CPQ Ingenieros reports a ransomware claim attributed to the threat actor thegentlemen, alleging that its networks have been encrypted and data may be exposed. This Spain-based firm, which designs process plants across chemical, pharmaceutical, biotechnological, food, and cosmetic industries, is assessing the impact on operations, clients, and compliance. #Spain
Tag: COMPLIANCE

The growing threat from End-of-Support edge devices has become a national cybersecurity liability as threat actors exploit outdated firewalls, routers, VPN gateways, and other perimeter appliances to gain access and pivot into federal networks. The Binding Operational Directive BOD 26-02 mandates time‑bound inventory, decommissioning, replacement, and continuous discovery to eliminate these…
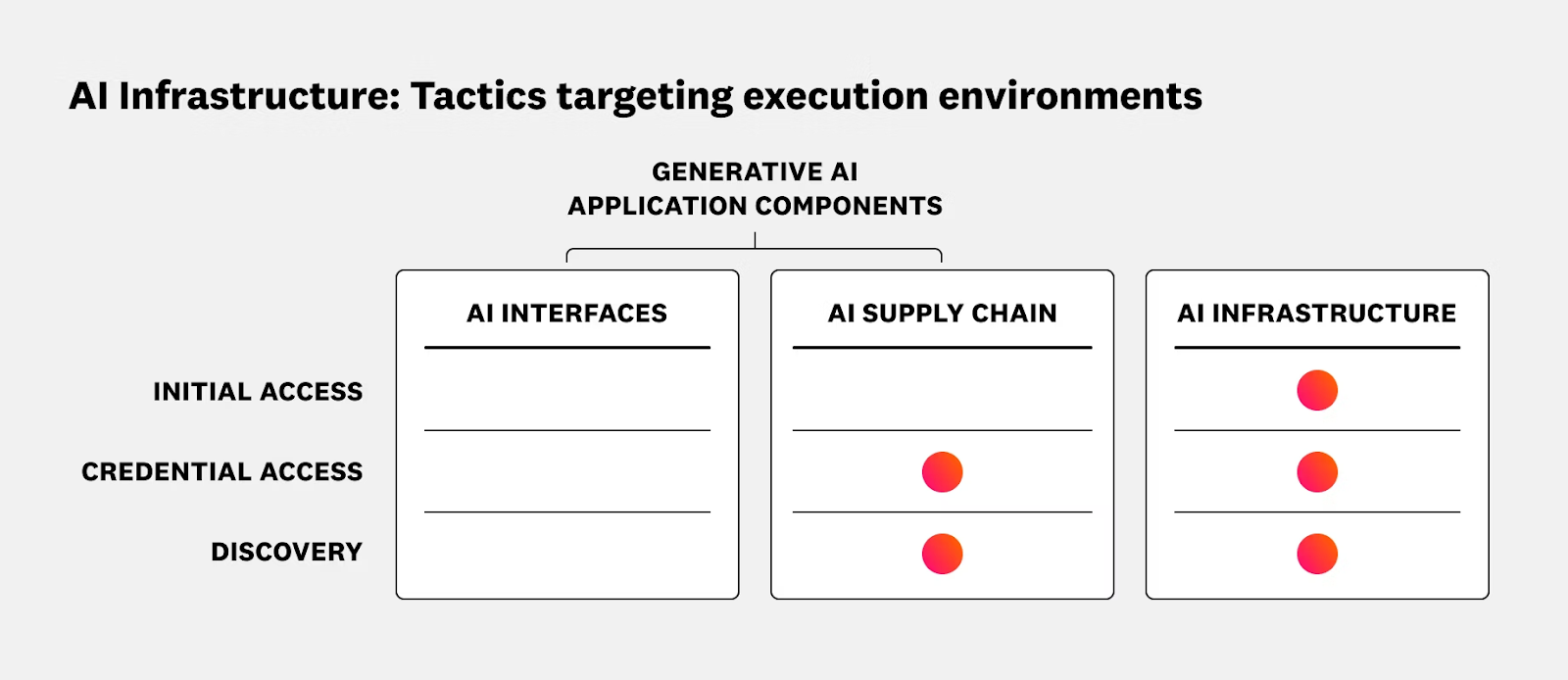
The article outlines security risks and operational best practices for running AI and ML workloads on Kubernetes and Oracle Cloud Infrastructure (OCI), emphasizing the shared responsibility model and the need to secure data planes, GPU nodes, inference services, and supply chains. It reviews recent AI-targeted incidents and promotes runtime protection, CI/CD hygiene, and integrated solutions such as Sysdig Secure with OKE to provide real-time detection and response. #ShadowRay2_0 #OCI

CISA has ordered federal civilian agencies to remove end-of-life hardware and software from networks within 12 months after warning that unsupported edge devices are being widely exploited by sophisticated threat actors. Agencies must inventory listed devices within three months, decommission them within a year, implement continuous discovery within two years, and…

Detections as Code (DaC) applies software development practices to detection rule creation and management, and Elastic has extended its detection-rules repository so users can author, test, version, and deploy rules as code across environments. The post details feature milestones (alpha → beta → general availability), new export filters and local loading options, schema auto-generation, CI/CD and unit testing examples, and training resources to help teams adopt DaC. #Elastic #DetectionRules
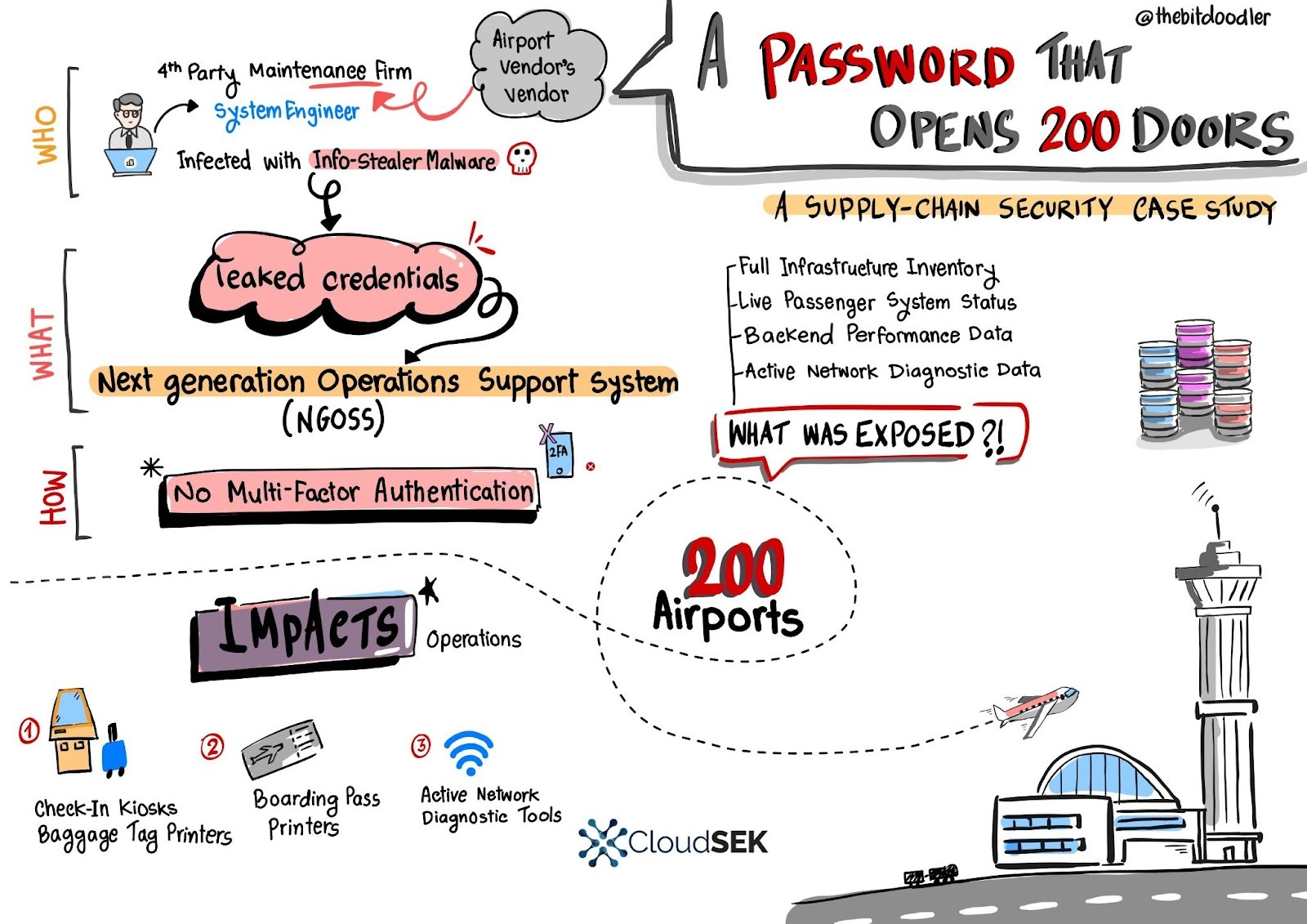
A single leaked username and password for a European fourth‑party engineer granted access to a central Next Generation Operations Support System (NGOSS) portal that managed operational dashboards for over 200 airports, exposing live infrastructure inventories, device statuses, and network diagnostic tools. SVigil detected the credential circulation and the vendor revoked access and enforced emergency MFA to avert potentially massive DoS and baggage-reconciliation outages. #SVigil #NGOSS

SecurityWeek’s Cyber Insights 2026 gathers experts who warn that cyberwarfare – driven by nation-state pre-positioning, AI-enabled operations, and rising geopolitical tensions – will escalate faster than criminal cybercrime in 2026. The report highlights blurred lines between criminal and state actors, the difficulty of attribution, and the need for improved detection, resilience,…

RapidFort raised $42 million in a Series A round led by Blue Cloud Ventures and Forgepoint Capital to accelerate its automated vulnerability elimination technology. The company’s platform secures the software lifecycle by generating SBOMs, offering near-zero-CVE container images, and applying runtime hardening to reduce attack surface while meeting standards like FedRAMP…

Write 2 sentences summarizing the content. At the end, add hashtags for specific keywords mentioned in the article—such as names of malware, threat actors, or affected organizations/systems. Avoid general terms like #malware, #ransomware, or #cybersecurity. Use this format: #Keyword1 #Keyword2…

French lawmakers approved a social media ban for children under 15 and restrictions on mobile phone use in high schools, passing the bill 130-21 in the National Assembly with implementation expected in September pending Senate review. The measure, championed by President Emmanuel Macron and aligned with recent actions in Australia and…

French police raided X’s offices as European investigations into the Grok AI chatbot focus on nonconsensual sexual deepfakes, potential child sexual abuse material, and the dissemination of Holocaust denial content. Authorities across France, the UK, and the EU — with Europol’s assistance and ICO scrutiny — have opened probes and summoned…

Civil society groups warn that NSO Group is using its submission to the Pall Mall Process to whitewash a long record of human rights abuses tied to its Pegasus spyware, while providing little transparency or evidence of enforcement. Critics and officials stress that consultation responses do not equal endorsement and call…
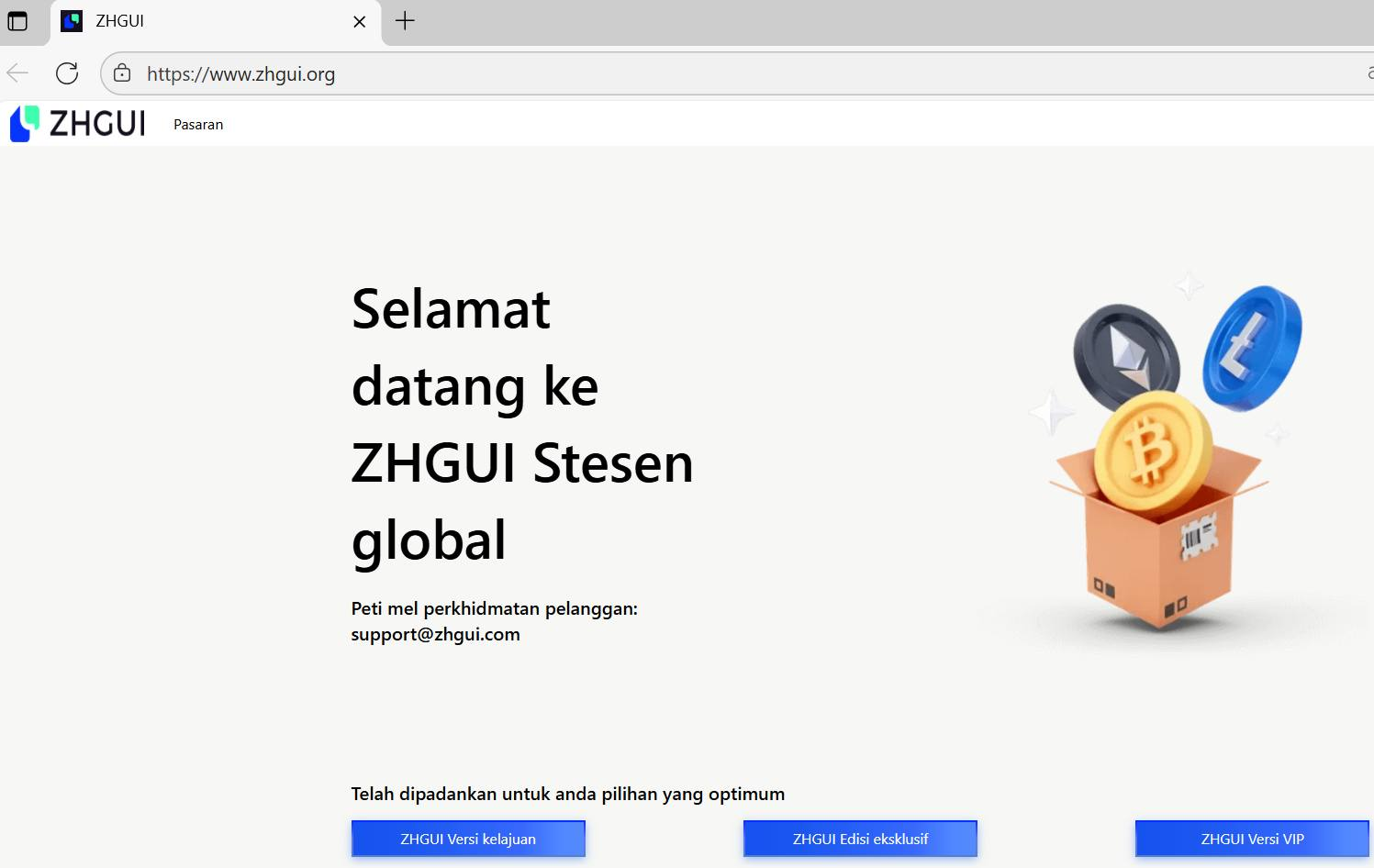
ZHGUI is a coordinated mirror-exchange and TRC20-focused fraud ecosystem that uses cloned domains, fake trading dashboards, social-engineering via WhatsApp communities, a self-submitted FinCEN MSB entry, and TRON-based wallets to harvest funds and KYC data from Mandarin-speaking investors in Southeast Asia. On-chain analysis links large USDT flows through a labelled “RazorPay” aggregation wallet (TETzN…) into an internal relay (TNKCBR…) and onward to major CEX deposit addresses, demonstrating a structured laundering pipeline. #ZHGUI #TRON

Microsoft will disable NTLM by default in the next Windows Server and associated Windows client releases as part of a multi-phase plan to eliminate the legacy protocol. Organizations should use enhanced NTLM auditing in Windows Server 2025 and Windows 11 24H2+, map dependencies, migrate to Kerberos, and test NTLM-off configurations to…
India’s Union Budget 2026–27 lays out a long-term digital infrastructure strategy focused on AI, cloud, data centres, semiconductors, and integrated cybersecurity to position India as a global hosting and manufacturing hub. Major measures include a tax holiday for foreign cloud providers until 2047, unified IT services rules, expanded semiconductor and electronics…
