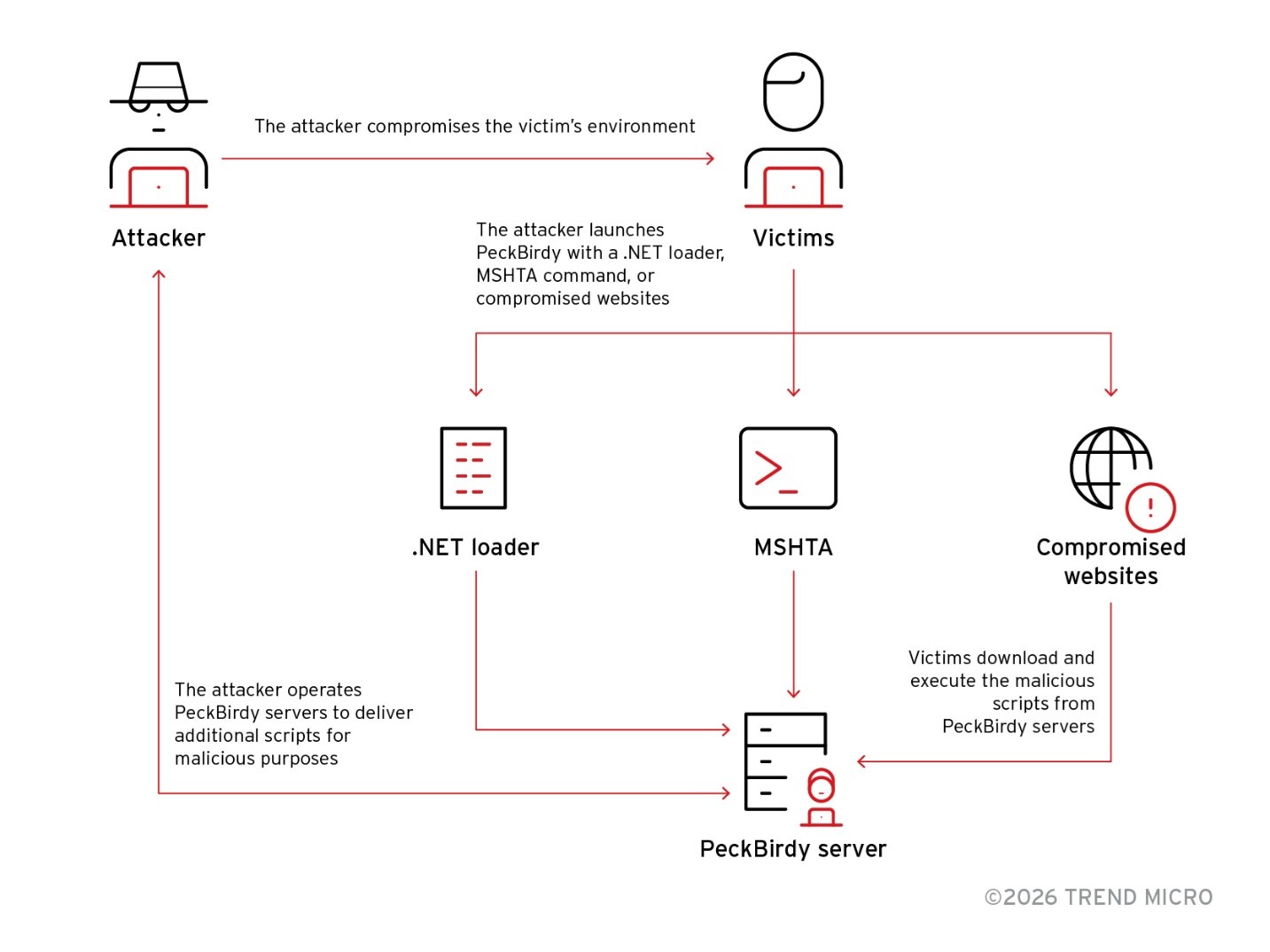
PeckBirdy is a versatile JScript-based command-and-control framework used by China-aligned APT groups since 2023 to abuse LOLBins and deliver modular backdoors across browsers, MSHTA, WScript, Classic ASP, NodeJS and .NET environments. Related campaigns SHADOW-VOID-044 and SHADOW-EARTH-045 deployed backdoors such as HOLODONUT and MKDOOR, used watering‑hole and phishing lures, exploited CVE-2020-16040, and…
Tag: DEFENSE EVASION

Zscaler ThreatLabz identified two Pakistan-linked campaigns in September 2025—Gopher Strike and Sheet Attack—targeting Indian government entities and using novel Golang tools and private GitHub repositories for C2 and payload staging. The Gopher Strike chain uses spearphishing PDFs leading to an ISO that delivers a Golang downloader (GOGITTER), a GitHub-based backdoor (GITSHELLPAD), and a Golang shellcode loader (GOSHELL) that ultimately deploys a Cobalt Strike Beacon. #GOGITTER #GITSHELLPAD #GOSHELL #CobaltStrike #APT36 #IndianGovernment

FortiGuard Labs describes a multi-stage Windows-focused campaign that uses social-engineered archives and LNK-triggered PowerShell to deploy staged loaders, abuse Defendnot to disable Microsoft Defender, install Amnesia RAT for extensive data theft and surveillance, and finally deliver Hakuna Matata–derived ransomware and a WinLocker to encrypt and lock victims’ systems. The operation leverages GitHub and Dropbox for modular hosting and the Telegram Bot API for C2 and exfiltration, while using registry and policy manipulation to suppress defenses and destroy recovery options. #Defendnot #AmnesiaRAT
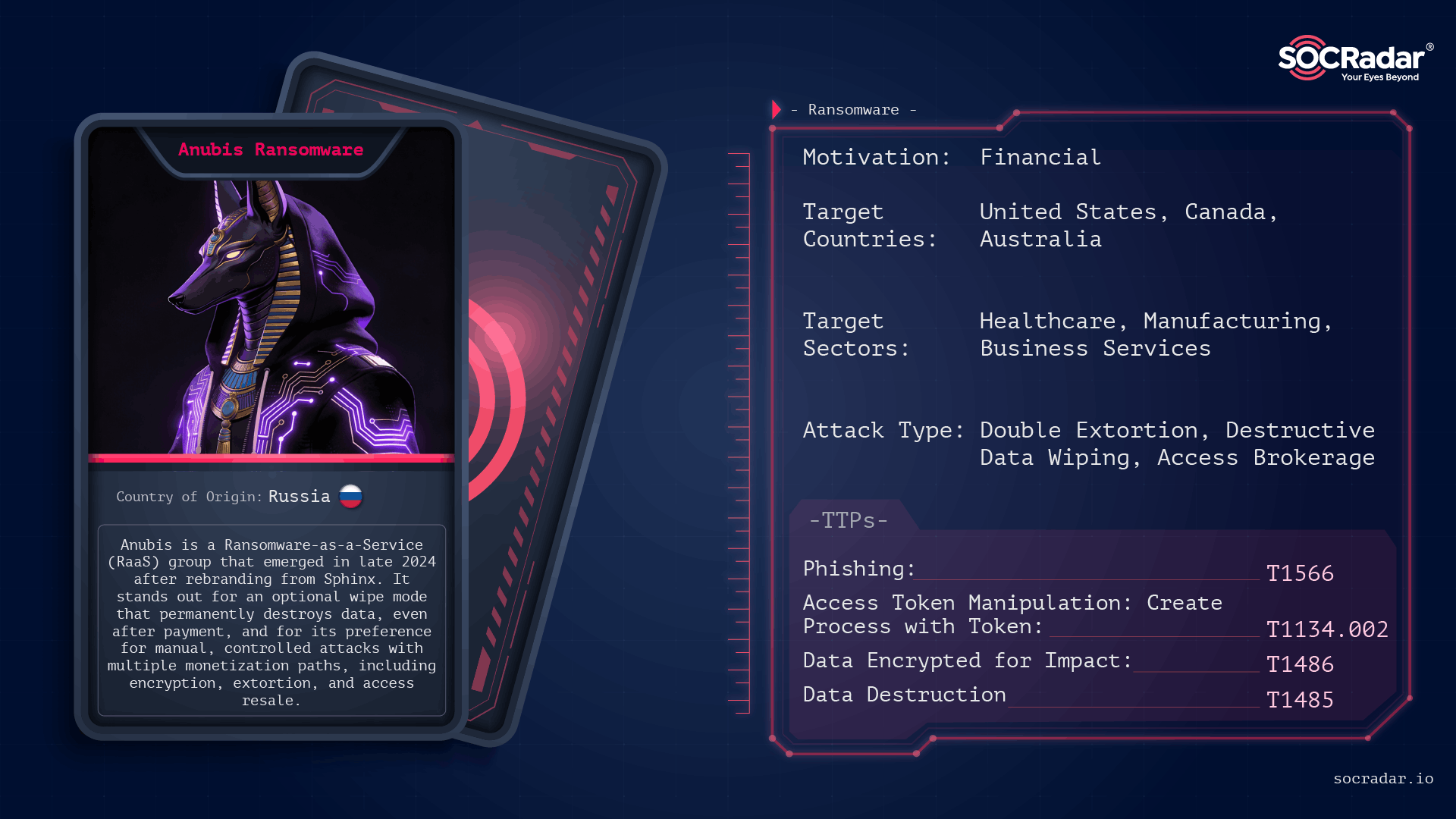
Anubis (formerly Sphinx) is a Ransomware-as-a-Service operation first observed in late 2024 that combines standard file encryption with an optional destructive wipe mode, permanently destroying data and removing decryption as a guaranteed outcome. Its affiliate-driven model and parallel monetization channels (data extortion and access resale) let operators choose between encryption, data-only extortion, or selling access, concentrating on high-value targets and controlled, high-impact intrusions. #Anubis #Sphinx
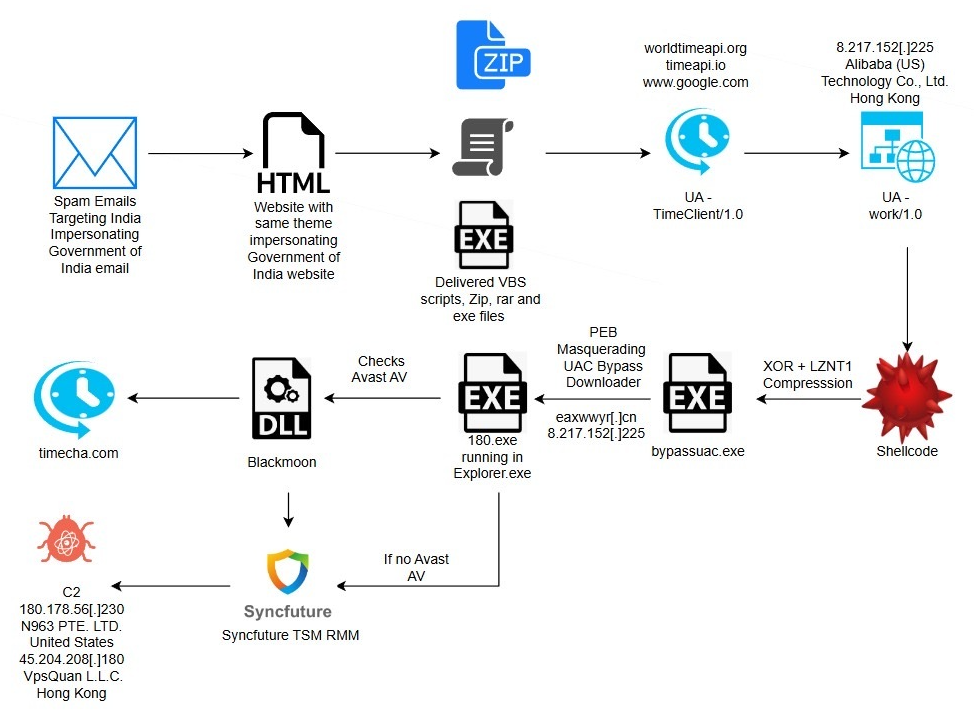
eSentire TRU uncovered a multi-stage espionage campaign targeting residents of India that uses phishing lures impersonating the Income Tax Department to deliver a DLL side-loading loader which fetches shellcode, bypasses UAC via a COM elevation moniker, and ultimately deploys a repurposed SyncFuture TSM platform for persistent remote surveillance. The intrusion chain includes anti-analysis, PEB process masquerading, Avast-specific GUI automation to create antivirus exclusions, service-based Safe Mode persistence, and multiple signed binaries and certificates abused to appear legitimate. #Blackmoon #SyncFuture
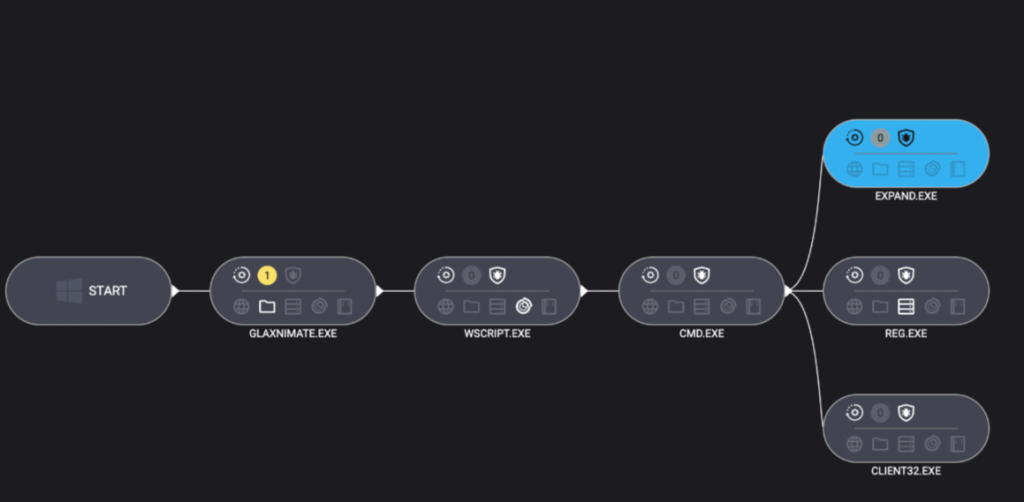
Remcos and NetSupport Manager were deployed via a multi-stage infection chain that relied exclusively on Windows built-in utilities (LOLBins) to evade detection and persist. The attack used forfiles, mshta, PowerShell curl and tar, scripting engines, and stealthy registry persistence before Malwarebytes detected and blocked the intrusion. #Remcos #NetSupportManager…
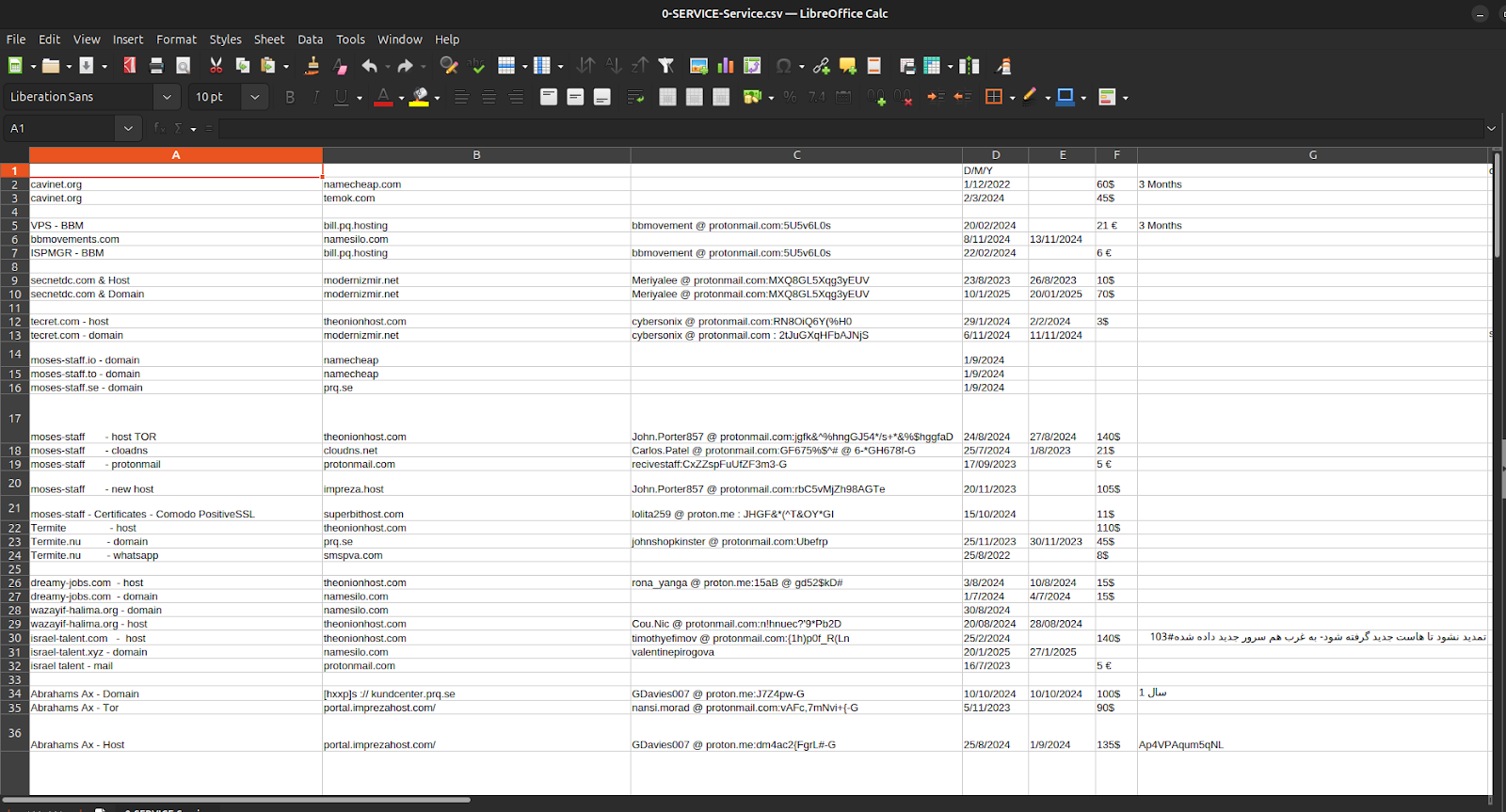
Episode 4 of the Charming Kitten / APT35 leaks exposes not sophisticated zero-day exploits but the bureaucratic infrastructure—spreadsheets, invoices, crypto receipts, hosting accounts, and one-time ProtonMail identities—that fund, procure, and maintain Iranian cyber operations. The documents tie APT35’s procurement and payment chains to Moses Staff’s leak domains and operational tooling, showing micro-crypto payments via Cryptomus, recurring European VPS providers (EDIS, Impreza), and repeatable, auditable workflows that convert state intent into persistent infrastructure. #APT35 #MosesStaff
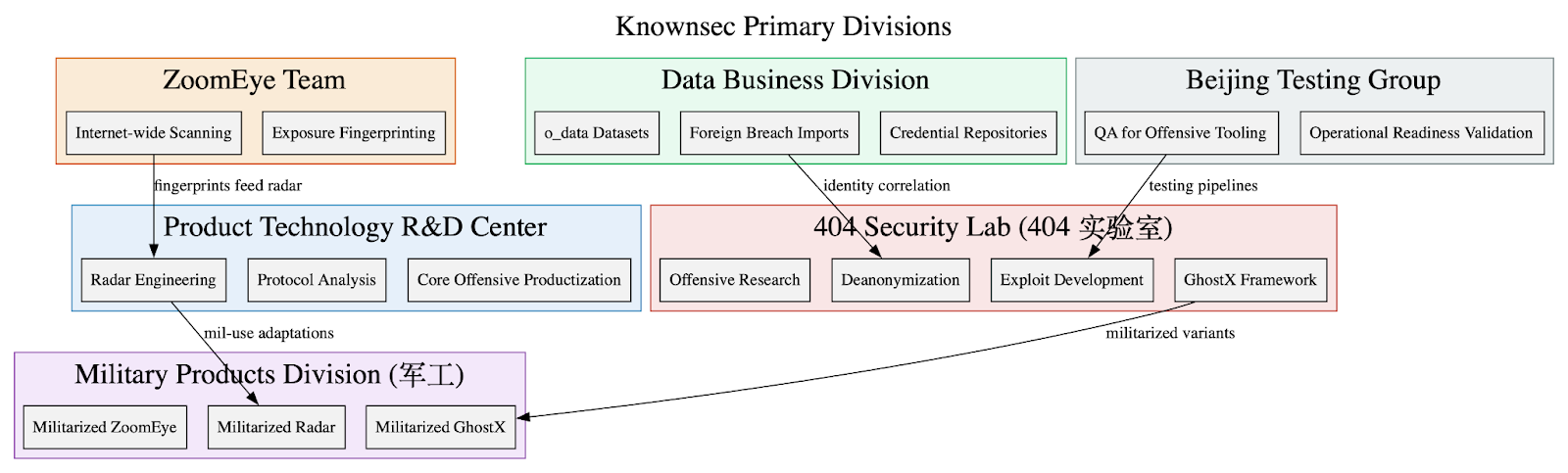
Leaked internal documents show Knownsec operates as a state-aligned cyber contractor supplying a vertically integrated espionage stack—ZoomEye/TargetDB reconnaissance, o_data_* identity correlation, GhostX/Un‑Mail exploitation and mailbox takeover, and Passive Radar PCAP-based internal mapping—to Chinese public‑security, military, and regulator customers. The corpus includes organizational charts, employee emails, high‑confidence IOCs targeting Taiwanese critical infrastructure, and detailed tradecraft emphasizing persistence, anti‑forensics, and APT‑style operational workflows. #Knownsec #GhostX
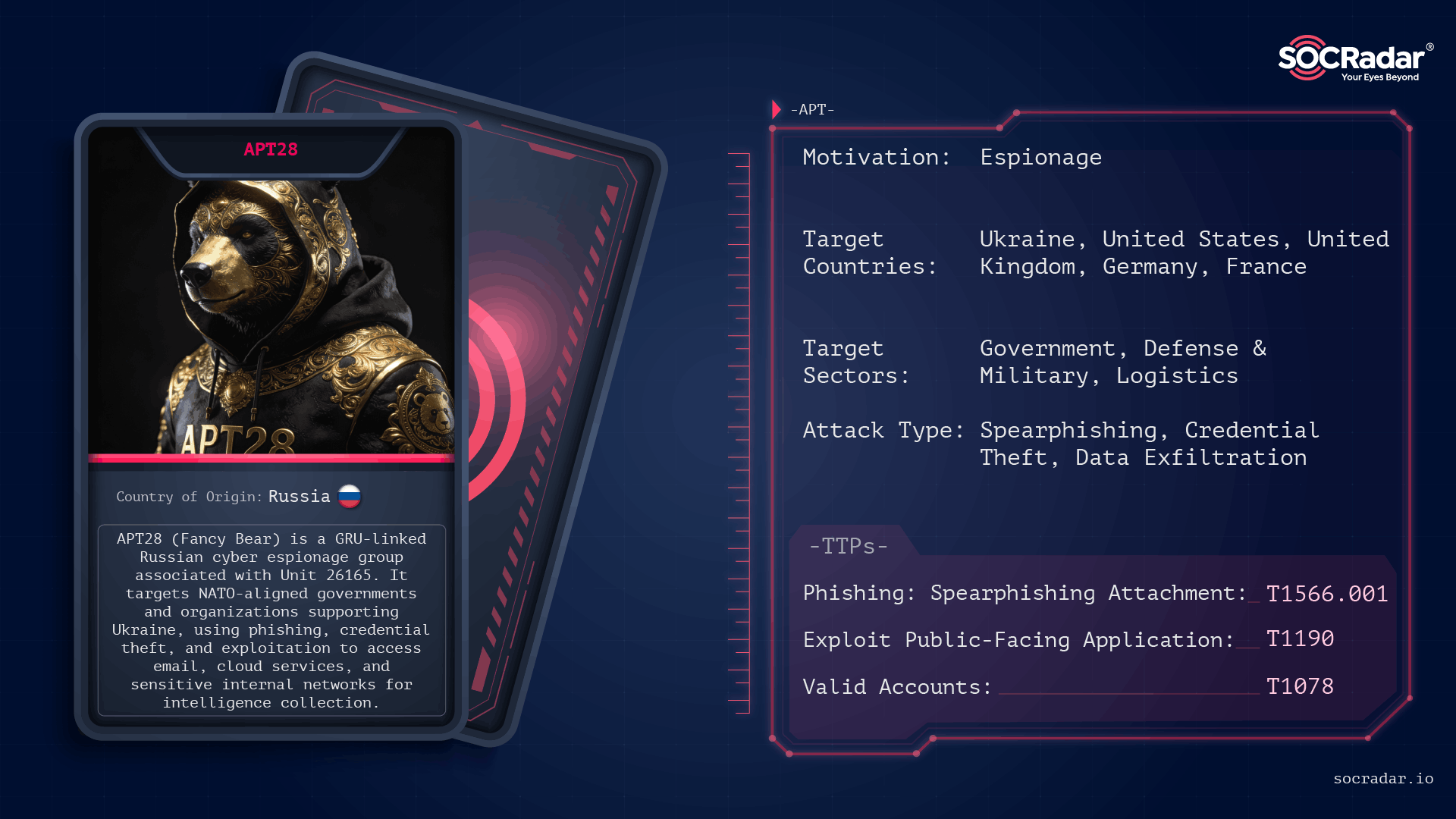
APT28 is a long-running, GRU-linked espionage group that prioritizes stealthy credential access, targeted phishing, and long-term intelligence collection across Europe, North America, and Ukraine. Recent reporting through 2025 highlights new tooling like the LAMEHUG AI-assisted malware and sustained credential/token harvesting campaigns against services such as UKR[.]net. #APT28 #LAMEHUG
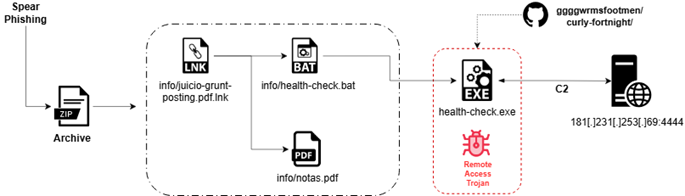
Seqrite Labs uncovered “Operation Covert Access,” a targeted spear-phishing campaign that abuses authentic Argentine federal court documents to deliver a multi-stage Rust-based Remote Access Trojan (CovertRAT) via a weaponized LNK, BAT loader, and a GitHub-hosted second-stage binary. The implant demonstrates extensive anti-VM/anti-debug checks, IPv4/IPv6 C2 fallback (default 181.231.253.69:4444), and a modular command set for persistence, data theft, file transfer, encryption, and privilege escalation. #CovertRATCiR #ArgentinaJudicialSector
SolyxImmortal is a Python-based Windows information-stealer that persistently collects browser credentials, documents, keystrokes, and screenshots and exfiltrates them via hardcoded Discord webhooks. The sample Lethalcompany.py establishes registry Run-key persistence, stages and compresses artifacts for stealthy long-term surveillance rather than propagation. #SolyxImmortal #Discord
Sysdig TRT’s analysis of VoidLink describes a Chinese-developed, Zig-built Linux malware framework that uses a three-stage fileless loader, serverside rootkit compilation (SRC) to produce kernel modules per-target, and multiple stealth/control channels including prctl, eBPF, and an ICMP covert channel. Despite advanced adaptive evasion, VoidLink’s memfd_create/execveat fileless execution, eBPF and kernel-module activity, and other runtime behaviors are detectable with tools like Falco and Sysdig Secure. #VoidLink #Sysdig

Mamba Phishing-as-a-Service Kit: How Modern adversary-in-the-middle (AiTM) Attacks Operate – CYFIRMA
CYFIRMA assesses Mamba 2FA is a scalable adversary-in-the-middle phishing framework that automates realistic Microsoft authentication flows to capture credentials, bypass MFA, and relay sessions with minimal user interaction. The report highlights encoded URL parameters, Microsoft-style password prompts, client-side password capture, rapid redirection to legitimate sites, and recommends hardened identity controls such as FIDO2/WebAuthn and continuous monitoring to mitigate risk. #Mamba2FA #Microsoft365

Cyble’s analysis describes deVixor, an evolving Android banking RAT distributed via fake automotive websites that deploy malicious APKs to Iranian users to harvest SMS-based financial data, capture credentials, perform keylogging, and surveil devices. The malware now includes WebView-based JavaScript injection, a remotely triggered ransomware module, and uses Telegram and Firebase for command-and-control and large-scale administration. #deVixor #IranianBanks

Medusa Ransomware is a rapidly expanding RaaS operation (also known as Storm-1175/Spearwing) that has abused unpatched RMM and public-facing application vulnerabilities to gain initial access, perform data exfiltration, and carry out file encryption across diverse sectors. Darktrace and other vendors have observed the group exploiting SimpleHelp and GoAnywhere flaws, abusing legitimate RMM tooling for C2 and persistence, and exfiltrating data to domains such as erp.ranasons[.]com. #Medusa #SimpleHelp