This week’s incidents show attackers exploiting ordinary files, trusted services, and routine workflows to gain control without relying on exotic exploits. From targeted spear-phishing that delivered the FALSECUB backdoor to malvertising and droppers seeding infostealers like TamperedChef, adversaries favor low-friction, large-scale, and patient operations. #FALSECUB #TamperedChef…
Tag: IOT

The article compares Stranger Things’ Upside Down to modern enterprise attack surfaces, warning that unmanaged IT, OT, IoT, and cloud assets act as unseen portals for threats like the Mind Flayer and Demogorgon. It calls for continuous visibility, remediation prioritization, IT/OT segmentation, and cross-functional teamwork to detect and stop threats before…

A critical authentication bypass in SmarterTools’ SmarterMail (tracked as WT-2026-0001) is being actively exploited shortly after a patch, allowing unauthenticated requests to reset any administrator password via the /api/v1/auth/force-reset-password endpoint. The flaw can be chained to achieve SYSTEM-level remote code execution through the product’s Volume Mount Command feature, and watchTowr Labs…
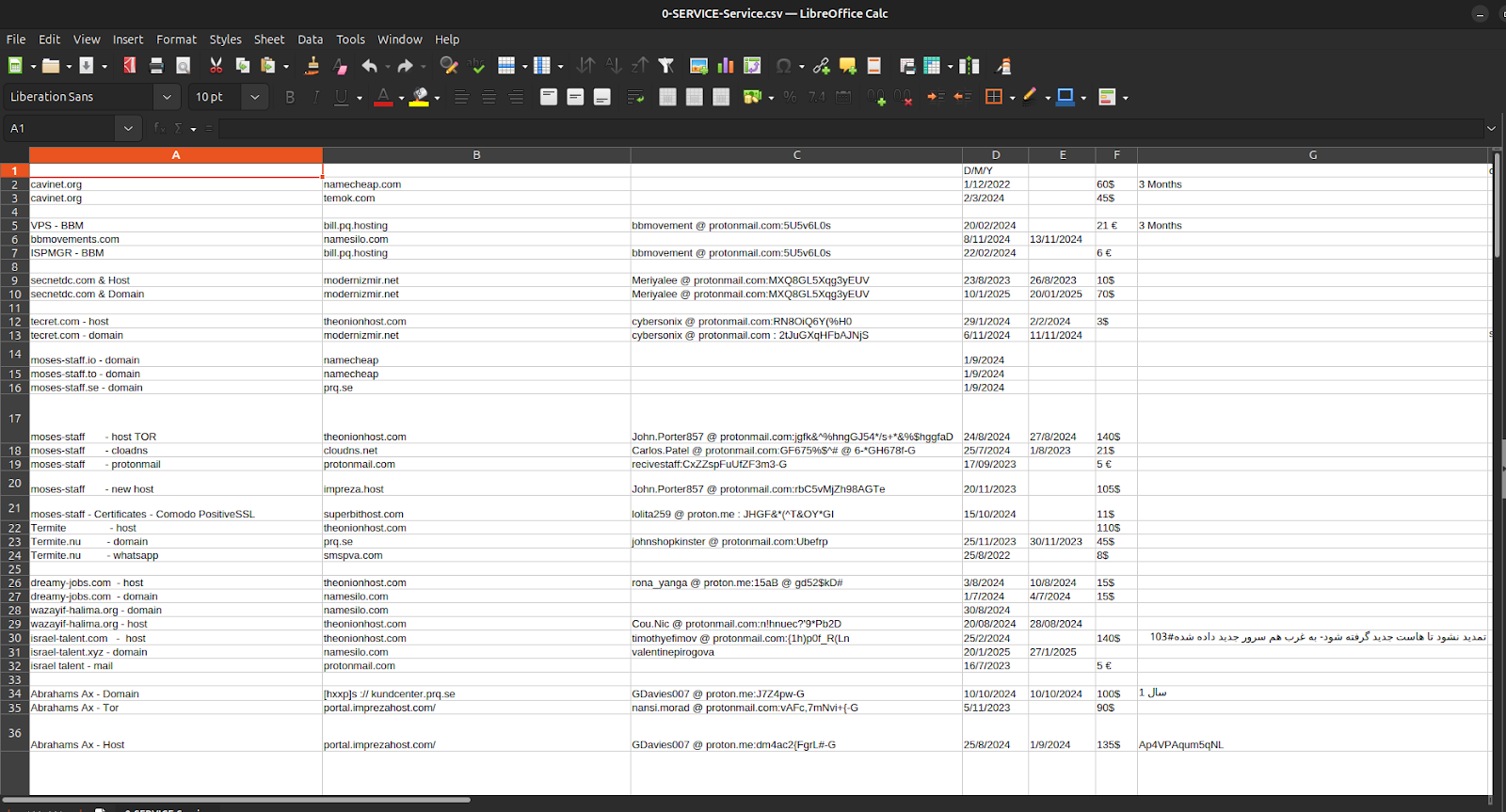
Episode 4 of the Charming Kitten / APT35 leaks exposes not sophisticated zero-day exploits but the bureaucratic infrastructure—spreadsheets, invoices, crypto receipts, hosting accounts, and one-time ProtonMail identities—that fund, procure, and maintain Iranian cyber operations. The documents tie APT35’s procurement and payment chains to Moses Staff’s leak domains and operational tooling, showing micro-crypto payments via Cryptomus, recurring European VPS providers (EDIS, Impreza), and repeatable, auditable workflows that convert state intent into persistent infrastructure. #APT35 #MosesStaff
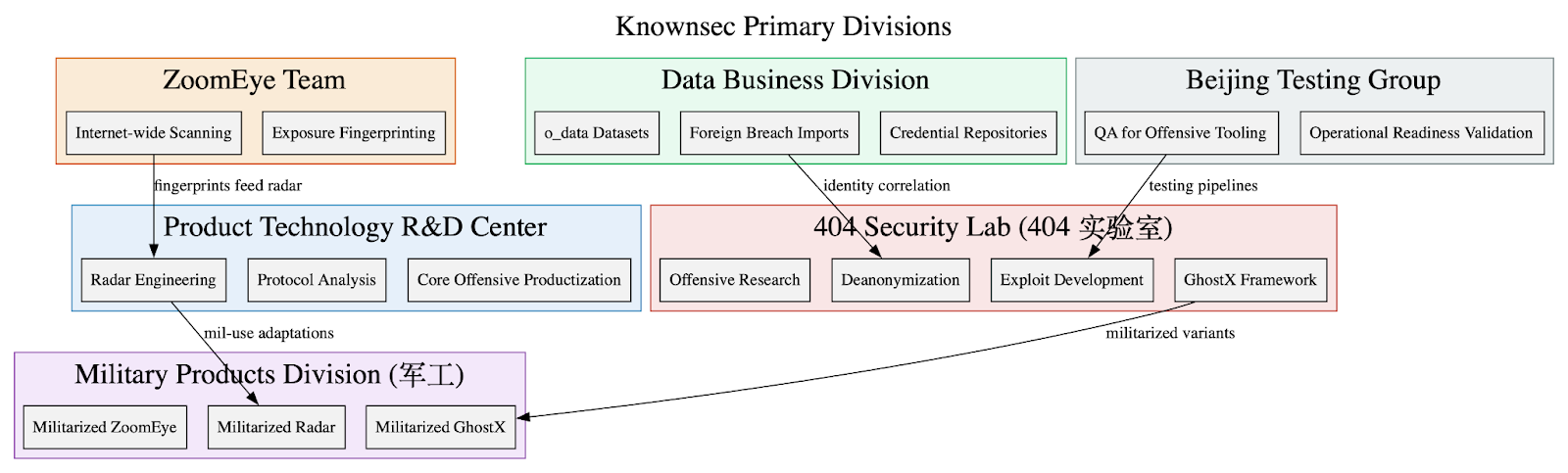
Leaked internal documents show Knownsec operates as a state-aligned cyber contractor supplying a vertically integrated espionage stack—ZoomEye/TargetDB reconnaissance, o_data_* identity correlation, GhostX/Un‑Mail exploitation and mailbox takeover, and Passive Radar PCAP-based internal mapping—to Chinese public‑security, military, and regulator customers. The corpus includes organizational charts, employee emails, high‑confidence IOCs targeting Taiwanese critical infrastructure, and detailed tradecraft emphasizing persistence, anti‑forensics, and APT‑style operational workflows. #Knownsec #GhostX
![Cybersecurity News | Daily Recap [21 Jan 2026] Cybersecurity News | Daily Recap [21 Jan 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, WordPress ACF plugin vulnerabilities put thousands of sites at risk, with one add-on affecting 100,000 sites and another flaw giving admins access on 50,000 sites. The roundup also notes patches for Zoom and GitLab addressing RCE and a high-severity 2FA bypass, a Cloudflare WAF bypass via the ACME path, AI-generated threats like VoidLink, and malware campaigns such as PDFSider and LinkedIn RAT. #VoidLink #PDFSider

A widespread spam wave exploits unsecured Zendesk support systems, flooding users with alarming and bizarre emails. Companies like Dropbox, 2K, and Discord were affected, highlighting vulnerabilities in support platform security. #ZendeskRelaySpam #UnsecuredSupportSystems
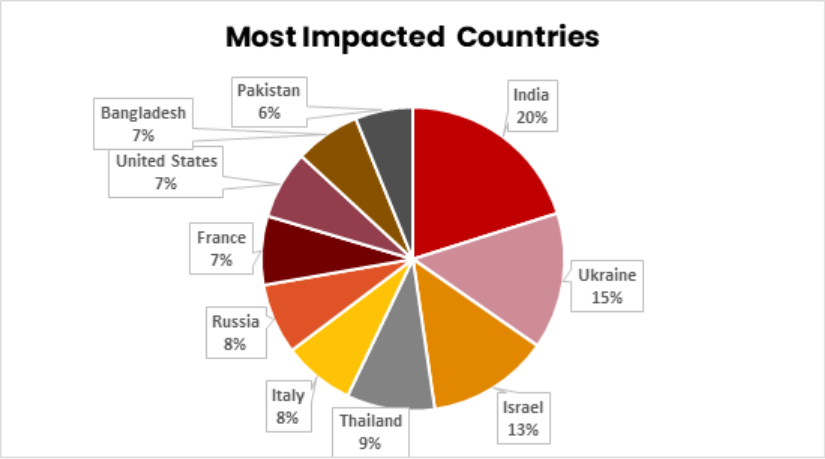
Hacktivists in 2025 shifted their focus from DDoS and defacements to targeting critical infrastructure, including ICS and IoT systems, with increased sophistication and alignment with nation-states. The threat landscape is expected to intensify in 2026, with more attacks on vulnerable OT and HMI systems, driven by geopolitical motives and automated scanning…
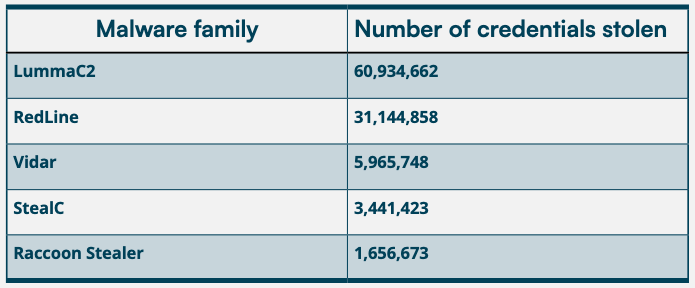
Despite ongoing security efforts, users continue to use simple and default passwords like ‘123456’ and ‘admin’, leaving critical systems vulnerable. The report highlights the persistent risk posed by reused, predictable credentials in enterprise environments, often exploited by malware and threat actors. #Lumma #RedLine…
![Cybersecurity News | Daily Recap [21 Jan 2026] Cybersecurity News | Daily Recap [21 Jan 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, The daily cybersecurity recap emphasizes proactive defence for 2026 with CISOs prioritizing attack surface visibility and threat hunting, while noting the ETSI AI security standard and Olympics-linked cyber risk as more connected environments emerge. The summary also highlights high-profile items across malware and threats, including Black Basta leadership and an INTERPOL Red Notice, the LOTUSLITE backdoor tied to a Mustang Panda campaign targeting the U.S. government, and notable vulnerabilities and incidents such as StealC, TamperedChef ads, RondoDox using an HPE OneView flaw, Windows Cloud PC bugs, GhostPoster extensions, the CIRO data breach, a Supreme Court hack, Iran TV hijack, and OpenAI ads. #BlackBasta #MustangPanda

TP-Link has released a patch for a severe vulnerability (CVE-2026-0629) that allows remote attackers to take full control of over 32 models of VIGI C and InSight surveillance cameras. This high-severity flaw enables password bypass via the web interface, putting many devices at risk of unauthorized access and data theft. #CVE-2026-0629…
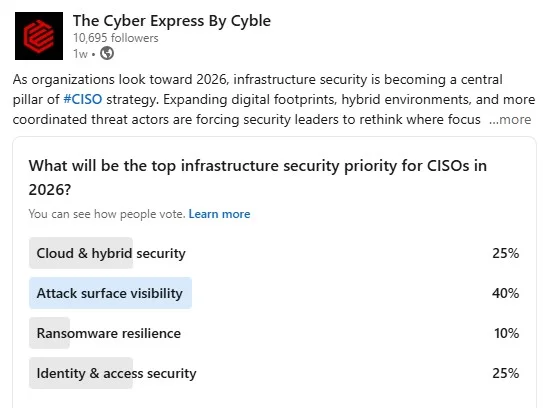
Modern organizations are prioritizing attack surface visibility as a key component of infrastructure security in 2026 due to the increasing complexity of digital assets across cloud, API, and hybrid environments. Industry experts highlight how interconnected priorities like identity management and governance are essential for effective cybersecurity strategies. #AttackSurfaceVisibility #APISecurity…
An Estonian security researcher unlocked every Äike e-scooter by reverse-engineering its Bluetooth security flaw, exposing critical vulnerabilities in the company’s IoT devices. This highlights the risks of default settings and poor key management in IoT products, especially after a manufacturer goes bankrupt. #Äike #IoTVulnerabilities…
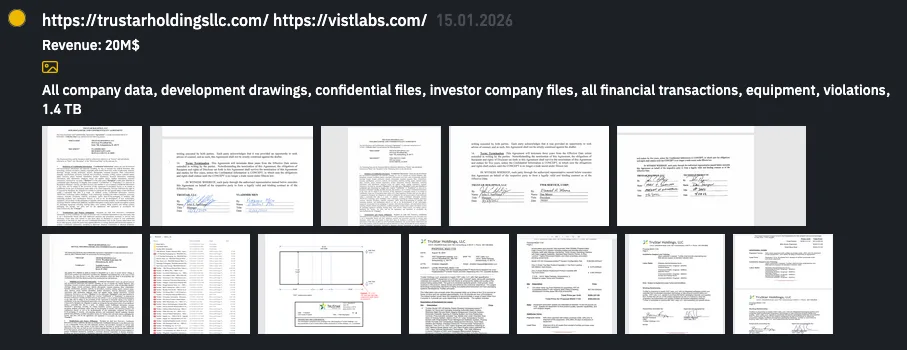
The INC Ransom group claims to have successfully breached two Illinois-based technology companies, TruStar Holdings and VIST Labs, exposing 1.4 TB of sensitive data. The attack involves the theft of corporate, technical, and financial information, highlighting significant cybersecurity risks for technology firms serving sensitive industries. #INC Ransom #TruStarHoldings #VISTLabs…

Novee, an offensive security startup, has emerged from stealth with $51.5 million in funding to develop an AI-driven penetration testing platform that simulates real-world hacking tactics. The platform aims to enhance vulnerability detection and automate security validation, empowering security teams to focus on complex threats. #Novee #AIcybersecurity…
