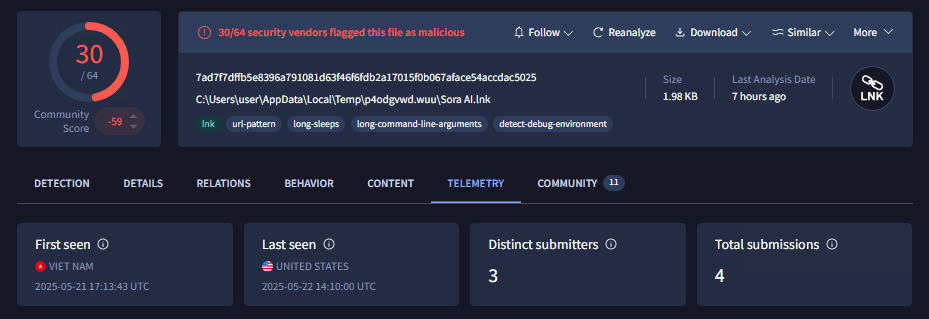
SoraAI.lnk is an information stealer malware masquerading as OpenAI’s Sora that uses Github to download its malicious payload and exfiltrate data via Telegram. It collects extensive user information including browser data, crypto wallets, game launcher configurations, and system files, before uploading the stolen data to an external hosting site if it exceeds a certain size. #SoraAI #TelegramBot #GoFile.io
Keypoints
- SoraAI.lnk is a shortcut file that initiates a multi-stage malware attack starting with PowerShell downloading payloads from a Github repository.
- The malware uses batch scripts (‘a.bat’, ‘f.bat’, ‘1.bat’) to download, extract, and execute multiple stages including a Python payload that runs the main information stealer.
- The Python payload collects data such as browser cookies, passwords, crypto wallet information, saved wifi credentials, and game launcher configuration files.
- Collected data is compressed into zip files and exfiltrated using a Telegram bot API; large files over 49MB are uploaded to ‘GoFile.io’ to avoid detection.
- The malware ensures persistence by adding autorun entries to launch its batch scripts on Windows startup.
- Targeted browsers include Chrome, Firefox, and Opera, with techniques to decrypt protected data using custom DLLs.
- Users are advised to only download files from trusted sources and use antivirus software such as K7 Total Security for protection.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – The malware uses shortcut files to launch cmd.exe and PowerShell scripts (‘SoraAI.lnk’ starts PowerShell with hidden attributes to execute batch files downloaded from Github).
- [T1105] Ingress Tool Transfer – Powershell scripts download batches and zip files from a Github repository for malware payload execution.
- [T1547] Boot or Logon Autostart Execution – ‘python.py’ adds batch scripts to Windows startup folder to achieve persistence.
- [T1005] Data from Local System – The malware collects browser cookies, passwords, crypto wallets, wifi profiles, and game launcher data from the infected system.
- [T1027] Obfuscated Files or Information – Batch scripts suppress command output and use environment isolation to avoid detection.
- [T1074] Data Staged – Collected data is compressed into a zip archive before exfiltration.
- [T1041] Exfiltration Over C2 Channel – The zip files are sent to the attacker using Telegram bot API.
- [T1102] Web Service – Large exfiltrated files are uploaded to ‘GoFile.io’ to bypass file size limitations of Telegram.
Indicators of Compromise
- [File Name] Malicious files involved in the infection chain – SoraAI.lnk (shortcut), a.bat, f.bat, 1.bat, python.py, chrome_decrypt.dll
- [File Hash] Hashes of key malicious files – D4B1F86B0D722935BDA299D37F7A2663a (SoraAI.lnk), 8358AF316ACDFD449D9E9F78FFC57500 (a.bat), 596C75805BE5AD3B44A0AAFA9E94DFC2 (f.bat), BE13272715927422332A14DBFE32CFF7 (1.bat), 9BABDE0DD32C1AB24EFB2C4D25BD0B10 (python.py), ED38E7C7E54B87841BDB013203EBF01B (chrome_decrypt.dll)
- [URL] Github repository hosting malicious payload – hxxp://github.com/ArimaTheH/a/raw/refs/heads/main/f.zip
Read more: https://labs.k7computing.com/index.php/a-soraai-clickbait/