A Russian-speaking threat actor used multiple generative AI services to breach more than 600 FortiGate firewalls across 55 countries in five weeks by targeting exposed management interfaces and weak credentials rather than exploiting zero-days. The campaign leveraged AI-assisted tooling (including a custom MCP server and LLMs) to automate reconnaissance, lateral movement, and attacks against backup infrastructure like Veeam, prompting recommendations to close exposed interfaces, enable MFA, and harden backups. #FortiGate #Veeam
Tag: ZERO-DAY

Intellexa’s Predator spyware can suppress iOS recording indicators to secretly stream camera and microphone feeds from infected devices. Jamf’s analysis shows Predator hooks SpringBoard’s sensor update path (HiddenDot::setupHook) to nullify SBSensorActivityDataProvider and prevent the green/orange dots from appearing, while using ARM64 pattern matching and PAC redirection to enable camera access. #Predator #Intellexa

A critical stack-based buffer overflow in Grandstream GXP1600 phones (CVE-2026-2329) can allow unauthenticated attackers to execute code as root and intercept calls. Rapid7 reported the flaw and Grandstream issued a firmware patch (1.0.7.81), though exploitation requires skill. #Grandstream #CVE2026-2329…

Attackers are actively exploiting CVE-2026-1731 in BeyondTrust Remote Support and Privileged Remote Access, enabling pre-authentication remote code execution via an OS command injection. CISA added the flaw to its KEV on Feb 13 with a three-day federal patch deadline; SaaS instances were auto-patched while self-hosted users must apply updates (RS 25.3.2, PRA 25.1.1+). #CVE-2026-1731 #BeyondTrust

CISA updated its Known Exploited Vulnerabilities catalog to flag CVE-2026-1731 — a critical unauthenticated remote code execution flaw in BeyondTrust Remote Support and Privileged Remote Access — after a public proof‑of‑concept led to in‑the‑wild exploitation and use in ransomware campaigns. Security firms and trackers including Palo Alto Networks, SecureCyber, and GreyNoise…
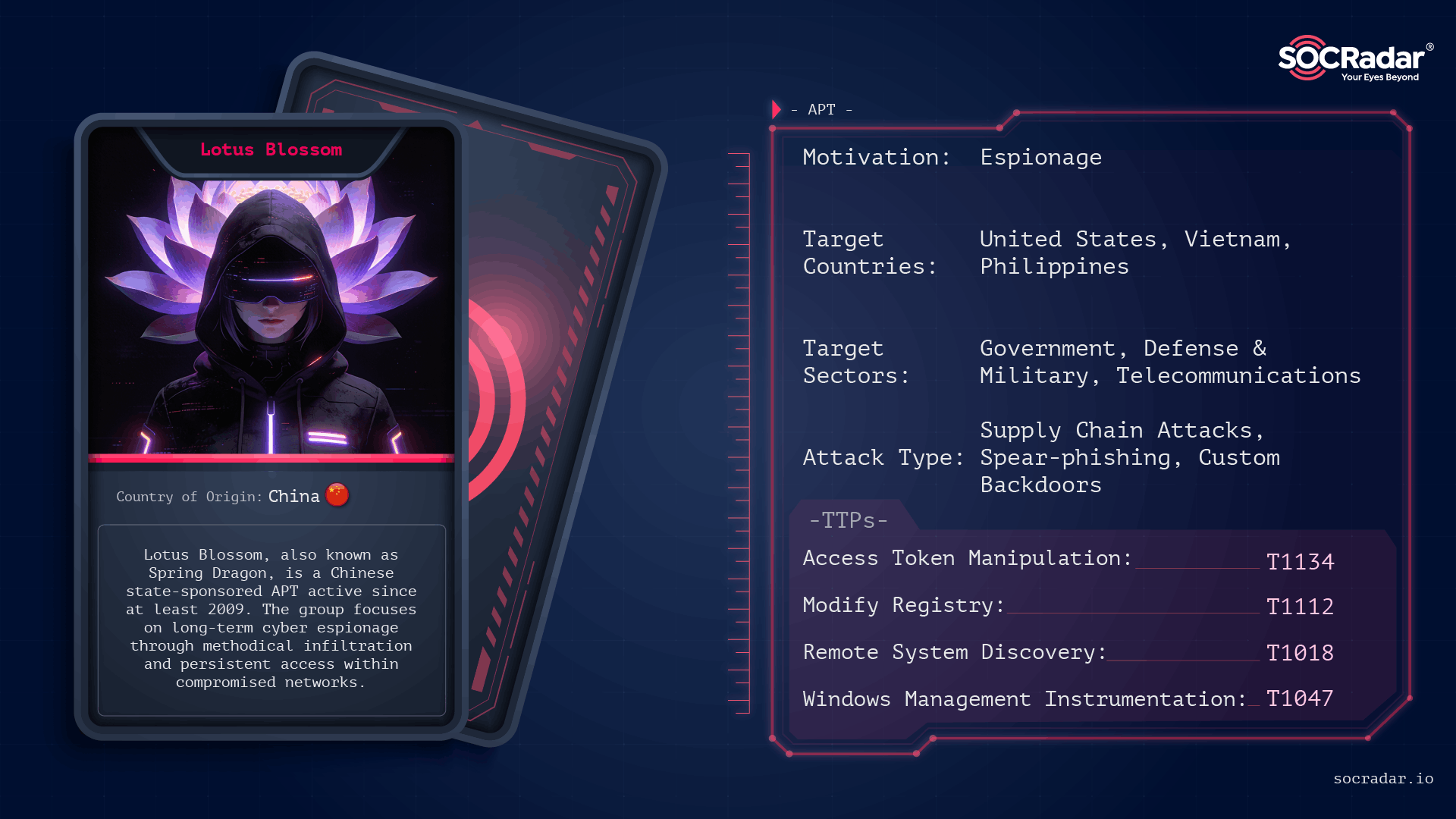
Lotus Blossom is a long-running, China-attributed APT that evolved from spear-phishing and watering-hole campaigns into sophisticated supply-chain compromises and targeted espionage using custom implants like Elise, Sagerunex, Hannotog, and Chrysalis. The group’s Notepad++ update-channel compromise and prior attacks against diplomatic, military, and maritime infrastructure demonstrate a “low-and-slow” intelligence collection approach emphasizing DLL sideloading, living-off-the-land techniques, and clandestine persistence. #LotusBlossom #Chrysalis

CISA ordered federal agencies to patch a maximum-severity hardcoded-credential vulnerability in Dell RecoverPoint (CVE-2026-22769) within three days after researchers found it has been actively exploited since mid-2024. Security firms attribute the exploitation to suspected Chinese threat cluster UNC6201, which has used the flaw for lateral movement and to deploy payloads including SLAYSTYLE, BRICKSTORM, and a new hard-to-analyze backdoor named GRIMBOLT. #UNC6201 #GRIMBOLT
![Cybersecurity News | Daily Recap [18 Feb 2026] Cybersecurity News | Daily Recap [18 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, the latest cyber threats cover exploited zero-days like Dell RecoverPoint CVE-2026-22769 used by UNC6201 to deploy GRIMBOLT/SLAYSTYLE with Ghost NICs, and a spectrum of high-impact flaws, supply-chain breaches, and targeted espionage campaigns. The recap also notes active exploitation of TeamT5 CVE-2024-7694, Ivanti EPMM backdoors bypassing patches, Keenadu firmware backdoors, CrescentHarvest espionage, and AI/Cloud risks including Copilot as C2 and Grok deepfakes, plus notable data leaks and enforcement actions. #UNC6201 #GRIMBOLT #SLAYSTYLE #DellRecoverPoint #TeamT5 #IvantiEPMM #Keenadu #CRESCENTHARVEST #Copilot #Grok #Eurail #Cellebrite #DavaIndia #Notepad++ #Chrysalis #PaloAltoNetworks #Koi #VulnCheck

A Chinese state-backed hacking group has been exploiting a critical zero-day in Dell RecoverPoint for Virtual Machines (CVE-2026-22769) since at least mid-2024 to deploy backdoors and target organizations across North America. Dell, Google/Mandiant and U.S. agencies have issued advisories and fixes, and CISA ordered immediate federal patching while researchers report use…

CISA warned that a vulnerability in TeamT5’s ThreatSonar Anti-Ransomware (CVE-2024-7694) has been exploited in the wild and was added to the Known Exploited Vulnerabilities catalog. The high-severity arbitrary file-upload flaw was patched in August 2024, but CISA ordered federal agencies to remediate it by March 10 due to the product’s use…

A critical zero-day, CVE-2026-22769, is being actively exploited in Dell RecoverPoint for Virtual Machines to enable unauthenticated attackers to gain root-level persistence via hardcoded Apache Tomcat credentials. Mandiant and GTIG attribute the campaign to Chinese cluster UNC6201, which has deployed SLAYSTYLE web shells and transitioned from BRICKSTORM to the AOT-compiled backdoor…
Two sentences summarizing the content. Threat actors quickly weaponized two Ivanti EPMM zero-days (CVE-2026-1281 and CVE-2026-1340) to achieve unauthenticated remote code execution via a bash arithmetic expansion trick, enabling rapid deployment of web shells and persistent backdoors. Over 4,400 internet-facing EPMM instances were identified across multiple sectors and countries, prompting CISA…
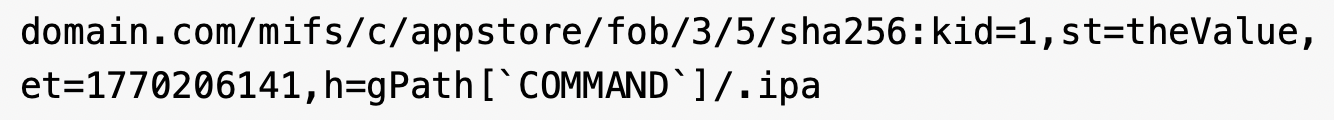
Two critical zero-day remote code execution vulnerabilities (CVE-2026-1281 and CVE-2026-1340) in Ivanti Endpoint Manager Mobile (EPMM) are being actively exploited to gain unauthenticated control of enterprise MDM infrastructure. Unit 42 documents automated mass scanning and exploitation leading to reverse shells, web shell installation, malware downloads (including the Nezha monitoring agent), and…
A high-risk zero-day vulnerability in Dell RecoverPoint for Virtual Machines (CVE-2026-22769) has been exploited since mid-2024 by a suspected PRC-nexus cluster tracked as UNC6201 to gain footholds in the virtualization layer and deploy backdoors. Researchers report UNC6201 upgraded its toolkit in September 2025 to include an AOT-compiled C# backdoor named GRIMBOLT…

A suspected Chinese state-backed group, UNC6201, has been exploiting a hardcoded-credential zero-day (CVE-2026-22769) in Dell RecoverPoint for Virtual Machines since mid-2024 to gain unauthenticated access and root persistence. The intruders deployed a new C# backdoor called Grimbolt (replacing Brickstorm) and used stealthy Ghost NICs on VMware ESXi to move laterally; Dell urges immediate remediation. #UNC6201 #Grimbolt
