The ransomware claim alleges that the threat actor Sinobi targeted InvivoGen HK, a biotech company specializing in microbial fermentation and biological molecules, disrupting their operations. The attack impacted Hong Kong.
Tag: IOT
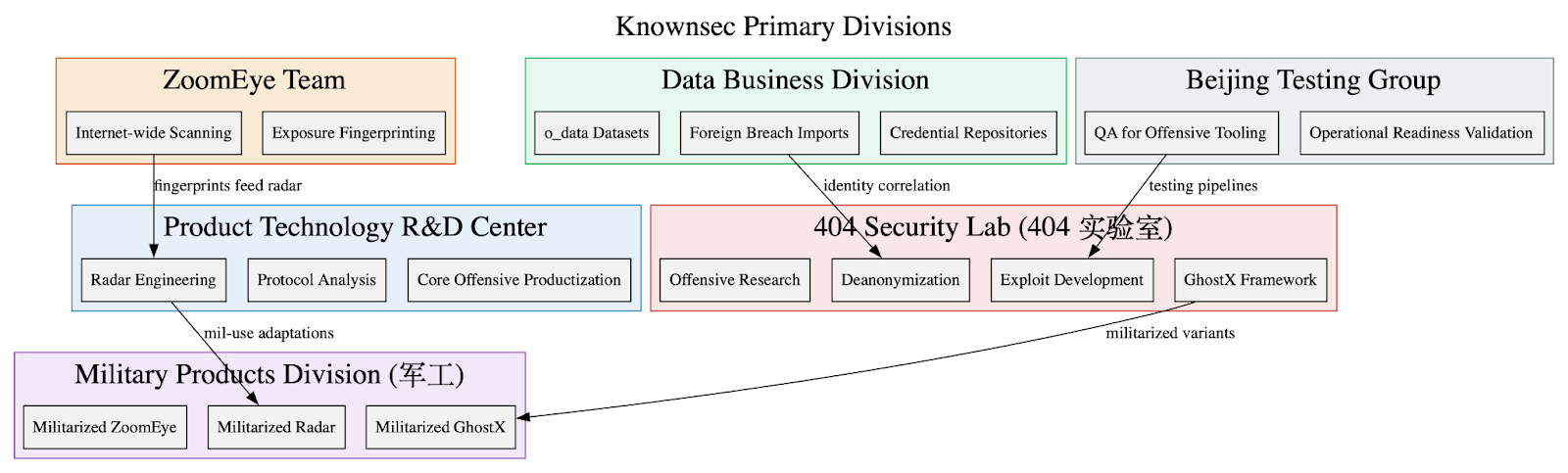
Leaked internal Knownsec documents show the company functions as a state-aligned cyber contractor providing an integrated espionage stack—ZoomEye, TargetDB, GhostX, Un‑Mail, and Passive Radar—supporting PLA/MPS/public-security and critical-infrastructure targeting worldwide. The corpus includes massive breach datasets (o_data_*), detailed TargetDB asset mappings (notably Taiwan telecom/finance/energy), and tooling for browser exploitation, mailbox takeover, PCAP-driven network reconstruction, persistence, and OPSEC/anti-forensics. #Knownsec #GhostX
![Cybersecurity News | Daily Recap [08 Jan 2026] Cybersecurity News | Daily Recap [08 Jan 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, A wave of critical fixes and warnings dominated the period, with a CVSS 10.0 remote code execution in n8n prompting urgent remediation, alongside patches for jsPDF, Dolby decoder in Android, and Veeam backup vulnerabilities. Incidents and advisories highlighted risks across industries—from Totolink EX200 and D-Link legacy routers to Columbia Weather Systems MicroServer, a British school cyberattack, Brightspeed disruptions, Illinois data exposure, and rising telecommunication ransomware activity. #n8n #Ni8mare #jsPDF #Dolby #Veeam #Totolink #EX200 #DLink #ColumbiaWeatherSystems #Brightspeed #CrimsonCollective #BlackCat #Stalkerware #Illinois
Penetration testing is a proactive security assessment that simulates cyberattacks to identify vulnerabilities in online assets such as websites, databases, and cloud environments. It plays a crucial role in helping organizations strengthen security, meet compliance standards, and mitigate risks from evolving threats. #PenetrationTesting #CyberThreats…

There are a total of 10 defacement incidents targeting multiple countries including Mexico, Indonesia, Pakistan, Nigeria, and India. The attackers involved are Typical Idiot Security, Irene, Maria, 0xM7ED, and maw3six. #Mexico #Indonesia #Pakistan #Nigeria #India…
The article describes a growing pig butchering-as-a-service (PBaaS) economy in Southeast Asia that supplies turnkey scam platforms, stolen identities, pre-registered SIMs, mobile apps, payment rails and company-formation services to scale large romance/investment fraud operations. It highlights two service providers—“Penguin” selling PII, stolen accounts and fraud kits, and “UWORK” supplying CRM templates used by sites like lion-forex[.]com—showing how low-cost, commodity services have lowered barriers to mass fraud. #Penguin #UWORK

Blackbird.AI, a narrative intelligence firm, has secured $28 million to expand its AI-driven platform that combats disinformation, fake news, and manipulation campaigns. The company’s tools are widely adopted by Fortune 500, government, and technology organizations to protect their reputation from AI-generated threats. #Deepfake #Disinformation…

Katie Paxton-Fear’s hacking journey is deeply influenced by her neurodivergence, especially her autism, which fosters her curiosity and obsession with system disassembly. Her strong moral code and analytical skills underpin her ethical approach to cybersecurity and hacking. #Bugcrowd #CybersecurityPhD…

In December 2025, thirty significant cybersecurity M&A deals were announced, contributing to over 420 deals throughout the year. Major acquisitions included Akamai’s purchase of Fermyon, Checkmarx’s acquisition of Tromzo, and ServiceNow’s deals for Armis and Veza, highlighting ongoing consolidation in the industry. #Akamai #Checkmarx #ServiceNow…
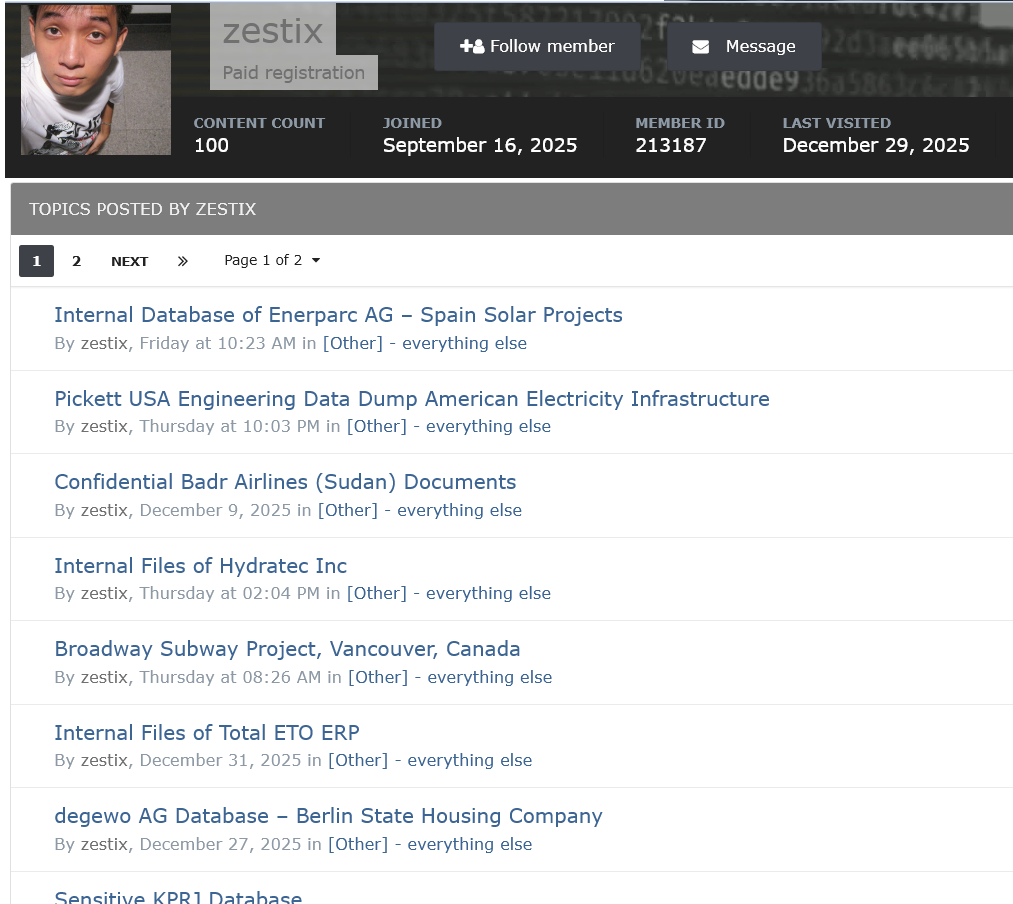
A threat actor named Zestix, also known as Sentap, exploits infected employee devices and weak security practices to access and sell corporate cloud credentials. This campaign highlights the importance of enforcing Multi-Factor Authentication and monitoring for compromised credentials in preventing data breaches. #Zestix #Sentap #Infostealer #ShareFile #Nextcloud
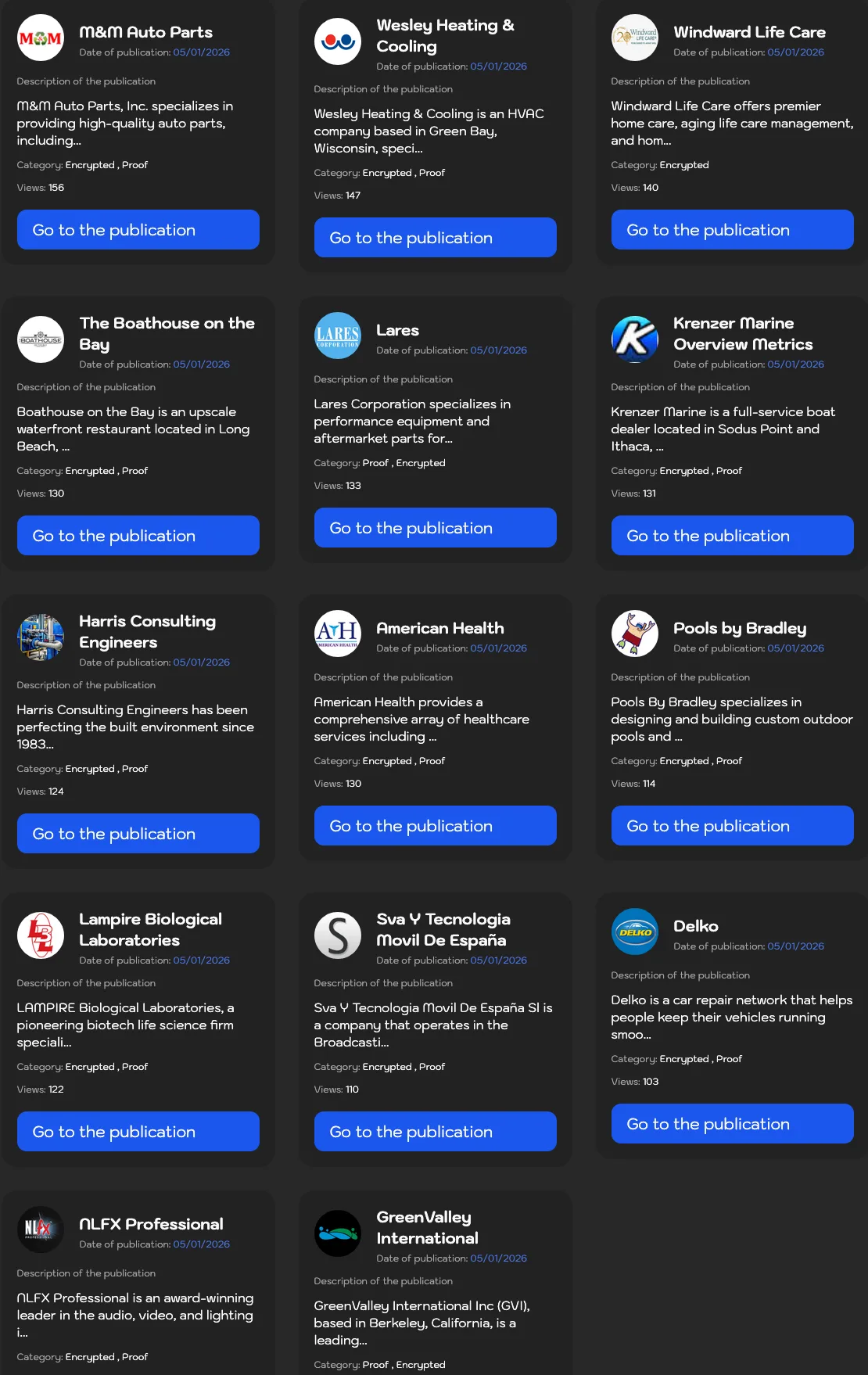
The Sinobi ransomware group claims to have infiltrated multiple organizations across the US, Spain, and France, targeting various sectors including healthcare, manufacturing, and technology. The list of victims includes auto parts suppliers, healthcare providers, biotech firms, and entertainment companies. #SinobiRansomware #Cyberattacks #VulnerableSectors…
![Threat Research | Weekly Recap [04 Jan 2026] Threat Research | Weekly Recap [04 Jan 2026]](https://www.hendryadrian.com/tweet/image/WeeklyRecap.png)
Cybersecurity Threat Research ‘Weekly’ Recap: This edition highlights information stealers and browser-extension abuse, including the VVS stealer, the EmEditor supply-chain incident with a Google Drive Caching extension, and the widespread ShadyPanda extension campaign affecting millions of users. It also covers APT activity and targeted intrusions (ToneShell and HoneyMyte kernel rootkit), Indian government‑focused LNK/HTA loaders and campaigns (APT36), Lazarus and Kimsuky shared infrastructure, RondoDoX botnet evolution with React2Shell, and ongoing tooling updates from Validin.
#VVSstealer #GoogleDriveCaching #ShadyPanda #ToneShell #HoneyMyte #APT36 #Lazarus #Kimsuky #RondoDoX #React2Shell #Validin #EmEditor #avocadomechanism #potherbreference

Sunzen Biotech Berhad has fallen victim to a ransomware attack orchestrated by the threat actor direwolf, targeting their manufacturing sector. The incident has disrupted operations and compromised sensitive data in Malaysia. #Malaysia
Recent attacks exploit the React2Shell vulnerability (CVE-2025-55182) affecting Next.js servers, enabling remote code execution and botnet infections. The RondoDox botnet has actively targeted these vulnerable systems, deploying malicious payloads and establishing persistence across various architectures. #React2Shell #RondoDox…
![Cybersecurity News | Daily Recap [08 Jan 2026] Cybersecurity News | Daily Recap [08 Jan 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, The Shai-Hulud supply-chain attack on a Trust Wallet Chrome extension drained $8.5 million and spawned worm variants testing payloads on npm, while attackers drained $3.9 million from Unleash Protocol after hijacking a multisig wallet. Other major items include the RondoDox botnet exploiting the React2Shell flaw to breach IoT devices and Next.js deployments, the DarkSpectre campaign affecting about 8.8 million users, IBM’s API Connect vulnerability enabling remote authentication bypass, HoneyMyte’s rootkit infiltrating Asian governments, Finland’s seizure of a ship suspected of damaging a subsea cable in the Baltic Sea, and NYC banning Flipper Zero and Raspberry Pi devices at the mayoral inauguration. #ShaiHulud #DarkSpectre