OtterCookie is a new stealer malware linked to the North Korean Lazarus Group, distributed via fake freelance job offers targeting professionals in tech, finance, and cryptocurrency sectors. It steals browser credentials, macOS keychains, and crypto wallets before exfiltrating data to a U.S.-based server and deploying a second-stage payload called InvisibleFerret. #OtterCookie #LazarusGroup #InvisibleFerret #ContagiousInterview #ANYRUN
Keypoints
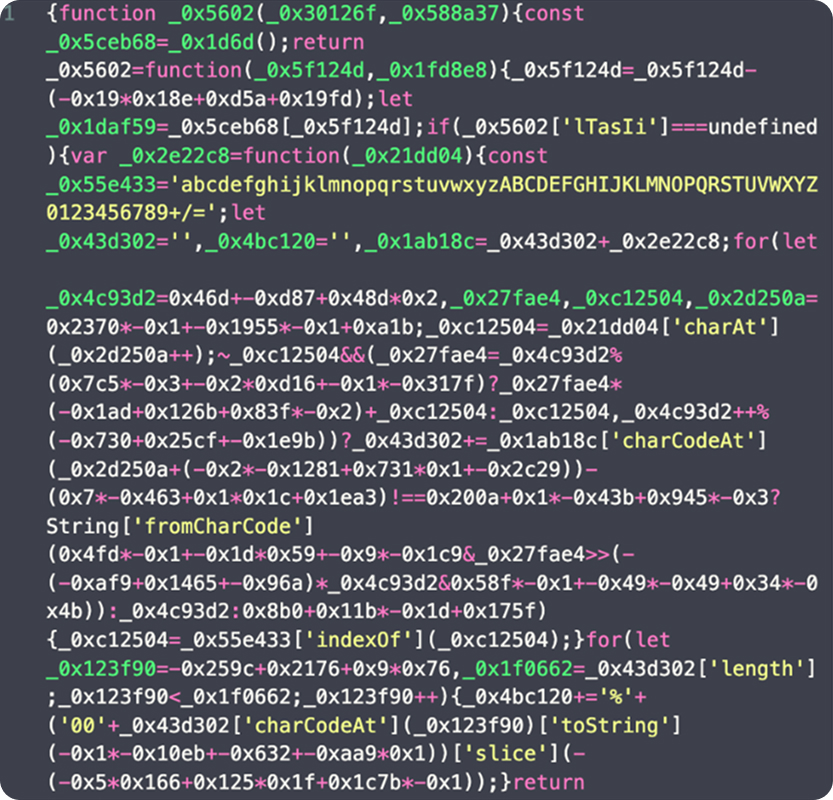
- OtterCookie is a JavaScript-based stealer malware distributed through deceptive freelance job offers within the Contagious Interview campaign.
- The malware executes payloads fetched from an external API via a require() call, triggered by an intentional app failure during initialization.
- Targets include browser credentials, macOS keychains, and cryptocurrency wallets such as Solana and Exodus, along with related browser extensions.
- Data is exfiltrated using port 1224 to a command-and-control server located in the United States (144.172.101.45), reusing tactics from previous Lazarus campaigns.
- OtterCookie facilitates multi-stage attacks by deploying InvisibleFerret, a cross-platform RAT, to maintain persistent access.
- ANY.RUN’s interactive sandbox detects OtterCookie early, including its obfuscated payload, and maps its behavior to MITRE ATT&CK techniques.
- The malware’s social engineering relies on clean, seemingly legitimate Node.js code repositories to lower victim suspicion.
MITRE Techniques
- [T1082] System Information Discovery – OtterCookie collects detailed system information to build a host profile (‘OtterCookie collects detailed information from the victim’s system’).
- [T1003] OS Credential Dumping – Accesses sensitive files including browser credential stores and macOS keychains for data theft (‘malware accesses sensitive local files such as /etc/passwd and /etc/shadow, along with browser credential stores and OS keychains’).
- [T1071] Application Layer Protocol – Uses HTTP(S) protocol to communicate with the command-and-control server for exfiltration (‘communicate with the command-and-control server (144.172.101.45) for data exfiltration’).
- [T1571] Non-Standard Port – Employs port 1224 for data exfiltration to evade detection (‘use of an uncommon port—1224—to evade standard detection mechanisms’).
Indicators of Compromise
- [IPv4] Command-and-control servers – 144.172.101.45 (exfiltration server), 135.181.123.177 (related infrastructure)
- [Domain] Remote API for payload delivery – chainlink-api-v3.cloud
- [URL] Payload and API endpoints – http://144.172.101.45:1224/, http[:]//chainlink-api-v3[.]cloud/api/service/token/56e15ef3b5e5f169fc063f8d3e88288e
- [SHA256 Hashes] Malware samples – aa0d64c39680027d56a32ffd4ceb7870b05bdd497a3a7c902f23639cb3b43ba1, 071aff6941dc388516d8ca0215b757f9bee7584dea6c27c4c6993da192df1ab9, and 2 more hashes
- [File Name] Suspicious archive – 0xhpenvynb-mvp_gamba-6b10f2e9dd85.zip
- [Cryptocurrency Wallet] Targeted Solana wallet – V2grJiwjs25iJYqumbHyKo5MTK7SFqZSdmoRaj8QWb9
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/ottercookie-malware-analysis/