ANY.RUN performed a full dynamic and static analysis of CastleLoader, revealing a multi-stage delivery (Inno Setup → AutoIt → process hollowing into jsc.exe) that injects a PE-only-in-memory payload used to deliver information stealers and RATs against government and critical infrastructure targets. The report includes an automated parser to extract configuration strings,…
Tag: DEFENSE EVASION

Cybersecurity researchers have uncovered VoidLink, a sophisticated malware framework targeting Linux-based cloud environments for long-term stealthy access. The malware’s modular and adaptive design, linked to Chinese threat actors, demonstrates a focus on cloud services like AWS, Azure, and Google Cloud. #VoidLink #CloudThreats…

In late October 2025, CIS CTI observed increased detections of a fake PDF converter called Crystal PDF on U.S. SLTT endpoints; analysis shows it is a managed .NET (F#) staged loader that performs in-memory execution, process injection, sandbox/VM checks, and contacts likely C2 domains. CIS links its spread to malvertising and…
CrazyHunter is a Go-based ransomware forked from the Prince builder that targets Windows environments—primarily healthcare organizations in Taiwan—using GPO abuse, BYOVD with a vulnerable Zemana driver, memory loaders, and multiple AV-killing components to rapidly propagate and evade defenses. The Trellix analysis details the full attack lifecycle, technical artifacts (including go.exe/go2.exe/go3.exe, bb.exe, crazyhunter.sys), mitigation recommendations, and IOCs for detection and response. #CrazyHunter #SharpGPOAbuse
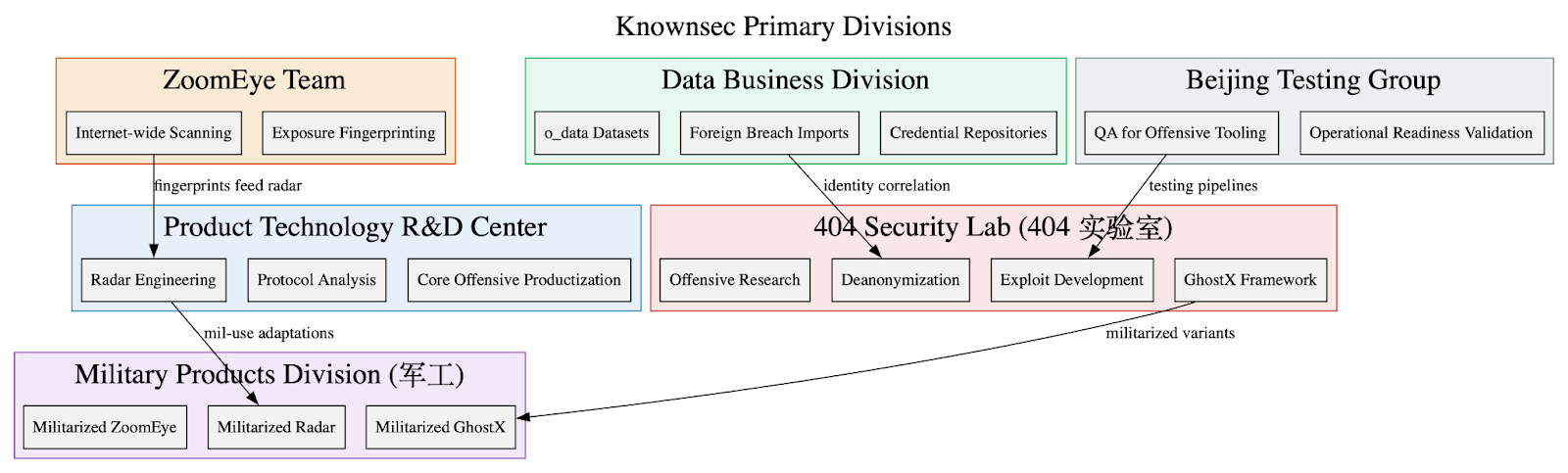
Leaked internal Knownsec documents show the company functions as a state-aligned cyber contractor providing an integrated espionage stack—ZoomEye, TargetDB, GhostX, Un‑Mail, and Passive Radar—supporting PLA/MPS/public-security and critical-infrastructure targeting worldwide. The corpus includes massive breach datasets (o_data_*), detailed TargetDB asset mappings (notably Taiwan telecom/finance/energy), and tooling for browser exploitation, mailbox takeover, PCAP-driven network reconstruction, persistence, and OPSEC/anti-forensics. #Knownsec #GhostX

SafePay emerged in late 2024 as a centralized, closed ransomware group that escalated rapidly into a global threat, using double-extortion by stealing financial and intellectual property data and pressuring victims via a Tor data leak site. Its modular Windows PE32 DLL employs compromised credentials, backdoors (e.g., QDoor), PowerShell discovery scripts, LOLBins (PsExec, regsvr32/rundll32), archiving and exfiltration tools (WinRAR, FileZilla, Rclone), defense evasion (killing AV/backup services, deleting Volume Shadow Copies, modifying boot settings), and a Cyrillic-language kill switch. #SafePay #QDoor

Zscaler ThreatLabz discovered three malicious npm packages—bitcoin-main-lib, bitcoin-lib-js, and bip40—that deploy a Node.js remote access trojan named NodeCordRAT which uses Discord for command-and-control. The malware exfiltrates Chrome credentials, .env files, and MetaMask data (including LevelDB .ldb files and seed phrases) and was distributed via postinstall scripts and PM2; #NodeCordRAT #bip40
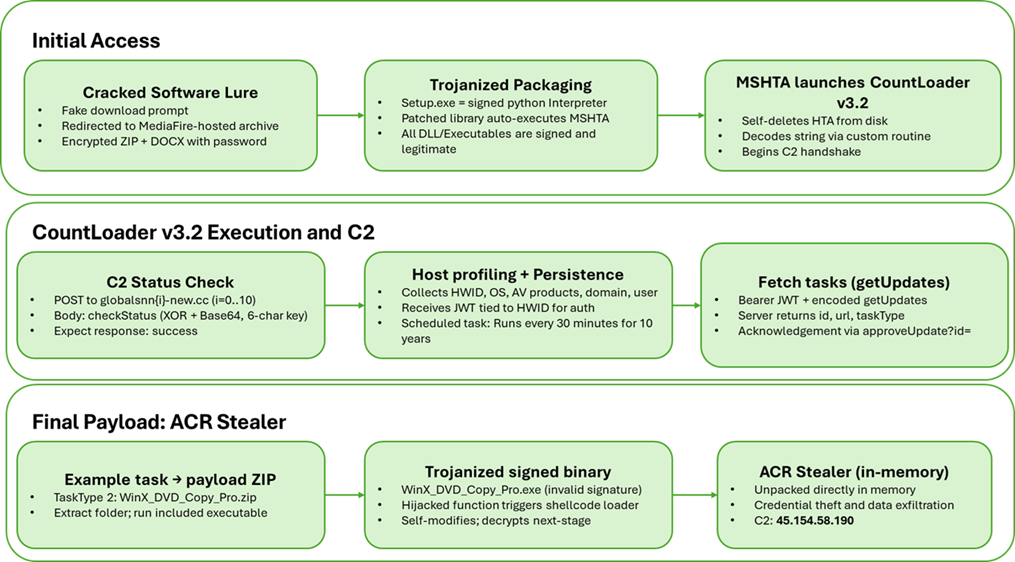
Howler Cell identified a multi-stage campaign distributing a new CountLoader v3.2 variant via cracked software sites that ultimately delivers an in-memory ACR Stealer payload. The loader expands capabilities (nine task types), employs MSHTA/PowerShell fileless execution, removable-media propagation, custom XOR+Base64 C2 encoding, and persistence via scheduled tasks. #CountLoader #ACRStealer
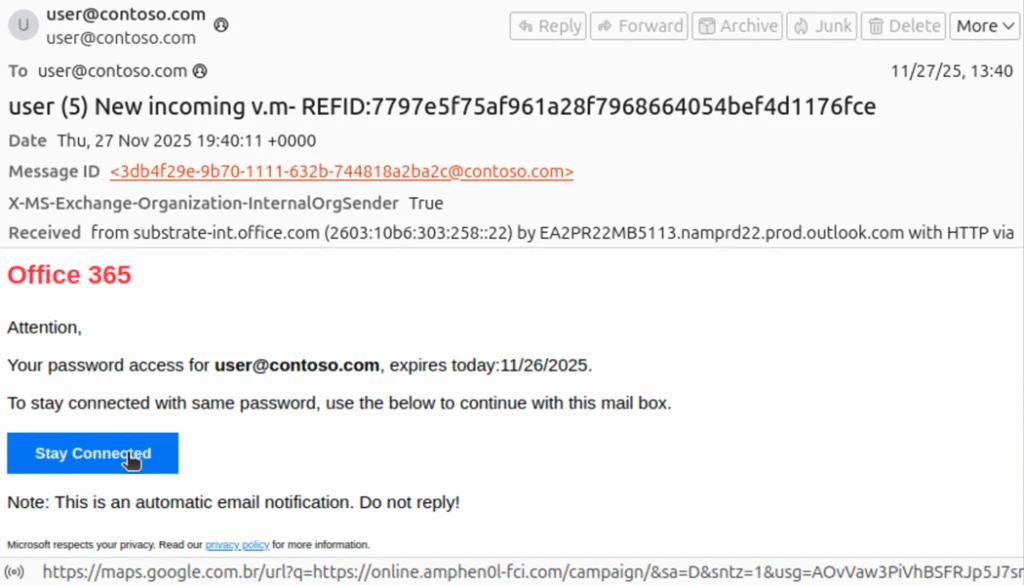
Phishing actors exploit complex mail routing and misconfigured spoof protections to send emails that appear to originate from an organization’s own domain, increasing success of credential phishing and invoice/financial scams. Microsoft observed widespread use of PhaaS platforms like Tycoon2FA in these opportunistic campaigns and recommends enforcing strict SPF/DMARC, properly configuring third-party connectors, and deploying phishing-resistant MFA to mitigate risk. #Tycoon2FA #Office365

Silver Fox, a Chinese cybercrime group, focuses on phishing campaigns in India using income tax-themed lures to distribute ValleyRAT, a modular remote access trojan. Their multi-pronged attack combines sophisticated malware techniques, SEO poisoning, and impersonation of trusted applications to target Chinese-speaking individuals and organizations worldwide. #SilverFox #ValleyRAT…

CYFIRMA attributes a targeted multi-stage, fileless espionage campaign to APT36 (Transparent Tribe) that uses weaponized LNK files masquerading as PDFs to deliver HTA loaders and in-memory .NET deserialization payloads. The operation deploys configuration and RAT payloads (ReadOnly/WriteOnly -> ki2mtmkl.dll, iinneldc.dll), adapts persistence based on detected AV products, and maintains encrypted C2 communications to 2.56.10.86 for surveillance and data exfiltration. #APT36 #ReadOnly
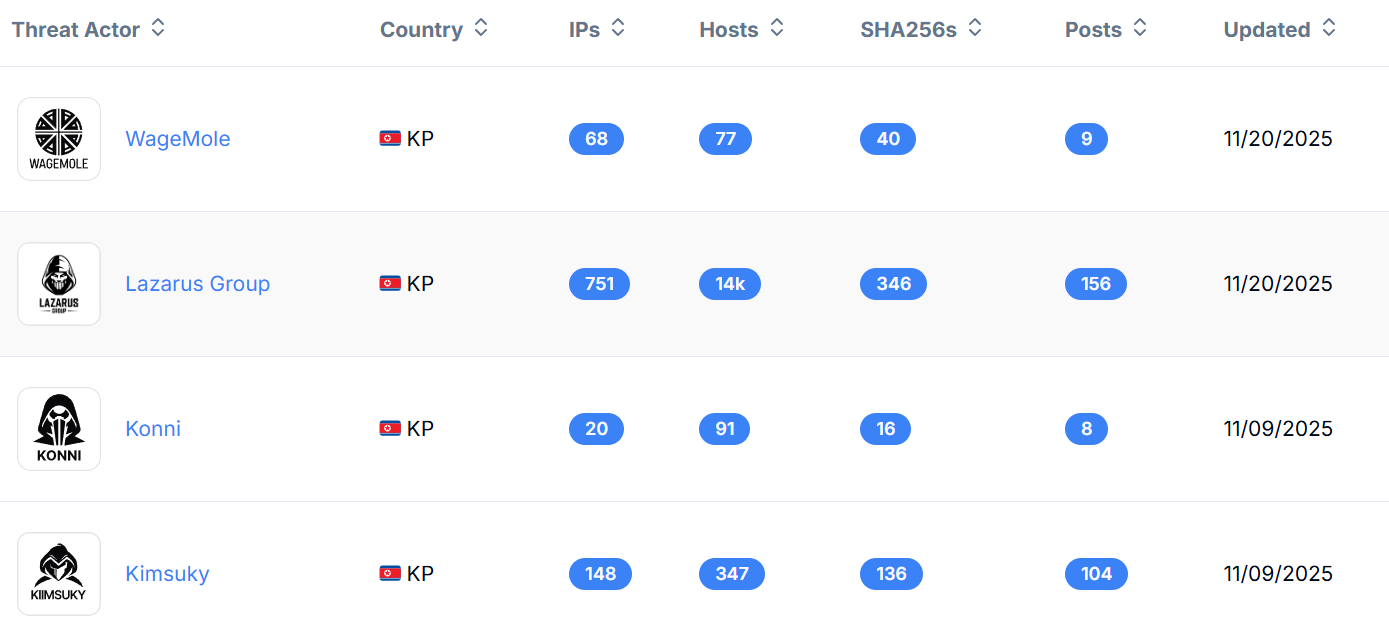
Hunt.io and Acronis mapped a broad DPRK operational infrastructure linking Lazarus, Kimsuky, and related subgroups through reused open directories, credential-harvest toolkits, FRP tunneling nodes, and certificate-linked clusters. The investigation exposed a new Linux Badcall variant, widespread MailPassView/WebBrowserPassView staging, identical FRP deployments on port 9999, and certificate pivots that reveal larger Lazarus ecosystems. #Lazarus #Badcall
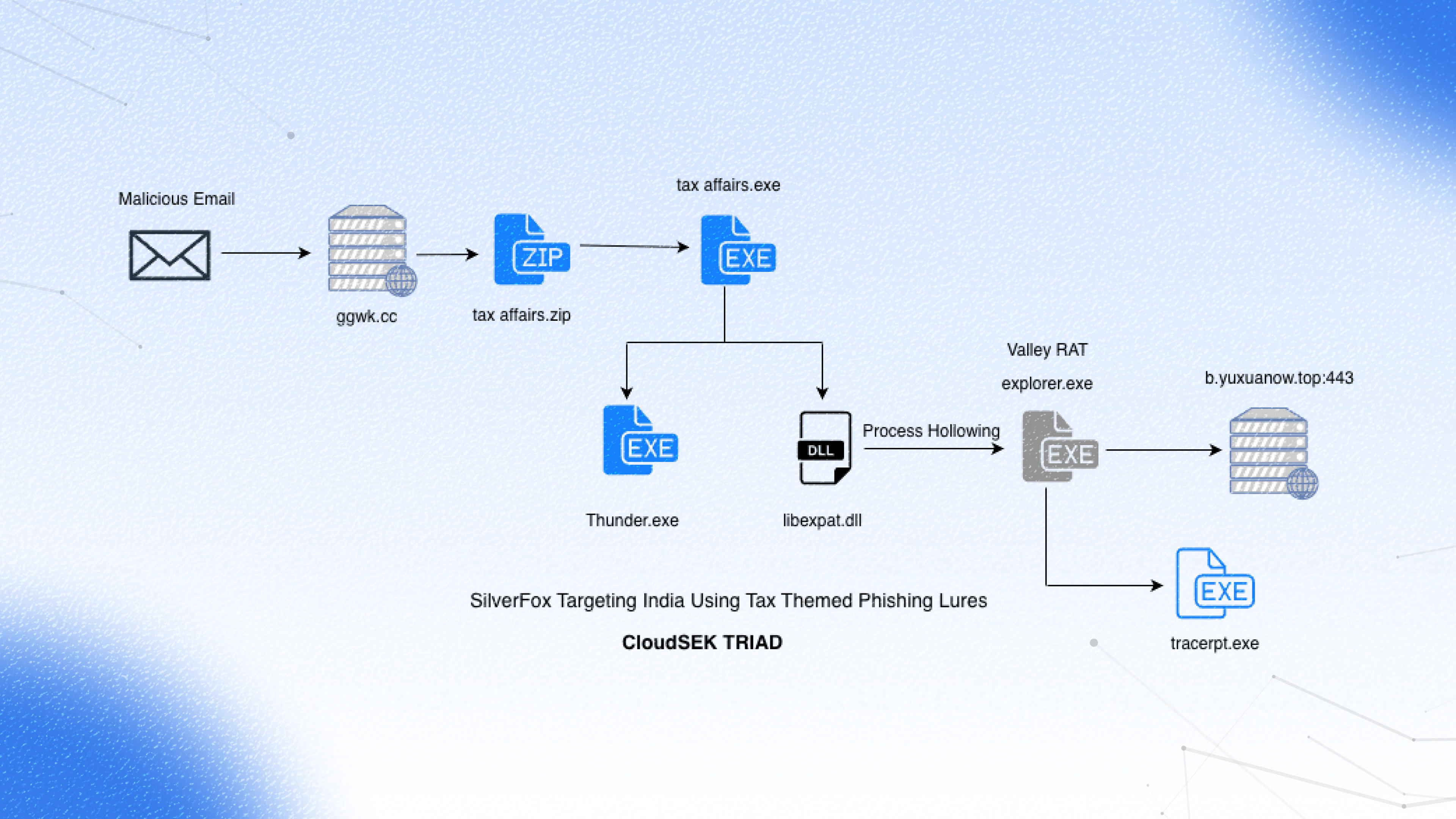
CloudSEK’s TRIAD uncovered an Income-tax-themed phishing campaign targeting India that uses an NSIS installer to drop a signed Thunder.exe and a malicious libexpat.dll, leading to in-memory Donut shellcode execution and deployment of Valley RAT. The report attributes the campaign to Silver Fox APT and details a multi-stage kill chain with DLL hijacking, process hollowing, registry-resident plugins for persistence, and a three-tier C2 infrastructure. #SilverFox #ValleyRAT

Threat actors are actively exploiting CVE-2024-36401 in GeoServer to deploy XMRig-based coin miners and auxiliary tools like NetCat, using PowerShell, bash, certutil, and custom downloaders across multiple campaigns (Type A, B, C). These campaigns reuse mining pool credentials, multiple hosting domains/IPs and employ persistence via NSSM and attempts to disable Windows…
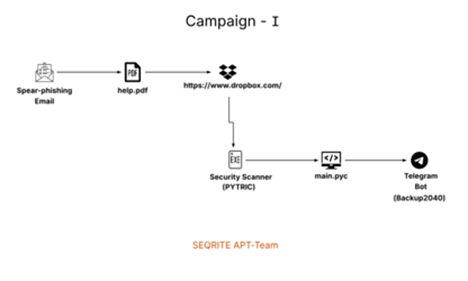
SEQRITE Labs tracked Operation IconCat (UNG0801), a Western Asia–linked activity cluster that targeted Israeli organizations using Hebrew-themed phishing lures and consistent antivirus‑icon spoofing to increase trust. Two campaigns delivered distinct implants — a PyInstaller Python wiper (PYTRIC) via a Check Point‑themed PDF and a Rust espionage implant (RUSTRIC) via a SentinelOne‑themed spear‑phishing Word document — while relying on Dropbox/HTTP C2 infrastructure and AV enumeration. #PYTRIC #RUSTRIC
