Anthropic’s new AI model, Mythos, is changing vulnerability management by identifying security flaws in hours or days and uncovering thousands of sensitive defects across every major operating system and web browser. It can generate precise exploits and chain vulnerabilities at machine speed—making traditional patching windows obsolete and threatening critical infrastructure, so defenders must move to continuous, real-time defenses #Mythos #PowerGrid
Category: Interesting Stuff

This issue of The Cybersecurity Pulse summarizes major supply-chain and data-exfiltration incidents—most notably Lapsus$ dumping a 96GB archive from Checkmarx via credentials stolen in the TeamPCP/Trivy compromise—and covers new AI-driven security tooling and vendor developments from Google, Wiz, and Amazon. It also highlights critical vulnerabilities and breaches, including the Copy Fail Linux LPE, ShinyHunters’ claims on Medtronic and Carnival, and insurer data showing misconfigured MFA as a significant loss driver. #Lapsus #Checkmarx

This article demonstrates how impacket-net uses three authentication paths—NTLM hash (Pass-the-Hash), Kerberos tickets, and AES keys—to enumerate and modify Active Directory objects against a domain controller in the ignite.local lab. It details user, group, computer, and local group operations, attacker persistence techniques, and mitigation strategies such as disabling machine account creation and monitoring directory change events. #impacket-net #ignite.local

This article documents sixteen techniques and tools for enumerating Active Directory users across LDAP, SAMR, RPC, LSARPC, and native Windows APIs, demonstrating commands and outputs against the ignite.local lab domain as the low-privileged user raj. It provides a comprehensive reference for offensive tradecraft while advising defenders on detection and mitigation strategies to harden and monitor Active Directory environments. #Impacket #BloodHound

This article presents a focused GRC study roadmap to replace aimless learning with a clear plan that covers cybersecurity fundamentals, GRC basics, and practical application. It outlines prioritized topics, exercises, and an offer for personalized guidance if you comment your target role and current level. #DecodedSecurity #CISSP

The article argues that the browser has evolved into a secondary operating system where compute, storage, identity, I/O, and communication converge, creating an opaque layer traditional security tools cannot fully observe. That blind spot breaks the assumption that authenticated sessions equal human agency, so detection and governance must move into the browser itself to prevent attacks like ClickFix and provide meaningful context. #KeepAware #ClickFix
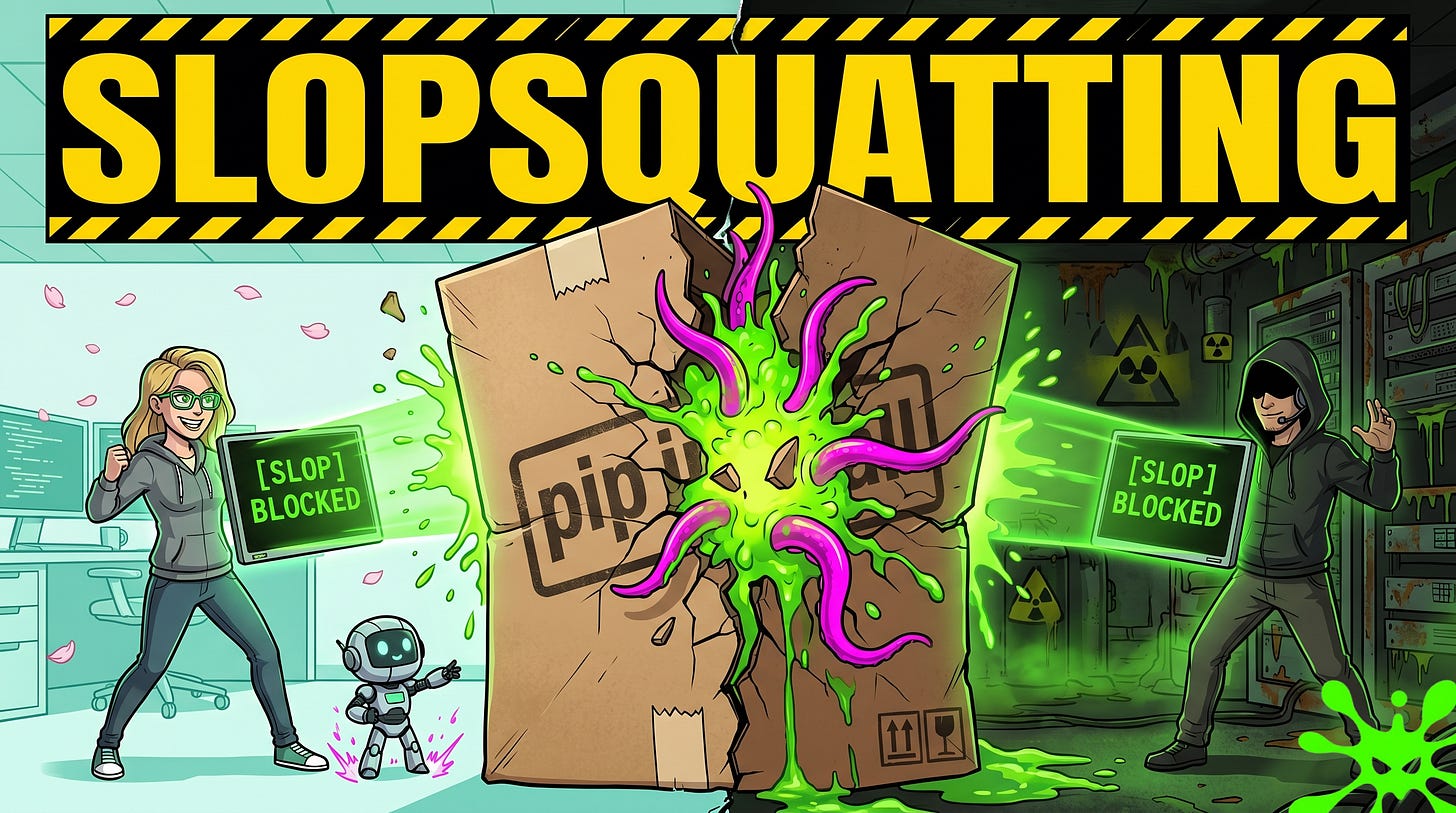
AI coding assistants often suggest plausible-sounding packages that do not exist, and attackers pre-register those hallucinated names on PyPI and npm to deliver malicious install hooks when developers copy-paste install commands. Research shows nearly 20% of AI-generated code references fake packages and 43% of hallucinations repeat across runs, and slopcheck stops nonexistent or suspicious packages at the install boundary. #Slopsquatting #slopcheck

Government impersonation scams have evolved into a large, highly coordinated global fraud ecosystem that exploits public trust in official institutions. CTM360’s GovTrap research shows attackers replicate entire government service environments across thousands of disposable domains and use multi-channel distribution to harvest credentials and payment data #GovTrap #CTM360

EVENmonitor streams Domain Controller Security logs in real time and decodes Windows events to reveal Active Directory attacks the moment they occur. This guide maps common AD attack techniques to their definitive Windows Event IDs, provides example commands and distinguishing forensic fields for detecting DCSync, AS‑REP Roasting, password spraying, Pass‑the‑Hash, Kerberoasting, privilege manipulation, and account lifecycle abuse #EVENmonitor #ActiveDirectory

This briefing summarizes major 2026 developments in cybersecurity and data governance, including ENISA’s new Technology and Innovation Radar methodology, EU–US biometric-sharing talks, multiple state and national AI and privacy laws, and updated guidance from national DPAs and the NCSC. It also highlights a tactical shift in China-linked cyber operations toward large covert networks of compromised devices exemplified by Raptor Train and noted campaigns like Volt Typhoon, raising detection and attribution challenges. #RaptorTrain #VoltTyphoon
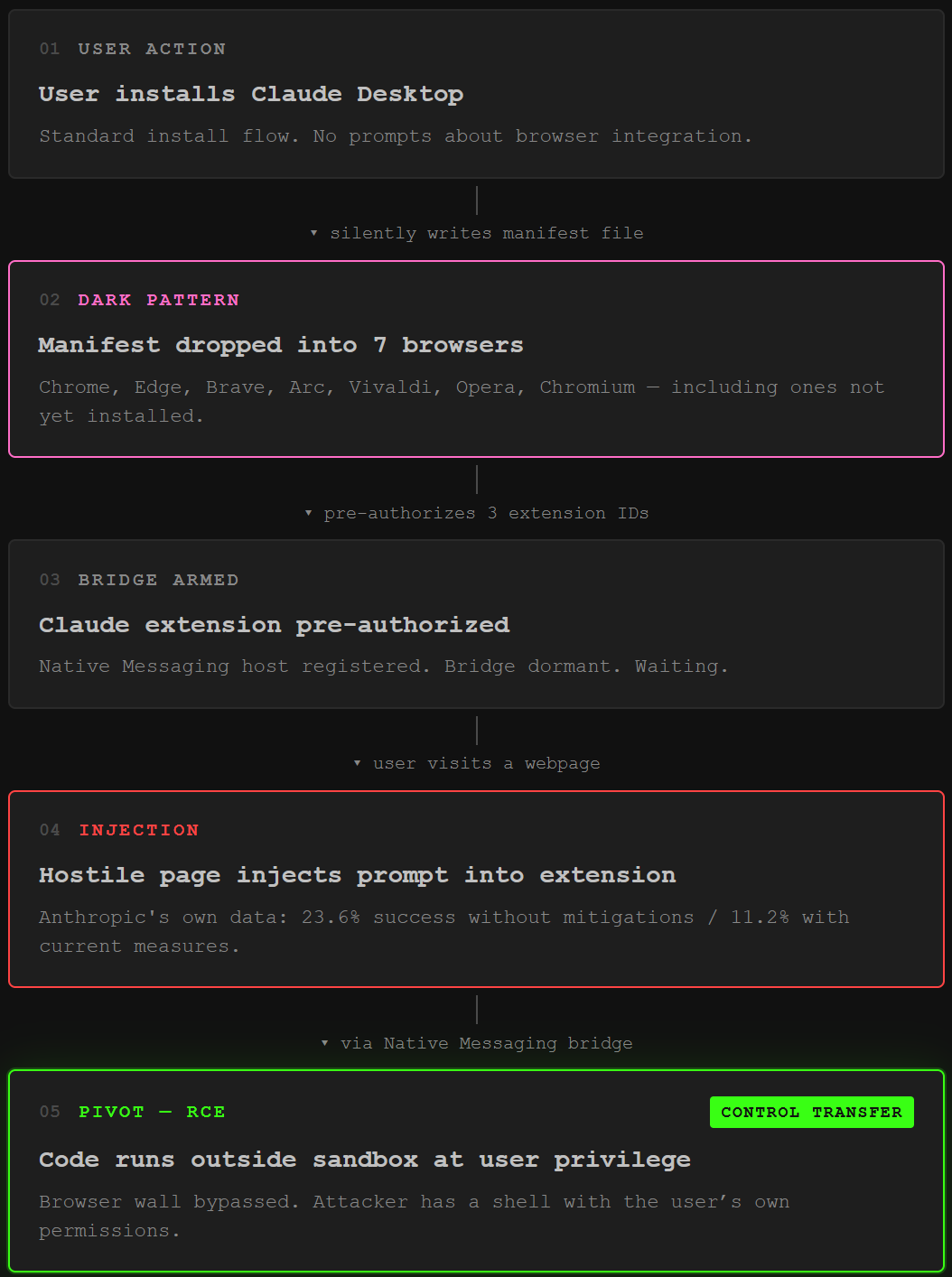
Anthropic’s week of incidents shows a recurring pattern: Claude Desktop silently installs a Native Messaging manifest into seven Chromium-based browser profiles, pre-authorizing extension IDs, while the MCP STDIO design and a predictable Mythos URL exposed critical supply-chain and access risks. Though no mass data exfiltration has been proven, the pre-positioned bridge and protocol design enable downstream prompt-injection and remote command execution scenarios that security researchers call a dangerous dark pattern and an architectural flaw. #ClaudeDesktop #ModelContextProtocol

This article demonstrates a full GPO-abuse attack chain in the ignite.local lab where a low-privilege user with delegated edit rights on a domain-linked GPO is used to push malicious scheduled tasks and scripts to reach the Domain Controller. Using BloodHound to discover writable GPOs and tools like pyGPOAbuse, SharpGPOAbuse, and StandIn, the attacker creates persistent local administrators and interactive reverse shells, while defenders are advised to treat GPO write access as Tier 0 and monitor SYSVOL/LDAP for tampering. #pyGPOAbuse #SharpGPOAbuse

Anthropic’s Claude Opus 4.7 introduced a new tokenizer that increased token counts by roughly 1.0–1.35× (and higher in the wild), changing how inputs are sliced and triggering pricing and compatibility concerns. The change also creates fresh untrained “glitch” tokens and a widened attack surface for token-level filter bypasses, special-token smuggling, and classifier desyncs, with no comprehensive sweep of the new vocabulary yet. #ClaudeOpus4.7 #SolidGoldMagikarp
Darwin Salazar’s The Cybersecurity Pulse covers this week’s major security events, including the Vercel OAuth-based compromise that led to Lumma Stealer token abuse, Anthropic Mythos access allegations, Lovable’s BOLA exposure, and three Microsoft Defender zero-days. It also highlights acquisitions and AI security startup launches, offers practical detection guidance for OpenAI Enterprise audit logs, and promotes webinars and events for security operators. #Vercel #LummaStealer

Security firm Fingerprint discovered a vulnerability in Firefox that allowed websites to track users by exploiting uniquely ordered retrieval of non-sensitive database metadata, enabling fingerprinting even in private browsing and the Tor browser. Mozilla patched the issue in Firefox 150 on April 21, 2026 after Fingerprint’s responsible disclosure, and researchers warn similar entropy-related flaws may surface as new AI models like Anthropic’s Claude Mythos emerge. #Firefox150 #Fingerprint
