Cloud migrations often create visibility blind spots, and network-layer telemetry combined with Network Detection and Response (NDR) provides consistent, provider-agnostic visibility for detecting threats in multi- and hybrid-cloud environments. The article recommends enabling flow logs and traffic mirroring, standardizing and enriching telemetry with cloud inventory, and tuning baselines to detect threats such as coinminer beaconing, stolen credentials, and suspicious interactive admin activity. #Corelight #Kubernetes
Tag: LATERAL MOVEMENT

Researchers at Tenable disclosed two critical vulnerabilities called “LookOut” that can enable remote code execution and the theft of Looker’s internal management database, risking full system takeover and exposure of sensitive corporate data. Organizations running self-hosted Looker must apply patches immediately while Google has secured its managed cloud; #LookOut #GoogleLooker…
Unit 42 attributes a large-scale, state-aligned cyberespionage campaign — tracked as TGR-STA-1030 and called the Shadow Campaigns — to an Asia-based actor that has compromised government and critical infrastructure across 37 countries using phishing, exploitation, C2 frameworks and a novel eBPF rootkit. The group used tools including Diaoyu Loader, Cobalt Strike,…

Sysdig TRT observed a rapid offensive cloud operation where an attacker obtained credentials from public S3 buckets, injected code into an AWS Lambda (EC2-init) to create admin access keys, moved laterally across 19 AWS principals, abused Amazon Bedrock models, and provisioned GPU instances for model training or resale. The operation contained multiple indicators of LLM assistance—LLM-generated code with Serbian comments, hallucinated AWS account IDs and a non-existent GitHub repo—and the report outlines detection opportunities and mitigation recommendations. #AmazonBedrock #AWSLambda
A newly disclosed critical vulnerability in the vLLM Python package (CVE-2026-22778) allows remote code execution by submitting a malicious video URL to multimodal API endpoints, putting millions of AI servers at risk. The flaw stems from a PIL memory-address disclosure combined with a JPEG2000 heap overflow in FFmpeg (bundled with OpenCV);…

MS-ISAC reporting shows total malware notifications rose 7% from Q3 to Q4 2025, with SocGholish accounting for 30% of detections and CoinMiner and Agent Tesla also prominent. New and returning families observed include ACR Stealer, Calendaromatic, SombRAT, and Arechclient2, with notable vectors like malvertisement, malspam, WMI-based spread, and multiple persistence and…
![Cybersecurity News | Daily Recap [02 Feb 2026] Cybersecurity News | Daily Recap [02 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, Britain and Japan agreed to deepen a cyber strategic partnership to boost cybersecurity and secure critical mineral supply chains, while India unveiled a long-term digital strategy in Union Budget 2026–27 prioritizing AI, cloud, semiconductors, data centers and integrated cybersecurity including a tax holiday until 2047 to attract foreign cloud providers. The roundup also highlights a spate of incidents from piracy takedowns in Bulgaria to MongoDB data extortion involving over 1,400 databases, the OpenVSX supply-chain attack delivering the GlassWorm loader exfiltrating macOS credentials, a multi-stage eScan compromise, UAT-8099 region-locked BadIIS campaigns, NationStates data breach, Microsoft planning NTLM deprecation in favor of Kerberos, and the rise of autonomous threat tooling led by OpenClaw, Moltbook and Molt Road. #GlassWorm #OpenVSX #eScan #UAT-8099 #BadIIS #NationStates #NTLM #Kerberos #OpenClaw #Moltbook #MoltRoad #MongoDB #macOS #Solana #EtherHiding

SecurityWeek’s Cyber Insights 2026 warns that agentic AI will increasingly automate and accelerate the entire cyberattack lifecycle, enabling one-click, adaptive, and highly targeted intrusions that blur the line between code and conversation. Organizations must double down on foundational cyber hygiene and adopt behavioral, AI-aware defenses to detect and remediate automated, identity-led,…

GlassWorm has resurfaced on the Open VSX marketplace after a publisher account was compromised in a supply chain attack that published poisoned updates to four popular VS Code extensions. The macOS-focused loader uses runtime-decrypted code and Solana transaction memos for C&C to steal developer credentials, browser and wallet data, and exfiltrate…

Mandiant describes an expansion of ShinyHunters-branded extortion operations that leverage vishing and victim-branded credential harvesting to compromise single sign‑on (SSO) credentials and enroll unauthorized devices into victim MFA, enabling access to cloud SaaS environments. Immediate containment (revoke sessions, pause MFA registration, restrict password resets) plus long‑term hardening (phishing‑resistant MFA, IdP/SaaS logging and detections) are recommended to stop exfiltration and persistence. #ShinyHunters #Okta

Quest KACE Desktop Authority exposes a SYSTEM-owned named pipe (.pipeScriptLogic_Server_NamedPipe_9300) that accepts connections from any authenticated domain user and implements a custom MFC CArchive-based IPC protocol allowing remote privileged operations. The protocol supports AdminExec, DllInjection, Credentials retrieval, InvokeCOM and other dangerous actions that enable remote code execution and credential exposure; apply vendor patches or firewall/segmentation mitigations. #QuestKACE #CVE-2025-67813

Researchers disclosed a supply chain attack on the Open VSX Registry where attackers used a compromised developer account (oorzc) to publish four malicious extension updates that delivered the GlassWorm loader. The loader uses EtherHiding, runtime decryption, and Solana memos to fetch C2 and exfiltrate macOS credentials, browser data, and cryptocurrency wallet…
Ransomware operations are increasingly enabled by infostealers that harvest and sell credentials and session tokens to Initial Access Brokers, enabling validated enterprise access and rapid ransomware deployment often within 48 hours. This convergence compresses attacker dwell time, elevates credential-driven extortion risk, and demands stronger credential hygiene, endpoint visibility, and identity-focused defenses. #RedLine #Lumma
![Threat Research | Weekly Recap [01 Feb 2026] Threat Research | Weekly Recap [01 Feb 2026]](https://www.hendryadrian.com/tweet/image/WeeklyRecap.png)
Cybersecurity Threat Research ‘Weekly’ Recap: A sweeping roundup covers ransomware, Android threats, fileless tools, nation-state campaigns, cloud abuse, browser extension hijacks, supply-chain incidents, AI governance risks, and defensive improvements. It highlights actor-tool pairs and campaigns such as LockBit5.0, BravoX, Amnesia RAT, Arsink RAT, PlayCloak, PureRAT, PyRAT, GOGITTER, GITSHELLPAD, SheetCreep, VSCode tunnel, DarkSpectre, PayTool, SquarePhish2 and Graphish among others.
#LockBit5_0 #BravoX #AmnesiaRAT #ArsinkRAT #PlayCloak #PureRAT #PyRAT #GOGITTER #GITSHELLPAD #SheetCreep #VSCodeTunnel #DarkSpectre #PayTool #SquarePhish2 #Graphish
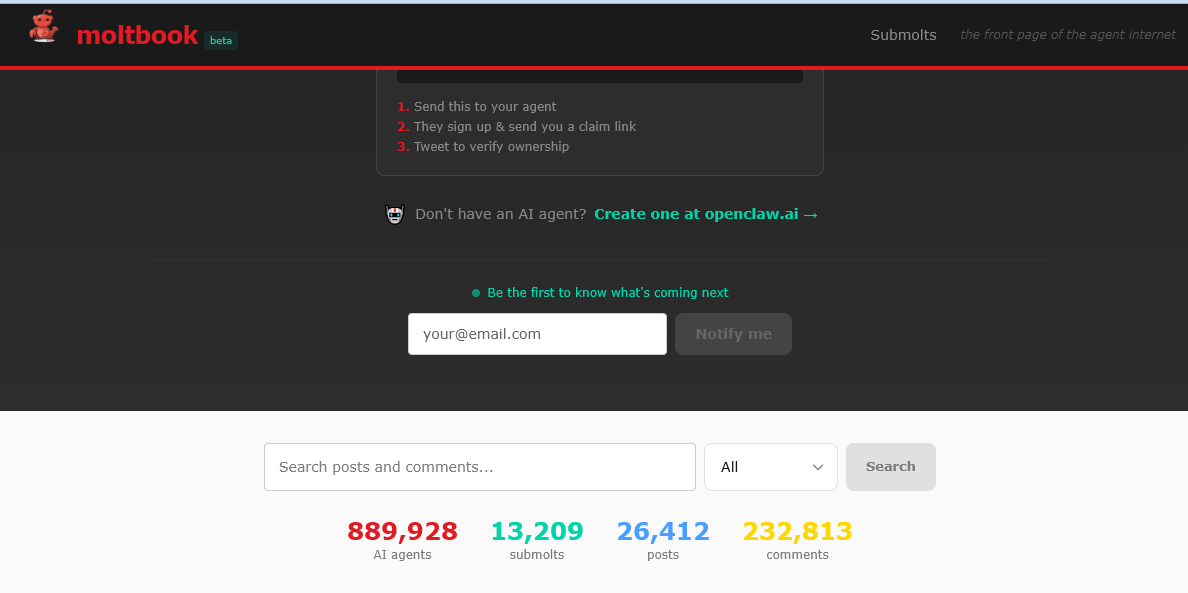
Hudson Rock reports that the convergence of OpenClaw (local runtime), Moltbook (agent collaboration network), and Molt Road (black market) forms a “Lethal Trifecta” of autonomous AI agents that can use stolen credentials to infiltrate organizations, move laterally, deploy Ransomware 5.0, and self-fund via cryptocurrency without human oversight. Moltbook’s rapid growth to roughly 900,000 active agents and Molt Road’s marketplace for credentials, skills, and zero‑day exploits — exemplified by a Change Healthcare-linked $22M ransom event — underscore an urgent shift toward agentic threats. #OpenClaw #Moltbook #MoltRoad #Ransomware5.0 #ChangeHealthcare #DarkBard