Threat actors frequently abuse legitimate remote access tools (RATs) such as ConnectWise ScreenConnect, Atera with Splashtop, and FleetDeck to deploy malware and conduct espionage. Notable campaigns include Social Security Administration spoofing in the U.S. and finance-themed attacks targeting Brazilian, French, and German speakers. #ConnectWiseRAT #FleetDeck #AteraSplashtop #SocialSecuritySpoofing
Keypoints
- ConnectWise ScreenConnect is the most abused legitimate RAT, appearing in 56% of active threat reports involving legitimate RATs in 2024.
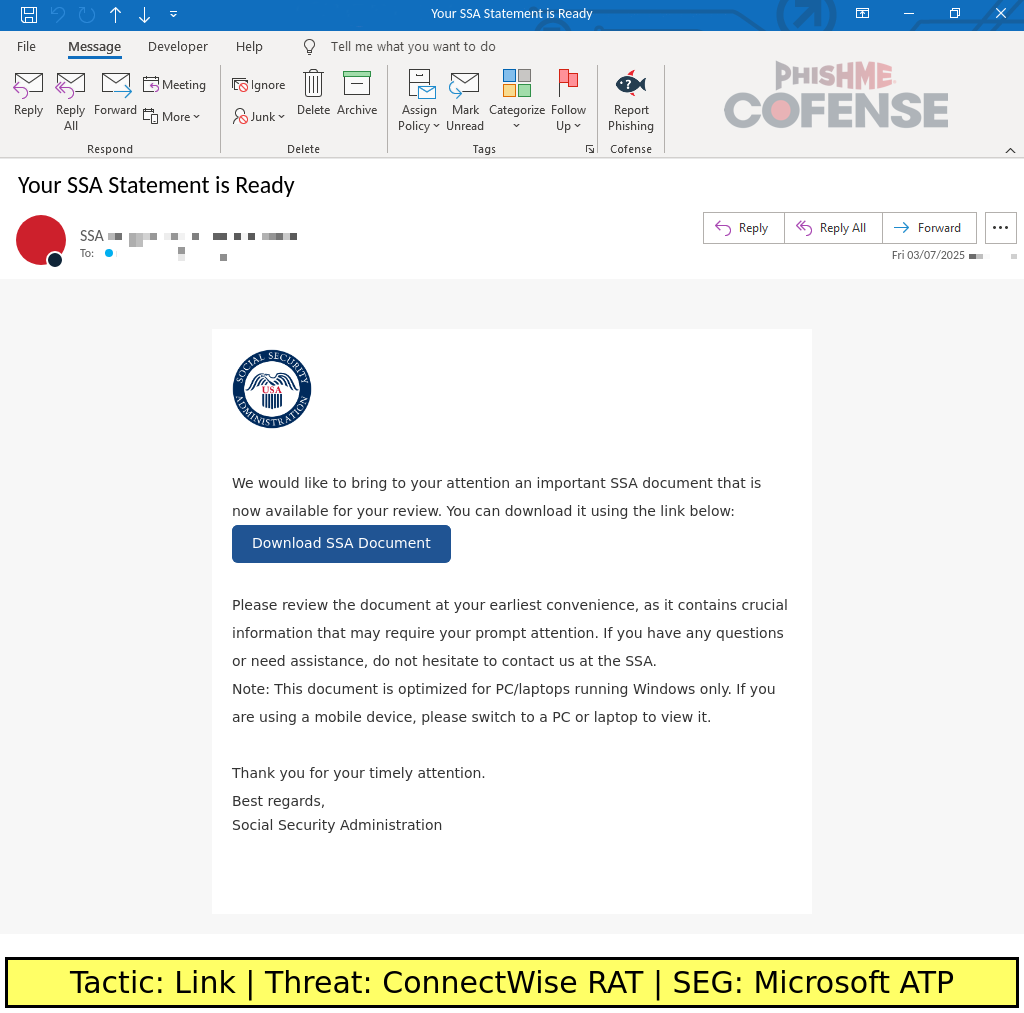
- Social Security Administration spoofing campaigns use ConnectWise RAT to distribute malicious payloads via benefit-themed emails in the U.S.
- FleetDeck saw high usage in mid-2024 with finance-themed campaigns targeting French and German speakers, often using invoice-themed emails.
- Atera with Splashtop integration is leveraged in Brazilian Portuguese language campaigns under legal or finance themes, exploiting a 30-day free trial for prolonged access.
- Threat actors exploit the legitimacy and free trial offerings of these RATs to deploy malware and maintain covert access in victim environments.
- Additional less common RATs abused include LogMeIn Resolve (GoTo RAT), Gooxion RAT, PDQ Connect, Mesh Agent, N-Able, and Teramind, each targeting specific languages or regions.
- Many campaigns utilize spoofed emails containing links that lead to RAT agent installers disguised as legitimate documents or software.
MITRE Techniques
- [T1071] Application Layer Protocol – RAT agents communicate with C2 servers using cloud infrastructure and custom URLs (e.g., “C2 servers … generally are formatted like …”).
- [T1190] Exploit Public-Facing Application – Threat actors exploit free trials and legitimate enterprise RAT features to gain access (“offer a 14-day free trial that is often abused by threat actors”).
- [T1204] User Execution – Victims are socially engineered to click embedded links in phishing emails that download RAT installers (“emails claim to deliver updated Social Security benefits statements … with embedded links”).
- [T1566] Phishing – Use of spoofed emails themed as official notifications such as Social Security benefits, invoices, or legal notices to trick victims (“Brazilian Labor Court-spoofing email … delivered an embedded link …”).
- [T1105] Ingress Tool Transfer – RAT agent installers are delivered via malicious links hosted on domains like files[.]fm and hosted on threat actor-controlled infrastructure (“embedded link to a document hosted on files[.]fm … delivers the ConnectWise RAT installer”).
Indicators of Compromise
- [File Names] Malicious RAT installers disguised as legitimate software or documents – examples include “PDF viewer.exe,” “OneDriveClient.exe,” and other executable agents.
- [Domains] C2 infrastructure domains used by threat actors – examples include “verify[.]uniupdate[.]net” for ConnectWise RAT and “files[.]fm” for shared file-themed campaigns.
- [URLs] Phishing and download URLs embedded in emails, often customized with random alphanumeric characters for ConnectWise RAT C2 servers; examples include custom URLs on ConnectWise cloud infrastructure.
- [Endpoints] Network API endpoints used by Atera and Splashtop agents for C2 communications, such as multiple relay servers with IPv4 addresses in their URLs.