The European Commission’s central mobile device management infrastructure was hit by a cyberattack on January 30 that may have exposed staff names and mobile numbers, but the system was contained and cleaned within nine hours with no compromise of mobile devices detected. Observers suspect a link to a Dutch campaign exploiting…
Tag: SUPPLY CHAIN

January 2026 saw 34 announced cybersecurity M&A deals, adding to a broader trend after more than 420 deals were cataloged in 2025. Major transactions include CrowdStrike’s acquisitions of SGNL and Seraphic, Delinea’s purchase of StrongDM, and several strategic buys across identity, cloud, API, and managed security services. #CrowdStrike #SGNL…

A single InfoStealer infection on a Lebanon-based machine likely owned by ISIS cell commander Qasura exposed years of encrypted XMPP chat logs, explosive synthesis manuals, and operational files that confirm IED attacks and cross-border logistics. The compromise allowed full mapping of the cell’s hierarchy, finances, smuggling routes, and sharia-sanctioned violence, showing how endpoint compromise can defeat messaging encryption. #InfoStealer #Qasura

KlearNow.AI, a US-based company, reports a ransomware incident in which the threat actor thegentlemen exfiltrated 3 TB of data, including two years of correspondence, a database dump, and all source code. They claim CBP declarations were filed for major clients such as BASF, Safran, and Sumitomo, while reiterating KlearNow.AI’s mission to simplify global trade with AI- and ML-driven logistics as a service #UnitedStates

This blog describes an automated, scalable cyber-range that uses Ludus to deploy multi-VM labs (GOAD and XZbot) and instruments every host with Elastic Agent/Defend to validate detections against real attacks. It details safe isolation techniques for running a live CVE-2024-3094 backdoor, shows how Elastic SIEM/XDR (Event Analyzer, Session Viewer) surfaces forensic “smoking guns,” and explains AI-driven hunting and response with Attack Discovery, the AI Assistant, and Elastic Workflows. #GOAD #XZbot

A ransomware claim targets Logility, a US-based provider of supply chain and retail planning solutions, attributed to the threat actor coinbasecartel. The claim indicates operational disruption and potential data exfiltration affecting Logility’s services.
#UnitedStates

Socket Threat Research discovered a coordinated supply chain attack that published malicious versions of the dYdX client libraries to npm and PyPI, embedding wallet-stealing credential exfiltration and, in the PyPI release, a Remote Access Trojan (RAT). The malicious packages exfiltrated seed phrases and device fingerprints to a typosquatting domain and the PyPI release used a 100-iteration obfuscation to deploy a RAT capable of arbitrary code execution and persistent access. #dYdX #priceoracle.site
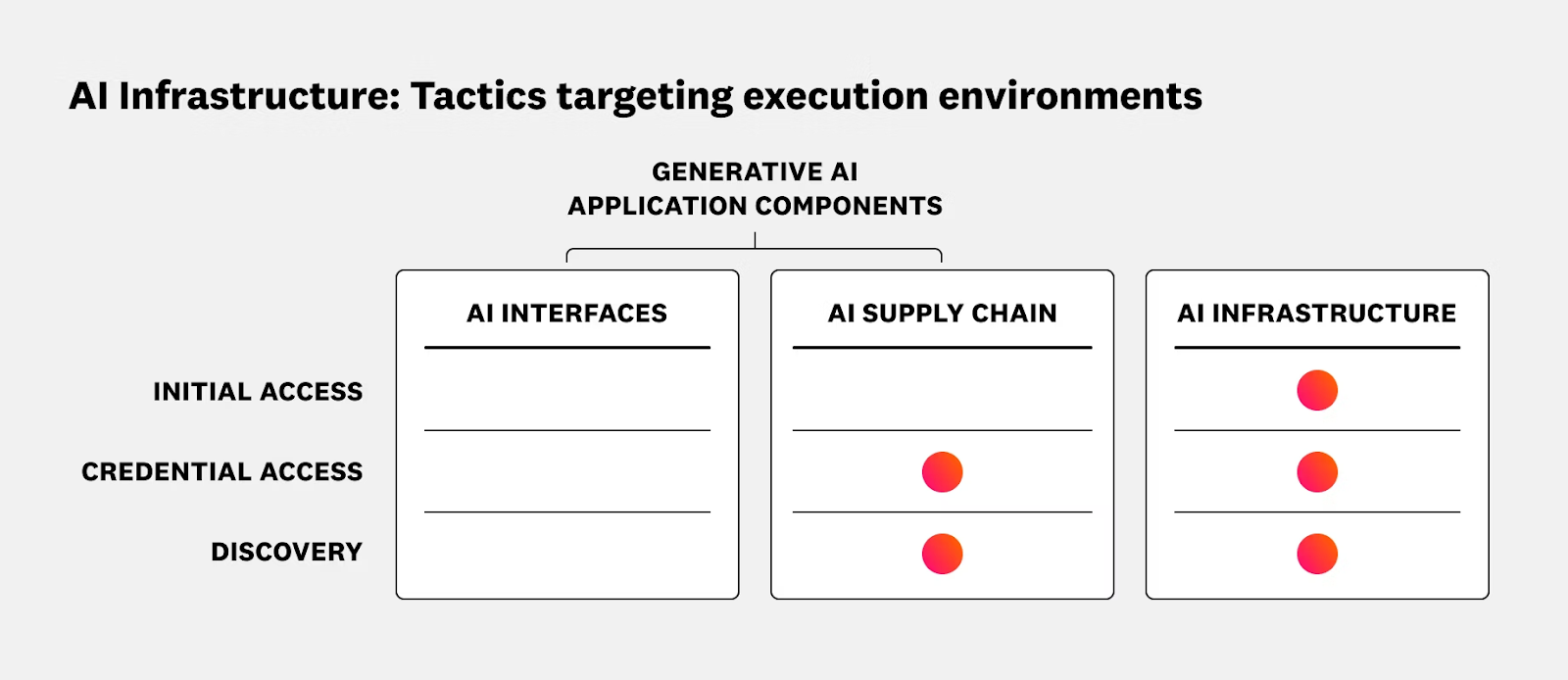
The article outlines security risks and operational best practices for running AI and ML workloads on Kubernetes and Oracle Cloud Infrastructure (OCI), emphasizing the shared responsibility model and the need to secure data planes, GPU nodes, inference services, and supply chains. It reviews recent AI-targeted incidents and promotes runtime protection, CI/CD hygiene, and integrated solutions such as Sysdig Secure with OKE to provide real-time detection and response. #ShadowRay2_0 #OCI
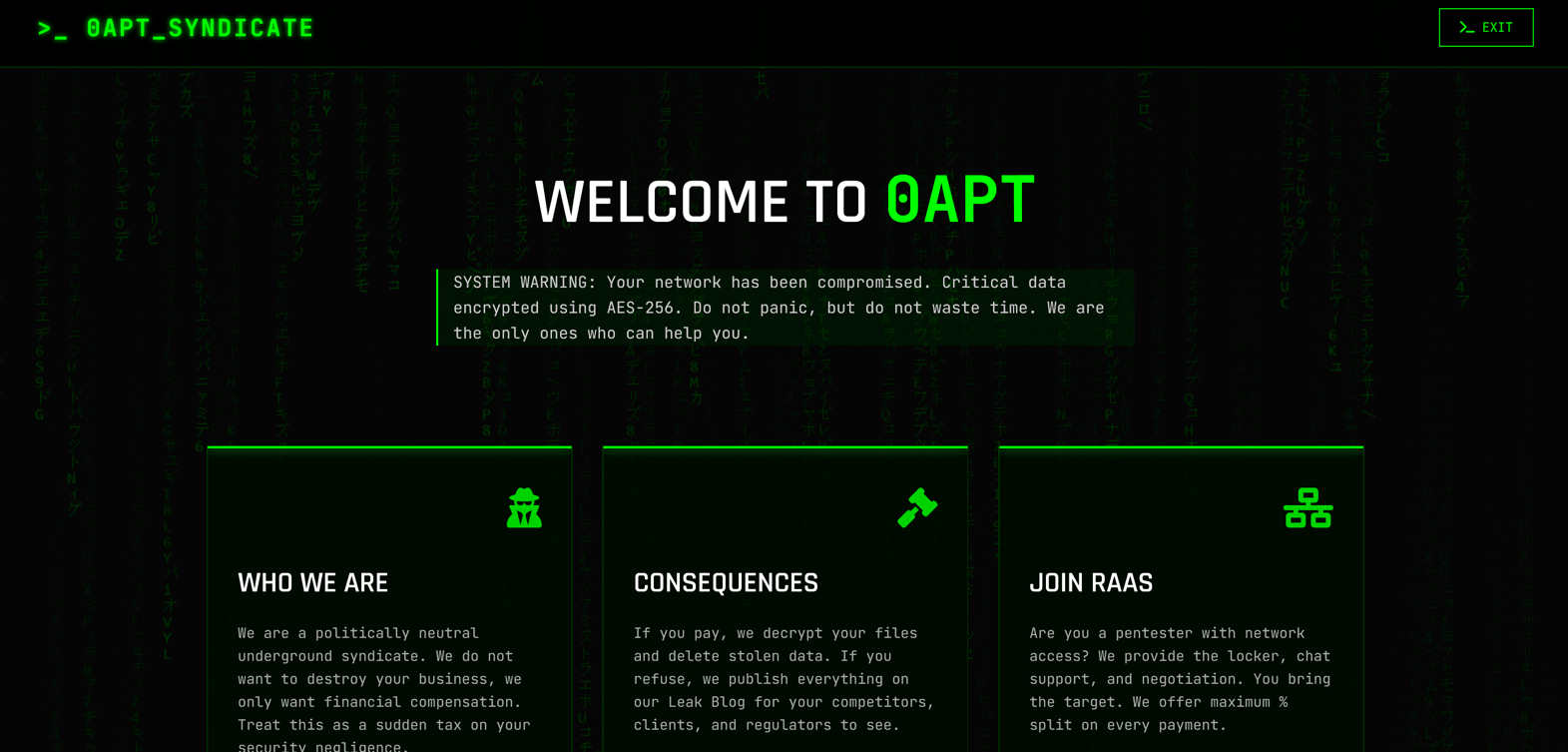
0APT surfaced in late January 2026 as a Ransomware-as-a-Service operation claiming hundreds of high-profile victims worldwide but rapid analysis has cast doubt on its technical capability. Evidence such as 0-byte dummy files, low-quality code and developer comments in Hindi/Urdu suggest 0APT may be a scam-as-a-service rather than a sophisticated ransomware cartel. #0APT #SolsticeEnergyGrid

Lotus Blossom has resurfaced with a sophisticated supply chain attack against the Notepad++ infrastructure and deployed a new custom backdoor called Chrysalis to spy on targets in Southeast Asia and Central America. The campaign uses a Warbird-protected loader, DLL side‑loading, commodity tools like Cobalt Strike, and undocumented system calls to evade…

Orca Security warns that GitHub Codespaces automatically executes VS Code–integrated configuration files when opening repositories or pull requests, creating a supply chain attack vector. Attackers can abuse .vscode files, devcontainer.json, and terminal variables to run commands, exfiltrate GitHub tokens and Codespaces secrets, and leverage vulnerabilities like “0.0.0.0 Day” to expand access….
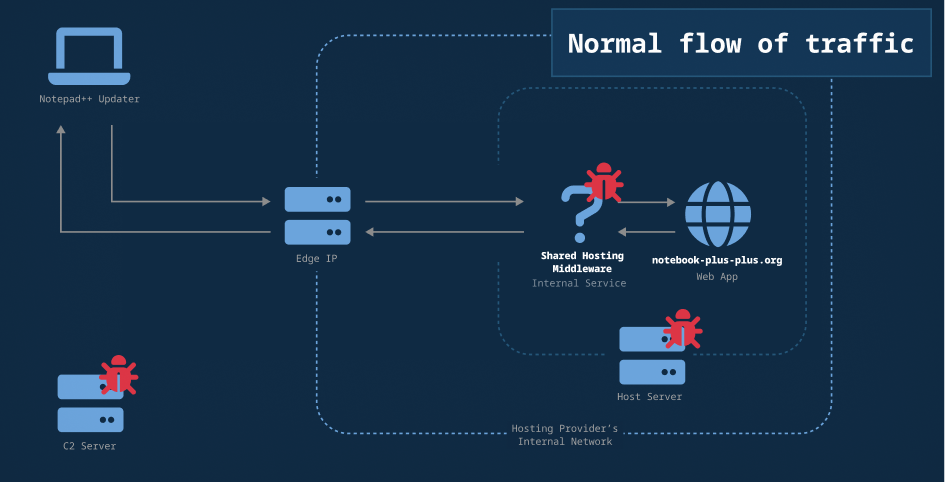
Researchers mapped additional network infrastructure and indicators linked to the February 2026 Notepad++ update-channel compromise, identifying C2 domains, Cobalt Strike beacon IPs, and likely malicious file-hosting addresses. Analysis shows the attackers used access to a shared hosting account to selectively redirect update traffic and deliver malicious payloads. #Notepad++ #CobaltStrike

Rui-Siang Lin, operating as “Pharaoh,” ran Incognito Market into a $105+ million darknet narcotics enterprise that facilitated hundreds of thousands of transactions and sold fentanyl-laced pills linked to at least one reported death. In March 2024 Lin was sentenced to 30 years, signaling that industrial-scale dark web marketplaces and their operators…
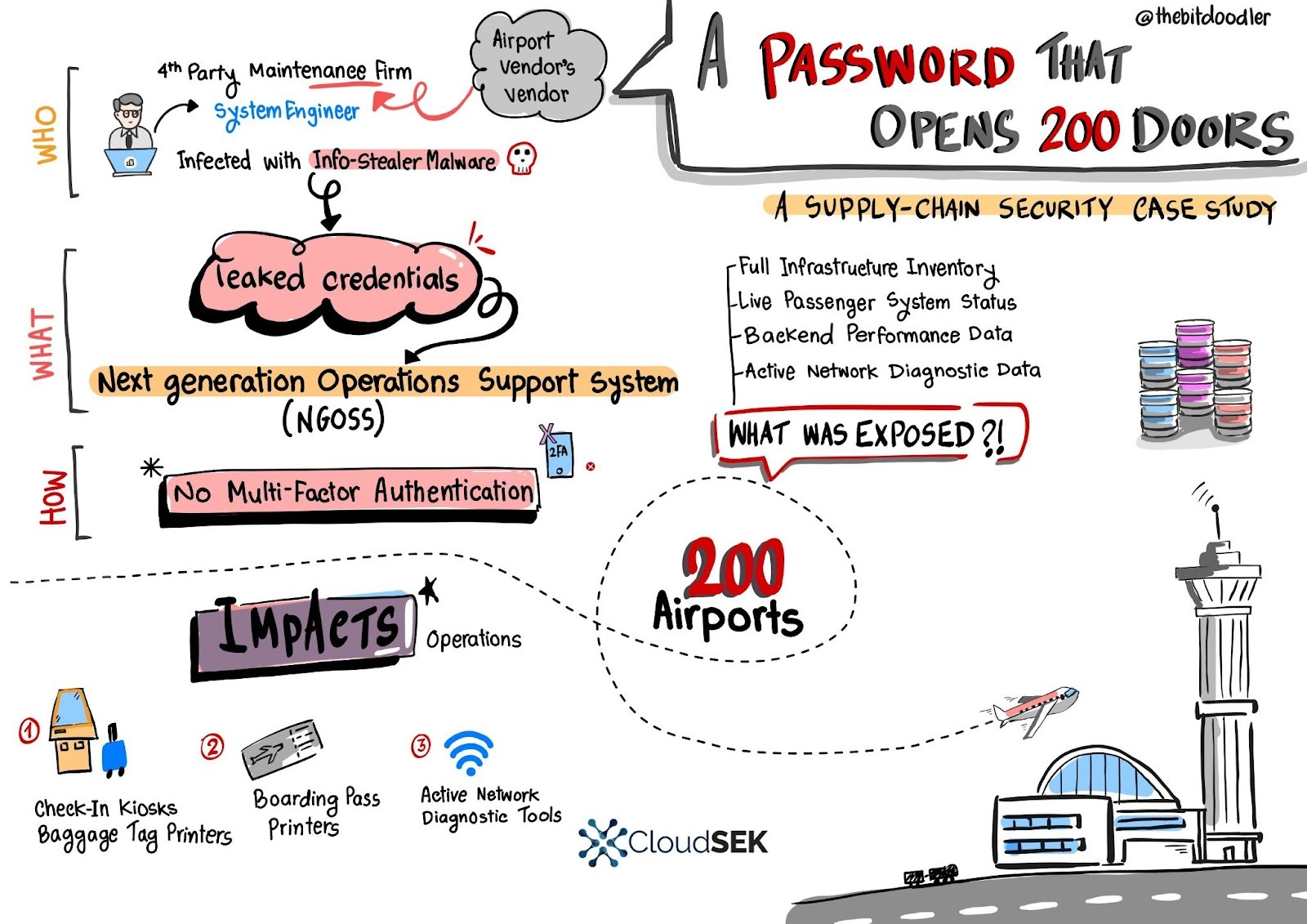
A single leaked username and password for a European fourth‑party engineer granted access to a central Next Generation Operations Support System (NGOSS) portal that managed operational dashboards for over 200 airports, exposing live infrastructure inventories, device statuses, and network diagnostic tools. SVigil detected the credential circulation and the vendor revoked access and enforced emergency MFA to avert potentially massive DoS and baggage-reconciliation outages. #SVigil #NGOSS

SecurityWeek’s Cyber Insights 2026 gathers experts who warn that cyberwarfare – driven by nation-state pre-positioning, AI-enabled operations, and rising geopolitical tensions – will escalate faster than criminal cybercrime in 2026. The report highlights blurred lines between criminal and state actors, the difficulty of attribution, and the need for improved detection, resilience,…
