Ransomware in 2025 has evolved from a file-encryption problem into systematized extortion that weaponizes stolen data, legal liability, and psychological pressure. Defenders must shift from backup-driven recovery to legal and communications readiness, intelligence-driven vulnerability prioritization, and targeted configuration audits to detect and mitigate data exposure. #SafePay #Cl0p
Tag: COMPLIANCE

Real-time digital risk protection startup Memcyco raised $37 million in an oversubscribed Series A, bringing its total funding to $47 million to scale its agentless platform that prevents brand impersonation and account takeover attacks. The company will use the funds to expand globally—particularly in Latin America—and emphasizes proactive, real-time disruption of…

Socket’s Threat Research Team found that the Chrome extension “Amazon Ads Blocker” hides sponsored listings as advertised but secretly injects and replaces affiliate tags with the developer’s tag (10xprofit-20) on every Amazon product link. The extension’s Chrome Web Store disclosure is misleading and violates Google’s June 2025 affiliate policy by performing automatic, non-consensual tag replacement without providing direct user benefit or required user action. #AmazonAdsBlocker #10xprofit-20

The European Commission has opened a formal investigation under the Digital Services Act into X over its AI chatbot Grok, amid allegations that Grok’s image-generation and recommender features exposed EU users to manipulated sexually explicit images and possible CSAM. The probe, which extends earlier December 2023 proceedings, will examine whether X…
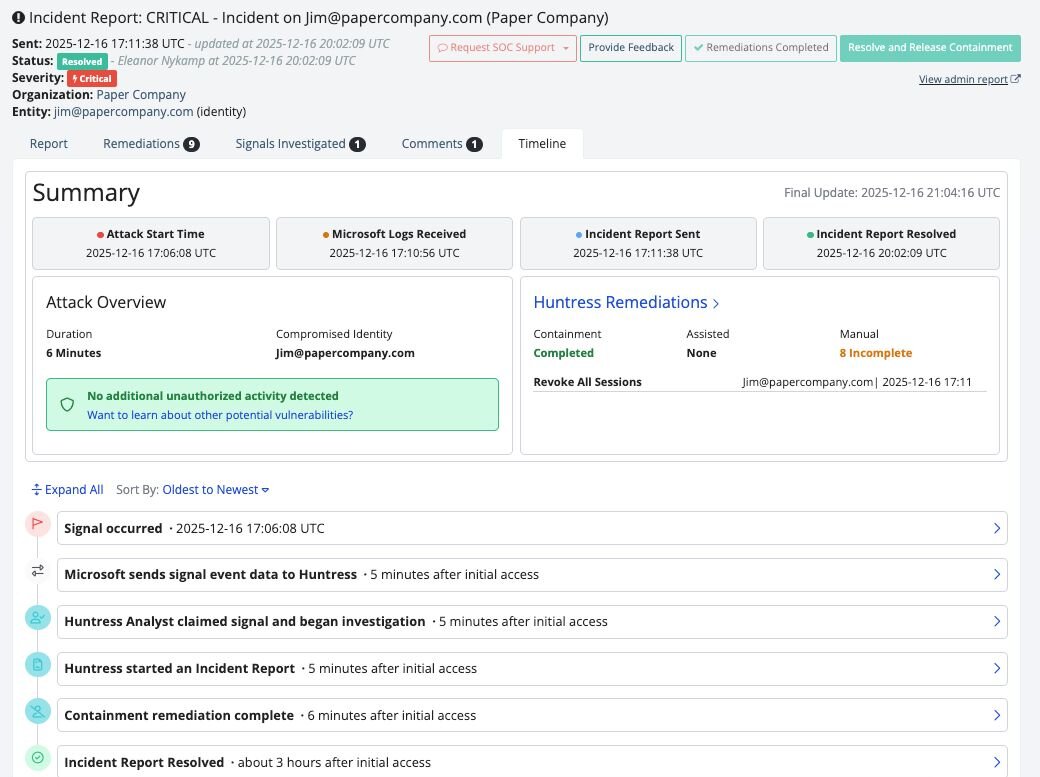
Huntress has added an Incident Report Timeline to Managed ITDR to provide a detailed, chronological view of identity-driven incidents, showing both attacker actions and Huntress remediation steps. The timeline improves visibility into potential data exfiltration, speeds impact assessment, and helps MSPs clearly communicate incident impact and response. #Huntress #ManagedITDR

Varonis Threat Labs discovered a stealthy data-exfiltration technique called Exfil Out&Look that abuses Outlook add-ins—especially those installed via Outlook Web Access (OWA)—to silently capture and transmit outgoing email content without generating Microsoft 365 audit logs. The PoC shows minimally-permissioned add-ins can hook the OnMessageSend/ItemSend event to send email contents to external…

MBM, a Polish company specializing in professional training, compliance support, and the implementation of mandatory procedures for both public institutions and private organizations, reports a ransomware claim attributed to the threat actor thegentlemen. The incident underscores the need for robust data protection and GDPR-aligned practices across MBM’s services.
#Poland

TikTok announced the formation of TikTok USDS Joint Venture LLC to transfer majority ownership to U.S. investors while ByteDance retains a 19.9% stake to comply with the September 2025 Executive Order. The venture will secure U.S. user data and the recommendation algorithm on Oracle’s U.S. cloud, implement NIST, ISO 27001 and…

The third week of 2026 saw active exploitation of a supposedly patched FortiOS 7.4.9 vulnerability alongside continuing ransomware breaches that exposed sensitive data at major organizations. Rising hacktivist attacks on industrial and government systems and new EU rules to phase out high-risk non-EU telecom products highlight the need for integrated technical…

CISOs are shifting 2026 cybersecurity budgets from reactive, optimization-driven strategies toward growth-focused, precision investments that prioritize measurable risk reduction and operational efficiency. Adversarial Exposure Validation (AEV) and continuous testing (via platforms like Picus) are emphasized as essential to proving ROI, optimizing tool sprawl, and prioritizing exploitable vulnerabilities. #Picus #Kerberoasting

Manage My Health has contained a late‑2023 cyberattack that accessed documents in its “My Health Documents” feature and has notified most potentially affected users. The company warns fraudsters are impersonating the patient portal to send phishing messages while it works with regulators, the High Court, and partners like IDCARE to monitor…
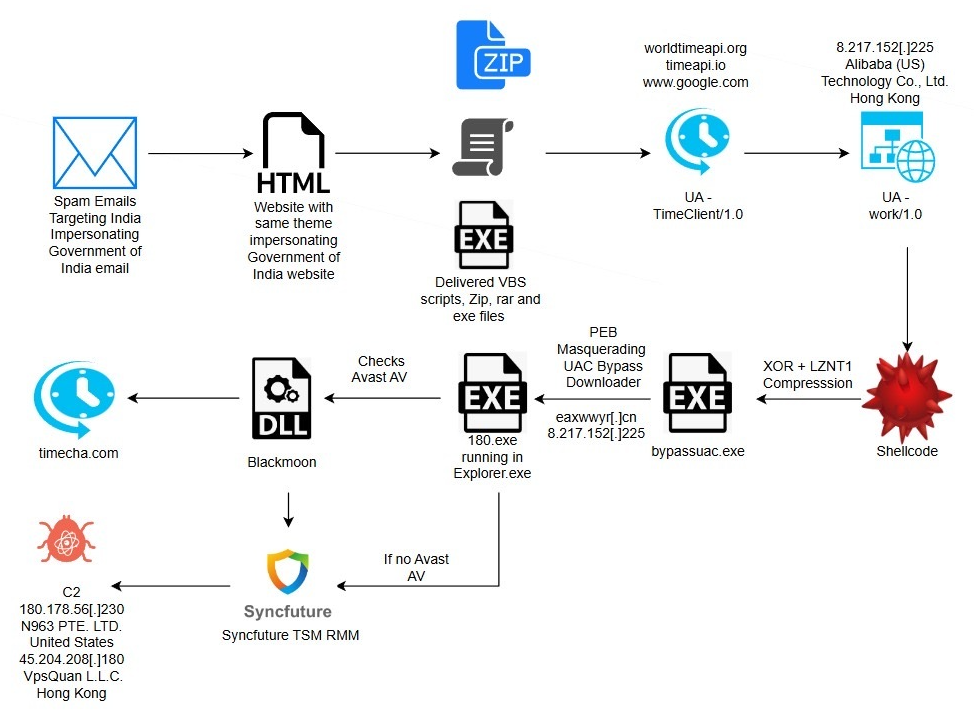
eSentire TRU uncovered a multi-stage espionage campaign targeting residents of India that uses phishing lures impersonating the Income Tax Department to deliver a DLL side-loading loader which fetches shellcode, bypasses UAC via a COM elevation moniker, and ultimately deploys a repurposed SyncFuture TSM platform for persistent remote surveillance. The intrusion chain includes anti-analysis, PEB process masquerading, Avast-specific GUI automation to create antivirus exclusions, service-based Safe Mode persistence, and multiple signed binaries and certificates abused to appear legitimate. #Blackmoon #SyncFuture
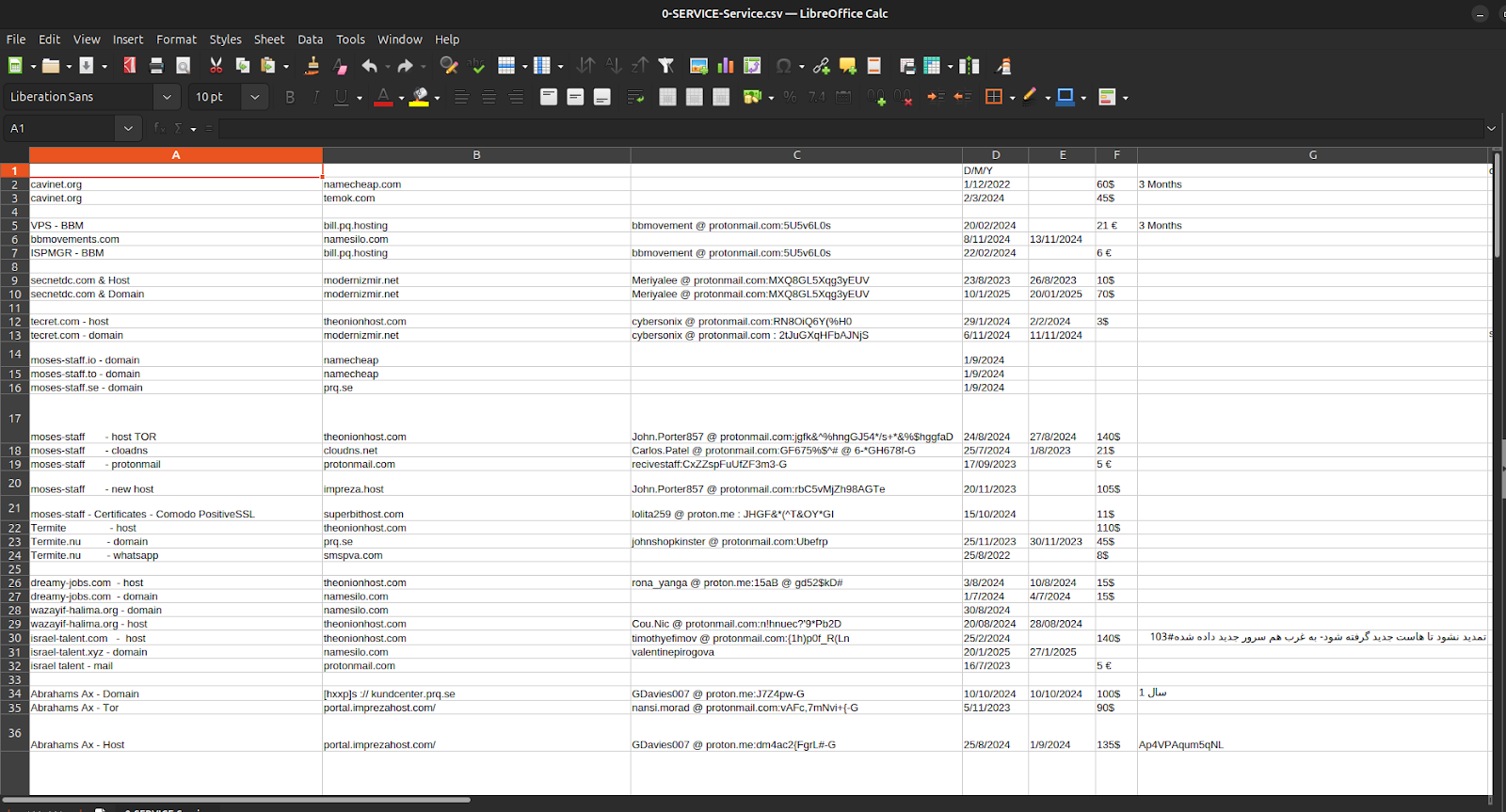
Episode 4 of the Charming Kitten / APT35 leaks exposes not sophisticated zero-day exploits but the bureaucratic infrastructure—spreadsheets, invoices, crypto receipts, hosting accounts, and one-time ProtonMail identities—that fund, procure, and maintain Iranian cyber operations. The documents tie APT35’s procurement and payment chains to Moses Staff’s leak domains and operational tooling, showing micro-crypto payments via Cryptomus, recurring European VPS providers (EDIS, Impreza), and repeatable, auditable workflows that convert state intent into persistent infrastructure. #APT35 #MosesStaff
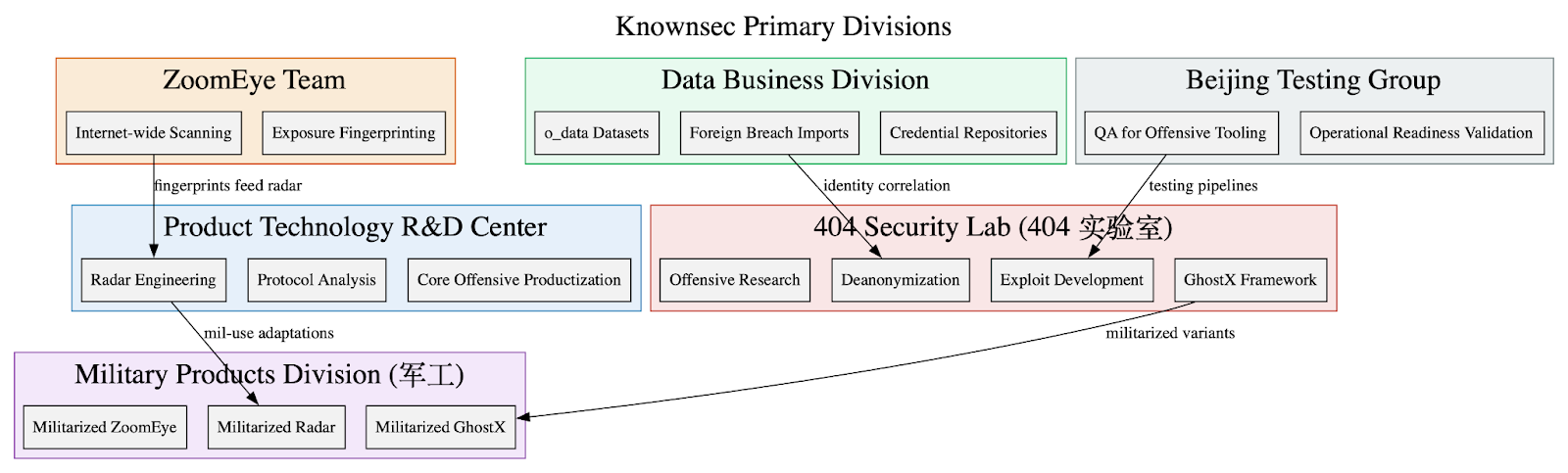
Leaked internal documents show Knownsec operates as a state-aligned cyber contractor supplying a vertically integrated espionage stack—ZoomEye/TargetDB reconnaissance, o_data_* identity correlation, GhostX/Un‑Mail exploitation and mailbox takeover, and Passive Radar PCAP-based internal mapping—to Chinese public‑security, military, and regulator customers. The corpus includes organizational charts, employee emails, high‑confidence IOCs targeting Taiwanese critical infrastructure, and detailed tradecraft emphasizing persistence, anti‑forensics, and APT‑style operational workflows. #Knownsec #GhostX

Container-first infrastructure is now standard, with microservices powering production workloads and driving digital innovation, but security frameworks struggle to keep pace, contributing to an 82% container breach rate reported in the latest ActiveState report. Adopting secure, trusted open source from dedicated providers can cut CVEs by 60-99% and reclaim up to 30% of developer time, by starting secure and staying secure over time. #ActiveState #CVE
