Arkanix Stealer, an information‑stealing operation promoted on dark web forums in late 2025, offered modular Python and premium C++ builds with VMProtect and extensive data‑theft capabilities across browsers, wallets, messengers, and gaming platforms. Kaspersky researchers found indicators of LLM‑assisted development, a short‑lived Discord community and referral program, and published IoCs while the operator abruptly took down the project two months after launch. #ArkanixStealer #Kaspersky
Tag: IOT

Multiple critical vulnerabilities (CVE-2026-25715, CVE-2026-24455, CVE-2026-26049, CVE-2026-26048) in the Jinan USR IOT PUSR USR-W610 (…
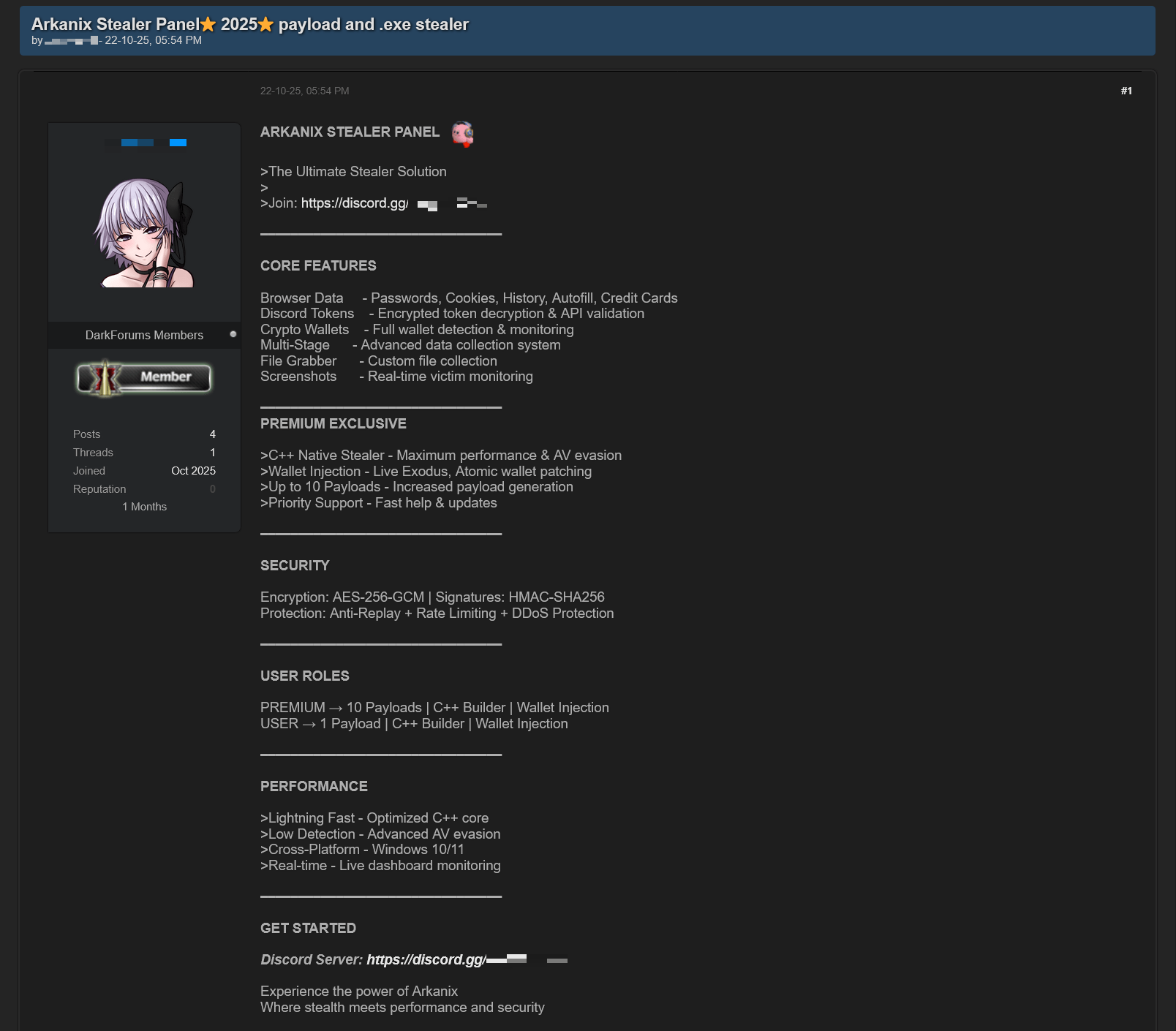
In October 2025 researchers discovered forum posts advertising a previously unknown MaaS called “Arkanix Stealer” offering both native C++ and Python implants, a configurable control panel, and payload generation. The malware harvested browser credentials, cryptocurrency wallets (using an embedded ChromElevator injector), system and application data, communicated with C2 endpoints on arkanix[.]pw, and the affiliate program and panel were subsequently taken down. #ArkanixStealer #ChromElevator

13 defacement incidents targeted websites in Brazil, the Philippines, Pakistan and Indonesia; attackers included spl1nt3r, Typical Idiot Security, Anonymous Davao Philippines, unknown_*3x and Maria. #Brazil #Philippines #Pakistan #Indonesia…
CVE-2026-1731 is a critical pre-authentication remote code execution vulnerability in BeyondTrust Remote Support’s thin-scc-wrapper WebSocket handler that Unit 42 has observed being actively exploited to deploy web shells, backdoors (including SparkRAT and VShell), create accounts, move laterally, and exfiltrate data across multiple sectors and countries. CISA added the vulnerability to its…

Industrial Control Systems (ICS) remain highly vulnerable because decades‑old hardware, outdated protocols, and operators’ inability to accept downtime prevent effective patching and replacement amid growing nation‑state pre‑positioning and ransomware pressure. To build long‑term resilience in 2026, experts recommend OT‑aware zero trust, identity‑centric controls, microsegmentation, continuous threat exposure management (CTEM), supply‑chain transparency,…

Attackers can bypass application whitelisting and executable restrictions by converting managed .NET assemblies into JScript loaders that execute in memory via Windows Script Host. The technique demonstrated uses DotNetToJScript to run x64 Meterpreter shellcode over HTTPS, blending into trusted components and evading binary-focused defenses. #DotNetToJScript #Meterpreter

Researchers uncovered DKnife, a Linux-based gateway-monitoring and adversary-in-the-middle framework used by China-nexus actors since at least 2019 to perform deep packet inspection, manipulate traffic, and deliver malware via compromised routers and edge devices. The modular toolkit hijacks binary and Android update downloads to deploy backdoors like ShadowPad and DarkNimbus and harvests…

US and UK agencies warned that discontinued edge devices — including firewalls, routers, switches, load balancers, IoT devices, and wireless access points — pose significant security risks because they no longer receive security updates. CISA’s Binding Operational Directive 26-02 requires federal agencies to inventory, update, and decommission end-of-support (EOS) edge devices…

CPQ Ingenieros reports a ransomware claim attributed to the threat actor thegentlemen, alleging that its networks have been encrypted and data may be exposed. This Spain-based firm, which designs process plants across chemical, pharmaceutical, biotechnological, food, and cosmetic industries, is assessing the impact on operations, clients, and compliance. #Spain
Researchers at Cisco Talos uncovered DKnife, an ELF-based post-compromise toolkit used since 2019 to hijack edge devices and perform deep packet inspection, traffic manipulation, and targeted malware delivery. The framework’s seven Linux components enable DNS and update hijacking, credential harvesting, and delivery of backdoors such as ShadowPad and DarkNimbus, and Talos attributes the activity to a China-nexus threat actor. #DKnife #ShadowPad

Ransomware operators are abusing virtual machines provisioned via ISPsystem’s VMmanager to host and deliver malicious payloads at scale, hiding C2 and distribution servers among legitimate infrastructure. Sophos found identical default Windows hostnames reused across multiple criminal campaigns — including WantToCry, LockBit, Qilin, Conti, BlackCat/ALPHV, and Ursnif — enabling evasion and complicating takedowns. #WantToCry #VMmanager

CISA has ordered federal civilian agencies to remove end-of-life hardware and software from networks within 12 months after warning that unsupported edge devices are being widely exploited by sophisticated threat actors. Agencies must inventory listed devices within three months, decommission them within a year, implement continuous discovery within two years, and…
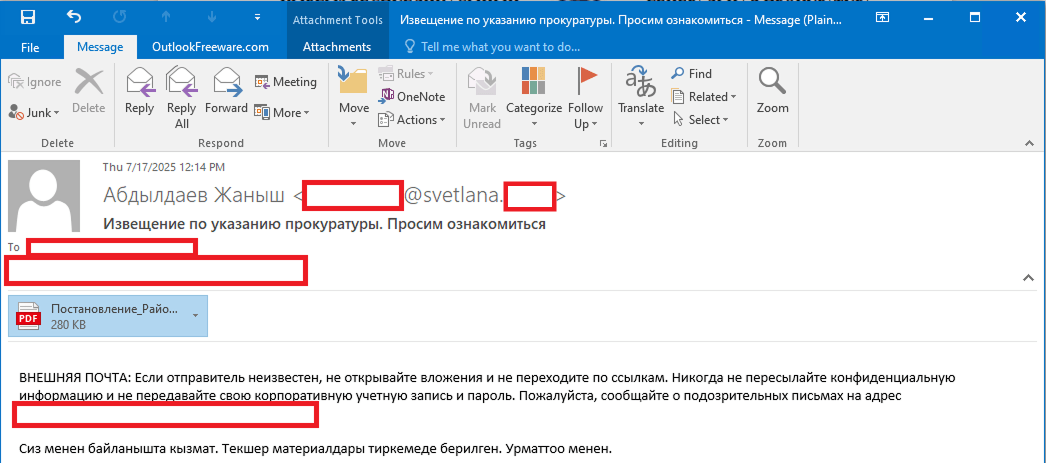
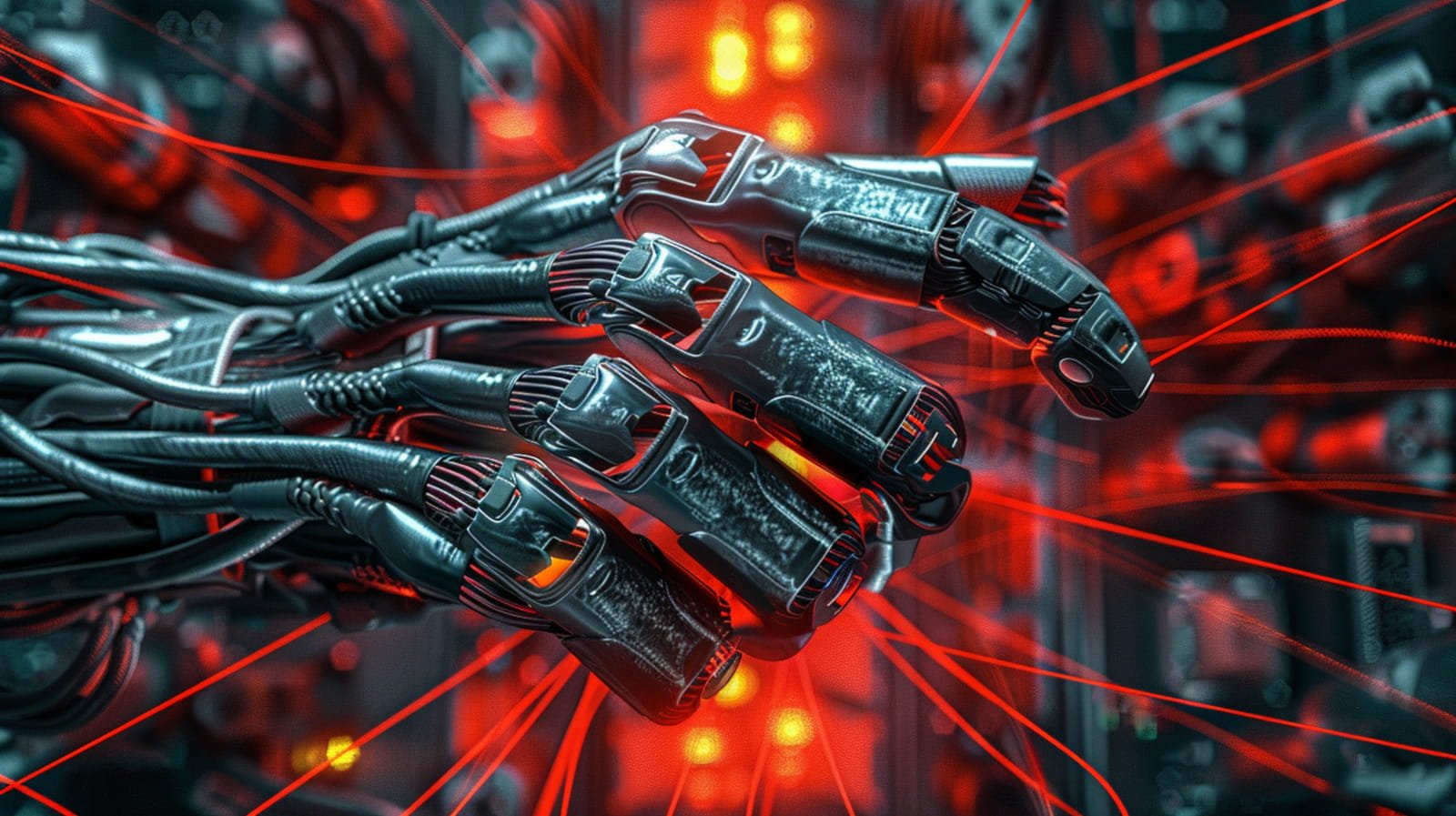
Stan Ghouls (aka Bloody Wolf) ran a targeted campaign primarily against organizations in Uzbekistan (and collateral victims in Russia, Kazakhstan, Turkey, Serbia, and Belarus) using spear-phishing PDFs that link to a Java-based loader which installs NetSupport remote management components. Investigators found roughly 50 victims in Uzbekistan, multiple new domains and a JAR/loader MD5 tied to the campaign, and discovered Mirai IoT binaries on a domain related to the threat infrastructure. #StanGhouls #NetSupport

There were 5 defacement incidents targeting websites in the Dominican Republic and Indonesia. The attackers involved were Typical Idiot Security, L4663R666H05T, and Maria. #DominicanRepublic #Indonesia…
