The InstallFix campaign uses malicious Google Ads to lure users searching for Anthropic’s Claude into fake installer pages that trick them into running PowerShell commands which fetch and execute multi-stage, fileless malware. The attack chain includes mshta-triggered HTA/VBScript, AMSI and SSL bypasses, victim-unique C2 URLs, and indicators linked to RedLine stealer. #InstallFix #AnthropicClaude
Keypoints
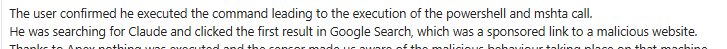
- Attackers purchase Google Ads for searches like “Claude Code” to deliver fake installer landing pages that present OS-specific commands encouraging users to execute them.
- The ClickFix command invokes mshta.exe to download a ZIP/HTA polyglot (claude.msixbundle) that appears legitimate but contains an appended VBScript HTA payload.
- The HTA decodes and launches a CMD/PowerShell stager that performs victim fingerprinting, disables SSL certificate validation, patches AMSI, and downloads a fileless stage from a victim-unique C2 domain.
- Telemetry captured mshta spawning cmd.exe/powershell.exe, scheduled task creation for persistence, and outbound network activity to attacker-controlled domains and IPs (e.g., oakenfjrod[.]ru; 104[.]21[.]0[.]95).
- Analysis recovered a payload file (SHA1: 811fbf0ff6b6acabe4b545e493ec0dd0178a0302, SHA256: 2f04ba77…) but final-stage execution was not confirmed due to endpoint protection termination.
- Indicators and behaviors observed align with known RedLine stealer activity, and the campaign targets multiple regions and industries globally via malvertising.
MITRE Techniques
- [T1566.002 ] Phishing: Search Engine Ads – Attackers used paid Google Ads to present sponsored search results that lead to a fake installer landing page (‘The fake install pages are distributed exclusively through Google Ads, specifically through sponsored search results’).
- [T1583.008 ] Malvertising – The campaign delivered malicious landing pages via advertising placements to deliver install commands (‘The fake install pages are distributed exclusively through Google Ads… the malvertising URL is designed to mimic a Google Ads link structure’).
- [T1218.005 ] Mshta (System Binary Proxy Execution) – mshta.exe was invoked to fetch and execute an appended HTA from a downloaded claude.msixbundle polyglot (‘The ClickFix command invokes mshta.exe with a remote URL pointing to claude.msixbundle’).
- [T1559.001 ] Component Object Model (COM) Abuse – The HTA VBScript abused Shell.Application COM to execute decoded commands silently (‘Shell.Application COM object … executes the decoded command via ShellExecute’).
- [T1059.005 ] VBScript/HTA Script Execution – Malicious VBScript embedded in the HTA decoded and launched the PowerShell execution sequence (‘The appended HTA executes VBScript silently inside mshta.exe’).
- [T1027 ] Obfuscated Files or Information – The attack used variable-splitting, base64/hex obfuscation, XOR and multiple decoding layers to hide payloads and keys (e.g., ‘DisplayEmailGnu() – hex-decodes… GetBiosDebian() – base64-decodes’).
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – A reconstructed PowerShell stager was executed (SysWOW64 PowerShell -EncodedCommand) to perform fingerprinting, SSL/AMSI bypass, and fileless fetch/execute (‘cmd.exe reconstructs powershell … invokes the 32-bit SysWOW64 PowerShell binary with a UTF-16LE base64-encoded payload’).
- [T1562 ] Impair Defenses (AMSI Bypass) – The stager RC4-decrypted AMSI bypass strings and overwrote amsiContext to disable AMSI scanning for the session (‘RC4-decrypts AMSI bypass strings … then writes 0x41414141 to amsiContext via [Runtime.InteropServices.Marshal]::WriteInt32’).
Indicators of Compromise
- [Domain ] malicious download and C2 infrastructure – download-version[.]1-5-8[.]com (hosted claude.msixbundle), oakenfjrod[.]ru (victim-unique C2 subdomains)
- [File name ] delivered payloads and installers – claude.msixbundle (ZIP/HTA polyglot), cloude-91267b64-989f-49b4-89b4-984e0154d4d1 (remote payload path)
- [File hash ] recovered payload artifacts – SHA1: 811fbf0ff6b6acabe4b545e493ec0dd0178a0302, SHA256: 2f04ba77bb841111036b979fc0dab7fcbae99749718ae1dd6fd348d4495b5f74
- [IP address ] observed outbound connections and C2 attempts – 104[.]21[.]0[.]95, 185[.]177[.]239[.]255, and attempted connections to 77[.]91[.]97[.]244
- [Command strings ] execution artifacts and obfuscation markers – presence of encoded PowerShell (-enc/-EncodedCommand/IEX) and AMSI-related string “AMSI_RESULT_NOT_DETECTED” used as XOR/decryption key
Read more: https://www.trendmicro.com/en_us/research/26/e/installfix-and-claude-code.html