The 2025 variant of the ViperSoftX PowerShell stealer showcases enhanced modularity, stealth, and persistence compared to its 2024 predecessor, with upgraded encryption and victim identification techniques. It targets cryptocurrency wallets and browser extensions while employing dynamic infrastructure synchronization and multilayer persistence mechanisms. #ViperSoftX #PowerShellMalware #CryptocurrencyStealer
Keypoints
- The 2025 variant uses a GUID-style mutex with longer sleep delays to evade sandbox and behavioral detection.
- Persistence is achieved via a three-layer fallback mechanism including scheduled tasks, registry run keys, and startup folder batch scripts.
- Unique 64-character hex GUIDs are generated per infection for stealthy victim identification and tracking.
- Communication utilizes base64-encoded HTTP GET requests and XOR-encrypted payloads to evade intrusion detection systems.
- Shift from deprecated WebClient to modern HttpClient enhances stealth by mimicking legitimate network behavior.
- Supports a wider range of cryptocurrency wallets, browser extensions, and password managers for expanded data theft capabilities.
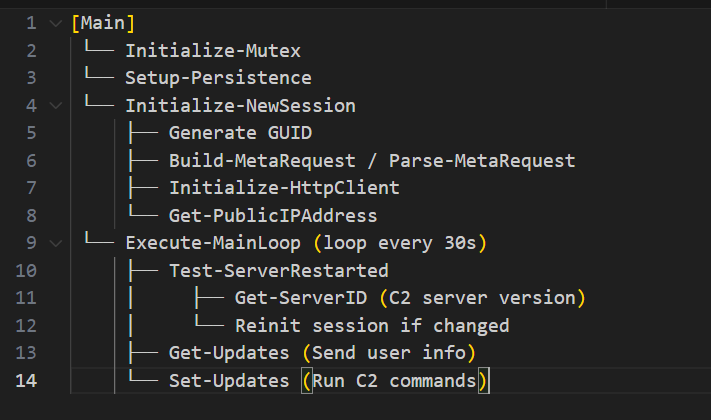
- Includes functionality to detect and adapt to C2 server redeployments by syncing server IDs and session states.
MITRE Techniques
- [T1053] Scheduled Task/Job – Registers a Windows scheduled task named “WindowsUpdateTask” to maintain persistence by running a batch file at user logon (“Registers a Windows scheduled task named as WindowsUpdateTask that runs the batch file at user logon”).
- [T1543.003] Create or Modify System Process: Windows Service – Uses Run registry key under HKCU for persistence (“Code to achieve persistence using the Windows Registry”).
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – Places a batch file in the user’s startup directory (“Places a bat file in the user’s startup directory”).
- [T1071.001] Application Layer Protocol: Web Protocols – C2 communication over HTTP GET requests encoded in base64 (“Constructs a HTTP GET request, encodes it in base64, and stores it in a variable”).
- [T1027] Obfuscated Files or Information – Payloads are XOR encrypted before being sent and decrypted from C2 server responses (“Encrypts the payload using a basic XOR cipher … Decrypts the received data”).
- [T1059.001] Command and Scripting Interpreter: PowerShell – Executes decoded payloads as PowerShell background jobs enhancing stealth (“Creates PowerShell jobs to run each decoded payload”).
- [T1033] System Owner/User Discovery – Collects victim’s public IP address using web services (“Tries multiple web services in fallback order to get public IP address”).
- [T1552.001] Unsecured Credentials: Credentials In Files – Targets browser wallets and password managers including MetaMask, Coinbase, and Keepass configurations (“Supports a larger list of extensions and wallets … making it easier to maintain or expand the malware’s functionalities”).
Indicators of Compromise
- [File Hash] Samples of malware variants – FEAA4AC1A1C51D1680B2ED73FF5DA5F22025 (2025 variant), 6549099FECFF9D41F7DF96402BCCDE9B (2024 variant)
- [File Name] Persistence scripts and payloads – winconfig.ps1 (self-copy location), hidden .bat launcher scripts in startup folder
- [Registry Key] Persistence mechanism – Run registry key under HKCU for auto-execution
Read more: https://labs.k7computing.com/index.php/in-depth-analysis-of-a-2025-vipersoftx-variant/