Check Point reported strong Q4 and full-year 2025 results while announcing acquisitions of Cyata, Cyclops, and Rotate to accelerate its AI-driven security and exposure management strategy. The company reportedly paid about $150 million for the three deals (including $85 million for Cyclops) as Q4 revenue hit $745 million and full-year revenue…
Tag: GOVERNANCE
![Cybersecurity News | Daily Recap [07 Feb 2026] Cybersecurity News | Daily Recap [07 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, BridgePay confirms a ransomware attack that knocked core payment systems offline, causing a nationwide outage and forcing some merchants to accept cash while the FBI and agencies investigate. Attacks span academia and government, including Spain’s Ministry of Science data leaks linked to GordonFreeman and BabLock/Femwar02 that took La Sapienza offline, affecting about 112,500 students, plus AI-enabled threat discussions and privacy concerns around surveillance tools.
#BridgePay #BabLock

The growing threat from End-of-Support edge devices has become a national cybersecurity liability as threat actors exploit outdated firewalls, routers, VPN gateways, and other perimeter appliances to gain access and pivot into federal networks. The Binding Operational Directive BOD 26-02 mandates time‑bound inventory, decommissioning, replacement, and continuous discovery to eliminate these…

Flare researchers discovered more than 10,000 public Docker Hub images in late 2025 that leaked production API keys, cloud tokens, CI/CD credentials, and AI model access tokens, exposing thousands of live non-human identities. These structural failures enabled real-world compromises like the UNC5537 Snowflake intrusions and the prolonged Home Depot token exposure, underscoring the need to detect, rotate, and revoke long-lived machine credentials. #UNC5537 #Snowflake

Identity security is rapidly evolving from simple username/password models into AI-driven governance, liveness biometrics, decentralized identity, passwordless passkeys, and machine identities that will define access in 2026. Organizations must treat identity as the central control plane for digital trust and adopt technologies like self-sovereign identity and post-quantum cryptography to stay ahead of sophisticated threats. #SailPoint #SelfSovereignIdentity

Civil society groups warn that NSO Group is using its submission to the Pall Mall Process to whitewash a long record of human rights abuses tied to its Pegasus spyware, while providing little transparency or evidence of enforcement. Critics and officials stress that consultation responses do not equal endorsement and call…

CEOs and other leaders are increasingly targeted through public profiles, travel disclosures, deepfakes, impersonation accounts, and leaked credentials—threats that can trigger multi‑million dollar losses and long‑lasting reputational damage. Executive monitoring solutions like Cyble deliver real‑time detection across surface, deep, and dark web sources, plus deepfake identification and contextualized alerts to protect…
![Threat Research | Weekly Recap [01 Feb 2026] Threat Research | Weekly Recap [01 Feb 2026]](https://www.hendryadrian.com/tweet/image/WeeklyRecap.png)
Cybersecurity Threat Research ‘Weekly’ Recap: A sweeping roundup covers ransomware, Android threats, fileless tools, nation-state campaigns, cloud abuse, browser extension hijacks, supply-chain incidents, AI governance risks, and defensive improvements. It highlights actor-tool pairs and campaigns such as LockBit5.0, BravoX, Amnesia RAT, Arsink RAT, PlayCloak, PureRAT, PyRAT, GOGITTER, GITSHELLPAD, SheetCreep, VSCode tunnel, DarkSpectre, PayTool, SquarePhish2 and Graphish among others.
#LockBit5_0 #BravoX #AmnesiaRAT #ArsinkRAT #PlayCloak #PureRAT #PyRAT #GOGITTER #GITSHELLPAD #SheetCreep #VSCodeTunnel #DarkSpectre #PayTool #SquarePhish2 #Graphish
![Cybersecurity News | Daily Recap [07 Feb 2026] Cybersecurity News | Daily Recap [07 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, a wave of critical flaws including n8n CVE-2026-1470/0863 enabling authenticated remote code execution and extensive updates across builds, alongside KEV catalog additions (Microsoft Office CVE-2026-21509, GNU InetUtils, SmarterMail, Linux kernel) highlight widespread risk across software, networks and OT. In parallel, state-backed and criminal groups continue weaponizing legacy flaws (WinRAR CVE-2025-8088 with UNC4895/RomCom, APT44, Turla), LLM/MCP abuses (Operation Bizarre Bazaar), C2 abuse (Sheet Attack), exposed AI tools (Bondu Panel, ChatGPT) and infrastructure attacks (IPIDEA takedown, Poland grid disruption), underscoring the need for resilient, AI-assisted defenses. #n8n #OperationBizarreBazaar

AI agents that select and execute capabilities based on language and metadata introduce a new attack surface called agentic tool chain attacks, which manipulate tool descriptions, schemas, and context to cause data leaks or unauthorized actions without changing code. Effective defenses require reasoning-layer controls such as signed manifests, version pinning, strict…
This weekly roundup covers major global cyber incidents, emerging threats in AI and ad fraud, critical zero-day patches, and growing regulatory scrutiny affecting public and private sectors. Highlights include the disruptive attack on Russian security firm Delta, the discovery of the ShadowHS Linux post-exploitation framework, Ivanti emergency fixes for CVE-2026-1281 and…
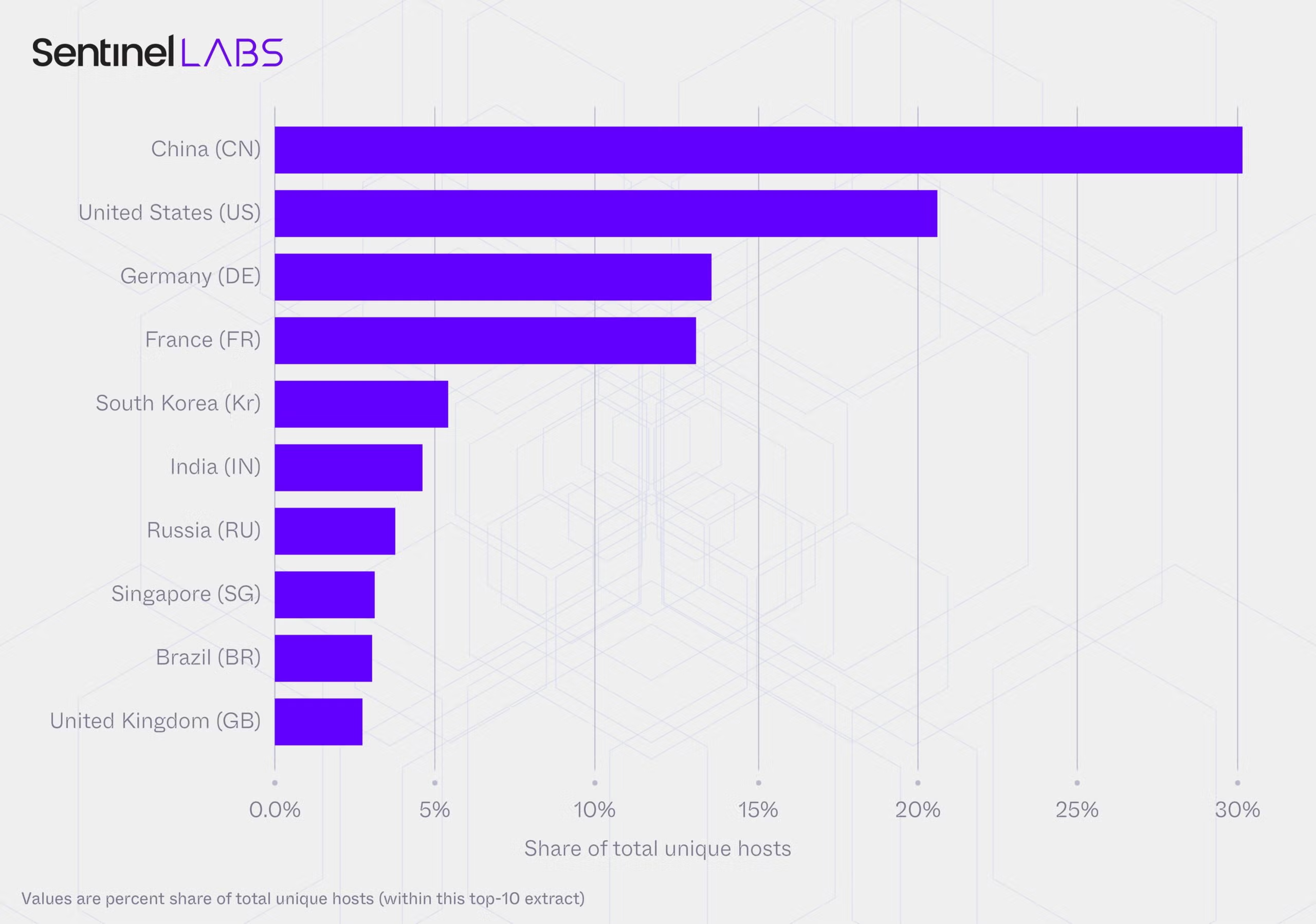
A joint SentinelLABS and Censys study found an unmanaged, publicly accessible layer of Ollama deployments spanning 175,108 hosts across 130 countries, with a persistent core of roughly 23,000 hosts generating the majority of observed activity. Nearly half of hosts expose tool-calling and multimodal capabilities while the ecosystem converges on a small set of model families and the Q4_K_M 4-bit quantization format, creating a brittle monoculture and governance gaps that complicate attribution and defense. #Ollama #Q4_K_M
![Cybersecurity News | Daily Recap [07 Feb 2026] Cybersecurity News | Daily Recap [07 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, The day’s cybersecurity news shows ongoing exploitation of the WinRAR CVE-2025-8088 to drop silent payloads into Windows Startup folders by nation-state and criminal groups. It also highlights high-severity flaws such as Grist Core RCE in Pyodide, React2Shell deserialization, Fortinet FortiOS SSO bypass, and other attacks, underscoring urgent patching and proactive defense. #WinRAR #React2Shell

The 2025 WiCyS Cyber Talent Study, analyzed by skillrex using an N2K diagnostic mapped to the NICE Framework, evaluates 604 WiCyS members and finds the community outperforming peers across most NICE Categories and many Specialty Areas. The report shows a roughly 4‑point composite advantage (~10%), highlights strong leadership and governance capabilities and measurable gains from targeted training, and identifies specific skill gaps to guide future WiCyS programs. #WiCyS #skillrex

OMICRON’s multi-year IDS deployments across more than 100 substations, power plants, and control centers revealed widespread technical, organizational, and operational security gaps in OT networks that expand the attack surface of energy infrastructure. StationGuard’s passive and active monitoring exposed unpatched PAC devices (including CVE-2015-5374), risky external connections, weak segmentation, and incomplete…
