State-sponsored APT activity originating in the Middle East focuses on long-term infiltration and intelligence collection using spear-phishing, malicious documents, and abuse of legitimate RMM tools. Defensive emphasis is placed on endpoint behavior-based EDR to detect post-execution activity and persistent misuse of legitimate administration platforms. #MuddyWater #Atera
Tag: THREAT INTELLIGENCE

A Russian-speaking, financially motivated actor used commercial generative AI to automate scanning and brute-force attacks against exposed FortiGate management interfaces, compromising over 600 devices in 55 countries. Amazon Threat Intelligence found the campaign leveraged multiple AI tools to scale credential harvesting, Active Directory compromise, and targeting of backup infrastructure consistent with…
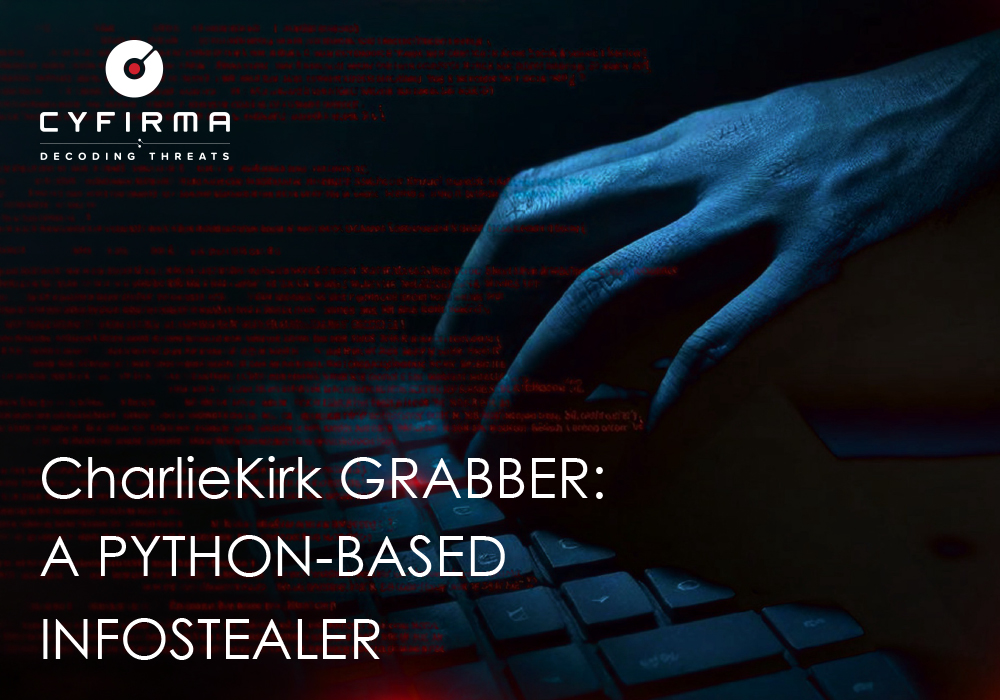
CharlieKirk Grabber is a Python-based Windows infostealer that performs rapid “smash-and-grab” credential harvesting, system reconnaissance, and immediate exfiltration using legitimate Windows utilities and multithreading to minimize runtime. It stages browser credentials, Discord tokens, Wi‑Fi and game session artifacts, compresses them, uploads the archive to GoFile, and sends the download link via Discord or Telegram for attacker retrieval. #CharlieKirk #GoFile

EC-Council Expands AI Certification Portfolio to Strengthen U.S. AI Workforce Readiness and Security
EC-Council launched the Enterprise AI Credential Suite with four new role-based AI certifications and an updated Certified CISO v4 to close the gap between rapid AI adoption and workforce readiness. The programs align to an Adopt.Defend.Govern framework and U.S. AI workforce priorities to reduce AI risk exposure and address significant reskilling…

CISA updated its Known Exploited Vulnerabilities catalog to flag CVE-2026-1731 — a critical unauthenticated remote code execution flaw in BeyondTrust Remote Support and Privileged Remote Access — after a public proof‑of‑concept led to in‑the‑wild exploitation and use in ransomware campaigns. Security firms and trackers including Palo Alto Networks, SecureCyber, and GreyNoise…

A newly observed Remcos RAT variant adds real-time surveillance—including live webcam streaming and online keylogging—and stronger evasion techniques that reduce forensic traces on Windows systems. Researchers at Point Wild’s Lat61 team report the strain fetches modular DLL plugins from C2 servers, decrypts configuration only in memory, resolves Windows APIs dynamically, and…
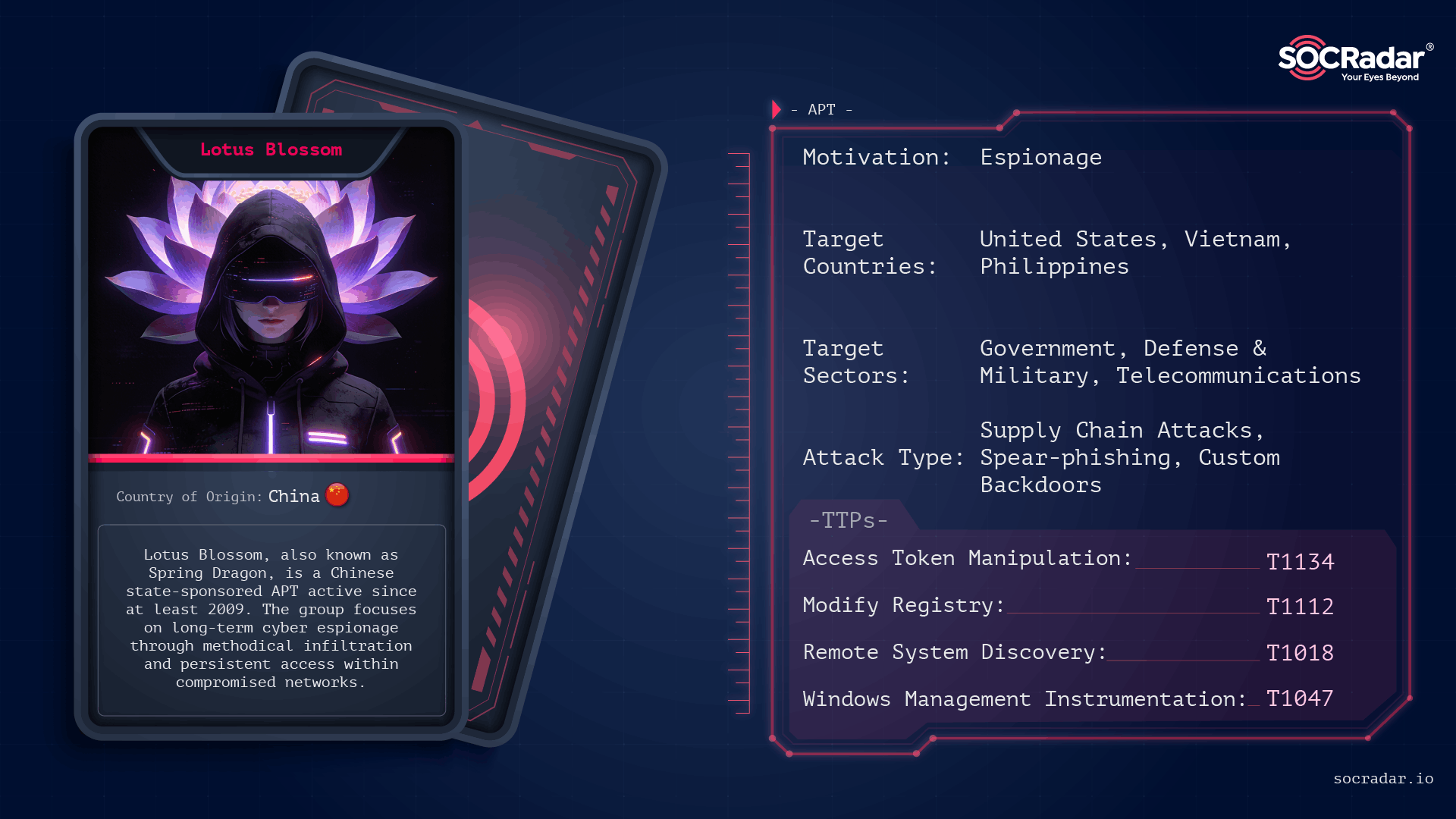
Lotus Blossom is a long-running, China-attributed APT that evolved from spear-phishing and watering-hole campaigns into sophisticated supply-chain compromises and targeted espionage using custom implants like Elise, Sagerunex, Hannotog, and Chrysalis. The group’s Notepad++ update-channel compromise and prior attacks against diplomatic, military, and maritime infrastructure demonstrate a “low-and-slow” intelligence collection approach emphasizing DLL sideloading, living-off-the-land techniques, and clandestine persistence. #LotusBlossom #Chrysalis
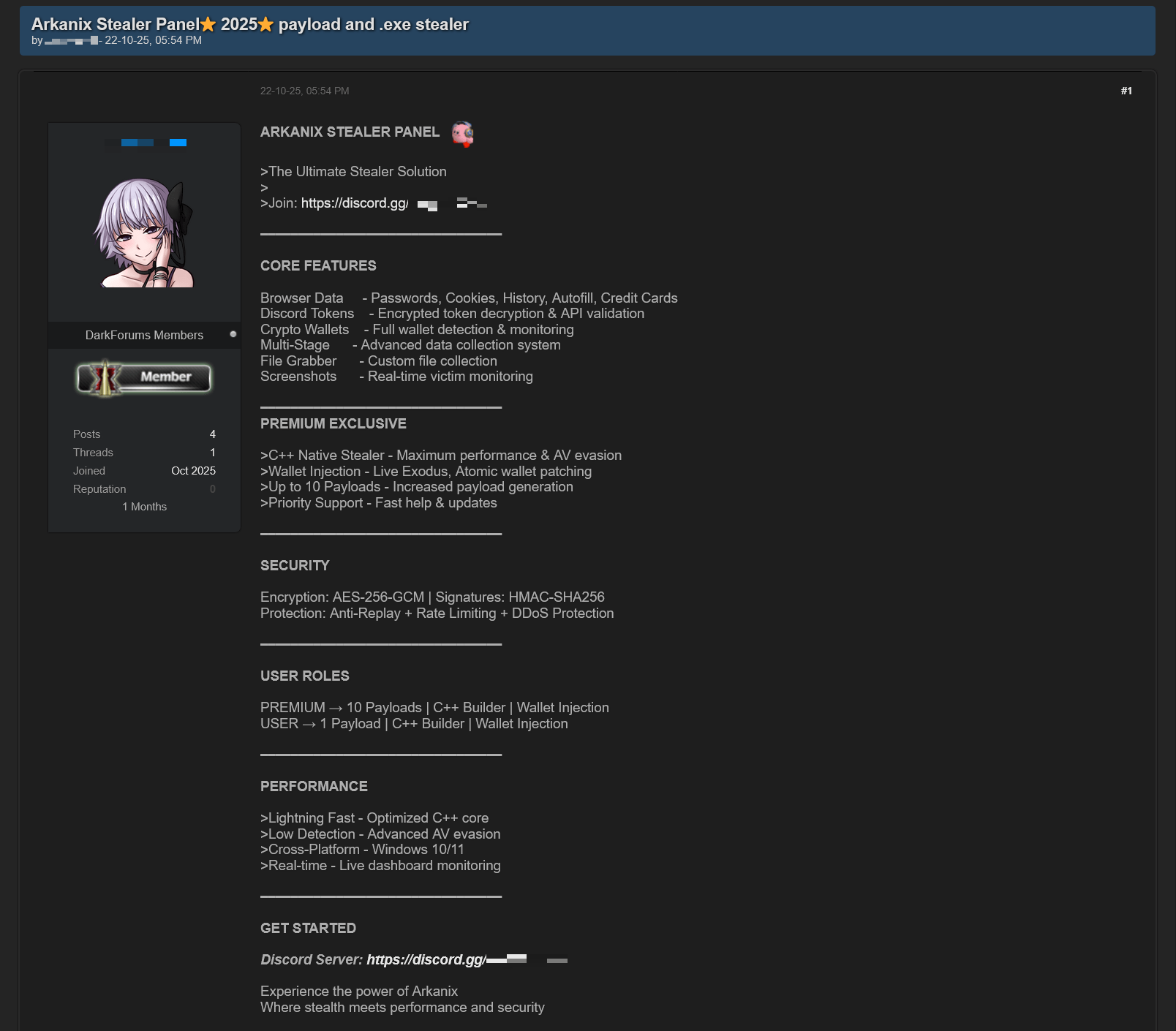
In October 2025 researchers discovered forum posts advertising a previously unknown MaaS called “Arkanix Stealer” offering both native C++ and Python implants, a configurable control panel, and payload generation. The malware harvested browser credentials, cryptocurrency wallets (using an embedded ChromElevator injector), system and application data, communicated with C2 endpoints on arkanix[.]pw, and the affiliate program and panel were subsequently taken down. #ArkanixStealer #ChromElevator
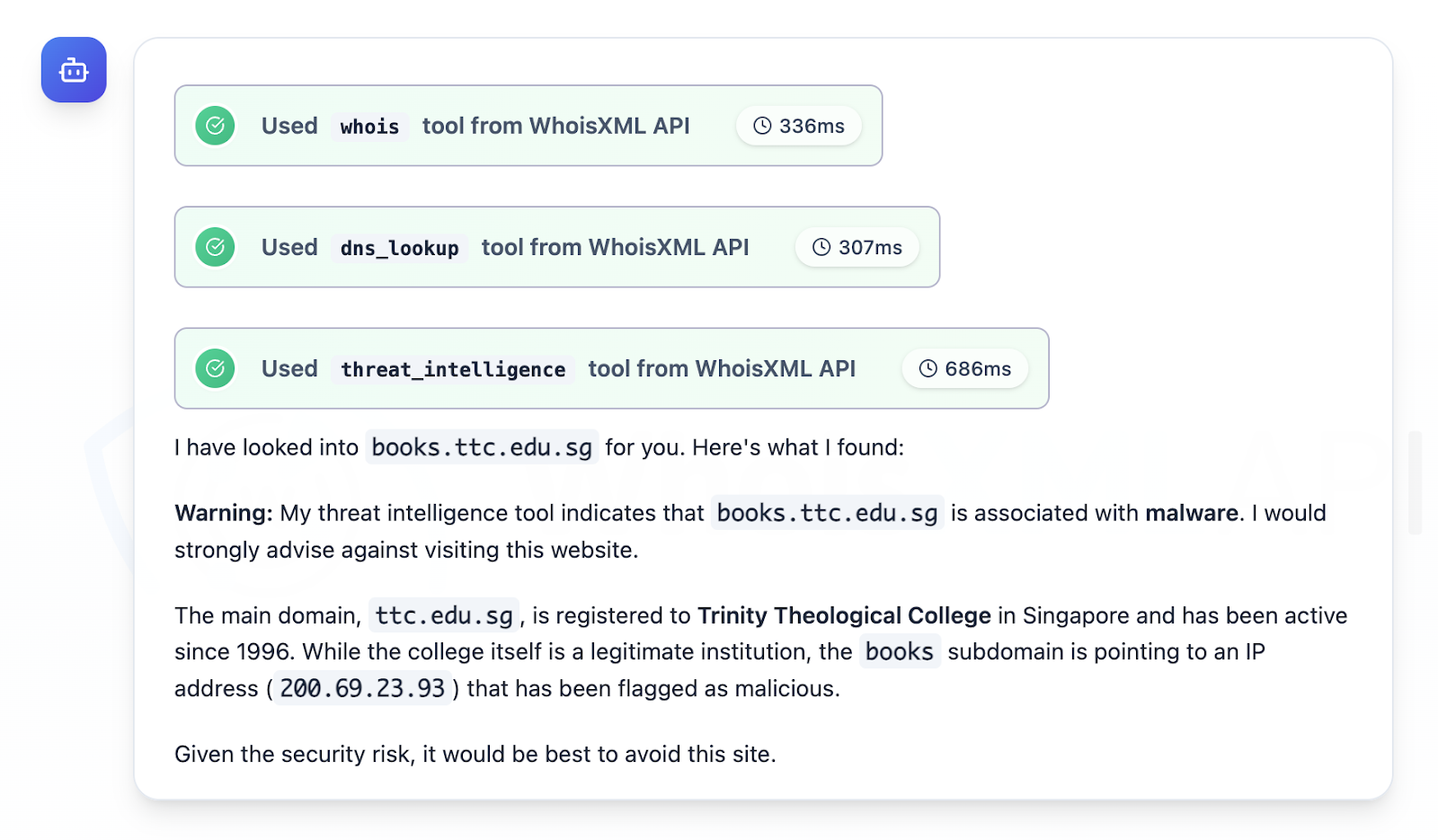
CloudSEK and follow-up research focused on QakBot as a top access trojan/loader that is commonly distributed via phishing, harvests credentials, maintains C2 access, delivers payloads, and moves laterally to enable targeted attacks and ransomware against email-reliant enterprises. The investigation analyzed Trellix IoCs (extracted 929 domains, filtered to 492, studied 125), 19 subdomains, multiple client and infrastructure IPs, and thousands of email-connected domains, identifying specific malicious artifacts (e.g., books[.]ttc[.]edu[.]sg -> 200[.]69[.]23[.]93) and providing a downloadable dataset for further hunting. #QakBot #Trellix
.jpg)
PromptSpy is the first known Android malware to integrate generative AI into its execution flow, using Google’s Gemini model to generate device-specific instructions that help it pin and persist in Recent Apps. The spyware also includes a VNC module for full remote access, can capture PINs and screen activity, and uses invisible overlays to block uninstallation. #PromptSpy #Gemini

CISA ordered federal agencies to patch a maximum-severity hardcoded-credential vulnerability in Dell RecoverPoint (CVE-2026-22769) within three days after researchers found it has been actively exploited since mid-2024. Security firms attribute the exploitation to suspected Chinese threat cluster UNC6201, which has used the flaw for lateral movement and to deploy payloads including SLAYSTYLE, BRICKSTORM, and a new hard-to-analyze backdoor named GRIMBOLT. #UNC6201 #GRIMBOLT

Researchers discovered a new Android banking malware named Massiv that disguises itself as an IPTV app to steal digital identities and access online banking accounts. In a campaign observed by ThreatFabric, Massiv targeted a Portuguese government app integrated with Chave Móvel Digital and uses screen overlays, keylogging, MediaProjection and Accessibility-based UI-tree control to bypass protections, open fraudulent accounts, and enable money laundering and account takeovers. #Massiv #ChaveMovelDigital

Security teams are overwhelmed by escalating attack volume and attacker throughput, making detection alone insufficient to prevent breaches. Operational Exposure Management — focusing on validated, reversible remediation — is required to shrink exposure dwell time and close the action gap. #ClickFix #Qilin

Attack Discovery, Workflows, and Agent Builder were combined to automatically detect, confirm, and triage a Chrysalis backdoor campaign delivered via a Notepad++ update supply-chain compromise, collapsing dozens of alerts into a single verified incident and creating a case and Slack channel with on-call responders already added. The automation verified C2, performed VirusTotal checks, ran ES|QL hunts, and executed incident actions (isolation, user suspension, IOC sweeps) in under four minutes instead of hours. #Chrysalis #LotusBlossom

A Chinese state-backed hacking group has been exploiting a critical zero-day in Dell RecoverPoint for Virtual Machines (CVE-2026-22769) since at least mid-2024 to deploy backdoors and target organizations across North America. Dell, Google/Mandiant and U.S. agencies have issued advisories and fixes, and CISA ordered immediate federal patching while researchers report use…