The article discusses the evolution of fake update campaigns led by the sophisticated malware CoinLurker, which utilizes advanced techniques to exfiltrate sensitive data while bypassing security measures. CoinLurker employs obfuscation and stealth to evade detection and primarily targets cryptocurrency-related information. Affected: users of cryptocurrency wallets, cybersecurity sector
Keypoints :
- CoinLurker, written in Go, is designed to evade detection while stealing data.
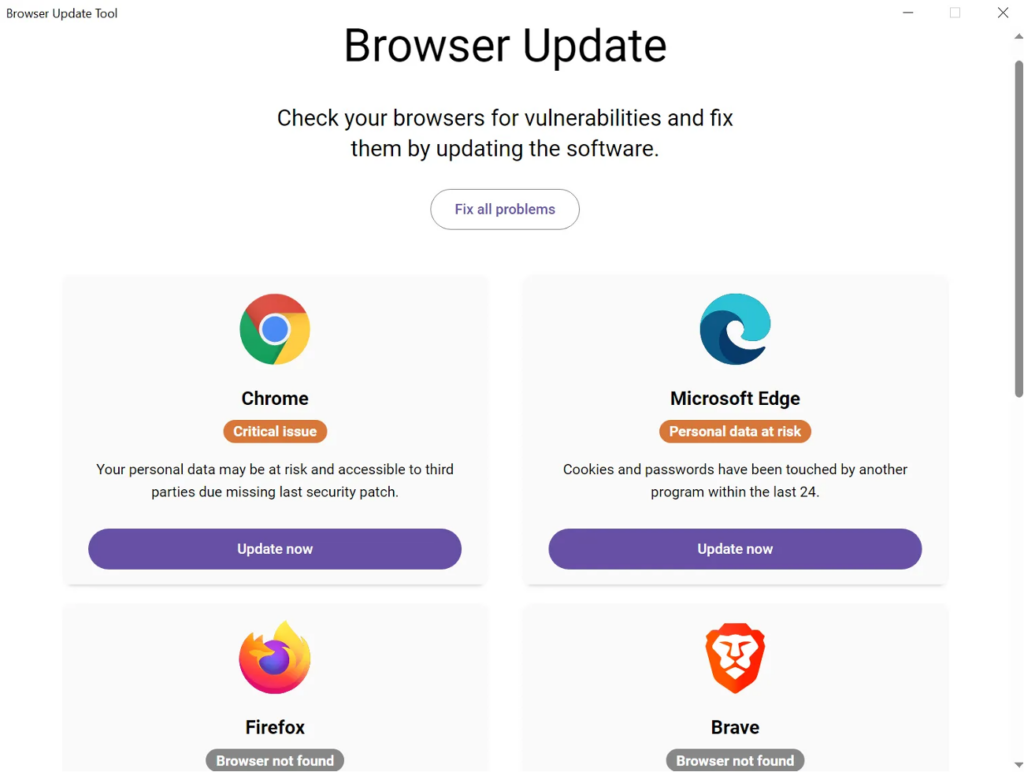
- Fake update campaigns incorporate deceptive prompt strategies that exploit user trust.
- Delivery tactics include fake software update notifications, malvertising, phishing emails, and compromised sites.
- Microsoft Edge Webview2 is leveraged to mask the malware’s execution.
- Obfuscation techniques like EtherHiding are used to conceal malicious payloads.
- CoinLurker targets directories associated with cryptocurrency wallets for data exfiltration.
- Morphisec’s Automated Moving Target Defense technology helps in preemptively blocking such attacks.
MITRE Techniques :
- T1041: Exfiltration Over Command and Control Channel – CoinLurker uses socket-based communication for C2 operations.
- T1071: Application Layer Protocol – CoinLurker communicates using HTTP/HTTPS protocols.
- T1203: Exploitation for Client Execution – Utilizes deceptive updates to initiate infections.
- T1483: Domain Generation Algorithms – CoinLurker employs dynamically resolved domains to evade detection.
- T1560: Archive Collected Data – It targets directories associated with cryptocurrency wallets.
Indicator of Compromise :
- [SHA-256] 324e1bf24f13d5a8f45cc5ee25d3dfe330a7e755b19901549976f2db02ca4fa4
- [SHA-256] c8adb9bf6997a9fa2738a09600a60abc4fb6334aa54b24166cf042afdc5a1064
- [SHA-256] a7eca930c2aa851cae3475cb4f5d599058816d51e1cc55a82ae976a030794aac
- [URL] md928zs[.]shop/endpoint
- [Domain] zovik[.]info
Full Story: https://www.morphisec.com/blog/coinlurker-the-stealer-powering-the-next-generation-of-fake-updates/