Check Point Research’s Cyber Security Report 2026 synthesizes findings from 2025 showing AI is embedded across the attack lifecycle, accelerating reconnaissance, social engineering, and malware development while introducing new governance risks. The report also highlights fragmented, data-only ransomware extortion, exploitation of unmonitored edge and perimeter devices, geopolitically aligned cyber activity, and measurable vulnerabilities in Model Context Protocols and ungoverned AI usage. #ModelContextProtocols #UnmonitoredDevices
Tag: GOVERNANCE
![Cybersecurity News | Daily Recap [27 Jan 2026] Cybersecurity News | Daily Recap [27 Jan 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, emergency fixes have been issued for Microsoft’s Office zero-day CVE-2026-21509 and a critical VMware vCenter DCERPC flaw (CVE-2024-37079) that attackers are already exploiting, with patches and mitigations urging rapid remediation. The roundup also highlights Dormakaba Exos flaws enabling remote door access, the Stanley malware-as-a-service for Chrome extensions, the Amatera infostealer via in-memory PowerShell with the ClickFix method, extortion-linked data breaches at Nike and by ShinyHunters, a Sandworm-linked DynoWiper attempt against Poland’s power grid, a Cloudflare BGP leak, and regulatory actions around Grok, AI privacy and platform governance. #OfficeZeroDay #CVE-2026-21509 #VMwareVCenter #CVE-2024-37079 #DormakabaExos #StanleyService #Amatera #DynoWiper #Sandworm #PolandPowerGrid #Nike #WorldLeaks #ShinyHunters #Cloudflare #BGPLeak #Grok #X

Black Duck’s “The Global State of DevSecOps: Balancing AI Usage and Risk in 2025” finds that organizations have achieved high deployment velocity but are accumulating security debt because of manual processes, tool sprawl, and overwhelming false positives that slow development. The report also describes AI as a double-edged sword—widely adopted and improving secure coding for many, yet introducing new risks and shadow-AI governance gaps that demand developer-centric workflow integration and formal AI governance. #BlackDuck #GitHubCopilot

AI agents are being embedded into regulated workflows and act autonomously in ways that undermine compliance controls designed for human actors. As agents drift, hold broad permissions, and produce opaque decisions, CISOs increasingly bear responsibility for identity, access, logging, and demonstrating continuous compliance. #SOX #GDPR

Relying on fully autonomous AI defenses creates a risky closed loop where poor data, model drift, and lack of oversight can produce systemic failure. To stay resilient against accelerating AI-enabled threats, organizations must pair human judgment with transparent governance, auditable models, and human-in-the-loop controls. #UnitedNationsScientificAdvisoryBoard #HumanInTheLoop…

Offensive security and red teaming are shifting from periodic exercises to continuous, AI-augmented programs that combine automation, threat intelligence, and human expertise to find and fix vulnerabilities faster. This evolution includes hybrid in-house and external models, greater collaboration with blue teams, and an urgent focus on combating AI-enhanced social engineering. #Bugcrowd…
The American Hospital Association has released two guides—Strategies for Medical Surge Management During Public Emergencies and Strategies for Cyber Preparedness in Health Care—to help U.S. hospitals strengthen preparedness, support staff, and sustain care during crises. The guidance centers on the “four S’s” (staffing, supply, space, systems) and offers practical measures such…

Comcast Business’s 2025 Threat Report analyzes 34.6 billion events (including 19.5B botnet resource-development events, 9.7B drive-by compromises, 4.7B phishing attempts, and 44,069 DDoS events) to map evolving attacker tactics such as proxy abuse, living-off-the-land techniques, and AI-enabled social engineering. It urges organizations to adopt multi-layered, AI-augmented defenses—prioritizing patching, phishing-resistant MFA, proactive threat hunting, and managed 24/7 SOC services—to reduce exposure and build enterprise resilience. #SocGholish #ComcastBusiness

SecurityWeek’s Cyber Insights 2026 gathers expert views warning that powerful quantum computers threaten current public-key encryption and that AI could accelerate quantum development and automate its use. The report urges urgent migration to post-quantum cryptography and preparation for a potential convergence of quantum computing and AGI that could enable fast, autonomous…

The European Commission has opened a formal investigation under the Digital Services Act into X over its AI chatbot Grok, amid allegations that Grok’s image-generation and recommender features exposed EU users to manipulated sexually explicit images and possible CSAM. The probe, which extends earlier December 2023 proceedings, will examine whether X…

Varonis Threat Labs discovered a stealthy data-exfiltration technique called Exfil Out&Look that abuses Outlook add-ins—especially those installed via Outlook Web Access (OWA)—to silently capture and transmit outgoing email content without generating Microsoft 365 audit logs. The PoC shows minimally-permissioned add-ins can hook the OnMessageSend/ItemSend event to send email contents to external…

OT incidents rarely begin with targeted process attacks; they arise from common enterprise weaknesses—shared credentials, permissive remote management, weak IT–OT boundaries, and limited operational visibility—that allow IT compromises to become OT outages. Treating recovery and containment as security controls (locking down management planes, extending detection into OT-adjacent systems, and ensuring tamper‑resistant backups) is the decisive factor in limiting operational impact. #Sygnia #JumpServers

CISOs are shifting 2026 cybersecurity budgets from reactive, optimization-driven strategies toward growth-focused, precision investments that prioritize measurable risk reduction and operational efficiency. Adversarial Exposure Validation (AEV) and continuous testing (via platforms like Picus) are emphasized as essential to proving ROI, optimizing tool sprawl, and prioritizing exploitable vulnerabilities. #Picus #Kerberoasting

The Bank of England’s CBEST assessments found widespread failures in basic cyber hygiene across financial firms and financial market infrastructures, with gaps in patching, hardening, identity and access control, detection, encryption, network security, incident response, and staff training. The report urges firms to address root causes through sustained measures—such as stronger…
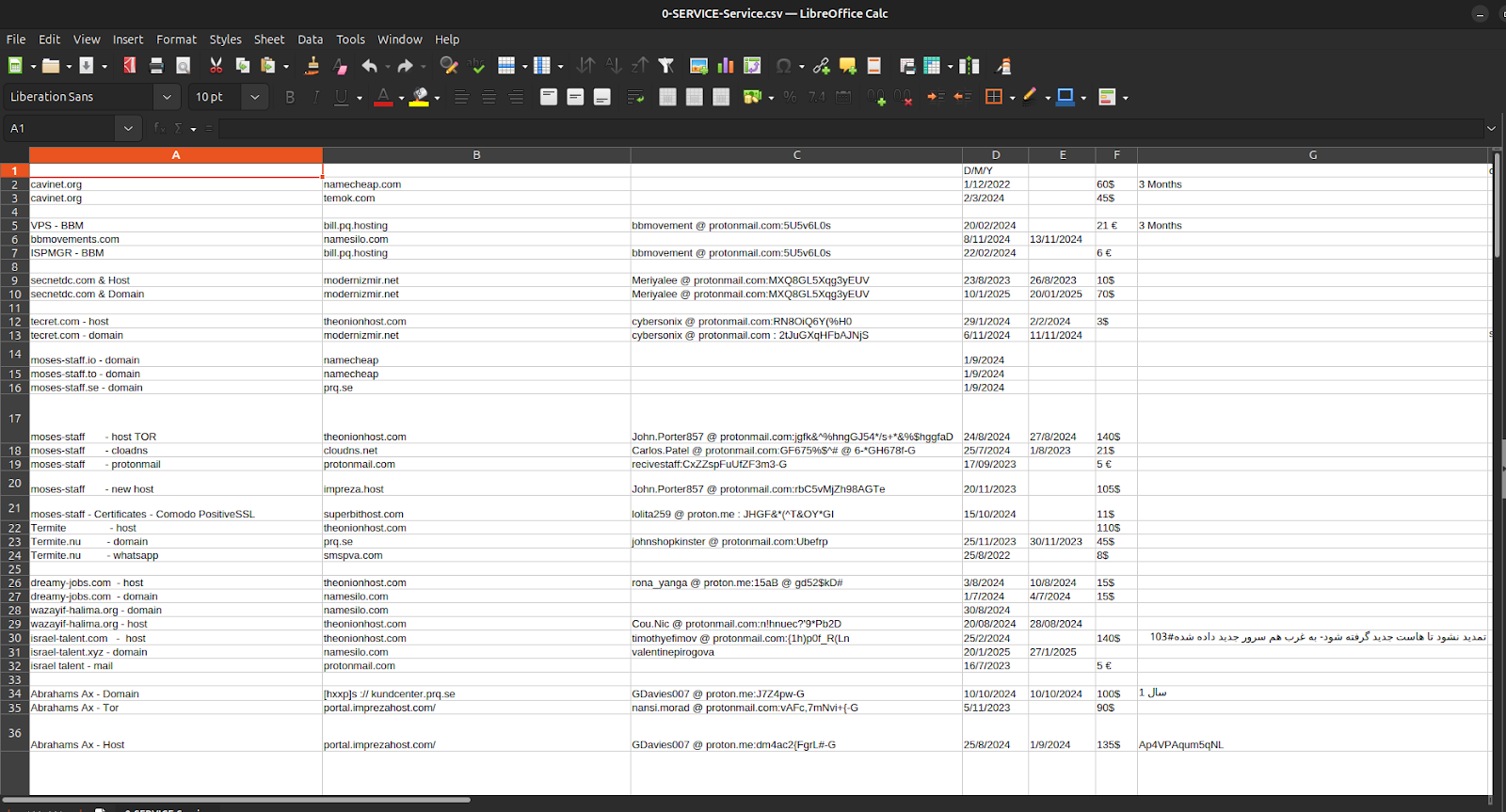
Episode 4 of the Charming Kitten / APT35 leaks exposes not sophisticated zero-day exploits but the bureaucratic infrastructure—spreadsheets, invoices, crypto receipts, hosting accounts, and one-time ProtonMail identities—that fund, procure, and maintain Iranian cyber operations. The documents tie APT35’s procurement and payment chains to Moses Staff’s leak domains and operational tooling, showing micro-crypto payments via Cryptomus, recurring European VPS providers (EDIS, Impreza), and repeatable, auditable workflows that convert state intent into persistent infrastructure. #APT35 #MosesStaff
