This article details the discovery and analysis of a suspicious Mach-O file named wsus, along with a suite of binaries targeting macOS systems primarily used by Chinese users. The analysis indicates possible links to Meiya Pico, a company involved in surveillance technology. Affected: macOS systems, Chinese communication applications like WeChat and QQ, and potentially users in China.
Keypoints :
- Suspicious Mach-O file named wsus discovered on VirusTotal.
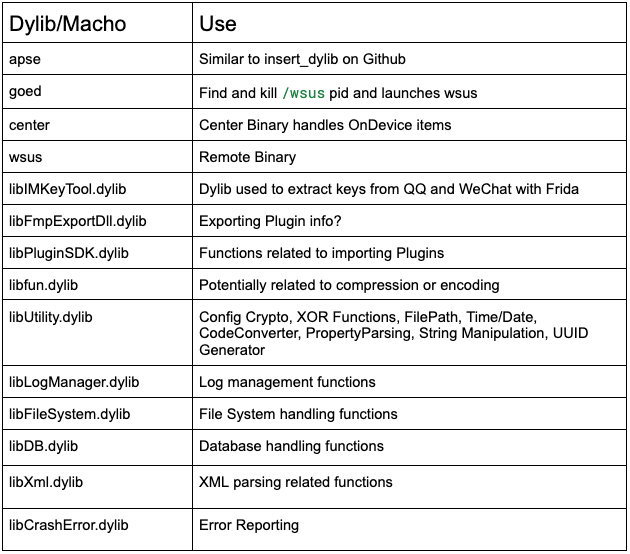
- Over 20 related binaries designed to capture data from macOS systems.
- The suite includes binaries for popular applications among Chinese users.
- Binary ‘goed’ is a misspelled version of Apple’s geod daemon.
- The suite performs obfuscation tactics to appear legitimate.
- Insights gathered suggest ties to Meiya Pico, a surveillance tech company.
- Installer package signed by “weihu chen” with associations to a tech partnership.
- Malware capabilities include data capture, configuration checks, and remote messaging.
- Links to both macOS and Windows surveillance technologies.
MITRE Techniques :
- T1070.001 – Indicator Removal on Host: Uninstall capabilities through CInstallProgress::CInstallProgressImp::Uninstall().
- T1583.001 – Acquire Infrastructure: Use of dynamic libraries to establish persistence and functionality.
- T1133 – External Remote Services: Communication via RPC for remote actions and updates.
- T1059.001 – Command and Scripting Interpreter: Execution of shell commands through functions like ExecTerminal().
- T1027 – Obfuscated Files or Information: Binaries use deceptive names and obfuscated file paths.
Indicator of Compromise :
- [SHA-256] 0fd32b8f304531e121e19a50f64586a446bf74818caa645bad8d6b71673a350a
- [SHA-256] d82e7ae41f2ed92136343e1ee8cef780704447af476b59e2e3bdd8d1b84dbb23
- [SHA-256] 203e82eb0085701598f21ef2478fad149e8e68335ce8602b118b23638be951e3
- [IP Address] 116.198.18.202
- [Signing Signature] weihu chen (QPV7YX8YQ9) – Apple Team ID Signature (Since Revoked)
Full Story: https://blog.kandji.io/pasivrobber