Businesses’ demand for speed and developers’ heavy workloads have undermined “shift left” security efforts, leading to unsafe use of public container images and loss of control over deployments. Qualys’ analysis of over 34,000 public images found roughly 7.3% malicious with many containing cryptominers and exposed secrets, prompting a recommendation to move security “down” into platform-level automation and golden paths. #DockerHub #AWS
Tag: COMPLIANCE

EC-Council Expands AI Certification Portfolio to Strengthen U.S. AI Workforce Readiness and Security
EC-Council launched the Enterprise AI Credential Suite with four new role-based AI certifications and an updated Certified CISO v4 to close the gap between rapid AI adoption and workforce readiness. The programs align to an Adopt.Defend.Govern framework and U.S. AI workforce priorities to reduce AI risk exposure and address significant reskilling…

Google says it blocked more than 255,000 Android apps from obtaining excessive access to sensitive user data and rejected over 1.75 million apps from Google Play through 2025 as part of strengthened protections. The company expanded AI-assisted reviews, Play Protect scanning, Play Integrity API checks, and Android 16 tapjacking defenses to detect malicious developers, curb review-bombing, and prevent app-based fraud. #Google #Android

Security teams are overwhelmed by escalating attack volume and attacker throughput, making detection alone insufficient to prevent breaches. Operational Exposure Management — focusing on validated, reversible remediation — is required to shrink exposure dwell time and close the action gap. #ClickFix #Qilin

This article argues that agentic GRC—AI agents that autonomously execute entire governance, risk, and compliance workflows—differs fundamentally from AI that merely automates individual tasks. It presents a five-step framework (workflow classification, trigger architecture, decision logic, outcome integration, and validation) with a CCM example and urges GRC teams to redesign processes for autonomous execution rather than incremental automation. #AgenticGRC #CCM #SOC2 #Anecdotes #AWS #CloudTrail #Intsight #8200 #YairKuznitsov

OpenAI rolled out Lockdown Mode and Elevated Risk labels to counter prompt injection attacks by adding deterministic infrastructure controls that prevent data exfiltration regardless of prompt manipulation. The features restrict network interactions for high-risk users and flag network-related capabilities to help administrators and users manage exposure. #OpenAI #LockdownMode…
![Cybersecurity News | Daily Recap [17 Feb 2026] Cybersecurity News | Daily Recap [17 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, the bulletin highlights Keenadu Android backdoor embedded in firmware and Google Play apps, a Lazarus-linked graphalgo campaign delivering a RAT, and APT28’s MacroMaze operation targeting Western and Central European governments. It also notes Eurail data breaches, Figure’s data exposure after an employee phishing attack, and governance probes like Grok, along with key vulnerabilities such as CVE-2026-2441 and patch guidance for Chrome, as well as passkeys and ISO 27001 considerations. #Keenadu #graphalgo #Lazarus #MacroMaze #Eurail #Figure #Grok #ShinyHunters #CVE20262441 #Phobos #LAPSUS$ #OperationAether #X

Citizen Lab found traces of Cellebrite’s commercial data-extraction technology on Kenyan activist Boniface Mwangi’s phone after his arrest, suggesting his private communications and photos were accessed. The discovery adds to allegations of Cellebrite being used against activists in multiple countries and has sparked calls for the company to publish its sales…

Ireland’s Data Protection Commission has opened a formal GDPR investigation into X over its Grok AI allegedly generating non-consensual sexual images of real people, including children. The inquiry joins parallel probes by the ICO, the European Commission, California’s attorney general, Ofcom, and French prosecutors and could result in significant EU‑wide fines and criminal measures. #Grok #X

Ireland’s Data Protection Commission has opened a large-scale GDPR investigation into Elon Musk’s X Internet Unlimited Company over its Grok AI generating nonconsensual sexually explicit deepfake images, including images reportedly involving children. The probe — running alongside separate EU and UK inquiries under the Digital Services Act — could result in…
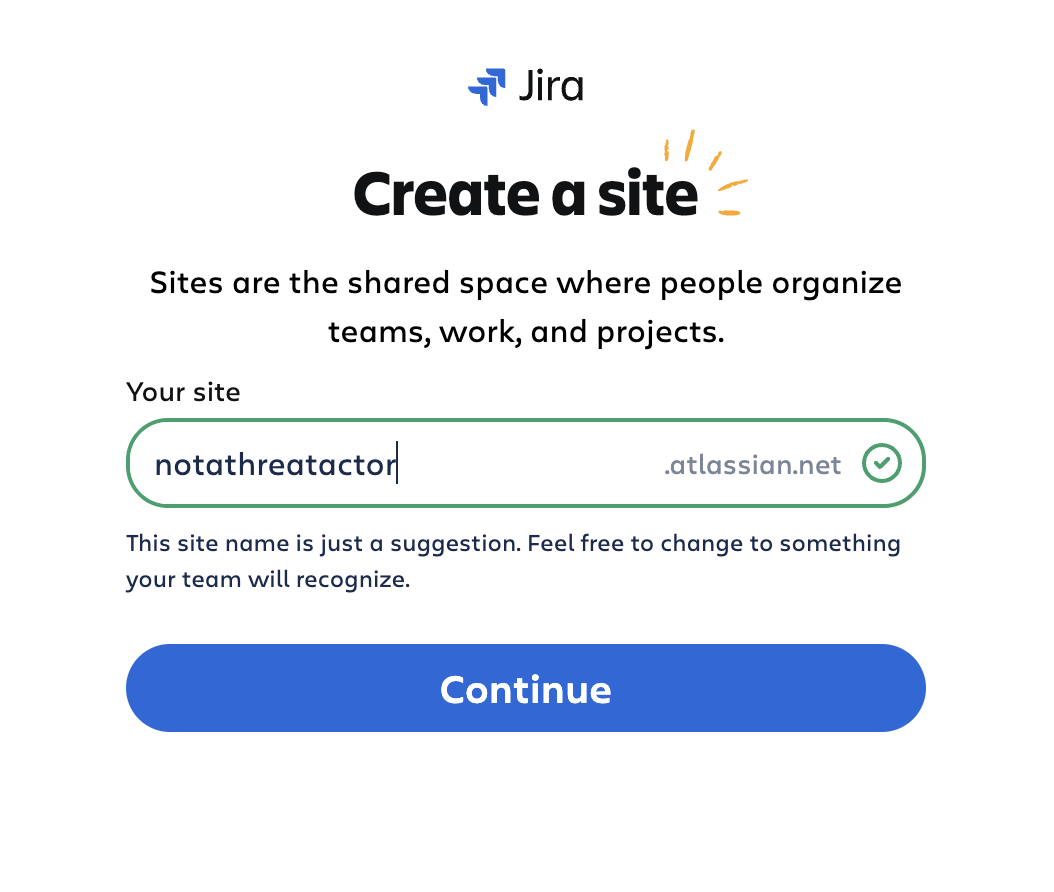
Threat actors created disposable Atlassian Jira Cloud instances and abused Jira Automation and the platform’s trusted atlassian.net email reputation to deliver automated, localized spam and targeted lures to recipients across multiple languages and sectors. The campaigns used integrated email-sending services and Keitaro TDS redirects to funnel victims to investment scams and…

A January breach of Eurail’s customer database has escalated into a large-scale identity theft crisis after attackers began offering millions of travelers’ sensitive records for sale on criminal marketplaces and publishing a sample on Telegram. The compromised information—names, passport numbers, ID numbers, IBANs, health data and contact details—puts DiscoverEU participants at…

CISA will remain operational during the DHS shutdown but at reduced capacity, requiring 888 of its 2,341 staff to work in excepted areas without pay while many projects and new work are curtailed. The KEV Catalog will remain online and can be updated for actively exploited vulnerabilities, but regulatory work like…

Passkeys, built on FIDO2 and WebAuthn, replace passwords with device-bound cryptographic authentication that reduces phishing, support costs, and improves user experience. For ISO/IEC 27001 organizations, a compliant transition requires risk-based prioritization, mapping passkey deployment to Annex A controls, documented recovery procedures, and monitoring for new attack vectors. #Passkeys #ISOIEC27001

DragonForce claims to have compromised Trace Environmental Systems Inc. (traceenv.com), a US-based provider of continuous stack emission monitoring systems and data collection solutions. The company serves ethanol production, power generation, chemical manufacturing, waste-to-energy, wastewater incineration, cogeneration/recovery/university facilities, and refineries. #UnitedStates
