TRM Labs raised $70 million in a Series C round to expand its AI capabilities for disrupting criminal networks and addressing national security risks. The funding, led by Blockchain Capital and bringing TRM’s valuation to $1 billion, will scale engineering and accelerate AI-powered investigative tools used by law enforcement and financial…
Tag: BLOCKCHAIN

Rublevka Team is an affiliate-driven cryptoscam operation that uses JavaScript-based Solana wallet drainers embedded in spoofed landing pages to trick victims into connecting wallets and signing malicious transactions, generating approximately $10.9 million in reported profits. Their infrastructure and monetization include a Telegram bot for campaign automation, shared and rotating domains, ready-made landing pages, and support for many wallet types (notably Phantom) to drain SOL and SPL tokens. #RublevkaTeam #Solana

Identity security is rapidly evolving from simple username/password models into AI-driven governance, liveness biometrics, decentralized identity, passwordless passkeys, and machine identities that will define access in 2026. Organizations must treat identity as the central control plane for digital trust and adopt technologies like self-sovereign identity and post-quantum cryptography to stay ahead of sophisticated threats. #SailPoint #SelfSovereignIdentity
Socket researchers identified a developer-account compromise in the Open VSX Registry that published malicious updates to four oorzc extensions embedding the GlassWorm loader, using staged AES-encrypted loaders and Solana transaction memos as a dynamic dead drop. The macOS-focused follow-on payload steals browser cookies, wallet files, keychain, AWS and SSH credentials and establishes persistence via a LaunchAgent; remove affected extensions, check for persistence, and rotate exposed tokens and keys. #GlassWorm #OpenVSX

Illegal cryptocurrency flows reached a record $158 billion in 2025, a 145% increase from 2024 despite the illicit share of on-chain volume dipping slightly to 1.2%. TRM Labs attributes the surge to sanctions-linked activity tied to Russia-associated networks (notably A7 and the A7A5 stablecoin), expanded nation-state use, major hacks including the Bybit breach, and growing scam and laundering sophistication. #Bybit #A7A5
TA584 increased its operational tempo in 2025, expanded geographic and language targeting, and changed its attack chains to include ClickFix social engineering, layered redirects, rapid domain rotation, and new payloads such as Tsundere Bot alongside XWorm. These changes produced high campaign churn, frequent use of PowerShell/Node.js-based installers and WebSocket/Ethereum-based C2 retrieval,…

Initial access broker TA584 has escalated operations, using hundreds of compromised aged accounts sent through SendGrid and Amazon SES to deliver geofenced redirect chains that funnel victims through CAPTCHA and ClickFix pages to run PowerShell loaders that deploy Tsundere Bot or XWorm in memory. Tsundere Bot, a Node.js-based malware-as-a-service that retrieves C2 via the Ethereum blockchain, communicates over WebSockets, checks system locale to avoid CIS languages, and supports data collection, lateral movement, SOCKS proxying and a built-in bot marketplace, is assessed to likely enable ransomware follow-on activity. #TA584 #TsundereBot

New Chainalysis research finds Chinese-language money laundering networks processed roughly 20% of illicit cryptocurrency in 2025, averaging $44 million laundered per day (about $16.1 billion) and contributing to an estimated $82 billion laundered on-chain last year. These professionalized operations advertise on Telegram, use “guarantee” marketplaces, money mules, swapping and “Black U”…

North Korean-linked group Konni (Opal Sleet, TA406) is deploying AI-generated PowerShell backdoors to target developers and engineers in the blockchain sector across the Asia-Pacific region. The campaign uses Discord-hosted lures, LNK/DOCX/CAB loaders, UAC bypasses, scheduled tasks, and XOR-encrypted in-memory execution to maintain persistence and execute C2-issued code. #Konni #PowerShell

Check Point Research identified a KONNI-linked phishing campaign targeting blockchain developers across the APAC region that uses Discord-hosted lures and weaponized LNK shortcuts to deploy a multi-stage infection chain. The operation deploys an AI-generated, obfuscated PowerShell backdoor, leverages UAC bypass and scheduled-task persistence, and communicates with a PHP-based C2 protected by a JavaScript/AES challenge. #KONNI #SimpleHelp
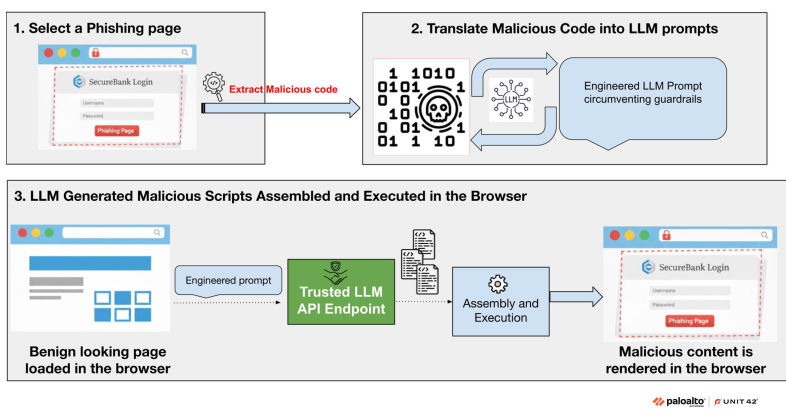
This article describes a novel AI-augmented attack where a benign webpage requests code from trusted LLM APIs, assembles malicious JavaScript in-browser at runtime, and renders personalized phishing pages that evade network-based detection. The report demonstrates a proof-of-concept that leverages prompt engineering and polymorphic LLM-generated code to bypass guardrails and recommends runtime…
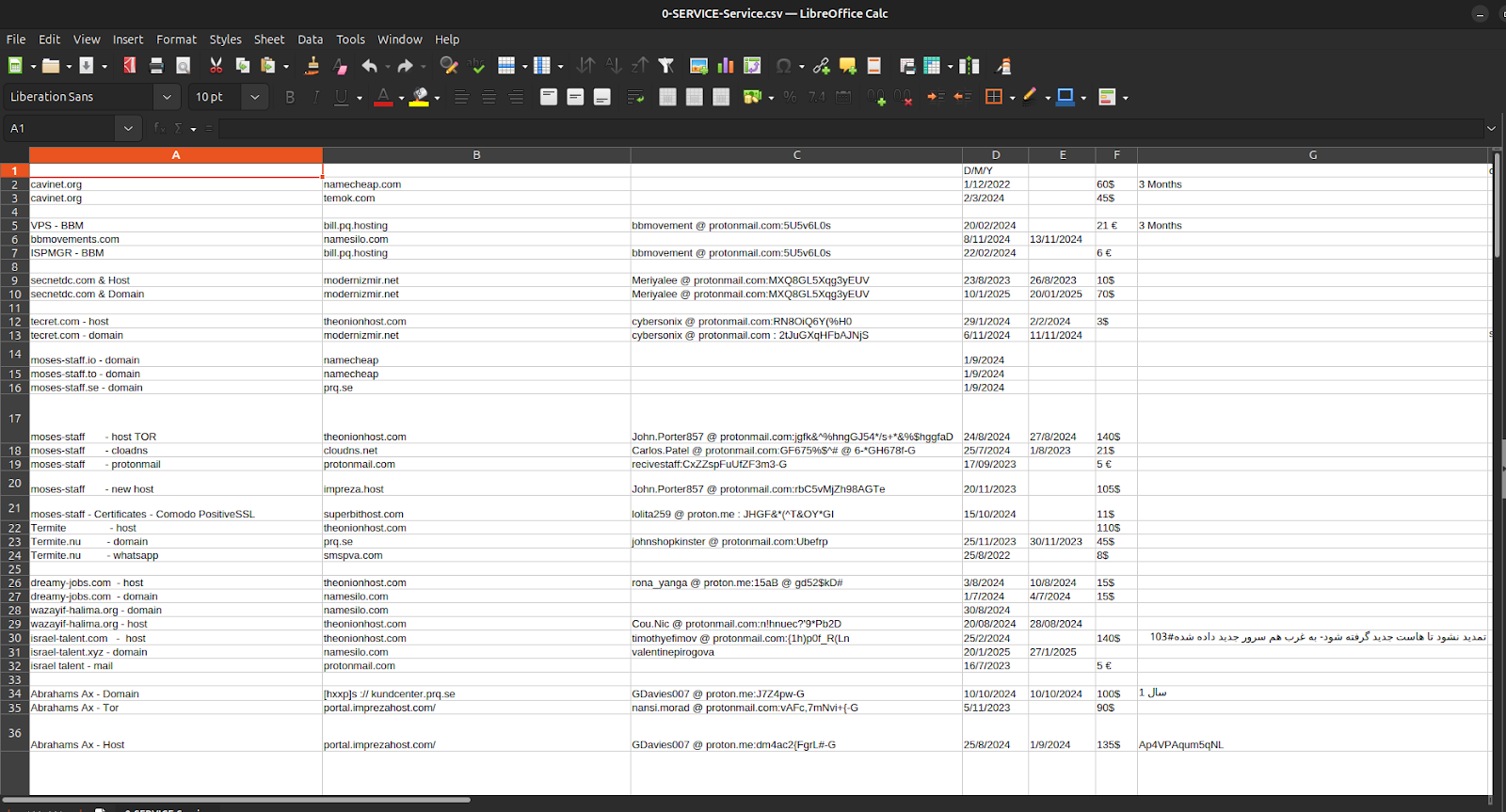
Episode 4 of the Charming Kitten / APT35 leaks exposes not sophisticated zero-day exploits but the bureaucratic infrastructure—spreadsheets, invoices, crypto receipts, hosting accounts, and one-time ProtonMail identities—that fund, procure, and maintain Iranian cyber operations. The documents tie APT35’s procurement and payment chains to Moses Staff’s leak domains and operational tooling, showing micro-crypto payments via Cryptomus, recurring European VPS providers (EDIS, Impreza), and repeatable, auditable workflows that convert state intent into persistent infrastructure. #APT35 #MosesStaff

Recorded Future / Insikt Group documents PurpleBravo, a North Korean-linked campaign that uses fraudulent developer/recruiter personas and malicious GitHub repositories to deliver infostealers and multi-platform RATs (BeaverTail, GolangGhost/PylangGhost, InvisibleFerret) targeting software developers—especially in the cryptocurrency sector and South Asia. The report details obfuscated JavaScript (Base64 + XOR), RC4/MD5 C2 protocols, registry Run-key persistence, Chrome credential-theft techniques (including DPAPI and app-bound bypasses), extensive C2 infrastructure (dozens of IPs and Astrill VPN nodes), and overlap with PurpleDelta activity. #PurpleBravo #BeaverTail

North Korean threat actors have advanced their hacking tactics by exploiting malicious Visual Studio Code projects to deliver backdoors and malicious payloads. This campaign uses sophisticated multi-stage techniques, including obfuscated JavaScript and task configuration files, to compromise target systems and maintain persistence. #NorthKorea #VisualStudioCode #Backdoor #Vercel #DPRK…

A Telegram-based illicit marketplace, Tudou Guarantee, is ceasing its major operations after processing over $12 billion in transactions, marking a significant shift in the cyber fraud landscape. Despite this, other marketplaces like HuiOne Guarantee and Xinbi Guarantee continue to operate, indicating a persistent threat environment. #TudouGuarantee #HuiOneGuarantee #XinbiGuarantee #PrinceGroup #PigButchering…
