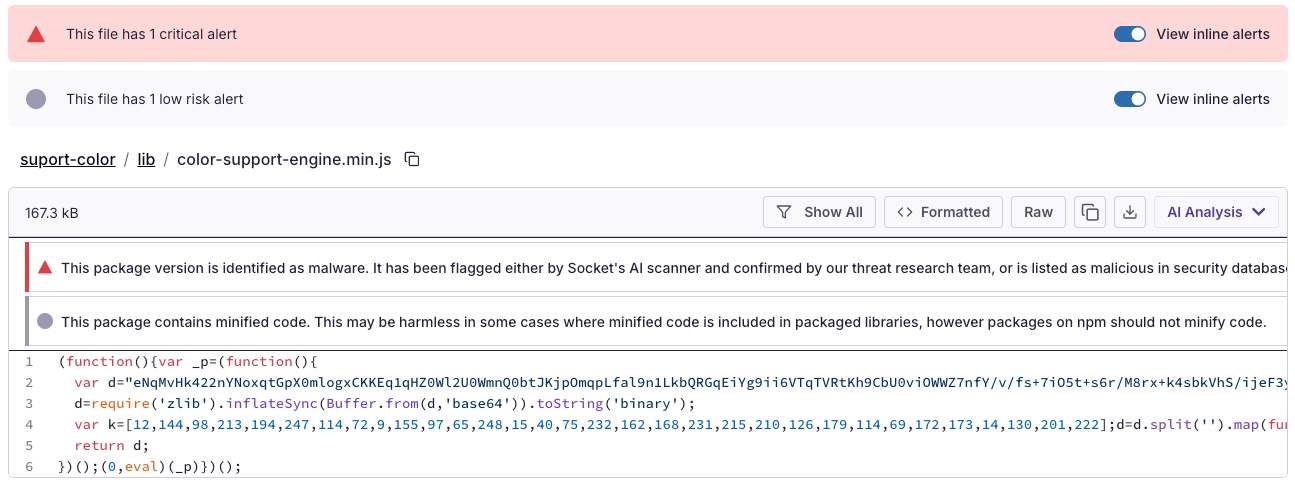
Socket’s Threat Research Team discovered a Shai-Hulud-like supply chain worm campaign tracked as SANDWORM_MODE that spread through at least 19 typosquatting npm packages and a malicious GitHub Action, harvesting developer and CI secrets, exfiltrating via HTTPS/GitHub API/DNS, and persisting via git hooks and MCP server injection targeting AI coding assistants. npm, GitHub, and Cloudflare removed related infrastructure, but defenders must treat the identified packages and injected workflows as active compromise risks and rotate/revoke affected tokens, audit global git templates, and inspect AI assistant configs for rogue MCP servers. #SANDWORM_MODE #suport-color
Tag: SUPPLY CHAIN

Businesses’ demand for speed and developers’ heavy workloads have undermined “shift left” security efforts, leading to unsafe use of public container images and loss of control over deployments. Qualys’ analysis of over 34,000 public images found roughly 7.3% malicious with many containing cryptominers and exposed secrets, prompting a recommendation to move security “down” into platform-level automation and golden paths. #DockerHub #AWS
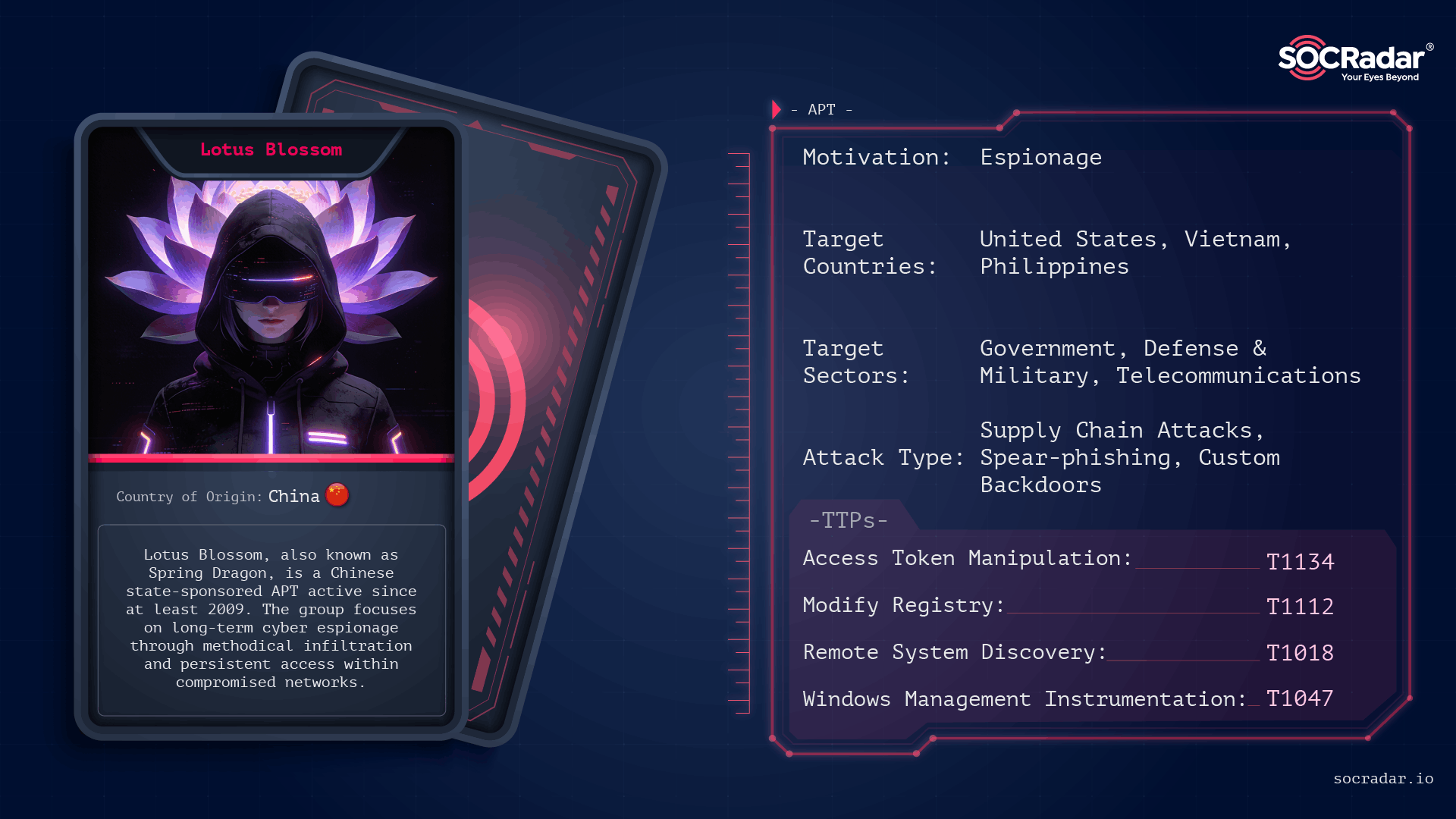
Lotus Blossom is a long-running, China-attributed APT that evolved from spear-phishing and watering-hole campaigns into sophisticated supply-chain compromises and targeted espionage using custom implants like Elise, Sagerunex, Hannotog, and Chrysalis. The group’s Notepad++ update-channel compromise and prior attacks against diplomatic, military, and maritime infrastructure demonstrate a “low-and-slow” intelligence collection approach emphasizing DLL sideloading, living-off-the-land techniques, and clandestine persistence. #LotusBlossom #Chrysalis
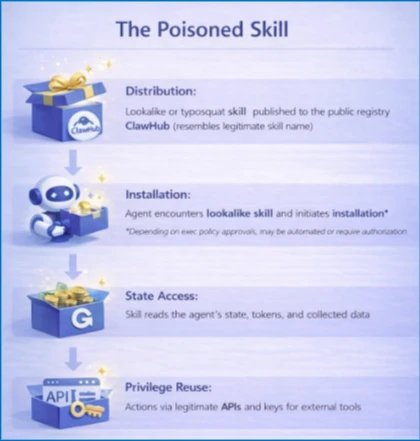
Self-hosted agent runtimes like OpenClaw significantly widen the execution boundary by ingesting untrusted text, downloading and executing external skills, and acting with the credentials of the host, creating risks of credential exposure, persistent memory manipulation, and host compromise. Organizations should treat OpenClaw as untrusted code execution and, if evaluated, run it only in isolated environments with dedicated non-privileged credentials, continuous monitoring, and a rebuild plan. #OpenClaw #Moltbook

Dragos’ 2025 report warns that three new OT-focused threat groups emerged while a Beijing-linked crew continued compromising cellular gateways, routers, and US electric, oil, and gas networks. The report details Voltzite’s long-term embedding in utility control systems, use of Sierra Wireless AirLink devices and the JDY botnet, and the roles of…

Security teams are overwhelmed by escalating attack volume and attacker throughput, making detection alone insufficient to prevent breaches. Operational Exposure Management — focusing on validated, reversible remediation — is required to shrink exposure dwell time and close the action gap. #ClickFix #Qilin

Researchers uncovered critical vulnerabilities in four widely used Visual Studio Code extensions — Live Server, Code Runner, Markdown Preview Enhanced, and Microsoft Live Preview — that together have been installed over 128 million times. OX Security warned these flaws could enable remote code execution, file exfiltration, and lateral movement from developer…
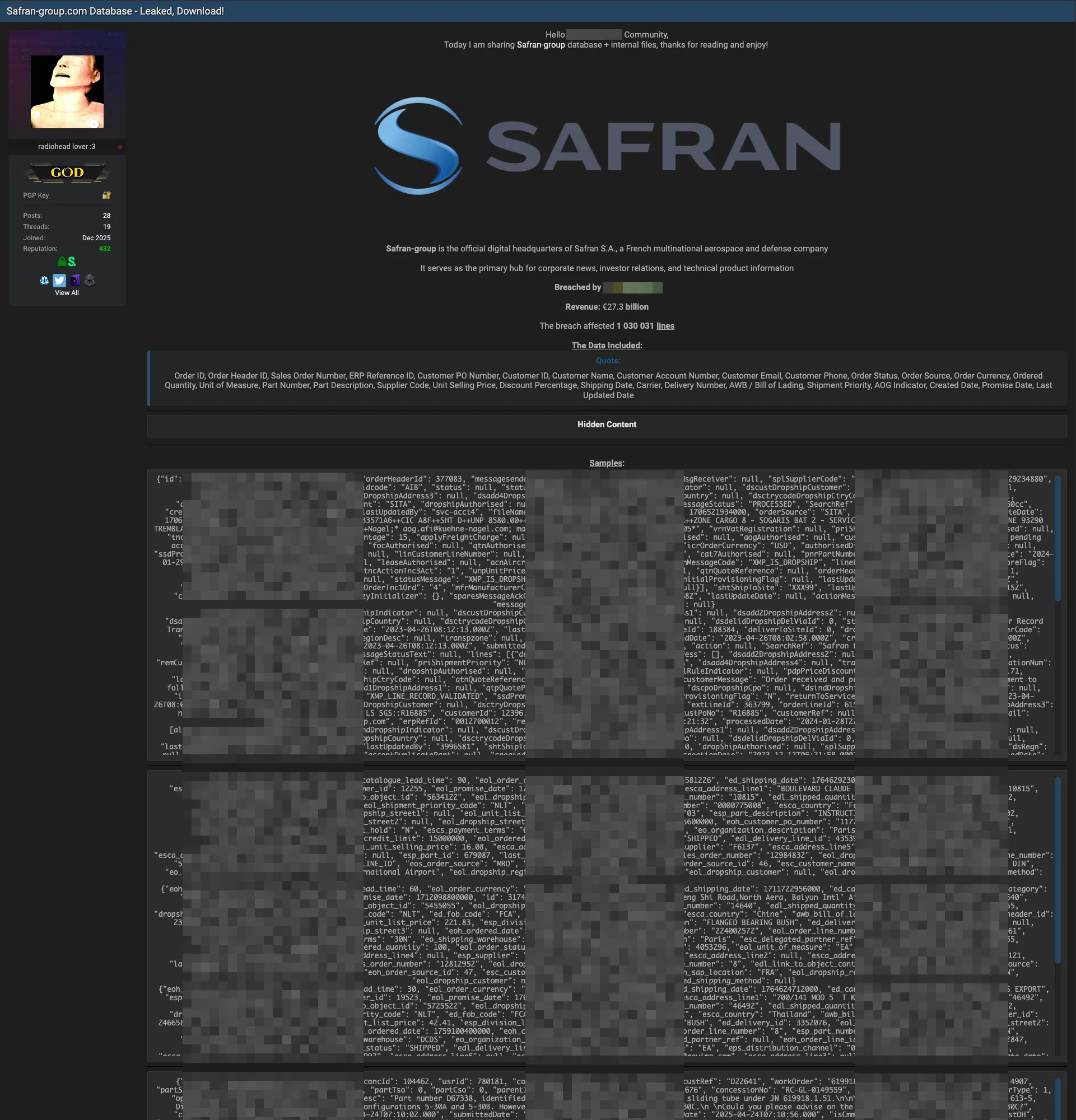
Safran S.A. has allegedly been breached after a threat actor posted 1,030,031 lines of the company’s database and internal files on a popular hacking forum. The leaked records reportedly include extensive customer, order, and supply-chain information such as names, contact details, ERP and order IDs, part numbers, prices, and shipping documents….

Attack Discovery, Workflows, and Agent Builder were combined to automatically detect, confirm, and triage a Chrysalis backdoor campaign delivered via a Notepad++ update supply-chain compromise, collapsing dozens of alerts into a single verified incident and creating a case and Slack channel with on-call responders already added. The automation verified C2, performed VirusTotal checks, ran ES|QL hunts, and executed incident actions (isolation, user suspension, IOC sweeps) in under four minutes instead of hours. #Chrysalis #LotusBlossom

Kaspersky researchers discovered a previously undocumented Android backdoor named Keenadu embedded in tablet firmware that can infect devices before they reach consumers and grant attackers virtually unrestricted control. The campaign, linked to advertising-fraud modules and found in devices from multiple manufacturers including Alldocube, resists standard Android removal methods and may require…

Palo Alto Networks has entered into a definitive agreement to acquire endpoint security company Koi, in a deal reported by Israeli outlets to be worth about $400 million. The acquisition aims to bring Koi’s agentic endpoint technology into Prisma AIRS and Cortex XDR to expand visibility and control over AI agents,…
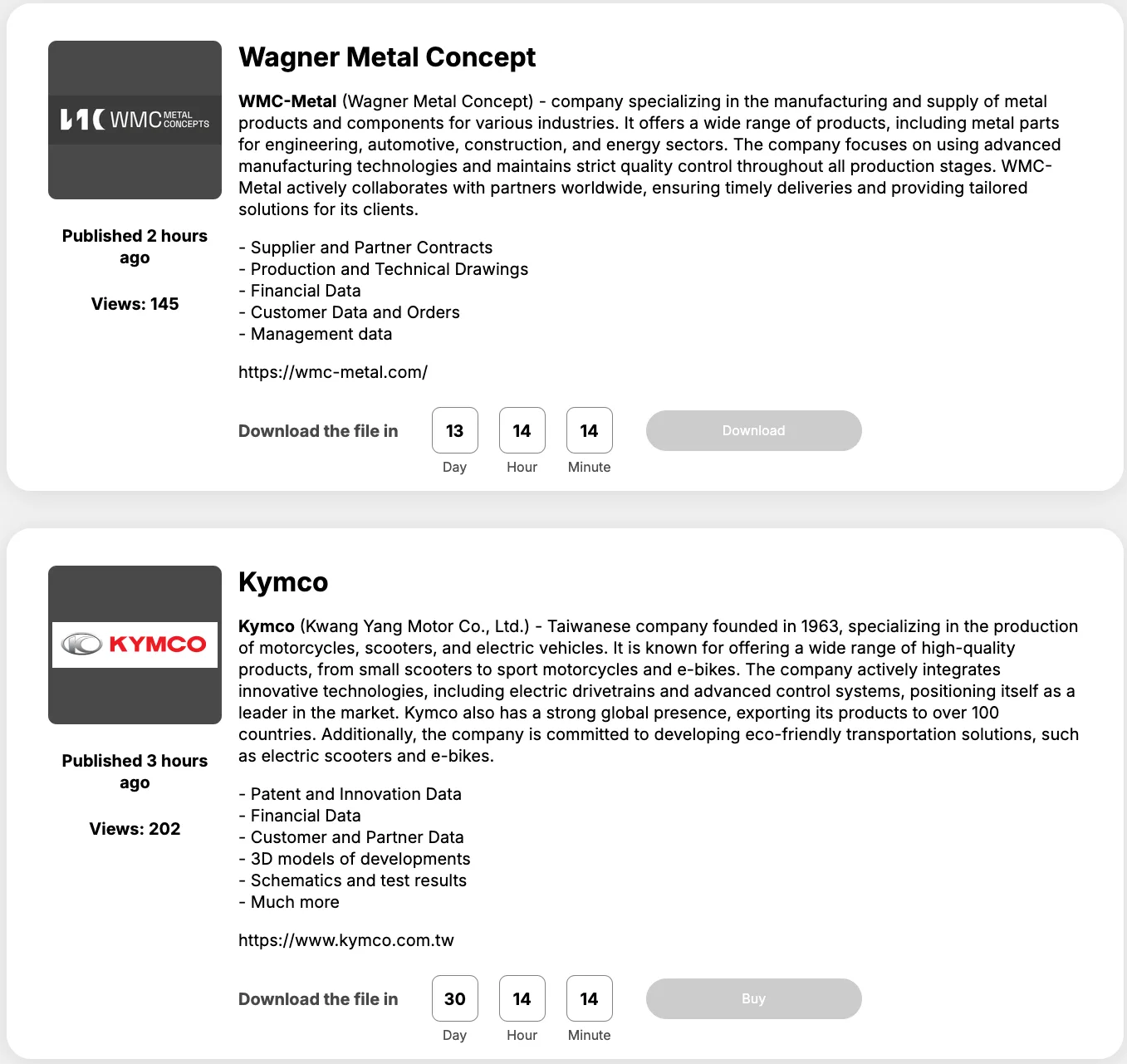
The Space Bears ransomware group claims to have compromised multiple organizations in a recent wave of data extortion attacks, posting an updated list of alleged victims. The group’s latest list names Wagner Metal Concept and Kymco and alleges theft of contracts, technical drawings, financial and customer data, patents, 3D models, and…

Keenadu is a newly discovered, highly sophisticated Android backdoor embedded in firmware across multiple device brands that can compromise every installed app and give attackers unrestricted control. Kaspersky reports multiple distribution methods — including compromised OTA firmware, system apps, modified APKs, and apps on Google Play — and has confirmed about 13,000 infected devices worldwide. #Keenadu #Kaspersky

Industrial Control Systems (ICS) remain highly vulnerable because decades‑old hardware, outdated protocols, and operators’ inability to accept downtime prevent effective patching and replacement amid growing nation‑state pre‑positioning and ransomware pressure. To build long‑term resilience in 2026, experts recommend OT‑aware zero trust, identity‑centric controls, microsegmentation, continuous threat exposure management (CTEM), supply‑chain transparency,…

The NCSC warns SMEs that assuming they are too small to be targeted is dangerous and urges urgent action through the UK government-backed Cyber Essentials baseline. Richard Horne stresses closing the awareness–action gap by implementing simple controls and using NCSC-assured support to reduce exposure to opportunistic automated attacks. #CyberEssentials #NCSC…