SecurityWeek’s Cyber Insights 2026 gathers experts who warn that cyberwarfare – driven by nation-state pre-positioning, AI-enabled operations, and rising geopolitical tensions – will escalate faster than criminal cybercrime in 2026. The report highlights blurred lines between criminal and state actors, the difficulty of attribution, and the need for improved detection, resilience,…
Tag: IOT

New Cyble research shows ransomware attacks rose about 30% since late 2025 and continued into January 2026, with many incidents targeting software and manufacturing supply chains. Top groups such as Qilin and CL0P led high-volume claims while several major supply-chain-related breaches and new ransomware affiliates increased the overall threat. #Qilin #CL0P…

MS-ISAC reporting shows total malware notifications rose 7% from Q3 to Q4 2025, with SocGholish accounting for 30% of detections and CoinMiner and Agent Tesla also prominent. New and returning families observed include ACR Stealer, Calendaromatic, SombRAT, and Arechclient2, with notable vectors like malvertisement, malspam, WMI-based spread, and multiple persistence and…

Identity security is rapidly evolving from simple username/password models into AI-driven governance, liveness biometrics, decentralized identity, passwordless passkeys, and machine identities that will define access in 2026. Organizations must treat identity as the central control plane for digital trust and adopt technologies like self-sovereign identity and post-quantum cryptography to stay ahead of sophisticated threats. #SailPoint #SelfSovereignIdentity

The Aisuru/Kimwolf botnet launched a record-breaking DDoS campaign that peaked at 31.4 Tbps and generated over 200 million HTTP requests per second, targeting telecommunications providers, IT organizations, and Cloudflare’s dashboard and infrastructure. Cloudflare reported it detected and automatically mitigated the attacks on December 19 and noted a 121% year-over-year increase in…
IClickFix is a widespread malicious JavaScript framework that has been injected into over 3,800 compromised WordPress sites since at least December 2024 to display a fake Cloudflare Turnstile (ClickFix) lure and deliver downstream payloads. The framework uses a YOURLS-based Traffic Distribution System, multi-stage obfuscated JavaScript, and clipboard-based social engineering to install NetSupport RAT via a PowerShell dropper. #IClickFix #NetSupportRAT

Check Point Research’s Cyber Security Report 2026 synthesizes findings from 2025 showing AI is embedded across the attack lifecycle, accelerating reconnaissance, social engineering, and malware development while introducing new governance risks. The report also highlights fragmented, data-only ransomware extortion, exploitation of unmonitored edge and perimeter devices, geopolitically aligned cyber activity, and measurable vulnerabilities in Model Context Protocols and ungoverned AI usage. #ModelContextProtocols #UnmonitoredDevices

SolarWinds released updates for Web Help Desk to patch multiple critical authentication bypass and remote command execution flaws, including CVE-2025-40551 through CVE-2025-40554, plus a high-severity hardcoded credentials issue. Administrators are urged to upgrade to Web Help Desk 2026.1 and apply patches immediately because WHD vulnerabilities have been repeatedly exploited in attacks and flagged by CISA. #SolarWinds #WebHelpDesk

Offensive security and red teaming are shifting from periodic exercises to continuous, AI-augmented programs that combine automation, threat intelligence, and human expertise to find and fix vulnerabilities faster. This evolution includes hybrid in-house and external models, greater collaboration with blue teams, and an urgent focus on combating AI-enhanced social engineering. #Bugcrowd…

Many major organizations appear to have been targeted in an Okta SSO vishing campaign tied to ShinyHunters that involved fake domains and leaked data listings. Security firms warn attackers used real-time client-side phishing kits to intercept credentials and bypass MFA, urging adoption of phishing-resistant methods like FIDO2 and tighter app and…
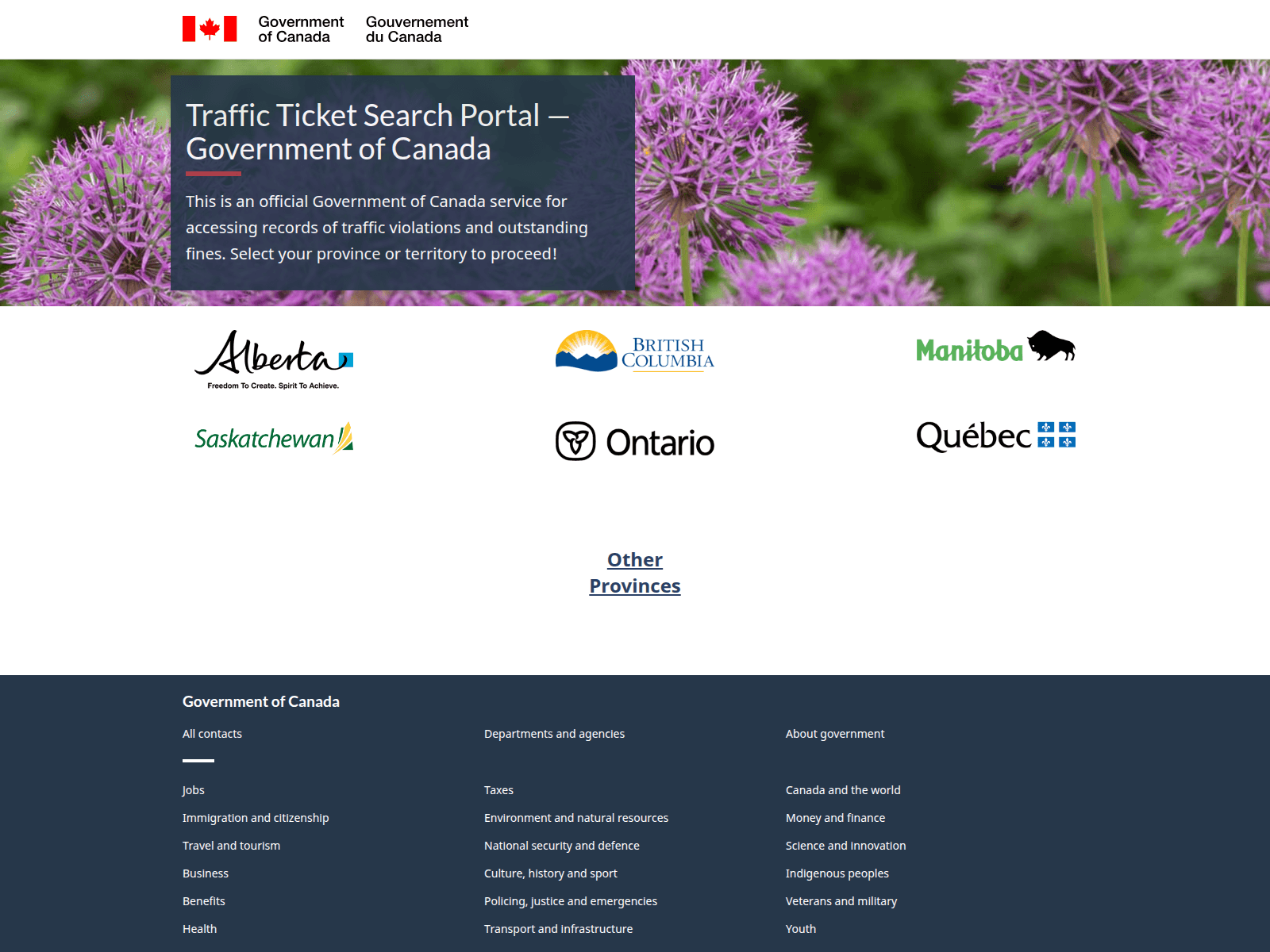
CloudSEK identified interconnected phishing campaigns impersonating Canadian government bodies and national brands (traffic-ticket portals, CRA, Canada Post, Air Canada) to harvest PII and financial data using SMS lures, typosquatted domains, and fake payment gateways. The activity aligns with the PayTool ecosystem and is being commoditized on underground forums by a seller advertising specialized phishing kits. #PayTool #theghostorder01

There were 9 defacement incidents targeting websites in Argentina, Mongolia, and Indonesia. The attacks were carried out by BontenSec, Typical Idiot Security, Maria, and T-XpLoiT. #Argentina #Mongolia #Indonesia…
![Cybersecurity News | Daily Recap [24 Jan 2026] Cybersecurity News | Daily Recap [24 Jan 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, phishing activity escalates with an AiTM campaign abusing SharePoint to steal Microsoft credentials, compromise inboxes, and bypass MFA in the energy sector, while vishing kits synchronize fake login pages with live calls targeting Google, Microsoft, and Okta. Ransomware and exploits dominate the headlines, from Osiris using POORTRY to disable protections and exfiltrate data to Wasabi, to INC recovery of encrypted data and Ploutus ATM jackpotting linked to Tren de Aragua, alongside critical vulnerabilities in FortiCloud SSO, SmarterMail, InetUtils telnetd, and widespread security updates from GitLab, Outlook iOS, curl, and Teams. #SharePoint #AiTM #Microsoft #Google #Okta #Osiris #POORTRY #Wasabi #INC #Ploutus #TrenDeAragua #FortiCloudSSO #FortiOS #SmarterMail #InetUtils #telnetd #GitLab #Outlook #curl #Teams #Pwn2OwnAuto #FALSECUB #TamperedChef #NetNTLMv1 #MnCHOICES #ActiveDirectory

A coordinated campaign is exploiting CVE-2026-24061, a critical authentication-bypass flaw in GNU InetUtils’ telnetd that allows attackers to gain root by injecting a crafted USER environment variable. Although observed exploitation is limited so far, affected systems should upgrade to GNU InetUtils 2.8 or disable telnetd/block TCP port 23 to prevent compromise. #CVE-2026-24061 #GNUInetUtils

TikTok announced the formation of TikTok USDS Joint Venture LLC to transfer majority ownership to U.S. investors while ByteDance retains a 19.9% stake to comply with the September 2025 Executive Order. The venture will secure U.S. user data and the recommendation algorithm on Oracle’s U.S. cloud, implement NIST, ISO 27001 and…
