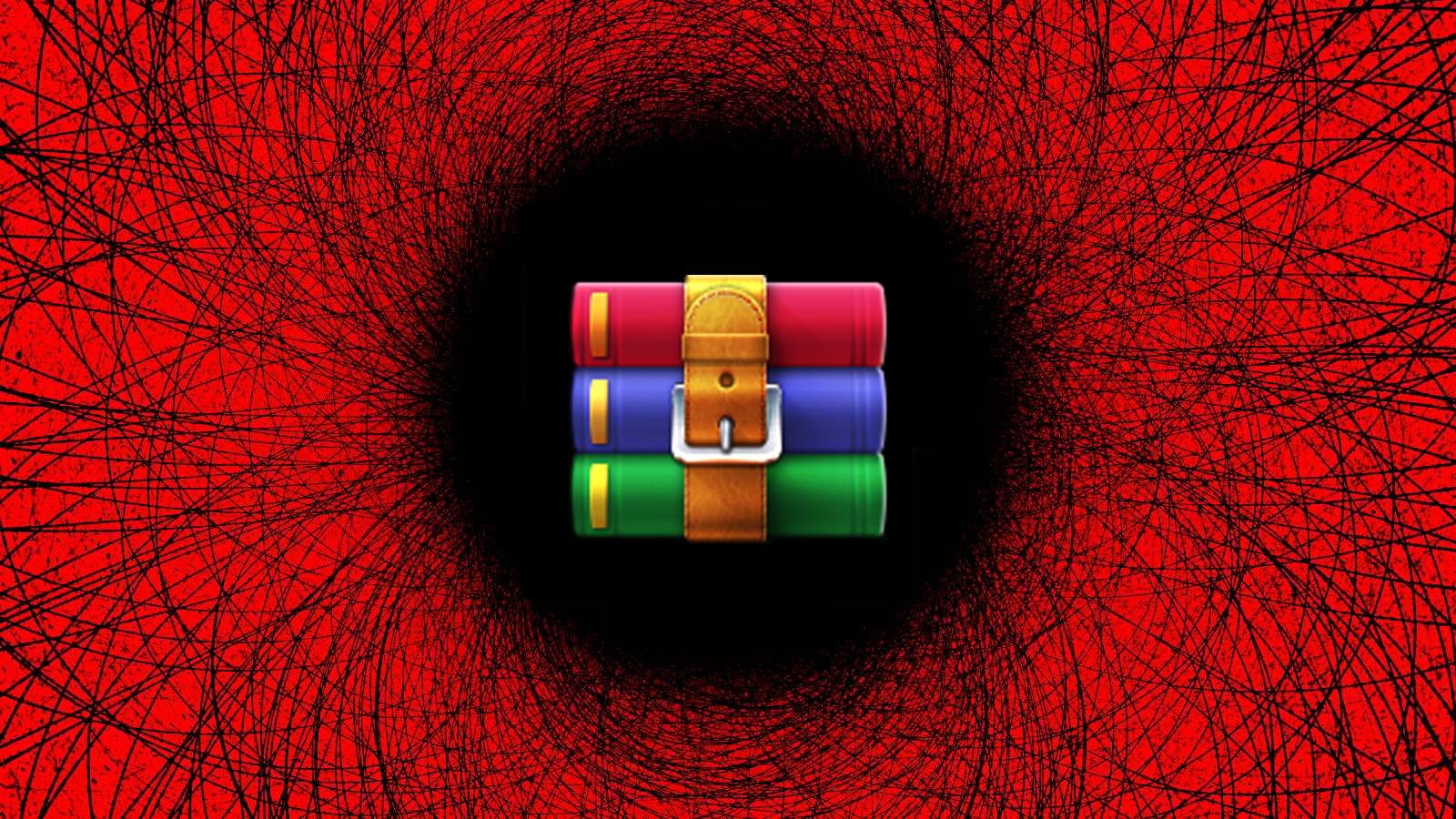
Amaranth Dragon, a threat actor linked to APT41, has been conducting espionage attacks against government and law enforcement organizations across Southeast Asia by exploiting the WinRAR path traversal flaw CVE-2025-8088. The group used legitimate tools alongside a custom Amaranth Loader and Cloudflare-backed C2 infrastructure to deliver encrypted payloads (including the Havoc framework and the TGAmaranth RAT), employ strict geofencing, and maintain stealth and persistence. #AmaranthDragon #CVE2025-8088 #WinRAR #TGAmaranthRAT

CISA confirmed that threat actors are exploiting a high-severity VMware ESXi sandbox escape tracked as CVE-2025-22225, which Broadcom patched in March 2025. Organizations are urged to apply vendor mitigations or follow BOD 22-01 guidance after CISA added the flaw to its Known Exploited Vulnerabilities list. #CVE-2025-22225 #VMwareESXi
![Cybersecurity News | Daily Recap [03 Feb 2026] Cybersecurity News | Daily Recap [03 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, attackers hijacked an OpenVSX publisher to push the GlassWorm macOS infostealer via malicious extension updates and Notepad++ update tampering, while researchers uncovered 341 ClawHub skills, OpenClaw one-click RCE from a critical token-exfiltration bug (CVE-2026-25253), and MoltBot used to push password-stealing malware across developer ecosystems. The Microsoft section notes APT28 exploiting CVE-2026-21509 to deploy the Covenant loader, NTLM is being phased out in favor of Kerberos, a Windows shutdown bug affects Windows 11 and 10 with a temporary workaround, ShinyHunters expanded extortion to vishing and MFA-credential harvesting alongside the PaneraBread breach, and destructive attacks on Polish energy sites via Fortinet devices, with Mozilla adding an AI controls panel in Firefox and policy moves toward stronger age verification and platform oversight. #GlassWorm #OpenVSX #Notepad++ #ClawHub #OpenClaw #MoltBot #AtomicStealer #CVE-2026-25253 #CVE-2026-21509 #APT28 #CovenantLoader #NTLM #Kerberos #PaneraBread #ShinyHunters #Sandworm #PolandGrid #Fortinet #Firefox #VirtualSecureMode

Ukraine’s CERT warns that Russian-linked APT28 is actively exploiting CVE-2026-21509 in multiple Microsoft Office versions using malicious DOC attachments to deploy the COVENANT loader. The exploit chain leverages WebDAV downloads, COM hijacking with EhStoreShell.dll, shellcode embedded in an image, and a scheduled task, and defenders are advised to apply Microsoft’s out-of-band Office updates or registry mitigations and monitor/block Filen C2 traffic. #CVE-2026-21509 #APT28

SecurityWeek’s Cyber Insights 2026 warns that agentic AI will increasingly automate and accelerate the entire cyberattack lifecycle, enabling one-click, adaptive, and highly targeted intrusions that blur the line between code and conversation. Organizations must double down on foundational cyber hygiene and adopt behavioral, AI-aware defenses to detect and remediate automated, identity-led,…

Poland’s CERT reported a Russia-linked attack on the national power grid that compromised communication and control systems at about 30 sites, allowing attackers to access ICS, upload malicious firmware, deploy wipers, and permanently damage some devices without causing electrical outages. The initial vector was internet-exposed Fortinet FortiGate devices using default credentials,…
