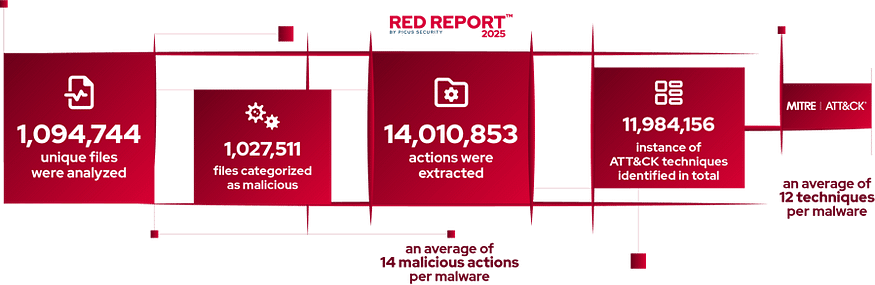
This article draws from the Picus 10 Critical MITRE ATT&CK Techniques report, this report highlights the 10 most common MITRE ATT&CK techniques used by cyber threat actors, based on analysis of over 1 million malware samples throughout 2024.
Report Keypoints:
- 93% of malicious actions were carried out using the top 10 ATT&CK techniques.
- Credential-stealing malware surged from 8% (2023) to 25% (2024).
- Malware is more complex, averaging 14 malicious actions and 12 ATT&CK techniques per sample.
- Evasion and persistence techniques like process injection and autostart execution are increasingly used.
- Encrypted communication (HTTPS, DoH) is now standard for hiding malicious traffic.
TOP 2— MITRE ATT&CK T1059 Command and Scripting Interpreter
Command and scripting interpreters (e.g., PowerShell, VBScript, Unix shells) are vital for automating tasks by system administrators and programmers. However, attackers exploit these tools to run harmful code on local and remote systems, carrying out activities like data collection, payload deployment, sensitive information access, and persistence via malicious binaries triggered at login. Since these pre-installed languages directly interact with the OS API, adversaries can operate discreetly, evading weak process monitoring. They also misuse LOLBins (Living Off the Land Binaries) — native system utilities used routinely — to download and execute files, perform reconnaissance, and exfiltrate data, often bypassing security policies that block known malicious executables. Although the T1059 technique is tied to MITRE ATT&CK’s Execution tactic, attackers leverage native OS utilities across various tactics to achieve their objectives.
Threat Research references that discuss T1059 Command and Scripting Interpreter
NimDoor macOS Cryptocurrency Stealer
North Korea-linked threat actors use AppleScript and Bash scripts to execute malicious commands and maintain control over compromised systems. The attack begins with social engineering via Telegram and fake Zoom SDK update scripts, which, once executed, trigger a multi-stage infection. A hex-encoded AppleScript runs every 30 seconds, beaconing to hardcoded C2 servers to exfiltrate process lists and execute remote scripts, effectively acting as a backdoor. Additionally, Bash scripts are used to steal sensitive data such as Keychain credentials and browser information
Auto-color Malware
Technique involves the execution of arbitrary commands through command-line interfaces or scripting environments. Once the Auto-color malware is manually executed with root privileges, it opens a reverse shell and uses command interpreters to execute arbitrary commands, modify or create files, act as a proxy, and dynamically alter configurations. This behavior enables the attacker to maintain control over the compromised system, evade detection, and persist by hooking into system processes. The malware also uses custom encryption for command-and-control (C2) communication and hides its network activity by manipulating system files like /proc/net/tcp, showcasing a sophisticated use of T1059 to maintain stealth and control.
CrazyHunter Ransomware
In the case of the MacKay Memorial Hospital incident, CrazyHunter leveraged batch scripts to orchestrate the execution of multiple components. These scripts initiated the disabling of endpoint protection tools, deployed the ransomware payload, and included fallback routines to ensure execution even if earlier steps failed. Specifically, the attackers used scripts to run executables like go2.exe and go.exe to disable EDR via a vulnerable driver (zam64.sys), followed by go3.exe to deploy the ransomware. If these failed, additional executables like av-1m.exe and bb.exe were triggered to kill antivirus processes and load the ransomware kernel driver. This procedural use of scripting interpreters allowed the attackers to automate and control the infection process, evade defenses, and ensure persistence across the compromised network.
SVG Smuggling via JavaScript Redirects
Embedding obfuscated JavaScript within SVG image files to execute malicious commands in the victim’s browser. This technique allows attackers to bypass traditional detection mechanisms by hiding script logic inside seemingly harmless image formats. The procedure begins with a phishing email — often from spoofed or lookalike domains — containing a malicious SVG file either as an attachment or a link. When the recipient opens the file in a browser, the embedded JavaScript (hidden in a CDATA section) decrypts a secondary payload using a static XOR key. This payload then uses JavaScript functions like Function() and atob() to reconstruct and execute a redirect to an attacker-controlled URL, often including a Base64-encoded identifier for tracking. This method avoids dropping files or requiring user interaction, making it stealthy and effective for credential harvesting or further exploitation.
SonicWall SMA Exploitation via OVERSTEP
UNC6148 campaign targeting SonicWall SMA 100 series appliances. This technique involves the use of command-line interfaces and scripting languages to execute malicious commands. In this case, after gaining access using stolen administrator credentials, the attacker established a reverse shell — likely through an unknown vulnerability — and used built-in command-line tools (cat, chmod, cp, etc.) to perform reconnaissance and manipulate files. They then deployed the OVERSTEP backdoor by executing a series of shell commands to decode and install a malicious ELF binary, modify system boot scripts, and preload the malware via /etc/ld.so.preload. This allowed the malware to hijack standard library functions, conceal its presence, and persist across reboots. The attacker also used shell commands to exfiltrate sensitive data and clean logs, demonstrating how T1059 enables stealthy, persistent control over compromised systems through direct command execution.
Android Cryptojacker Disguised as Banking App Exploits Device Lock State
The malware, disguised as a legitimate banking app, uses XMRig, an open-source Monero miner, embedded within a fake application. Once installed, the app monitors the device’s lock state and battery level. When the device is locked, it silently downloads and decrypts a malicious .so payload, writes it as an executable (d-miner), and uses command-line arguments to launch XMRig via a native command interpreter. This execution is triggered using Java methods that construct and pass mining parameters—such as pool address, wallet ID, and CPU thread count—to the miner. The mining halts when the device is unlocked and resumes upon locking, allowing it to persist stealthily. This abuse of scripting and command execution aligns directly with T1059, where adversaries use interpreters to run malicious code, in this case, to hijack device resources for unauthorized cryptomining.
Rainbow Hyena Phishing Alert
Attackers distribute phishing emails with malicious .LNK files embedded in polyglot .ZIP archives. When a victim opens the .LNK file, it triggers a PowerShell command that searches for and executes a malicious DLL using rundll32.exe. This DLL, part of the custom backdoor PhantomRemote, collects system information and communicates with a command-and-control (C2) server. The backdoor then receives and executes further commands via cmd.exe, such as downloading additional payloads or running shell commands, effectively leveraging scripting interpreters to maintain control and evade detection.
