Anthropic’s week of incidents shows a recurring pattern: Claude Desktop silently installs a Native Messaging manifest into seven Chromium-based browser profiles, pre-authorizing extension IDs, while the MCP STDIO design and a predictable Mythos URL exposed critical supply-chain and access risks. Though no mass data exfiltration has been proven, the pre-positioned bridge and protocol design enable downstream prompt-injection and remote command execution scenarios that security researchers call a dangerous dark pattern and an architectural flaw. #ClaudeDesktop #ModelContextProtocol
Keypoints
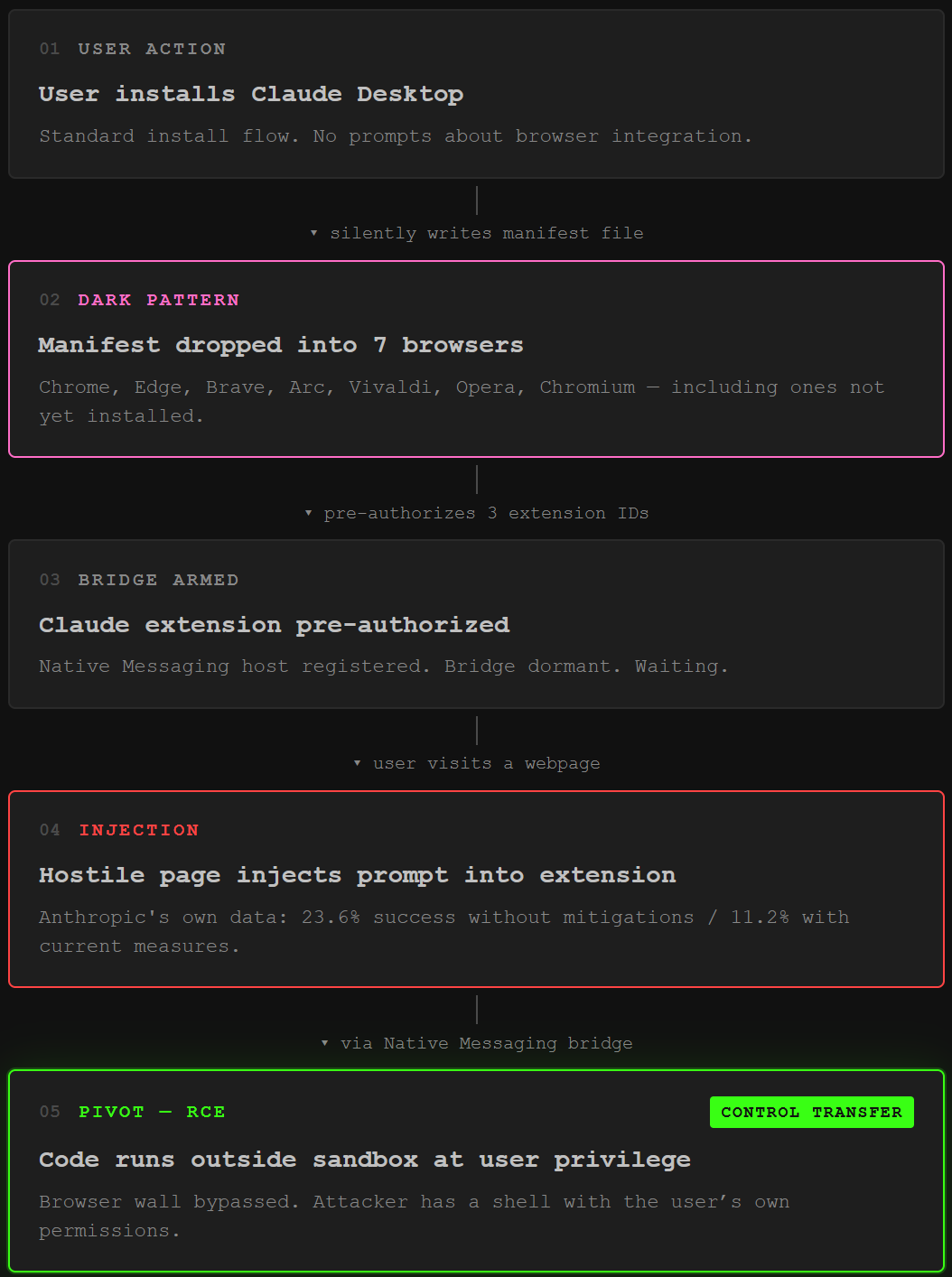
- Claude Desktop silently writes a Native Messaging manifest into Chrome, Edge, Brave, Arc, Vivaldi, Opera, and Chromium profile directories on macOS.
- The manifest pre-authorizes specific Claude extension IDs to connectNative to a local helper, creating a sandbox bypass that can be activated by a malicious extension or prompt injection.
- Anthropic’s Model Context Protocol (MCP) STDIO transport can be abused for arbitrary command execution, impacting multiple SDKs and potentially ~200,000 vulnerable instances.
- An unreleased Mythos model became accessible after a vendor breach and predictable URL patterns, allowing a Discord group to use it for a month without internal detection.
- Anthropic has characterized these behaviors as expected and declined protocol-level fixes, leaving defenders to harden individual implementations while researchers label the pattern a dangerous dark pattern.