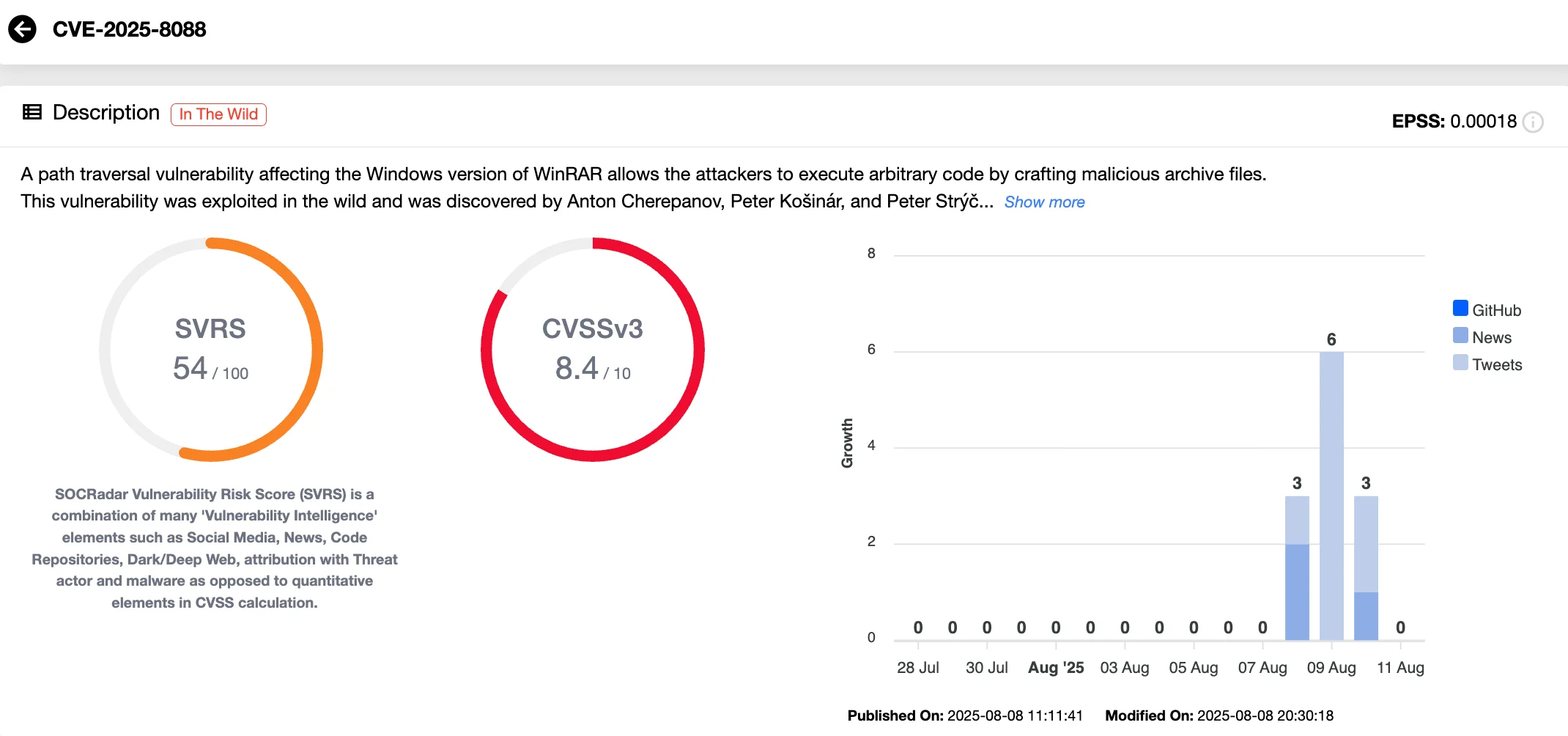
A WinRAR zero‑day, CVE-2025-8088, allowed attackers to abuse alternate data streams and path traversal to extract malicious files into privileged locations and was exploited in the wild from July 18, 2025 until patched in WinRAR 7.13 on July 30, 2025. ESET attributes primary exploitation to Russia-aligned RomCom (aka Storm-0978/UNC2596) and other actors like Paper Werewolf, with observed payloads including Mythic Agent, SnipBot variants, RustyClaw, and MeltingClaw. #CVE-2025-8088 #RomCom #MythicAgent #SnipBot #RustyClaw #MeltingClaw
Keypoints
- CVE-2025-8088 is a path traversal vulnerability in WinRAR/UnRAR that abuses alternate data streams (ADSes) to extract files outside intended directories.
- All WinRAR versions up to 7.12 were vulnerable; exploitation was observed from July 18, 2025 and a patch was released in WinRAR 7.13 on July 30, 2025.
- ESET links primary exploitation to RomCom (Storm-0978/Tropical Scorpius/UNC2596), targeting financial, defense, manufacturing, and logistics firms via spearphishing with RAR lures.
- Three execution chains were observed: Mythic Agent via COM hijacking, a SnipBot variant using anti-analysis checks, and RustyClaw/MeltingClaw downloaders with modular C2s.
- Other actors, including Paper Werewolf, also exploited the flaw—possibly after purchasing an exploit—and combined it with CVE-2025-6218 in some campaigns.
- Attacks achieve persistence by placing DLLs in %TEMP% or %LOCALAPPDATA% and dropping .lnk shortcuts into Startup folders to execute on login.
- Mitigations: upgrade to WinRAR 7.13+, update UnRAR.dll dependencies, enforce extraction path restrictions, educate users on spearphishing, and monitor for .lnk and unexpected DLLs.
MITRE Techniques
- [T1204] User Execution – Victims are tricked into extracting RAR archives (spearphishing job application lures) which trigger payload extraction. Quote: ‘the archive appears to contain a single innocuous file… hidden from the user’s view, however, are multiple malicious ADS entries.’
- [T1055] Process Injection – Malicious DLLs are placed and used to decrypt and execute embedded shellcode (‘DLL decrypts and executes embedded shellcode’).
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – Crafted .lnk files are dropped into the Startup folder and registry manipulation hijacks COM object PSFactoryBuffer for persistence (‘Crafted .lnk shortcut files can be dropped into the Startup folder’ and ‘Registry manipulation hijacks COM object PSFactoryBuffer’).
- [T1105] Ingress Tool Transfer – Downloaders (RustyClaw, MeltingClaw) fetch additional malware from attacker-controlled infrastructure (‘Fetches additional malware, including the MeltingClaw downloader’).
- [T1562] Impair Defenses (Anti-analysis) – SnipBot variant performs anti-sandbox checks by verifying recent document activity to avoid analysis (‘Uses anti-sandbox checks by verifying recent document activity’).
- [T1203] Exploitation for Client Execution – CVE-2025-8088 is exploited in crafted archives to achieve arbitrary file placement and execution on the client system (‘a vulnerability … allows an attacker to trick WinRAR into extracting files outside the user’s intended directory’).
Indicators of Compromise
- [File names / hashes] Malicious RARs and payloads – Adverse_Effect_Medical_Records_2025.rar (SHA-1: 371A5B8BA86FBCAB80D4E0087D2AA0D8FFDDC70B), cv_submission.rar (SHA-1: D43F49E6A586658B5422EDC647075FFD405D6741)
- [File names / hashes] Executables and DLLs – Complaint.exe (SHA-1: AB79081D0E26EA278D3D45DA247335A545D0512E), install_module_x64.dll (SHA-1: 01D32FE88ECDEA2B934A00805E138034BF85BF83)
- [File names / hashes] Additional payload examples – ApbxHelper.exe (SHA-1: 1AEA26A2E2A7711F89D06165E676E11769E2FD68), msedge.dll (SHA-1: AE687BEF963CB30A3788E34CC18046F54C41FFBA)
- [C2 domains / IPs] Command-and-control infrastructure – 162.19.175[.]44 / gohazeldale[.]com (MeltingClaw C2), 194.36.209[.]127 / srlaptop[.]com (Mythic agent C2)
- [C2 domains / IPs] Additional C2 examples – 85.158.108[.]62 / melamorri[.]com (RustyClaw C2), 185.173.235[.]134 / campanole[.]com (SnipBot C2)
Read more: https://socradar.io/cve-2025-8088-winrar-zero-day-exploited-targeted/