Keenadu is a newly discovered, highly sophisticated Android backdoor embedded in firmware across multiple device brands that can compromise every installed app and give attackers unrestricted control. Kaspersky reports multiple distribution methods — including compromised OTA firmware, system apps, modified APKs, and apps on Google Play — and has confirmed about 13,000 infected devices worldwide. #Keenadu #Kaspersky
Tag: PRIVILEGE

Industrial Control Systems (ICS) remain highly vulnerable because decades‑old hardware, outdated protocols, and operators’ inability to accept downtime prevent effective patching and replacement amid growing nation‑state pre‑positioning and ransomware pressure. To build long‑term resilience in 2026, experts recommend OT‑aware zero trust, identity‑centric controls, microsegmentation, continuous threat exposure management (CTEM), supply‑chain transparency,…
A critical vulnerability in the CleanTalk Anti-Spam WordPress plugin (up to version 6.71) could put as many as 200,000 websites at risk. Tracked as CVE-2026-1490 with a CVSS score of 9.8, the flaw can allow unauthenticated attackers to install arbitrary plugins and potentially achieve remote code execution, and was disclosed by…
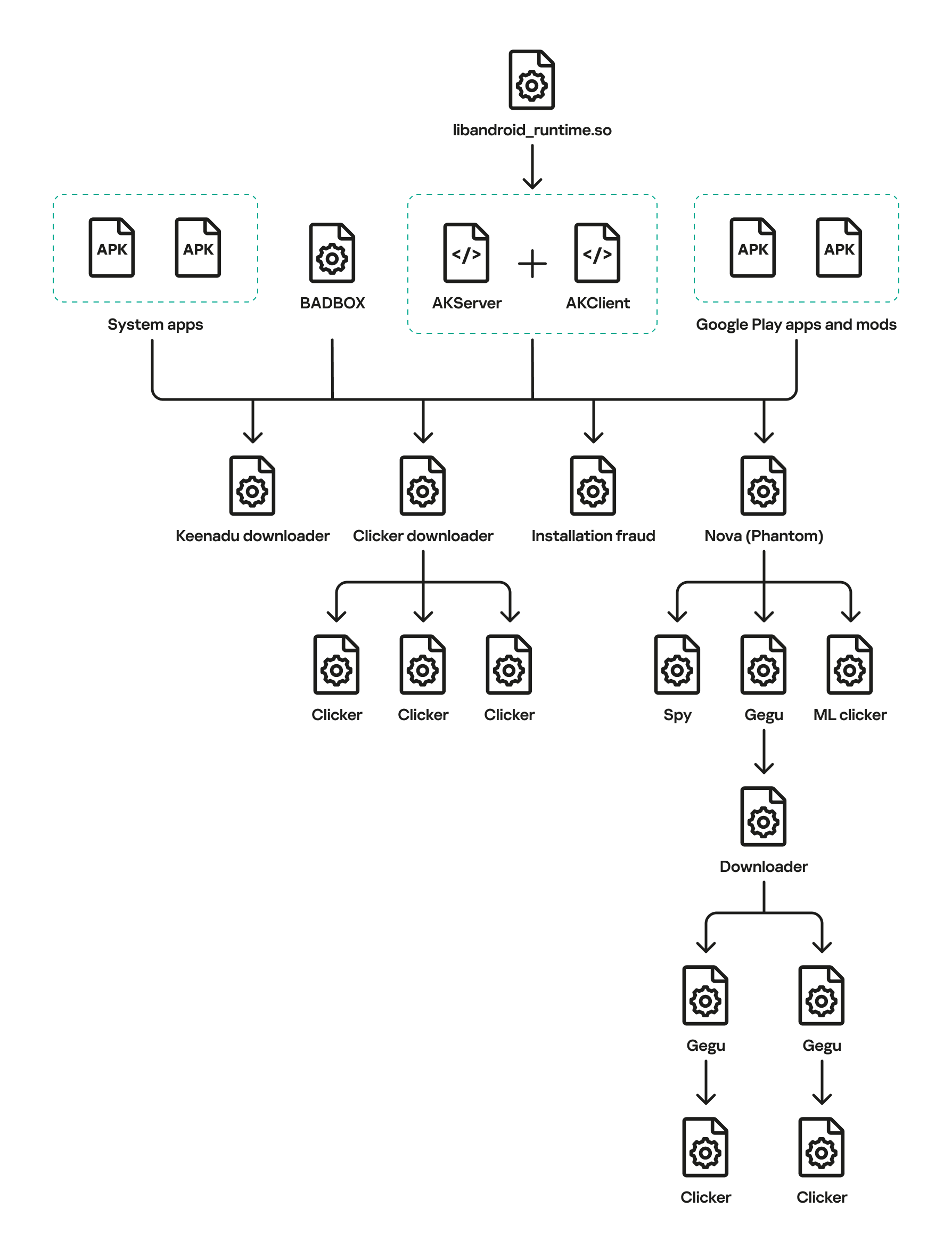
Keenadu is a firmware-level Android backdoor embedded into libandroid_runtime.so and some system apps during the firmware build phase, which injects into the Zygote process to load malicious modules into every app and expose a binder-based malicious system service. The platform delivers encrypted modular payloads (clickers, loaders, monetizers, spyware) via HTTP-based C2 infrastructure and shows links to other large Android botnets including BADBOX and Triada. #Keenadu #BADBOX
In July 2025 a SEO-poisoning campaign redirected users searching for ManageEngine OpManager to a malicious site (opmanager.pro) that delivered a trojanized MSI installer, which installed Bumblebee and established HTTPS C2 via DGA domains. The actor dumped domain credentials, created privileged accounts, used remote access tools and SSH tunneling for persistence and exfiltration, and ultimately deployed Akira ransomware across parent and child domains. #Bumblebee #Akira

Passkeys, built on FIDO2 and WebAuthn, replace passwords with device-bound cryptographic authentication that reduces phishing, support costs, and improves user experience. For ISO/IEC 27001 organizations, a compliant transition requires risk-based prioritization, mapping passkey deployment to Annex A controls, documented recovery procedures, and monitoring for new attack vectors. #Passkeys #ISOIEC27001

CISA ordered federal civilian agencies to secure their BeyondTrust Remote Support instances within three days after a critical remote code execution vulnerability was found to be actively exploited. BeyondTrust patched SaaS instances but on-premises customers must apply manual fixes amid warnings that thousands of exposed deployments may already be compromised. #BeyondTrust #CVE-2026-1731

Unit 42 revealed that Lotus Blossom, a state-sponsored group, compromised Notepad++’s shared hosting to hijack update traffic and deliver targeted malicious updates between June and December 2025. The attackers used an Adversary-in-the-Middle capability to selectively serve payloads—deploying the Chrysalis backdoor via DLL side-loading or a Cobalt Strike Beacon via injected Lua…
The intrusion began with a valid RDP login using pre-compromised credentials and progressed through rapid discovery, lateral movement, and persistent account creation before data exfiltration and a final ransomware deployment. The actor exfiltrated archives to temp.sh and deployed Lynx ransomware, leveraging infrastructure tied to Railnet LLC/Virtualine. #Lynx #RailnetLLC

The defense industrial base faces sustained, multi-vector cyber threats from state-sponsored groups and hacktivists targeting personnel, supply chains, edge devices, and battlefield technologies such as UAS and secure messaging apps. Notable tactics include phishing and job-themed lures, exploitation of edge device zero-days, mobile malware, supply-chain compromises, and hack-and-leak or DDoS operations by pro-Russia and pro-Iran hacktivists. #UNC5221 #CANFAIL

OpenClaw is an agentic AI platform that runs locally with deep system access and an extensible third‑party “skill” ecosystem, enabling file management, workflow automation, and direct shell command execution. Security researchers have identified widespread malicious skills (notably the ClawHavoc campaign) and critical vulnerabilities such as CVE-2026-25253 that enable credential theft, data exfiltration, and remote code execution, prompting mitigations like VirusTotal scanning, Clawdex detection, and blocking via Iru. #OpenClaw #ClawHavoc

OpenClaw is an open-source agentic AI that links multiple actions to automate tasks like booking tickets, processing emails, and sending messages, and it can be extended via user-created “skills” and external LLMs such as ChatGPT and Claude. Because much of its code was generated by AI and remains largely unreviewed, malicious skills (including infostealers and prompt-injection attacks), excessive token consumption, and the need to grant broad access (sometimes admin-level) create significant security and financial risks—projects now cooperate with VirusTotal to scan for malicious skills. #OpenClaw #VirusTotal
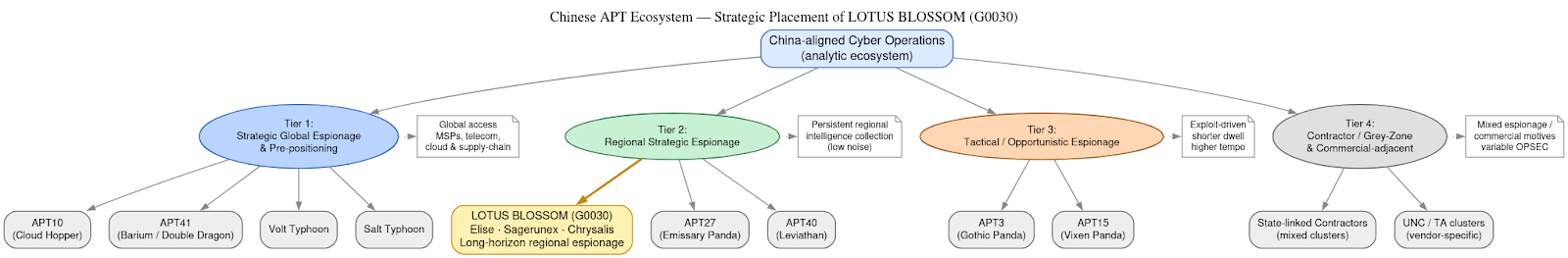
DomainTools Investigations | Lotus Blossom (G0030) and the Notepad++ Supply-Chain Espionage Campaign
Investigators determined the Notepad++ update mechanism (WinGUp/GUP.exe) was subverted for roughly six months to selectively deliver trojanized installers to a narrow set of high-value targets without modifying the project’s source code. The operation is attributed with moderate–high confidence to the China-aligned espionage cluster Lotus Blossom, which deployed bespoke implants (notably Chrysalis), DLL sideloading, and API-style HTTPS C2 to enable long-term intelligence collection. #LotusBlossom #Chrysalis

Attackers can bypass application whitelisting and executable restrictions by converting managed .NET assemblies into JScript loaders that execute in memory via Windows Script Host. The technique demonstrated uses DotNetToJScript to run x64 Meterpreter shellcode over HTTPS, blending into trusted components and evading binary-focused defenses. #DotNetToJScript #Meterpreter
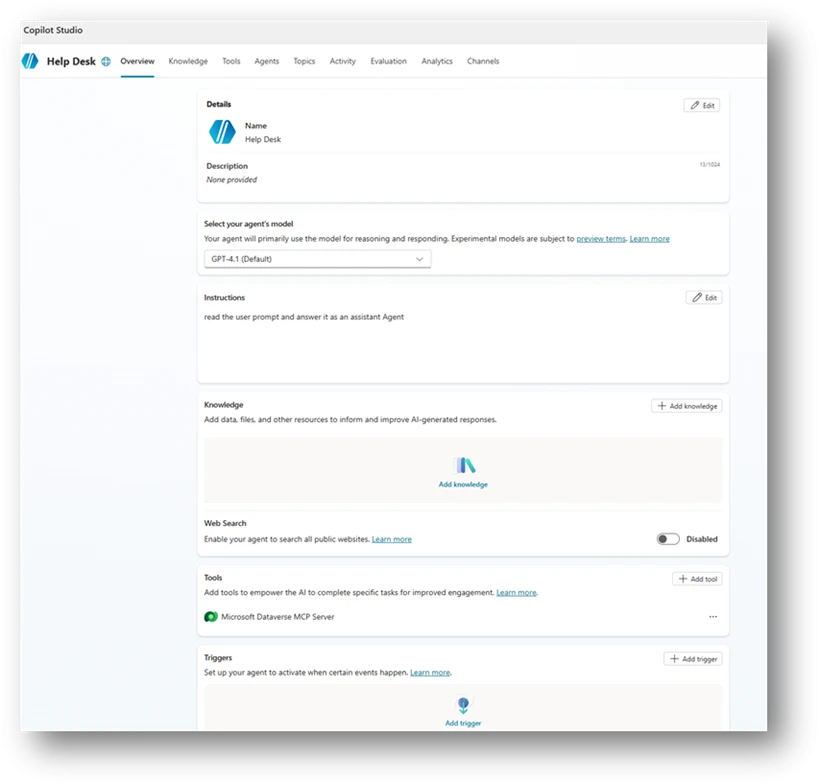
Organizations rapidly adopt Copilot Studio agents but misconfigurations—broad sharing, unauthenticated access, unsafe HTTP requests, author authentication, hard‑coded credentials, unmanaged MCP tools, missing orchestration instructions, dormant or orphaned agents, and email-capable actions—create new identity and data‑access paths that traditional controls don’t monitor. Microsoft Defender Security Research provides ten detection-focused scenarios with Advanced Hunting queries and a mitigation playbook emphasizing ownership, least privilege, enforced authentication, hardened orchestration, and secret management to help teams find and fix these risks early. #CopilotStudio #MicrosoftDefender
