Morphisec Threat Labs has identified a multi-stage malware known as ValleyRAT, linked to the Silver Fox APT group. This investigation reveals an evolution in the actor’s TTPs and highlights their focused targeting of high-value roles within organizations. The malware exploits both familiar distribution methods and sophisticated payload injection techniques to compromise systems. Affected: malware, remote access trojans, Silver Fox APT, finance sector, technology sector
Keypoints :
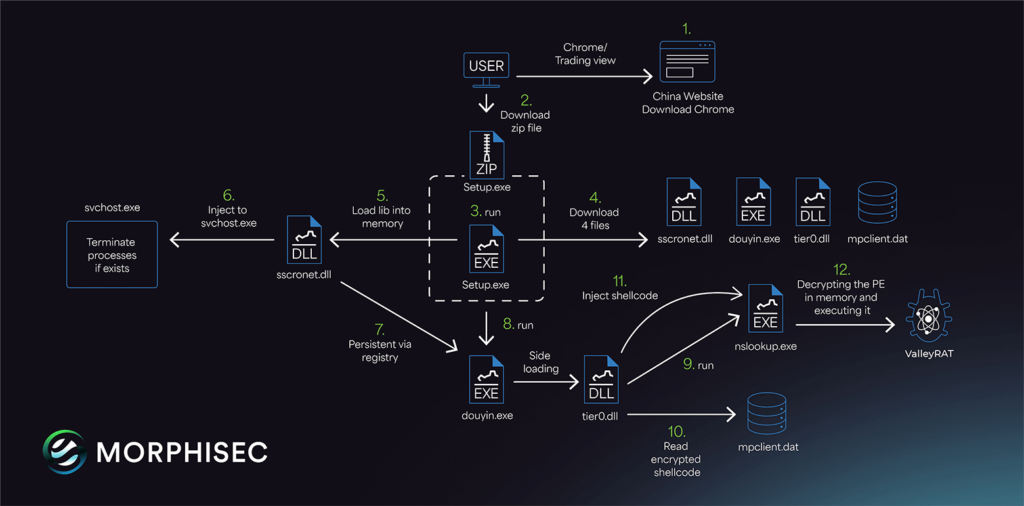
- ValleyRAT is a sophisticated multi-stage malware attributed to Silver Fox APT.
- The actor has updated their distribution tactics this year, utilizing the same URL for different versions of the attack.
- Targets include high-value roles in finance, accounting, and sales departments.
- Mimics popular software through installer file names to avoid detection.
- Employs legitimate signed executables for DLL search order hijacking.
- Utilizes phishing websites to lure victims into downloading malware.
- Payload includes the installation of files that allow for persistence and remote execution.
- Masquerades as legitimate applications like Douyin (Chinese version of TikTok) and uses DLL side-loading.
- Involves monitoring user activity, including keylogging and screen capturing, while evading detection.
- Communicates with command and control servers for additional instructions and operations.
MITRE Techniques :
- Initial Access (T1071) – Malicious payloads delivered via phishing emails and impersonated websites.
- Execution (T1203) – Running the malware through executables disguised as benign software.
- Persistence (T1547) – Creates entries in the registry to ensure the malware runs at startup.
- Privilege Escalation (T1068) – Requesting administrator privileges upon execution.
- Defense Evasion (T1211) – Utilizing DLL hijacking and process injection to avoid detection.
- Credential Access (T1056) – Keylogger functionality to capture user input.
- Collection (T1115) – Enumerating and capturing user screen data and keystrokes.
- Command and Control (T1071) – Establishes communication with external servers for further instructions.
Indicator of Compromise :
- [IP Address] 149.115.250.19
- [IP Address] 149.115.052.91
- [Domain] https://anizom[.]com/
- [Domain] https://karlost[.]club/
- [Hash] 968b976167b453c15097667b8f4fa9e311b6c7fc5a648293b4abd75d80b15562
Full Story: https://www.morphisec.com/blog/rat-race-valleyrat-malware-china/