The 2025 Cybersecurity M&A and Capital Markets Report highlights a record $119 billion in strategic activity with significant growth in AI security investments, multiple billion-dollar acquisitions, and a dynamic market shift toward AI-driven defense solutions. The report underscores AI’s transformative impact on cybersecurity offense and defense, with rapid vendor emergence and evolving governance challenges representing the central focus for future security strategies. #AISecurity #CyberArk #Wiz #MomentumCyber
Tag: GOVERNANCE

Cyber Insights 2026 predicts a rapidly evolving cybersecurity landscape where CISOs face increasing complexity, AI-induced risks, regulatory pressures, and burnout. The role will transform into a broader executive position, emphasizing AI governance, personal liability, and organizational resilience. #CISO #AIThreats…

Dr. Amit Chaubey discusses the expanding “2026 Business Blast Radius,” emphasizing how external dependencies and geopolitical risks threaten global infrastructure and organizational resilience. The rising cyber threats, including AI-enabled identity attacks and cloud exploits, demand a collective, proactive security approach. #ChakraX #GlobalCyberThreats…
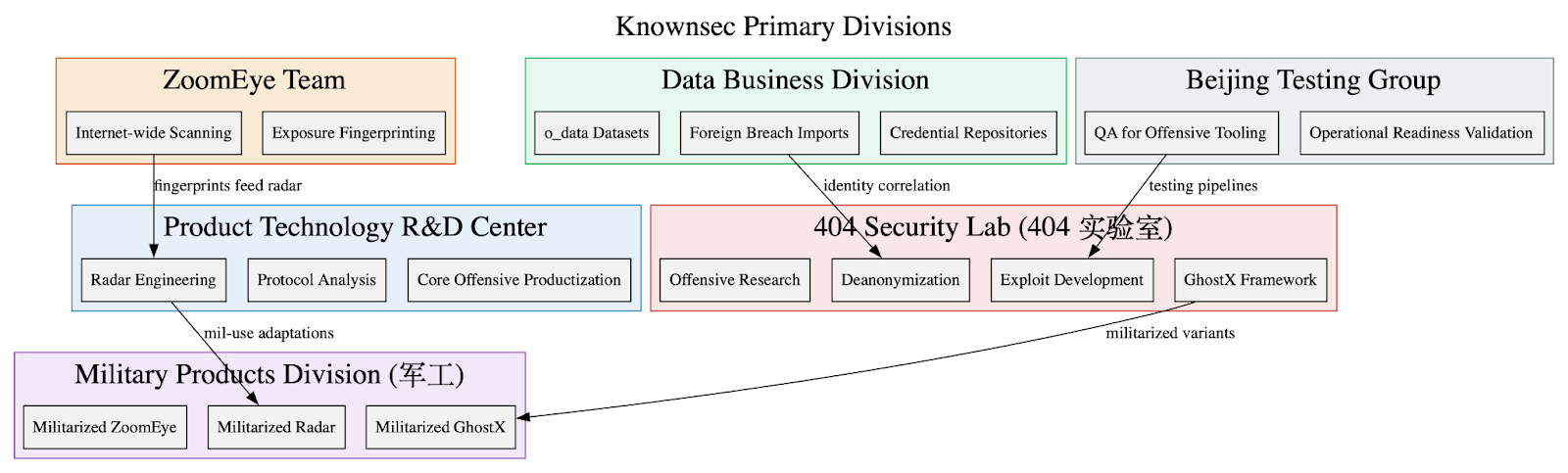
Leaked internal Knownsec documents show the company functions as a state-aligned cyber contractor providing an integrated espionage stack—ZoomEye, TargetDB, GhostX, Un‑Mail, and Passive Radar—supporting PLA/MPS/public-security and critical-infrastructure targeting worldwide. The corpus includes massive breach datasets (o_data_*), detailed TargetDB asset mappings (notably Taiwan telecom/finance/energy), and tooling for browser exploitation, mailbox takeover, PCAP-driven network reconstruction, persistence, and OPSEC/anti-forensics. #Knownsec #GhostX

The first week of 2026 highlights the increasing complexity and global reach of cyber threats affecting various sectors from education to government. Effective cybersecurity responses now demand coordinated efforts, regulatory measures, and heightened awareness across all levels. #HighamLaneSchool #WhiteSupremacistWebsites #UKCyberSecurity #Prosura #USCyberCoalitions…

The United States is withdrawing from numerous international organizations, citing concerns over redundancy, mismanagement, and conflicting interests. This move could impact global cyber governance and international legal frameworks, emphasizing a focus on national sovereignty. #UNFrameworkConvention #CyberGovernance #InternationalLaw #USWithdrawal…

Artificial intelligence is evolving from passive tools to autonomous agents capable of making decisions and executing actions, increasing security risks. Organizations must implement advanced guardrails and frameworks to manage new threats like context injection and action-level exploits. #AgenticAI #SecurityFramework…

The UK government has introduced the Government Cyber Action Plan to enhance the resilience of public sector digital infrastructure against sophisticated cyber threats. This strategic initiative aims to improve coordination, accountability, and skills to better protect critical services from cyberattacks. #NCSC #GovCyberResilience…
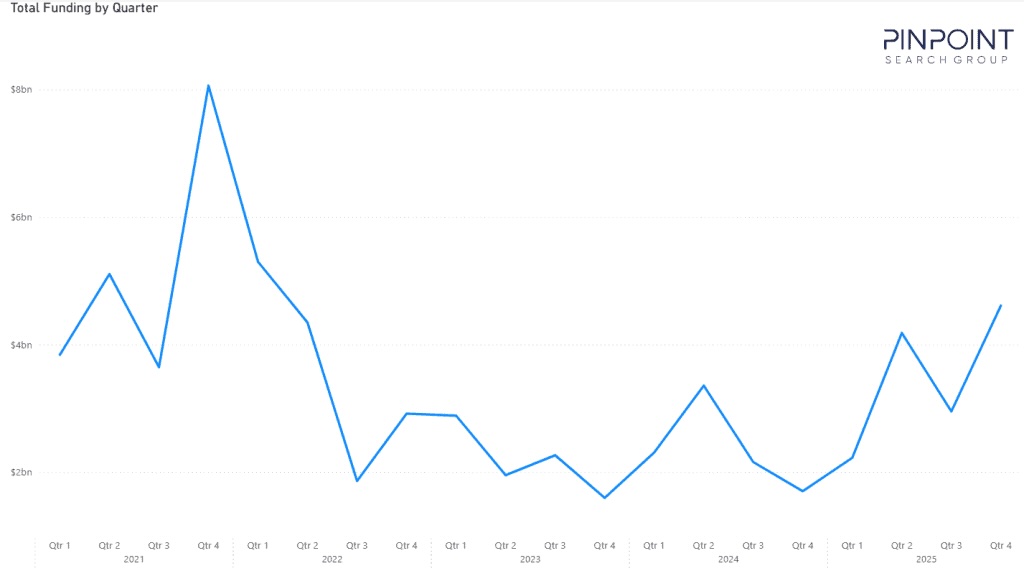
Cybersecurity funding reached nearly $14 billion in 2025, marking a strong rebound after a contraction since 2021, with growth focused on governance, identity, and AI security. Investors are now favoring vendors with proven outcomes, emphasizing strategic links to operational disciplines and evolving buyer needs. #CybersecurityFunding #AIProtection…

Securing AI must be approached as a lifecycle challenge that crosses development, operations, data, supply chain, and user interaction boundaries rather than fitting into any single existing security function. The article outlines five categories of enterprise AI risk and recommends lifecycle-based frameworks, real-time monitoring, supplier validation, and governance to maintain trust, accountability, and resilience. #ISOIEC42001 #NISTAIRMF

This article emphasizes that cybersecurity in 2026 will require a focus on resilience over prevention due to increasing automation and sophistication in cyber threats. Building organizational resilience through governance, technology, and culture is essential for enduring emerging risks like AI manipulation, third-party vulnerabilities, and quantum threats. #CyberResilience #AIThreats…

The UK Government’s new “Cyber Action Plan” highlights the urgent need to address critical vulnerabilities in public sector digital infrastructure, including widespread reliance on legacy systems. The plan introduces new oversight, accountability, and workforce initiatives to improve cybersecurity resilience across government departments. #CrowdStrike #NHSecurity…

The article discusses the fragmentation of digital identities across various platforms and the emergence of identity dark matter, which includes unmanaged, non-human, and orphaned identities. It emphasizes the security risks associated with ungoverned identities and promotes shifting to identity observability for comprehensive security and compliance. #IdentityDarkMatter #OrchidSecurity…
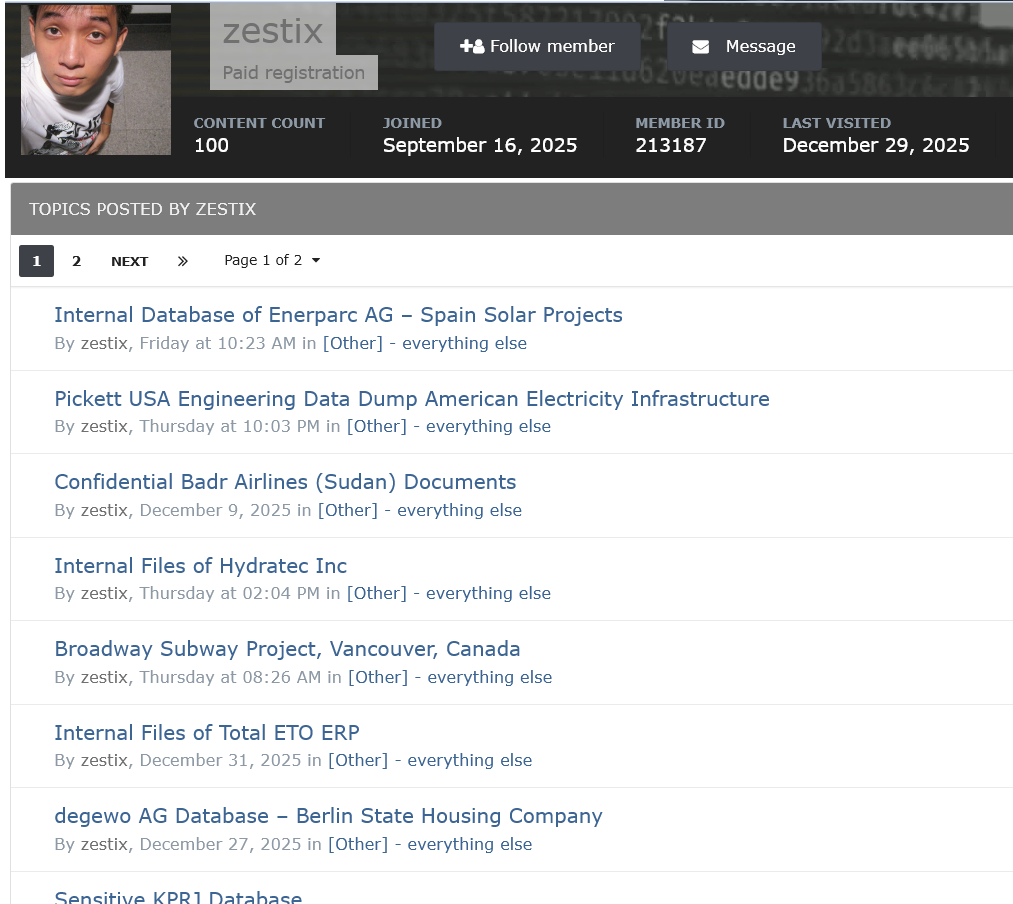
A threat actor named Zestix, also known as Sentap, exploits infected employee devices and weak security practices to access and sell corporate cloud credentials. This campaign highlights the importance of enforcing Multi-Factor Authentication and monitoring for compromised credentials in preventing data breaches. #Zestix #Sentap #Infostealer #ShareFile #Nextcloud
Agentic AI introduces new identity challenges for security teams, emphasizing the need for lifecycle management and visibility to prevent breaches. Proper governance and correlation of identity signals are critical to ensuring safe and scalable AI deployment. #AgenticAI #IdentitySecurity
