France’s Ministry of Economy disclosed a breach of the national bank account registry FICOBA that exposed information on 1.2 million accounts after an official’s credentials were stolen. The intrusion occurred in late January, the attacker’s access has been terminated, and affected individuals are being notified but warned about potential scams and…
Tag: PRIVILEGE

Security teams are overwhelmed by escalating attack volume and attacker throughput, making detection alone insufficient to prevent breaches. Operational Exposure Management — focusing on validated, reversible remediation — is required to shrink exposure dwell time and close the action gap. #ClickFix #Qilin

Researchers uncovered critical vulnerabilities in four widely used Visual Studio Code extensions — Live Server, Code Runner, Markdown Preview Enhanced, and Microsoft Live Preview — that together have been installed over 128 million times. OX Security warned these flaws could enable remote code execution, file exfiltration, and lateral movement from developer…
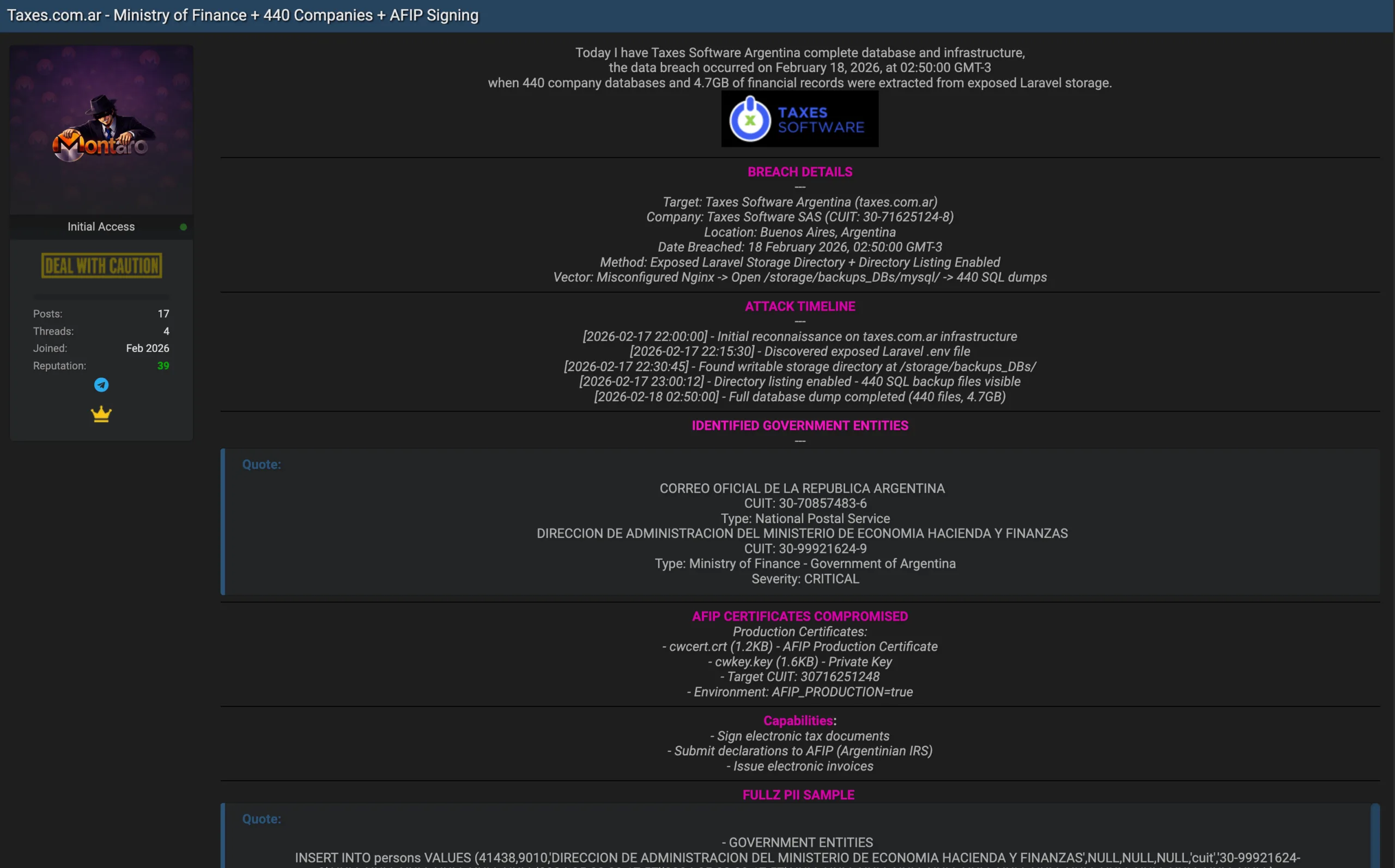
Taxes Software Argentina, a Buenos Aires-based tax management software provider, has reportedly been compromised, exposing internal infrastructure and sensitive data for 440 client companies. The threat actor claims to have exploited a misconfigured Nginx server and an exposed Laravel storage directory to leak a 4.7 GB database dump containing AFIP certificates…

The article describes how a mature underground access economy commoditizes remote credentials, infostealer logs, breach databases, and web shells, letting specialists trade and monetize each part of the attack chain. This industrialized market features products like Fortinet VPN credentials, infostealer families (e.g., Redline), and operators such as DAISY CLOUD that sell…

Researchers at Forcepoint X-labs found a campaign targeting organisations in the UK, US, Canada, and Northern Ireland where attackers impersonate the US Social Security Administration to trick users into running a malicious .cmd script. The script disables Windows defenses, hides payloads using Alternate Data Streams, and silently installs ConnectWise ScreenConnect as…

Researchers disclosed a critical unauthenticated stack-based buffer overflow in Grandstream GXP1600-series VoIP phones that can enable remote code execution with root privileges. Tracked as CVE-2026-2329 with a CVSS score of 9.3, the flaw resides in the web API (/cgi-bin/api.values.get), affects multiple GXP16xx models, and was patched in firmware 1.0.7.81. #CVE-2026-2329 #GrandstreamGXP1600…

A Chinese state-backed hacking group has been exploiting a critical zero-day in Dell RecoverPoint for Virtual Machines (CVE-2026-22769) since at least mid-2024 to deploy backdoors and target organizations across North America. Dell, Google/Mandiant and U.S. agencies have issued advisories and fixes, and CISA ordered immediate federal patching while researchers report use…

Flare researchers observed threat actors rapidly sharing proof-of-concept exploits, offensive tools, and stolen administrator credentials for SmarterMail vulnerabilities CVE-2026-24423 and CVE-2026-23760, leading to automated mass exploitation and confirmed ransomware activity. Incidents including a SmarterTools breach and ties to the Warlock cluster highlight that email servers are identity-critical and require urgent patching, segmentation, and enhanced monitoring. #SmarterMail #CVE-2026-24423

CISA warned that a vulnerability in TeamT5’s ThreatSonar Anti-Ransomware (CVE-2024-7694) has been exploited in the wild and was added to the Known Exploited Vulnerabilities catalog. The high-severity arbitrary file-upload flaw was patched in August 2024, but CISA ordered federal agencies to remediate it by March 10 due to the product’s use…
Two sentences summarizing the content. Threat actors quickly weaponized two Ivanti EPMM zero-days (CVE-2026-1281 and CVE-2026-1340) to achieve unauthenticated remote code execution via a bash arithmetic expansion trick, enabling rapid deployment of web shells and persistent backdoors. Over 4,400 internet-facing EPMM instances were identified across multiple sectors and countries, prompting CISA…

Acronis TRU uncovered a targeted espionage campaign named CRESCENTHARVEST that uses Farsi-language protest lures to trick victims into opening malicious .LNK shortcuts and install a multi-module stealer/RAT. The implant chain relies on DLL sideloading via a signed Google binary, extracts browser app‑bound keys, logs keystrokes and exfiltrates data to a C2 in Riga. #CRESCENTHARVEST #AcronisTRU

Kaspersky discovered a sophisticated Android backdoor named Keenadu embedded in device firmware that can silently harvest data and remotely control infected tablets. The backdoor is injected via libandroid_runtime.so into the Zygote process, uses a client-server AKServer/AKClient architecture to load malicious modules, and has been observed in Alldocube firmware and other undisclosed…

Cloud attacks move faster than traditional incident response can handle, with short-lived instances, rotating identities, and expiring logs that can erase evidence in minutes. Automated, context-aware forensics that correlates workload telemetry, identity activity, API operations, network movement, and asset relationships lets teams reconstruct attack timelines in minutes and respond decisively. #ContextAwareForensics…

Sinobi is a Ransomware-as-a-Service operation that emerged in mid-2025 and appears to be a rebrand or successor to the Lynx and INC Ransom families based on significant code overlap. The group uses a closed affiliate model and double-extortion tactics—gaining access via compromised credentials and CVE exploits, exfiltrating data with Rclone, and encrypting files with Curve-25519/AES-128-CTR to demand payment. #Sinobi #Lynx
