Zscaler ThreatLabz identified a March 2026 campaign that weaponized an OpenClaw “DeepSeek-Claw” skill to trick AI agents and developers into executing concealed installers that deploy Remcos RAT or GhostLoader. The attacks used DLL sideloading of a signed GoToMeeting binary, in-memory ETW/AMSI patching, TEA decryption for Remcos, and an obfuscated Node.js installer for GhostLoader to achieve persistence and data theft. #Remcos #GhostLoader
Keypoints
- A malicious OpenClaw “DeepSeek-Claw” skill was published to manipulate AI agentic workflows and developers into executing poisoned installation instructions.
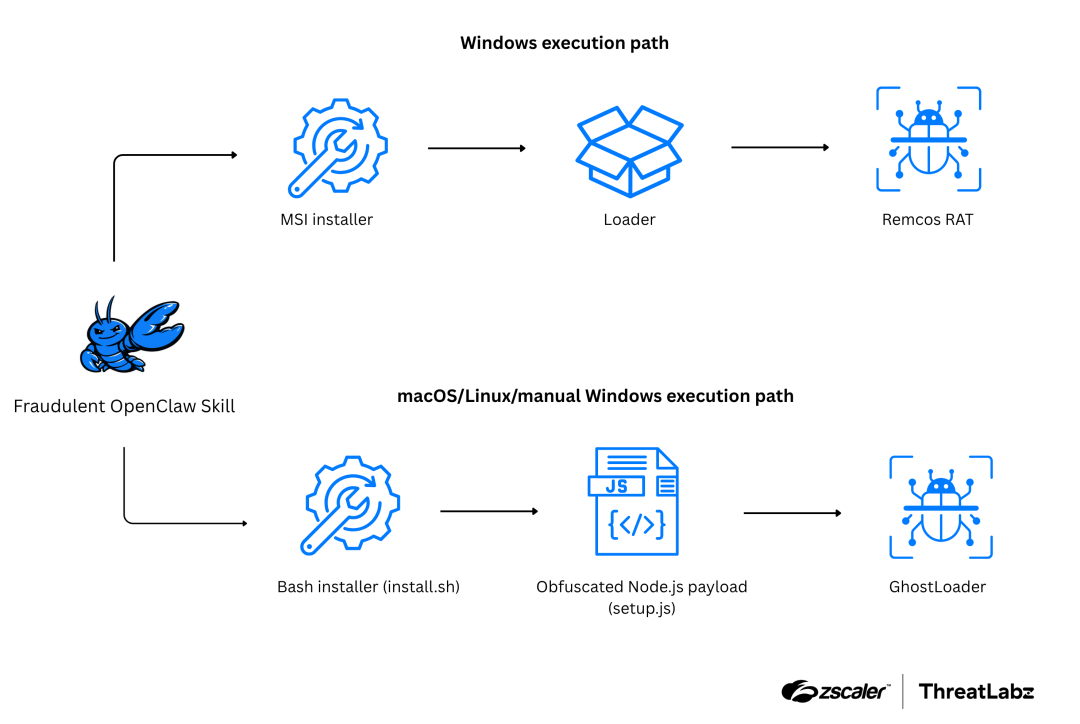
- On Windows, a PowerShell/cmd one-liner downloads a remote MSI that installs Remcos RAT via a sideloaded malicious g2m.dll alongside a legitimate G2M.exe.
- The in-memory shellcode loader patches ETW and AMSI, performs anti-debug/anti-VM checks, and decrypts the Remcos payload using TEA (CBC) before execution.
- Remcos establishes a TLS-encrypted C2, logs keystrokes, steals browser cookies and clipboard data, and can maintain remote interactive access.
- An alternate cross-platform path uses obfuscated Node.js/npm lifecycle scripts and Bash installers to deploy GhostLoader, which harvests keychains, SSH keys, wallets, and API tokens.
- Zscaler detects related artifacts via cloud sandboxing and flags the campaign with detections such as Win32.Backdoor.RemcosRat and Win32.Dropper.RemcosRat.
MITRE Techniques
- [T1195.002 ] Supply Chain Compromise – Publishing a deceptive DeepSeek-Claw skill on OpenClaw to compromise AI agentic workflows. (‘Publishing a deceptive DeepSeek-Claw skill on OpenClaw to compromise AI agentic workflows.’)
- [T1204.002 ] User Execution: Malicious File – Tricking the AI agent (or user) into parsing poisoned markdown (SKILL.md) to initiate the download. (‘Tricking the AI agent (or user) into parsing poisoned markdown (SKILL.md) to initiate the download.’)
- [T1059.003 ] Command and Scripting Interpreter: Windows Command Shell – Executing initial payload via cmd /c to start msiexec and fetch the remote MSI. (‘Executing initial payload via cmd /c.’)
- [T1218.007 ] System Binary Proxy Execution: Msiexec – Using msiexec /q /i to silently download and execute the malicious remote MSI file. (‘Using msiexec /q /i to silently download and execute the malicious remote MSI file.’)
- [T1059.004 ] Command and Scripting Interpreter: Unix Shell – Executing install.sh via bash to bootstrap the GhostLoader infection on macOS/Linux. (‘Executing install.sh via bash to bootstrap the GhostLoader infection on macOS/Linux.’)
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – Executing setup.js via npm lifecycle scripts as a first-stage dropper. (‘Executing setup.js via npm lifecycle scripts as a first-stage dropper.’)
- [T1574.002 ] Hijack Execution Flow: DLL Side-Loading – Abusing a legitimate signed GoToMeeting executable (G2M.exe) to side-load the malicious g2m.dll loader. (‘Abusing the legitimate, signed GoToMeeting executable (G2M.exe) to side-load the malicious g2m.dll loader.’)
- [T1562.001 ] Impair Defenses: Disable or Modify Tools – In-memory patching of ETW and AMSI to blind EDR telemetry. (‘In-memory patching of ETW and AMSI to blind EDR telemetry.’)
- [T1497.001 ] Virtualization/Sandbox Evasion: System Checks – Utilizing temporal latency checks and scanning for in-memory 0xCC software breakpoints to detect analysis environments. (‘Utilizing temporal latency checks and scanning for in-memory 0xCC software breakpoints.’)
- [T1027 ] Obfuscated Files or Information – Utilizing TEA in CBC mode to decrypt the Remcos payload dynamically in memory. (‘Utilizing the TEA in CBC mode to decrypt the Remcos payload dynamically in memory.’)
- [T1056.002 ] Input Capture: GUI Input Capture – Employing terminal-based social engineering (spoofed sudo prompts) to capture macOS/Linux user credentials. (‘Employing terminal-based social engineering (spoofed sudo prompts) to capture macOS/Linux user credentials.’)
- [T1555.001 ] Credentials from Password Stores: Keychain – Harvesting macOS Keychain databases (GhostLoader). (‘Harvesting macOS Keychain databases (GhostLoader).’)
- [T1552.004 ] Unsecured Credentials: Private Keys – Stealing local SSH keys from developer environments. (‘Stealing local SSH keys from developer environments.’)
- [T1005 ] Data from Local System – Pilfering cryptocurrency wallets and cloud service API tokens. (‘Pilfering cryptocurrency wallets and cloud service API tokens.’)
- [T1539 ] Steal Web Session Cookie – Stealing active browser sessions/cookies to bypass MFA. (‘Stealing active browser sessions/cookies to bypass MFA.’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 communication established by Remcos RAT and GhostLoader to exfiltrate stolen developer data and maintain remote access. (‘C2 communication established by Remcos RAT and GhostLoader to exfiltrate stolen developer data and maintain remote access.’)
Indicators of Compromise
- [File Hash ] MSI and loader hashes – 1c267cab0a800a7b2d598bc1b112d5ce, 2A5F619C966EF79F4586A433E3D5E7BA, and 2 more hashes
- [URL / Domain ] Remote MSI download URLs – hxxps://cloudcraftshub[.]com/api, hxxp://dropras[.]xyz/MSI
- [IP Address ] Remcos C2 – 146[.]19.24[.]131:2404
- [Domain ] GhostLoader C2 – hxxps://trackpipe[.]dev
- [GitHub Repository ] Malicious OpenClaw skill source – https://github.com/Needvainverter93/deepseek-claw
- [File Name ] Malicious binaries and scripts – G2M.exe, g2m.dll, remcos.exe, setup.js