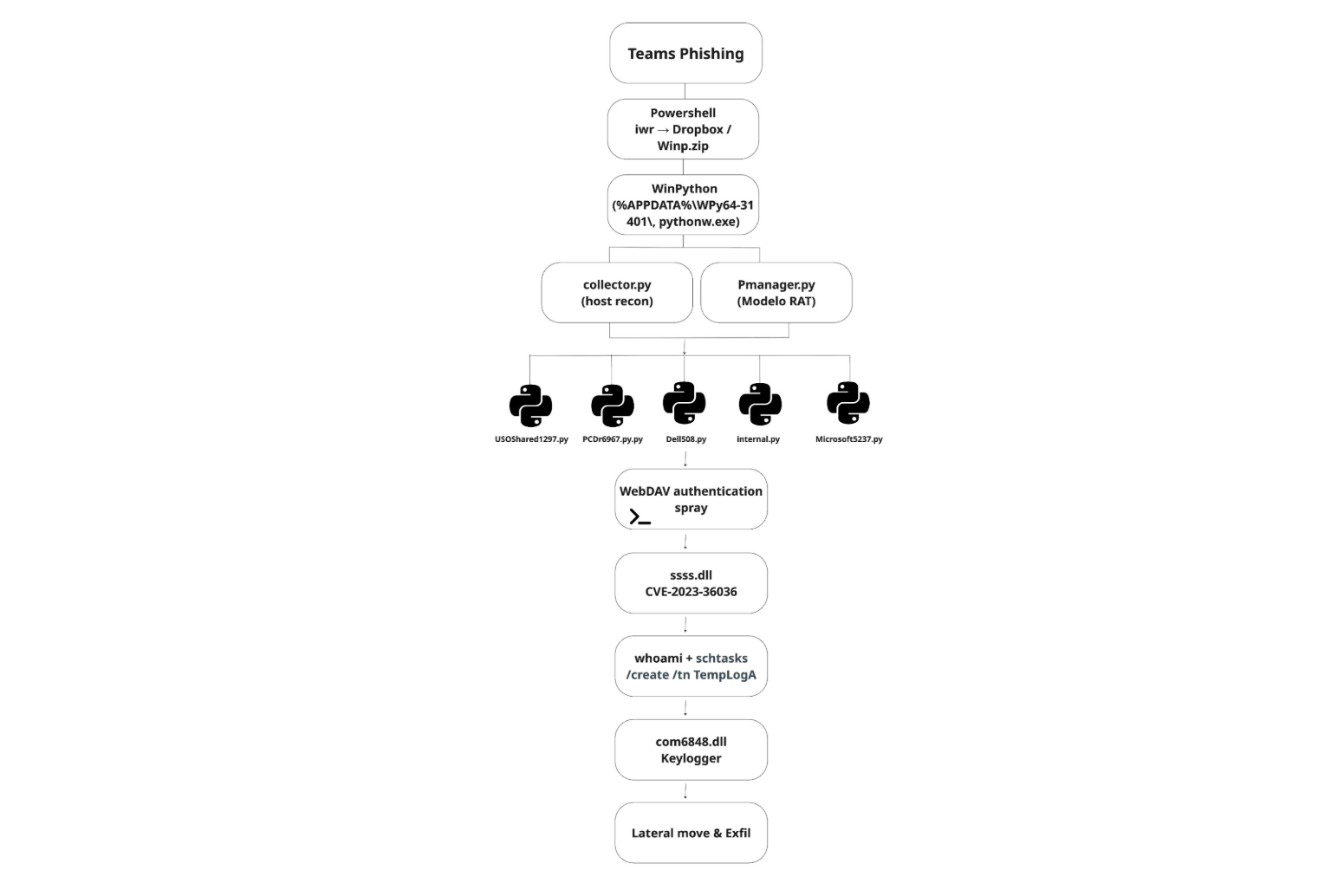
Rapid7 investigated a 2026 enterprise intrusion that began with a fake Microsoft Teams “IT Support” message, then progressed through Dropbox-hosted Python malware, privilege escalation with CVE-2023-36036, credential harvesting, and lateral movement. The campaign was linked to ModeloRAT and KongTuke, showing how Teams abuse, Living-off-the-Land tools, and identity theft can rapidly turn initial access into broad enterprise compromise. #ModeloRAT #KongTuke #MicrosoftTeams #CVE-2023-36036
Keypoints
- Attackers used Microsoft Teams external access to impersonate “IT Support” and message a targeted employee.
- A PowerShell stager downloaded a Dropbox-hosted ZIP archive that launched portable Python payloads in the background.
- The malware performed host reconnaissance, collected system and network details, and sent results back to command-and-control infrastructure.
- The primary backdoor behavior matched ModeloRAT, previously associated with KongTuke-related activity.
- Attackers escalated privileges using CVE-2023-36036, a cldflt.sys heap buffer overflow exploit that led to SYSTEM access.
- Post-exploitation activity included scheduled-task persistence, Active Directory enumeration, WinRM/RDP movement, and deployment of additional proxy/tunnel modules.
- A fake Windows lock screen was used to harvest the user’s domain password, enabling further access and likely memory dump exfiltration.
MITRE Techniques
- [T1566.003] Phishing: Spearphishing via Service – The attacker used Microsoft Teams as the delivery channel to impersonate IT support and target a user (‘the attacker used a newly created tenant … to impersonate “IT Support” and messaged a targeted employee’).
- [T1204.002] User Execution: Malicious File – The victim interaction led to execution of a hidden PowerShell command and staged payload retrieval (‘Shortly after the interaction, a hidden PowerShell command executed on the victim’s machine’).
- [T1059.001] Command and Scripting: PowerShell – PowerShell was used for staging, hidden execution, reconnaissance, persistence, and remote session handling (‘hidden PowerShell sessions’, ‘powershell -NoProfile -NoExit’).
- [T1059.006] Command and Scripting: Python – Portable Python was used to run collector.py, Pmanager.py, and other malware modules (‘Start-Process … pythonw.exe … collector.py’).
- [T1105] Ingress Tool Transfer – The attacker downloaded payloads from Dropbox and transferred additional modules to hosts (‘reached out to Dropbox to retrieve a ZIP archive’).
- [T1218.011] System Binary Proxy Execution: Rundll32 – rundll32.exe was used to launch DLL payloads for execution (‘rundll32.exe ssss.dll startproc’).
- [T1053.005] Scheduled Task/Job: Scheduled Task – Persistence was established with a SYSTEM-level scheduled task (‘created a scheduled task (TempLogA)’).
- [T1068] Exploitation for Privilege Escalation – CVE-2023-36036 was exploited to elevate privileges to SYSTEM (‘a custom privilege escalation exploit targeting CVE-2023-36036’).
- [T1134.001] Access Token Manipulation: Token Impersonation – The exploit flipped a privilege bit and launched payloads under a SYSTEM token (‘immediately launches internal.py as SYSTEM’).
- [T1134.004] Access Token Manipulation: Parent PID Spoofing – The malware used process-creation tricks and helper-thread behavior to manage execution under elevated context (‘spawns a helper thread … launches internal.py as SYSTEM’).
- [T1562.001] Impair Defenses – The attacker used hidden windows, background execution, and artifact removal to reduce visibility (‘CREATE_NO_WINDOW’, ‘the archive was immediately extracted and deleted’).
- [T1027] Obfuscated Files or Information – Malware modules were obfuscated to hinder analysis (‘all other python modules dropped by malware are obfuscated’).
- [T1027.002] Software Packing – The payload was delivered as a portable WinPython environment and extracted archive (‘portable WinPython environment’).
- [T1027.009] Embedded Payloads – DLLs contained encrypted embedded payloads that were decrypted in memory (‘contains an encrypted payload’).
- [T1620] Reflective Code Loading – Multiple DLLs reflectively loaded second-stage payloads into memory (‘reflectively loads a second stage stage2.dll’).
- [T1036.005] Masquerading – The attacker used fake names and benign-looking scripts to blend in (‘reusing the same backdoor under different names’).
- [T1140] Deobfuscate/Decode Files or Information – The malware decrypted embedded payloads and decoded content before execution (‘The decryption key was conveniently provided on the command line’).
- [T1112] Modify Registry – The exploit relied on registry/cloud-files related configuration to register a fake sync provider (‘points to %TEMP%cldflt’).
- [T1055] Process Injection – The attack chain used memory-resident loading and process manipulation to run payloads (‘launches additional Python scripts’).
- [T1056.002] Input Capture: GUI Input Capture – A fake lock screen captured the user’s password when typed (‘The DLL captures it, and writes the result to disk’).
- [T1558.003] Steal or Forge Kerberos Tickets: Kerberoasting – The attacker requested vulnerable Kerberos tickets against service accounts (‘performed Kerberoasting against service accounts’).
- [T1003.001] OS Credential Dumping: LSASS Memory – DumpIt was used to capture RAM that may contain LSASS credentials (‘DumpIt captures physical RAM, including LSASS process memory’).
- [T1018] Remote System Discovery – The attacker enumerated accessible internal systems during reconnaissance and via WebDAV validation (‘enumerate accessible systems’).
- [T1087.002] Account Discovery: Domain Account – Active Directory enumeration was used to count and identify domain users (‘returns the total number of domain user accounts’).
- [T1082] System Information Discovery – The malware gathered system identity, patch level, and OS details (‘systeminfo, domain queries’).
- [T1016] System Network Configuration Discovery – Network visibility commands were used to map connectivity (‘getmac.exe, arp -a, Get-NetTCPConnection’).
- [T1033] System Owner/User Discovery – The attacker checked privilege context and user state (‘whoami /all’).
- [T1083] File and Directory Discovery – The malware enumerated files and directories and saved recon output (‘saved the results to %TEMP%configA.json’).
- [T1021.006] Remote Services: WinRM – The attacker established remote PowerShell sessions through WinRM (‘established a remote PowerShell session (WinRM)’).
- [T1021.001] Remote Services: RDP – The attacker used RDP to access another workstation (‘authenticate via RDP to another workstation’).
- [T1570] Lateral Tool Transfer – Additional modules were deployed across hosts to expand capabilities (‘3 additional Python modules were deployed’).
- [T1071.001] Application Layer Protocol: Web Protocols – C2 communications used HTTP over port 80 to blend with normal traffic (‘created a long-running HTTP beacon over port 80’).
- [T1095] Non-Application Layer Protocol – The reverse shell used TCP sockets and non-HTTP shell communications (‘TCP reverse shell’).
- [T1090.001] Proxy: Internal Proxy – A SOCKS5 proxy was deployed to route attacker tools through the victim (‘Routes attacker’s tools … through victim into internal network’).
- [T1090.002] Proxy: External Proxy – The attacker used external tunneling and proxy infrastructure for access and egress (‘Reverse TCP tunnel’).
- [T1572] Protocol Tunneling – The attack used WebDAV and HTTP tunneling to move data and validate credentials (‘WebDAV authentication spray’).
- [T1573] Encrypted Channel – The malware used encrypted or obfuscated communications and payload handling (‘communication format … match what has been previously observed’).
- [T1132.001] Data Encoding: Standard Encoding – The campaign used encoded/structured HTTP endpoints and parameterized paths for control (‘/handshake’, ‘/command/
‘). - [T1568] Dynamic Resolution – The infrastructure rotated across multiple hardcoded C2 servers (‘rotates across 5 hardcoded C2 servers’).
- [T1567.002] Exfiltration Over Web Service – Data was likely exfiltrated via anonymous file-sharing services (‘likely exfiltrated via uploadnow[.]io’).
- [T1041] Exfiltration Over C2 Channel – Recon data and outputs were sent back to C2 servers (‘The reconnaissance output … is sent back to the C2’).
Indicators of Compromise
- [Domains/URLs] Dropbox-hosted payload delivery and file transfer – dropbox[.]com/scl/fi/[REDACTED]/vuzggemyofftzpk6.zip, uploadnow[.]io
- [IP addresses] Primary and secondary C2 infrastructure – 46.225.231[.]170, 144.172.99[.]68, and 64.94.85[.]158, plus 87.120.186[.]229 and 149.248.78[.]202
- [IP addresses] Reverse shell, proxy, and tunneling servers – 144.172.88[.]18, 64.190.113[.]187, and 45.59.122[.]231, plus 96.9.125[.]29 and 104.194.152[.]246
- [IP addresses] Additional tunneling endpoints – 207.246.114[.]50 and 149.28.96[.]170
- [File names] Python malware and payloads – Winp.zip, collector.py, Pmanager.py, internal.py, USOShared1297.py, Microsoft5237.py, Dell508.py, PCDr6967.py
- [File names] DLL payloads and exploit components – ssss.dll, testdllLPE.dll, com6848.dll, stage2.dll
- [File paths] Persistence and sync-root locations – %TEMP%cldfltLink.log, %TEMP%cldflt, %TEMP%configA.json
- [Hashes] Malware sample hashes – 930263c0843744e269b615fb2ec79f83d7bd8b2cbf75e31fd5ea6c1aaa4e48fd, b00c1cbcfb98d2618a5c2ccb311da94f3c57709a397be6c8de29839f4e943976, and f5b2dbd8ec9671c0261f093ebc5f3d35920b592458a3b800cc946265111e67d0
- [Tenant/account identifiers] Rogue Microsoft 365 tenant and impersonation artifacts – UCICasociacion.onmicrosoft[.]com, cdc15b4d-6fd6-4e90-9ee9-357fea475047
- [Registry keys/Cloud Files identifiers] Persistence and Cloud Files abuse – HKLMSOFTWAREMicrosoftWindowsCurrentVersionExplorerSyncRootManagerPLURIBUS!*, PLURIBUS, {904EE598-0511-4664-82A8-22C4A7501044}