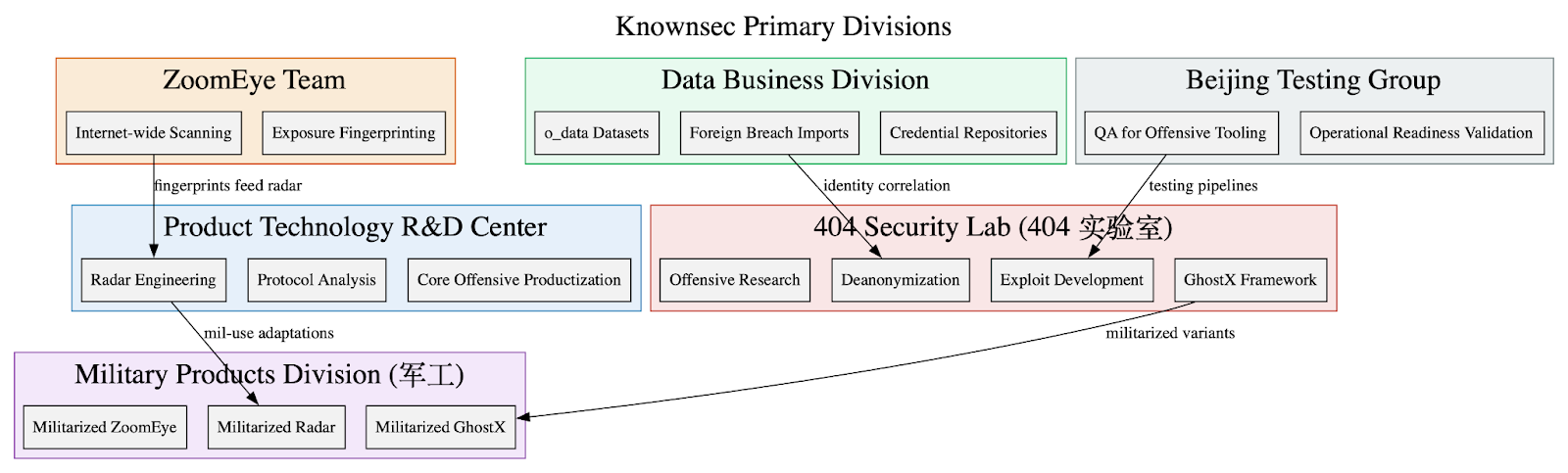
Leaked internal documents show Knownsec operates as a state-aligned cyber contractor supplying a vertically integrated espionage stack—ZoomEye/TargetDB reconnaissance, o_data_* identity correlation, GhostX/Un‑Mail exploitation and mailbox takeover, and Passive Radar PCAP-based internal mapping—to Chinese public‑security, military, and regulator customers. The corpus includes organizational charts, employee emails, high‑confidence IOCs targeting Taiwanese critical infrastructure, and detailed tradecraft emphasizing persistence, anti‑forensics, and APT‑style operational workflows. #Knownsec #GhostX
Tag: GOVERNANCE

This article discusses the growing importance, proliferation, and security challenges of Application Programming Interfaces (APIs) in the context of AI advancements and cyber threats. It highlights how the rapid increase in APIs, especially with autonomous AI systems, expands the attack surface, making effective security measures more critical than ever. #SesameOp #OpenAIAPI…

This article highlights the increasing cyber threats faced by healthcare organizations in 2025, emphasizing the need for enhanced cyber resilience strategies. It discusses the importance of Zero Trust, AI, supply chain vigilance, and leadership accountability in strengthening cybersecurity in healthcare. #CyberResilience #HealthcareSecurity #AI #ZeroTrust #SupplyChainSecurity…

Enterprise AI adoption is accelerating, expanding security boundaries across Cloud, SaaS, and Endpoint environments and exposing a complex, AI-driven attack surface. Traditional security tools struggle to protect AI assets, making advanced AI security posture management essential for full visibility, risk assessment, data lineage, and zero-trust enforcement across the AI ecosystem. #HuggingFace #ModelContextProtocol

SentinelLABS’ analysis finds that current LLM benchmarks from major players reduce continuous, collaborative security work to isolated, static tasks and therefore do not measure the operational outcomes defenders need. Benchmarks such as Microsoft’s ExCyTIn-Bench, Meta’s CyberSOCEval/CyberSecEval 3, and CTIBench show LLMs struggle with multi-hop investigations, poor calibration on severity, and evaluation loops that rely on vendor models to judge vendor models. #ExCyTIn-Bench #CyberSOCEval

Organizations must focus on identity security to prevent sophisticated breaches, leveraging tools like Identity Threat Detection & Response (ITDR) for in-depth visibility. Tenfold offers an all-in-one platform combining Identity Governance and Security, enabling proactive threat detection and efficient management. #IDThreatDetection #IdentityGovernance
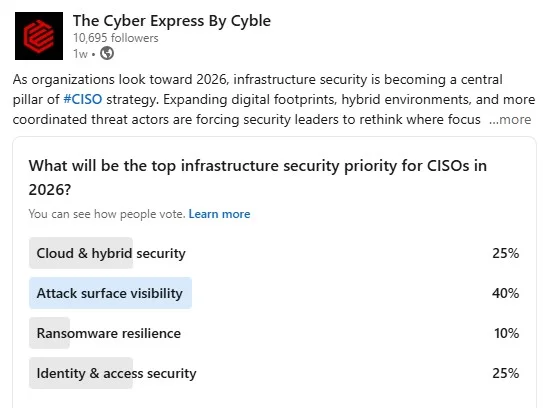
Modern organizations are prioritizing attack surface visibility as a key component of infrastructure security in 2026 due to the increasing complexity of digital assets across cloud, API, and hybrid environments. Industry experts highlight how interconnected priorities like identity management and governance are essential for effective cybersecurity strategies. #AttackSurfaceVisibility #APISecurity…
![Cybersecurity News | Daily Recap [16 Jan 2026] Cybersecurity News | Daily Recap [16 Jan 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, AI & ML security dominates the recap with threats ranging from voice cloning, PLC vulnerabilities, and poisoned dependencies to privilege escalation via AI agents and escalating workflow risks. The report highlights a mix of incidents, patches, and enforcement actions across vendors, botnets, data breaches, and regulatory penalties, underscoring the need to secure workflows, access controls, and AI governance. #VoidLink #Kimwolf #Aisuru #FortiSIEM #PLUGGYAPE #GrokBlock #GrokProbe #Eurail #Kyowon #FreeMobile #RedVDS #Verizon #Uganda #Siemens #Schneider #Aveva #PhoenixContact #Tines #Aikido #CrowdStrike #FTC #GM

The 2026 cybersecurity landscape continues to evolve with significant incidents impacting national security, public trust, and business continuity. Key themes include AI regulation, state internet blackouts, data breaches, and the disruption of cybercrime services. #GrokAI #RedVDS…

Security leaders believe that managing third-party supply chain resilience and leveraging AI for automation will be the key to cybersecurity efficiency in 2026. They emphasize the importance of simplifying security processes, industry-wide AI governance, and fostering collaborative threat intelligence. #DORA #NIS2 #AIautomation #ThreatSharing…

The 2025 State of Shadow AI Report reveals the widespread and persistent use of unsanctioned AI applications in enterprises, highlighting critical security risks, especially related to tools like OpenAI and low-security-rated apps such as Jivrus Technologies and Happytalk. It emphasizes the urgent need for real-time discovery, governance, and remediation strategies to manage shadow AI exposure, particularly in small and mid-sized organizations. #ShadowAI #OpenAI #RecoSecurity
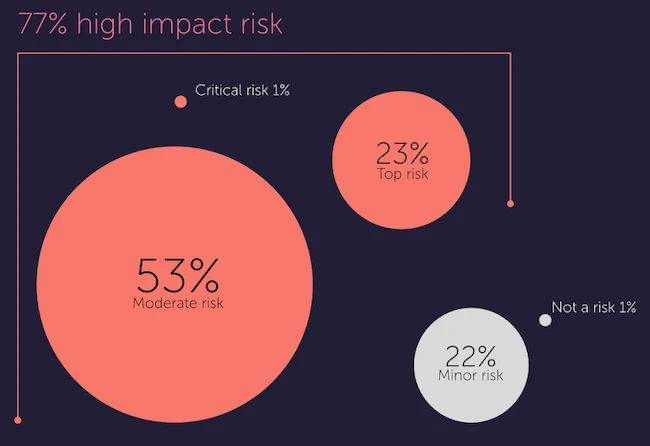
Third-party cyber risks are increasing due to expanding vendor ecosystems, yet visibility into extended supply chains remains limited. Regulatory pressures are growing, but many organizations are not fully prepared to address complex third-party threats. #Panorays #ThirdPartyRisk…
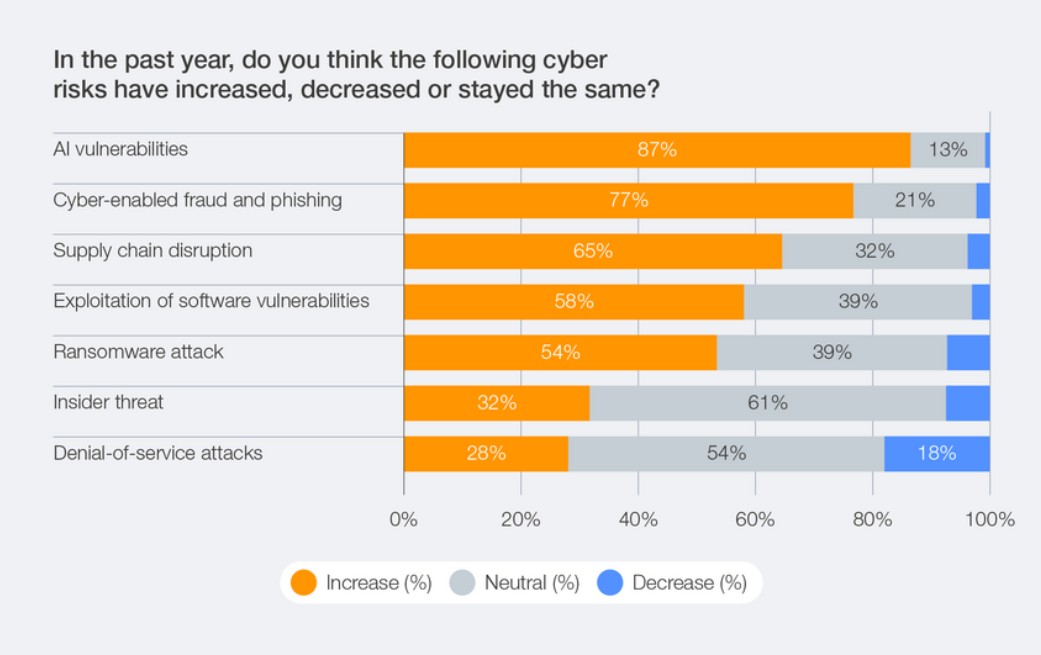
The World Economic Forum’s annual cybersecurity outlook highlights AI as the primary driver of change and concern in cybersecurity, with organizations increasingly assessing AI security risks. Top concerns include AI vulnerabilities, cyber-enabled fraud, and geopolitical threats, prompting organizations to adopt AI-driven defense strategies and governance models. #AIsecurity #CyberEnabledFraud…

Research shows a significant increase in third-party applications accessing sensitive data without justification, with government and education sectors experiencing sharp rises in malicious activity. Despite prioritizing web security, most organizations lack implemented solutions to mitigate these risks, emphasizing governance gaps and over-permissioned tracking tools like Facebook Pixel and Google Tag Manager….

Nicole Ozer’s appointment to the California Privacy Protection Agency board signals a strengthened focus on privacy rights, digital civil liberties, and responsible data governance in California. This leadership update coincides with evolving national security and cybersecurity efforts, highlighting the importance of experienced governance in digital rights protection. #CaliforniaPrivacyAct #NicoleOzer #CalPrivacy #NSADeputyDirector…