EC-Council launched the Enterprise AI Credential Suite with four new role-based AI certifications and an updated Certified CISO v4 to close the gap between rapid AI adoption and workforce readiness. The programs align to an Adopt.Defend.Govern framework and U.S. AI workforce priorities to reduce AI risk exposure and address significant reskilling…
Tag: GOVERNANCE

Global leaders at the India AI Impact Summit 2026 warned that AI is evolving faster than governance and security can keep up, spotlighting risks from unequal access, concentration of power, and rising threats like deepfakes. Speakers including Sundar Pichai, Dario Amodei, and N. Chandrasekaran urged Responsible AI at scale, international governance,…

AI is actively reshaping cyber risk, driving AI-powered ad fraud, deepfake incidents, and novel malware events while regulators and enterprises race to respond in real time. This weekly roundup highlights AI-driven ghost click ad fraud, the Ireland GDPR probe into X’s Grok, and a suspected ransomware incident at Advantest, underscoring the…
![Cybersecurity News | Daily Recap [19 Feb 2026] Cybersecurity News | Daily Recap [19 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, today’s briefing covers a surge of mobile threats led by PromptSpy leveraging Google Gemini for Android phishing in Argentina, along with Massiv banking malware and Keenadu infections spanning Russia, Japan, Germany, Brazil and the Netherlands. The update also highlights critical CVEs in Dell RecoverPoint for VMs, several VS Code extensions, Grandstream GXP1600 and Honeywell CCTV, notable breaches like Figure and ScreenConnect hijacks, evolving surveillance tools usage, and recent enforcement actions such as Red Card 2.0, with AI governance and security funding developments shaping the broader cyber landscape. #PromptSpy #Gemini #Argentina #Massiv #ChaveMovelDigital #Keenadu #Russia #Japan #Germany #Brazil #Netherlands #BRICKSTORM #GRIMBOLT #DellRecoverPointForVMs #VSCode #Grandstream #Honeywell #SmarterMail #Figure #ScreenConnect #VoltTyphoon #Cellebrite #Predator #TPLink #EX1227432 #Copilot #Grok #RedCard2
Self-hosted agent runtimes like OpenClaw significantly widen the execution boundary by ingesting untrusted text, downloading and executing external skills, and acting with the credentials of the host, creating risks of credential exposure, persistent memory manipulation, and host compromise. Organizations should treat OpenClaw as untrusted code execution and, if evaluated, run it only in isolated environments with dedicated non-privileged credentials, continuous monitoring, and a rebuild plan. #OpenClaw #Moltbook

This article argues that agentic GRC—AI agents that autonomously execute entire governance, risk, and compliance workflows—differs fundamentally from AI that merely automates individual tasks. It presents a five-step framework (workflow classification, trigger architecture, decision logic, outcome integration, and validation) with a CCM example and urges GRC teams to redesign processes for autonomous execution rather than incremental automation. #AgenticGRC #CCM #SOC2 #Anecdotes #AWS #CloudTrail #Intsight #8200 #YairKuznitsov

At the India AI Impact Summit 2026, global leaders highlighted the need to move AI in education from pilots to large-scale, responsible, and equitable classroom adoption centered on teachers and pedagogy. They called for 2026 to be a year of action emphasizing teacher training, transparent AI literacy policies, interoperable infrastructure, and…

At the India AI Impact Summit 2026, leaders from government, industry, and academia argued that scaling AI must be matched by strong governance and cyber readiness. Panelists stressed proactive measures like red teaming and continuous stress-testing to counter industrialized threats such as deepfake audio and preserve public trust. #Deepfake #Cyble…
![Cybersecurity News | Daily Recap [19 Feb 2026] Cybersecurity News | Daily Recap [19 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, the bulletin highlights Keenadu Android backdoor embedded in firmware and Google Play apps, a Lazarus-linked graphalgo campaign delivering a RAT, and APT28’s MacroMaze operation targeting Western and Central European governments. It also notes Eurail data breaches, Figure’s data exposure after an employee phishing attack, and governance probes like Grok, along with key vulnerabilities such as CVE-2026-2441 and patch guidance for Chrome, as well as passkeys and ISO 27001 considerations. #Keenadu #graphalgo #Lazarus #MacroMaze #Eurail #Figure #Grok #ShinyHunters #CVE20262441 #Phobos #LAPSUS$ #OperationAether #X

Industrial Control Systems (ICS) remain highly vulnerable because decades‑old hardware, outdated protocols, and operators’ inability to accept downtime prevent effective patching and replacement amid growing nation‑state pre‑positioning and ransomware pressure. To build long‑term resilience in 2026, experts recommend OT‑aware zero trust, identity‑centric controls, microsegmentation, continuous threat exposure management (CTEM), supply‑chain transparency,…

The India AI Impact Summit 2026 convened global leaders, ministers, researchers and industry in New Delhi to position the Global South as a co-creator of AI governance and to translate policy into scalable implementation across People, Planet and Progress. Key themes included aligning AI adoption with mass employability, digital sovereignty, open-source…

Passkeys, built on FIDO2 and WebAuthn, replace passwords with device-bound cryptographic authentication that reduces phishing, support costs, and improves user experience. For ISO/IEC 27001 organizations, a compliant transition requires risk-based prioritization, mapping passkey deployment to Annex A controls, documented recovery procedures, and monitoring for new attack vectors. #Passkeys #ISOIEC27001

Secure Service Edge (SSE) is often promoted as the modern answer for securing access across GenAI, hybrid work, and SaaS sprawl, but many deployments prove the architecture without actually reducing the highest-priority risks. Agentless session security — which provides browser-native, session-level visibility and DLP without endpoint agents — addresses gaps around GenAI prompts, unmanaged devices, and post-login actions and can deliver faster time-to-value. #SecureServiceEdge #AgentlessSessionSecurity

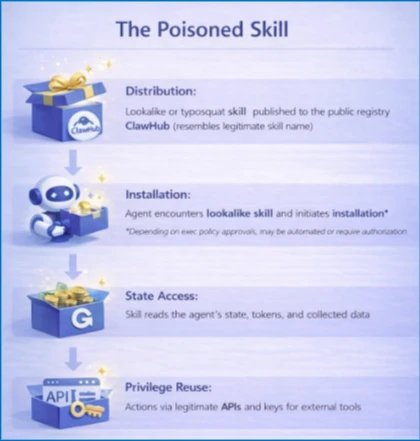
OpenClaw is an agentic AI platform that runs locally with deep system access and an extensible third‑party “skill” ecosystem, enabling file management, workflow automation, and direct shell command execution. Security researchers have identified widespread malicious skills (notably the ClawHavoc campaign) and critical vulnerabilities such as CVE-2026-25253 that enable credential theft, data exfiltration, and remote code execution, prompting mitigations like VirusTotal scanning, Clawdex detection, and blocking via Iru. #OpenClaw #ClawHavoc
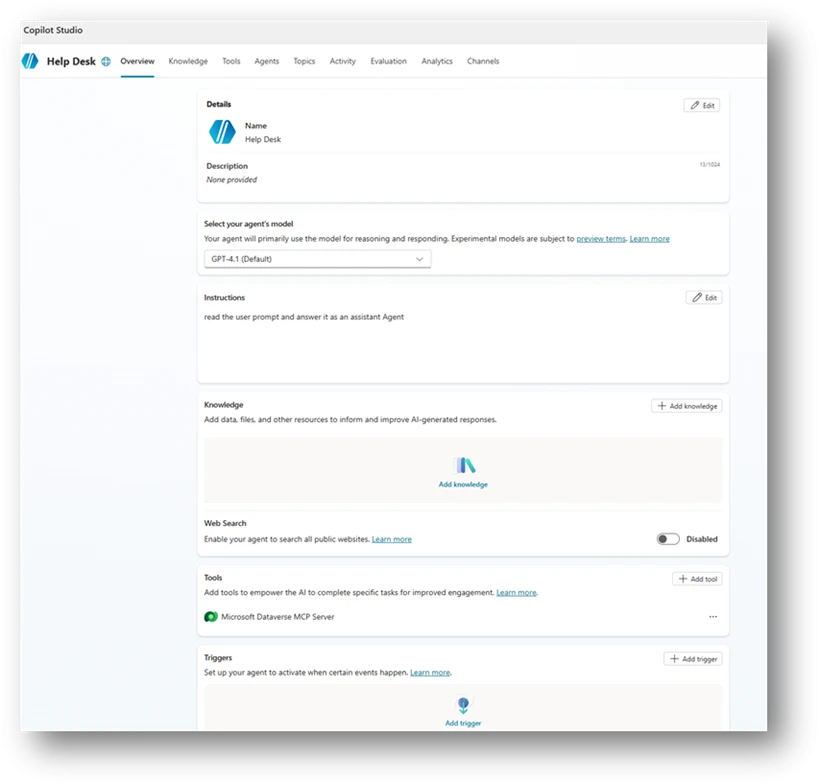
Organizations rapidly adopt Copilot Studio agents but misconfigurations—broad sharing, unauthenticated access, unsafe HTTP requests, author authentication, hard‑coded credentials, unmanaged MCP tools, missing orchestration instructions, dormant or orphaned agents, and email-capable actions—create new identity and data‑access paths that traditional controls don’t monitor. Microsoft Defender Security Research provides ten detection-focused scenarios with Advanced Hunting queries and a mitigation playbook emphasizing ownership, least privilege, enforced authentication, hardened orchestration, and secret management to help teams find and fix these risks early. #CopilotStudio #MicrosoftDefender
