Zanubis is an advanced Android banking Trojan that has evolved since 2022, primarily targeting Peruvian banks and financial institutions by using overlay attacks and accessibility permissions to steal credentials and perform remote control. Its continuous development includes new features such as SMS hijacking, fake update overlays, reinforced encryption, and silent installation tactics to evade detection and increase infection rates. #Zanubis #SUNAT #PeruvianBanks
Keypoints
- Zanubis first appeared in August 2022 targeting Peruvian banks and cryptocurrency exchange users through fake legitimate apps.
- The malware uses Android accessibility permissions for overlay attacks to capture user credentials stealthily.
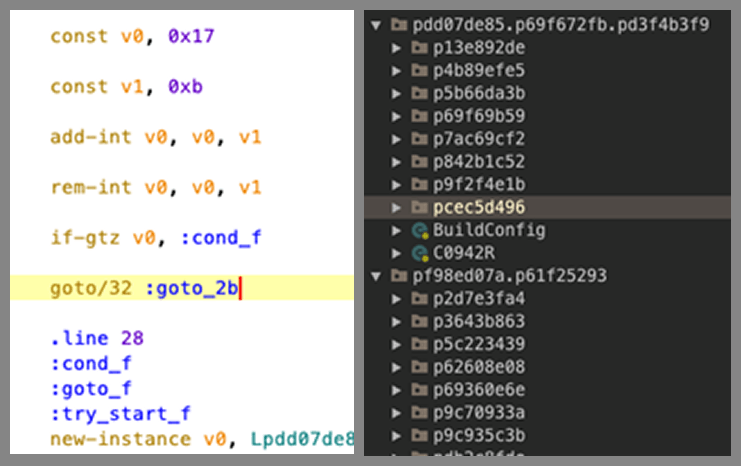
- In 2023, Zanubis introduced code obfuscation using Obfuscapk and implemented deceptive social engineering tactics to obtain permissions.
- New features include SMS hijacking as the default SMS app to intercept two-factor authentication codes and fake Android update overlays to lock victim devices.
- In 2024, the Trojan upgraded its encryption methods using AES with keys derived via PBKDF2 and expanded its targeting to virtual cards and cryptocurrency wallets.
- By 2025, Zanubis changed distribution tactics impersonating Peruvian energy and banking entities and employed silent installation to evade user detection.
- The threat actors appear to operate from Peru, focusing on local financial institutions with continuous updates and refined malware capabilities.
MITRE Techniques
- [T1548] Abuse Elevation Control Mechanism – Zanubis gains accessibility permissions by manipulating users through fake instructional web pages to enable malware capabilities (‘displayed a fake instructional webpage using WebView… button labeled “Go to Accessibility” redirected to settings’).
- [T1056.001] Keylogging – The malware monitors user interface events such as taps and text input to capture credentials (‘track user interface events such as taps, focus changes, and text input, effectively capturing sensitive information’).
- [T1528] Steal Application Access Tokens – Zanubis hijacks SMS messages by setting itself as the default SMS app to intercept authentication codes (‘set itself as the default SMS app on the device, intercepting all incoming messages’).
- [T1436] Screen Capture – The malware uses screen recording to capture user interactions within targeted apps (‘activate screen recording to capture everything the user did within the app’).
- [T1071.001] Application Layer Protocol – Communication with the command and control server uses encrypted protocols including RC4 and AES over WebSocket and Socket.IO (‘communication with the C2 API was encrypted with RC4… newer versions use AES in ECB mode’).
- [T1565.001] Data from Local System – Collected user logs and device information are stored locally before exfiltration (‘stored locally and later sent to the C2 server upon request’).
- [T1553] Subvert Trust Controls – Zanubis displays fake Android system update overlays to lock devices and prevent user intervention (‘simulated a legitimate Android system update… rendered device unusable’).
- [T1547] Boot or Logon Autostart Execution – The malware disables battery optimization to ensure persistence and background activity (‘bypass battery optimization… ensuring it can remain active in the background indefinitely’).
- [T1608] Stage Capabilities – The malware downloads and installs payloads silently using the PackageInstaller class (‘dropper attempts to silently install the final payload, Zanubis, using the PackageInstaller class without user involvement’).
Indicators of Compromise
- [File Hashes] Zanubis 2025 version sample hashes – hash example: 81f91f201d861e4da765bae8e708c0d0fd43666006938b7c77b990b2b4531b9a8, and over 30 additional variants uploaded from Peru.
- [File Names] Fake app names used for distribution – “BoletaXXXXXX” and “FacturaXXXXXX” mimicking invoices for an energy sector company, and fake bank advisor app names to lure victims.
- [URLs] Hardcoded C2 server URLs – example includes initial hardcoded URL for WebSocket communication used for data exfiltration in early versions.
- [App Package Names] List of targeted financial applications in Peru – includes over 40 banking and financial app package names used for overlay triggers.
Read more: https://securelist.com/evolution-of-zanubis-banking-trojan-for-android/116588/