This article revisits a fake YouTube DMCA phishing campaign, showing that older IP, favicon, and CSS-hash pivots quickly went stale while C2 banner and header fingerprints kept revealing new infrastructure. It also shows how Malwarebytes indicators like dmca-notification[.]info and blacklivesmattergood4[.]com can be expanded through title-tag and redirect-pattern pivots to uncover many related domains. #dmca-notification #blacklivesmattergood4 #YouTube
Keypoints
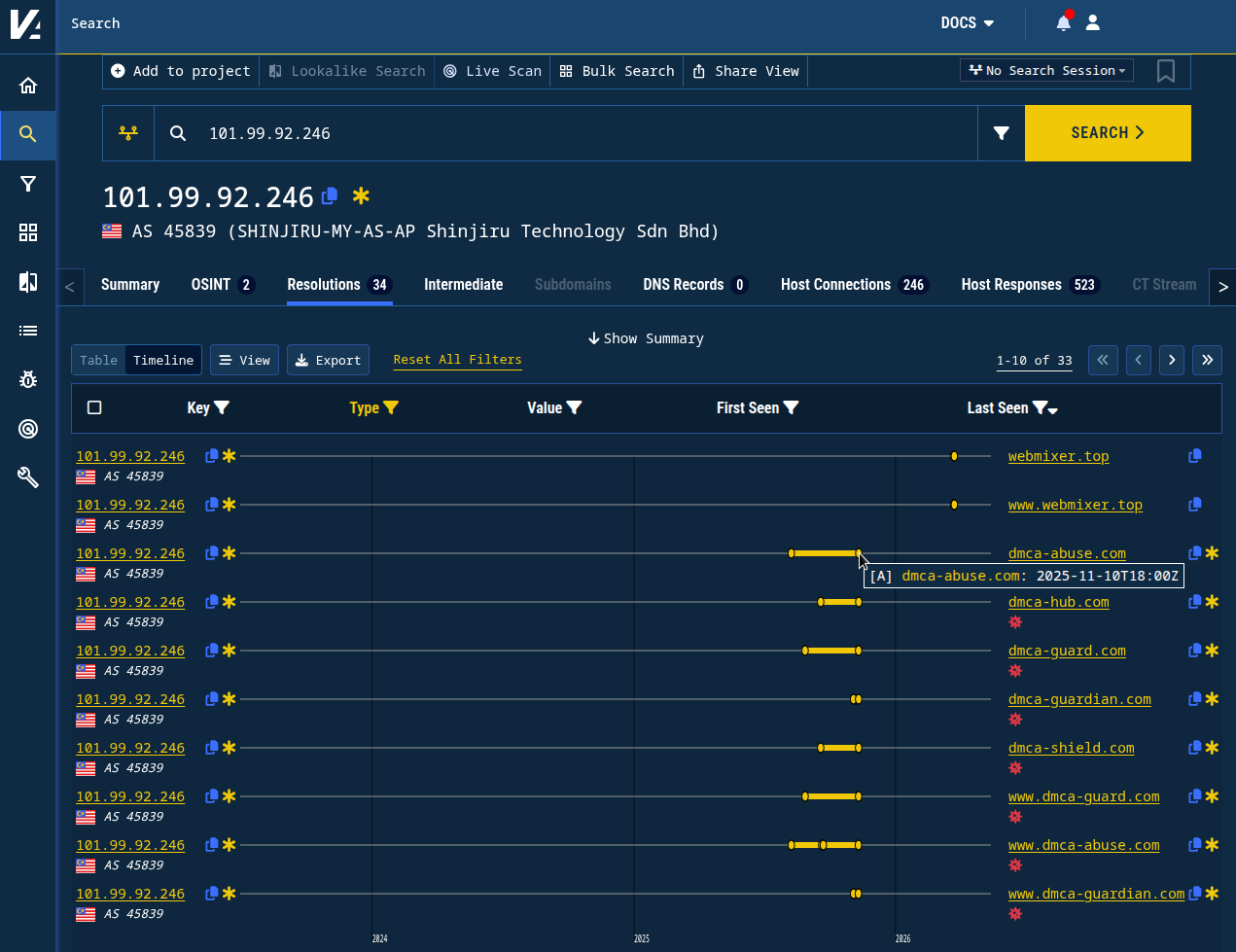
- Older pivots from the November 2025 investigation, including IP addresses and simple hashes, quickly stopped producing new results.
- CSS class and favicon hashes from the earlier campaign also showed little or no continued activity.
- C2 banner hash and header-hash pivots remained useful and continued to expose related infrastructure months later.
- The April 2026 Malwarebytes campaign used a different phishing flow, including a fake Google login built with a Browser-in-the-Browser technique.
- The phishing site dmca-notification[.]info produced a title-tag fingerprint that matched hundreds of related domains in Validin.
- The credential-harvesting domain blacklivesmattergood4[.]com redirected to /youtube/main/, which helped identify nearly 100 additional domains with the same pattern.
- The article concludes that Validin can amplify point-in-time indicators into broader infrastructure discovery using historical DNS, header hashes, title tags, and redirect patterns.
MITRE Techniques
- [T1566 ] Phishing – The campaign used fake copyright notices and login lures to trick YouTube creators into engaging with malicious sites (‘fake “DMCA Takedown” scam targeting YouTube creators’ and ‘fake Google login’).
- [T1185 ] Browser Session Hijacking – The newer campaign used a Browser-in-the-Browser technique to create a convincing fake login window (‘used a different flow: a personalized, fake Google login using a Browser-in-the-Browser technique’).
- [T1071.001 ] Web Protocols – The phishing and credential-harvesting infrastructure relied on web traffic, redirects, and hosted pages to communicate and collect credentials (‘the domain redirects to /youtube/main/’ and ‘crawled the primary phishing site’).
- [T1588.006 ] Obtain Capabilities: Malware – The lure attempted to get victims to download malware under the guise of resolving a copyright complaint (‘The scam attempted to lure victims into downloading malware’).
- [T1036 ] Masquerading – The domains and pages impersonated legitimate YouTube/Google copyright and verification workflows to appear trustworthy (‘fake “DMCA Takedown”’ and ‘copyright notice campaign’).
- [T1598 ] Phishing for Information – The campaign sought credentials through a credential-harvesting endpoint (‘blacklivesmattergood4[.]com (reported as a credential-harvesting domain)’).
Indicators of Compromise
- [IP addresses] historical DNS and C2-related infrastructure – 101.99.92[.]246, 101.99.89[.]94, and other IPs such as 46.151.182[.]8 and 45.156.87[.]34
- [Domains] phishing and related infrastructure – dmca-notification[.]info, blacklivesmattergood4[.]com, and dozens of related domains such as dmca-takedown[.]info and youtube-dmca[.]cfd
- [Hash values] class, favicon, banner, and header fingerprints – a927b832d5f0baf0fea5a427588da6c5, 1e69c76842689565c2c46580042f2e54, and 5dab1fa5f7d42e5eca2385ce3dad1f03
- [Header hashes] Cloudflare-fronted C2 response patterns – d40097143f9b1abeee08, d40097143f9b99e0163d, and d40097143f9bb3172887
- [Redirect paths] credential-harvesting behavior – /youtube/main/ used as a recognizable redirect target
- [Certificate subject strings] self-signed certificate naming pattern tied to C2 infrastructure – /C=US/ST=New York/L=Seoul/O=SilicoBrain Networks/OU=Helpdesk/CN=recordcustomers.network
Read more: https://www.validin.com/blog/dmca_phishing_revisited/