Cybersecurity Threat Research ‘Weekly’ Recap: This overview highlights infostealers, RATs, supply-chain and CI/AI toolchain compromises, vulnerabilities, ransomware activity, and phishing campaigns, featuring notable actors and families such as CharlieKirk, XWorm, SANDWORM_MODE, QakBot, and Lynx. It also emphasizes trends like AI-driven C2 abuse, adaptive phishing via Telegram, firmware and mobile backdoors, and notable incidents involving Dell RecoverPoint, Ivanti EPMM, BeyondTrust, and SolarWinds WHD. #CharlieKirk #ArkanixStealer #MIMICRAT #ClickFix #LunarApplication #XWorm #TrustConnect #DocConnect #Foxveil #GrayCharlie #AtlassianJira #SANDWORM_MODE #Notepad++ #LotusBlossom #Chrysalis #UNC6201 #DellRecoverPoint #BeyondTrust #IvantiEPMM #SolarWindsWHD #IngressNGINX #QakBot #SinobiRansomware #LynxRansomware #Keenadu #Velociraptor #Cloudflared #DaisyCloud #Redline
Tag: RAAS
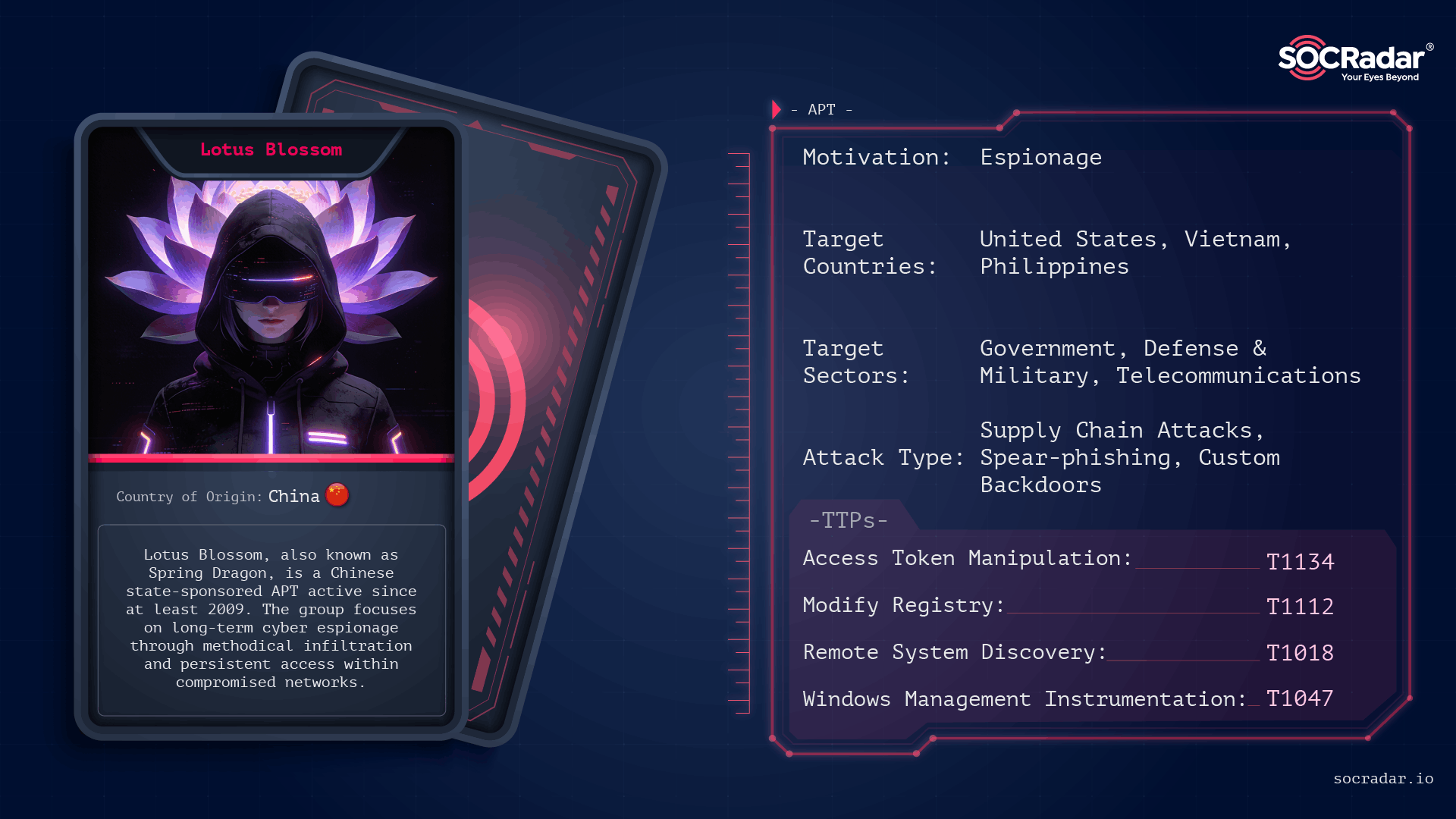
Lotus Blossom is a long-running, China-attributed APT that evolved from spear-phishing and watering-hole campaigns into sophisticated supply-chain compromises and targeted espionage using custom implants like Elise, Sagerunex, Hannotog, and Chrysalis. The group’s Notepad++ update-channel compromise and prior attacks against diplomatic, military, and maritime infrastructure demonstrate a “low-and-slow” intelligence collection approach emphasizing DLL sideloading, living-off-the-land techniques, and clandestine persistence. #LotusBlossom #Chrysalis

Security teams are overwhelmed by escalating attack volume and attacker throughput, making detection alone insufficient to prevent breaches. Operational Exposure Management — focusing on validated, reversible remediation — is required to shrink exposure dwell time and close the action gap. #ClickFix #Qilin

Sinobi is a Ransomware-as-a-Service operation that emerged in mid-2025 and appears to be a rebrand or successor to the Lynx and INC Ransom families based on significant code overlap. The group uses a closed affiliate model and double-extortion tactics—gaining access via compromised credentials and CVE exploits, exfiltrating data with Rclone, and encrypting files with Curve-25519/AES-128-CTR to demand payment. #Sinobi #Lynx

Polish police arrested a 47-year-old in the Małopolska region suspected of ties to the Phobos ransomware group and seized computers and phones containing stolen credentials, credit card numbers, and server access data. The arrest was part of Operation Aether, an international Europol-coordinated effort that has disrupted Phobos infrastructure, led to extraditions and server seizures, and warned hundreds of companies of imminent attacks. #Phobos #OperationAether
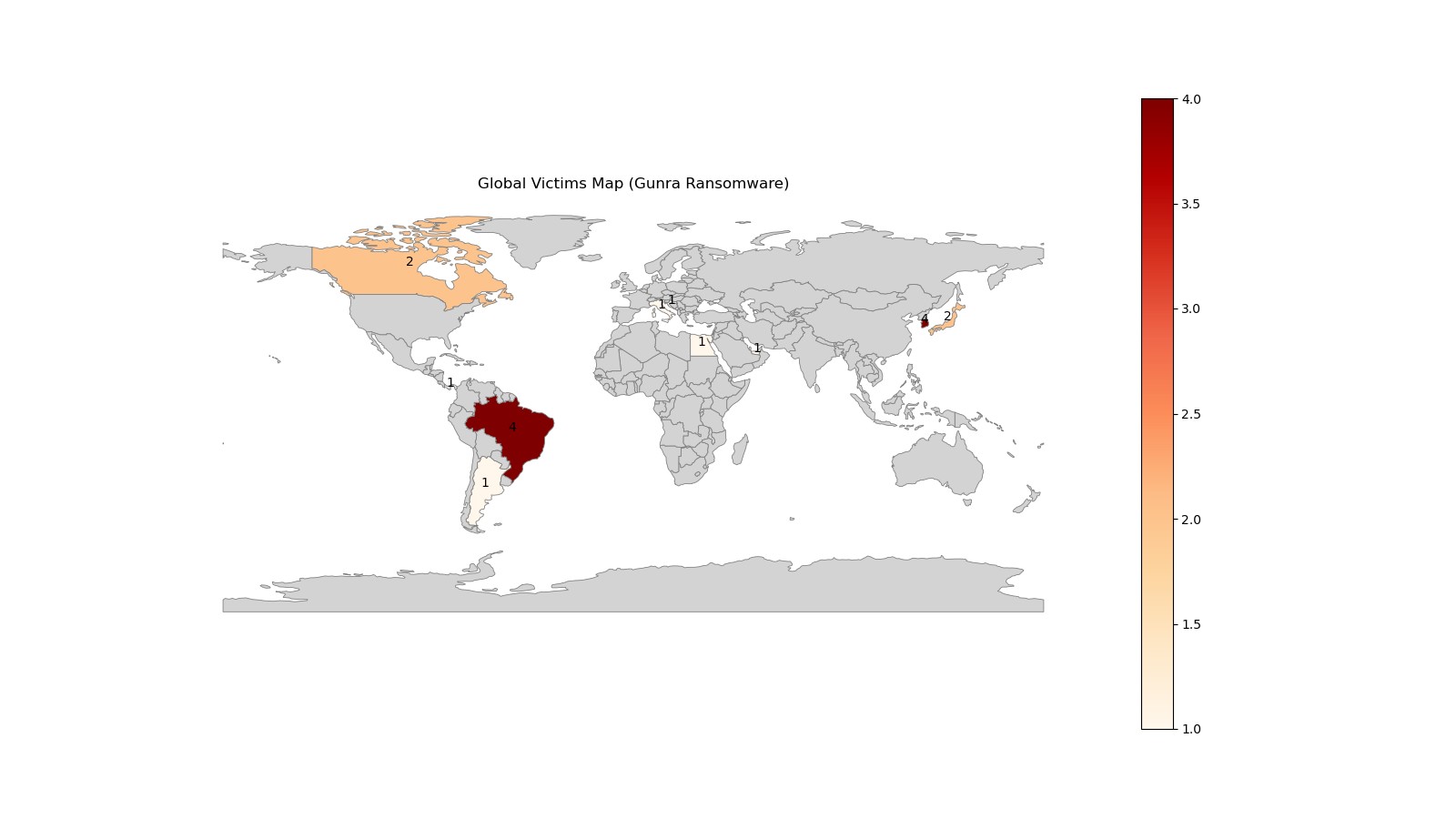
CloudSEK researchers infiltrated a newly launched Gunra affiliate program in January 2026, obtaining RaaS management panel credentials and a live ransomware sample for detailed technical analysis. The Gunra locker is an offline-capable, multi-threaded encryptor that uses per-file ChaCha20 keys protected with RSA-4096, selective system exclusions, .ENCRT renaming, and a Tor-based payment portal. #Gunra #CloudSEK
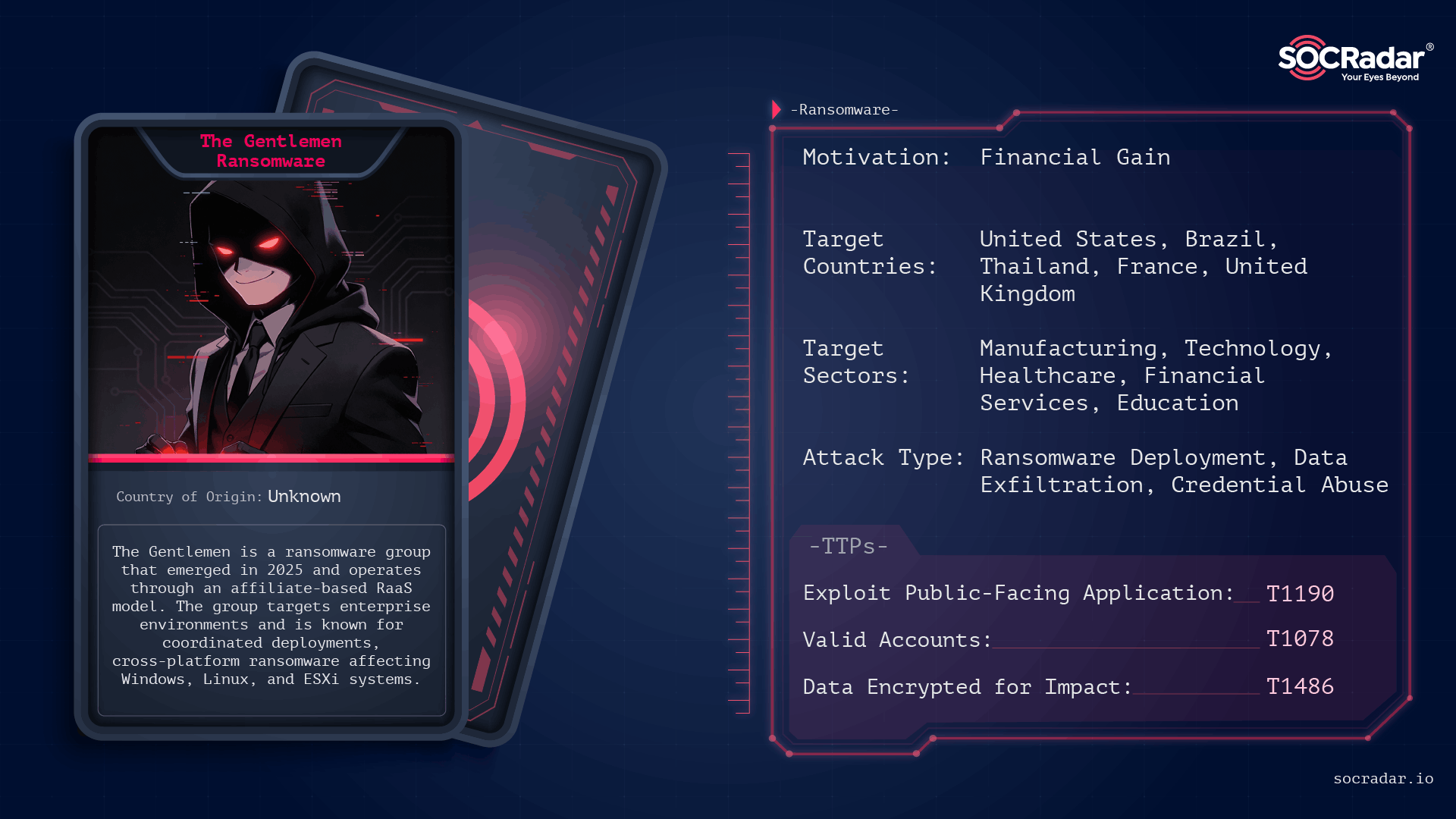
The Gentlemen is an operationally disciplined ransomware group first observed in mid-to-late 2025 that conducts double‑extortion attacks across Windows, Linux, NAS, BSD, and ESXi environments using password‑protected, operator-driven builds. Their campaigns leverage exposed internet-facing services and compromised administrative credentials, and victims have been publicly listed on a Dark Web leak site. #TheGentlemen #ESXi
Coveware’s report concludes that pure data-exfiltration extortion is no longer widely profitable, prompting many ransomware groups to return to encryption or seek other ways to monetize network access. Despite low overall payment rates after breaches like MOVEit and Cleo, average ransom settlements rose due to isolated high-impact incidents, and attackers such…

Conpet, Romania’s national oil pipeline operator, disclosed a cyberattack that disrupted its corporate IT systems and took down its website while operational systems remained functional. The Qilin ransomware gang claimed responsibility, alleging nearly 1TB of stolen data and posting leaked documents, and authorities including national cybersecurity bodies and DIICOT are investigating. #Conpet #Qilin
Ransomware operations are increasingly enabled by infostealers that harvest and sell credentials and session tokens to Initial Access Brokers, enabling validated enterprise access and rapid ransomware deployment often within 48 hours. This convergence compresses attacker dwell time, elevates credential-driven extortion risk, and demands stronger credential hygiene, endpoint visibility, and identity-focused defenses. #RedLine #Lumma
![Threat Research | Weekly Recap [22 Feb 2026] Threat Research | Weekly Recap [22 Feb 2026]](https://www.hendryadrian.com/tweet/image/WeeklyRecap.png)
Cybersecurity Threat Research ‘Weekly’ Recap: A sweeping roundup covers ransomware, Android threats, fileless tools, nation-state campaigns, cloud abuse, browser extension hijacks, supply-chain incidents, AI governance risks, and defensive improvements. It highlights actor-tool pairs and campaigns such as LockBit5.0, BravoX, Amnesia RAT, Arsink RAT, PlayCloak, PureRAT, PyRAT, GOGITTER, GITSHELLPAD, SheetCreep, VSCode tunnel, DarkSpectre, PayTool, SquarePhish2 and Graphish among others.
#LockBit5_0 #BravoX #AmnesiaRAT #ArsinkRAT #PlayCloak #PureRAT #PyRAT #GOGITTER #GITSHELLPAD #SheetCreep #VSCodeTunnel #DarkSpectre #PayTool #SquarePhish2 #Graphish

LockBit 5.0 is an evolved, cross-platform ransomware variant that uses the ChaCha20 256-bit stream cipher across Windows, Linux, and ESXi environments while adopting modular, stealthy behaviors to evade detection. The sample analyzed scored 1/65 on VirusTotal and the variant includes features such as in-memory execution, ETW patching, VSS Coordinator usage for shadow copy removal, and an irreversible hashing method for API/process resolution. #LockBit5.0 #ChaCha20
![Threat Research | Weekly Recap [22 Feb 2026] Threat Research | Weekly Recap [22 Feb 2026]](https://www.hendryadrian.com/tweet/image/WeeklyRecap.png)
Cybersecurity Threat Research ‘Weekly’ Recap: the report highlights AI‑generated malware frameworks like VoidLink, AI‑driven KONNI backdoors, real‑time LLM‑assembled phishing, and evolving ransomware such as AnubisRaaS and Osiris, alongside supply‑chain and watering‑hole compromises across multiple industries. It also covers state‑sponsored espionage, credential theft campaigns, and defensive insights for detection, telemetry, and incident response. #VoidLink #KONNI #AnubisRaaS #Osiris #CharmingKitten #APT28 #PurpleBravo #Evelyn
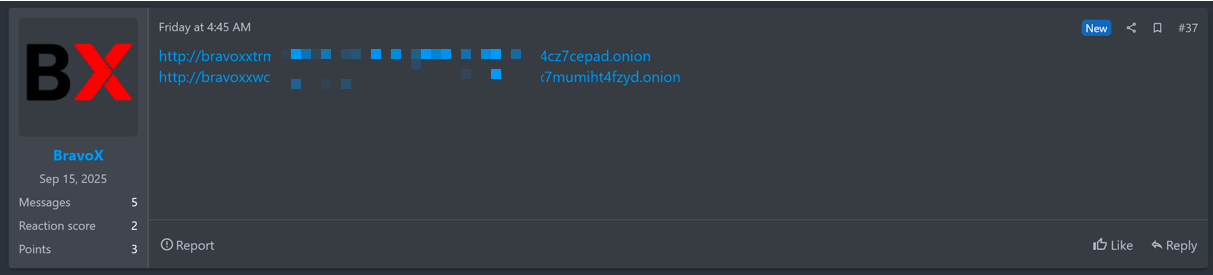
BravoX is a newly observed Ransomware-as-a-Service operation that publicly surfaced on January 23, 2026 after posting a Tor address on the RAMP forum and launching a TOR-based data leak site. The operation currently lists three alleged U.S. victims (two healthcare, one retail) and is advertising a selective affiliate model to scale its activities. #BravoX #RAMP
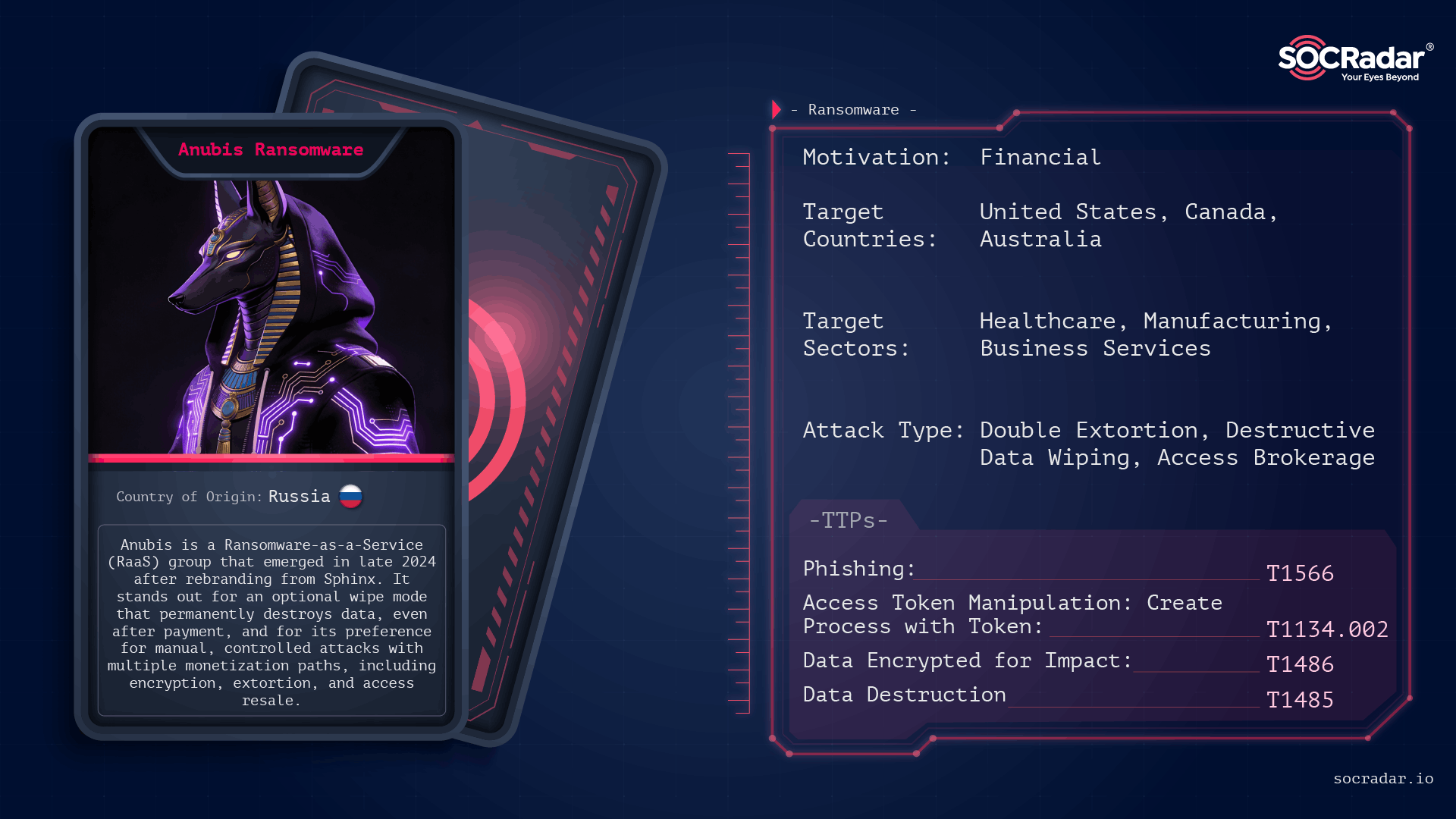
Anubis (formerly Sphinx) is a Ransomware-as-a-Service operation first observed in late 2024 that combines standard file encryption with an optional destructive wipe mode, permanently destroying data and removing decryption as a guaranteed outcome. Its affiliate-driven model and parallel monetization channels (data extortion and access resale) let operators choose between encryption, data-only extortion, or selling access, concentrating on high-value targets and controlled, high-impact intrusions. #Anubis #Sphinx